基于TPM的可信网络连接技术TNC IF-T协议绑定v2.0第5版
需积分: 1 106 浏览量
更新于2024-06-22
收藏 728KB PDF 举报
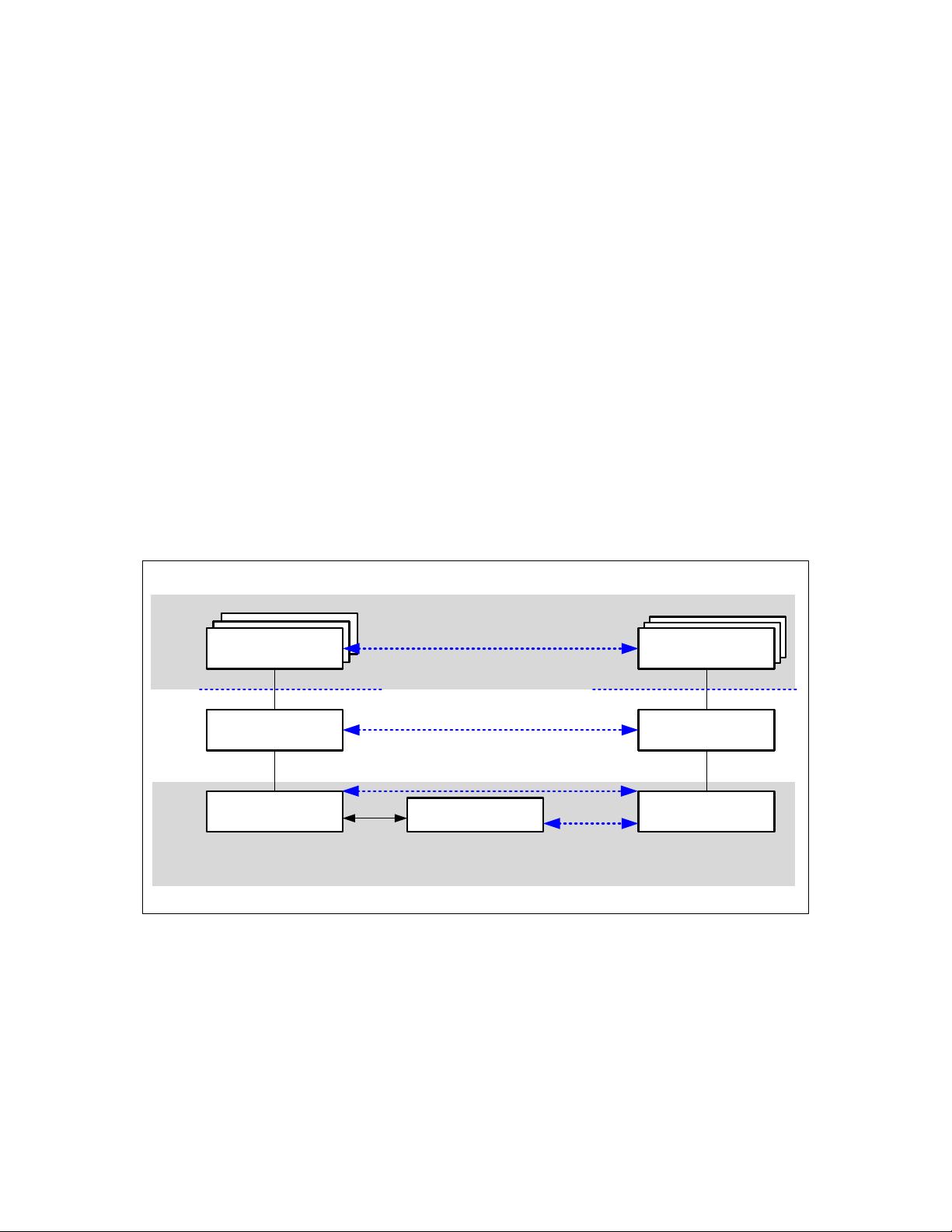
本资源是一份名为"TNC_IFT_EAP_v2_0_r5-a2.pdf"的技术规范文档,主要关注于基于TPM(Trusted Platform Module)的可信网络连接(TNC)通信技术。TPM是一种安全芯片,用于增强计算机平台的安全性和可信度,而TNC则是通过TPM实现的一种安全网络连接协议。
该文档详细规定了TNC IF-T(Trusted Network Communication IF for Tunneled EAP Methods)协议的绑定,专注于隧道化EAP(Extensible Authentication Protocol)方法的特定版本,即第2.0修订版第5版。EAP是一种在网络中验证用户身份的通用框架,而TNC IF-T则扩展了这一框架,通过TPM的保护,确保在传输过程中数据的完整性和隐私性。
文档中强调,这份技术规范是"AS IS"形式提供,即无任何保证,包括但不限于商品质量、非侵权性、适合特定目的或任何其他源于提案、规格或样例的保修。TCG(Trusted Computing Group)明确声明对此规范的使用责任自负,并且不对任何由此产生的知识产权侵犯、采购替代品的成本、利润损失、数据丢失或其他间接或特殊损害承担责任。
这份规范对于开发人员、系统管理员和安全专家来说具有重要意义,因为它提供了实现高度安全的网络连接所需的清晰指导,尤其是在支持TPM的环境中,这对于防止未经授权的访问和保护敏感信息至关重要。遵循这份规范有助于确保系统的可靠性和安全性,同时提醒用户在实施时应充分理解并处理相关的法律和责任问题。
2023-07-21 上传
2022-09-14 上传
2023-07-21 上传
2023-07-21 上传
2023-07-21 上传
2023-07-21 上传
2023-07-21 上传
2023-07-21 上传

书香度年华
- 粉丝: 1w+
- 资源: 383
最新资源
- 前端协作项目:发布猜图游戏功能与待修复事项
- Spring框架REST服务开发实践指南
- ALU课设实现基础与高级运算功能
- 深入了解STK:C++音频信号处理综合工具套件
- 华中科技大学电信学院软件无线电实验资料汇总
- CGSN数据解析与集成验证工具集:Python和Shell脚本
- Java实现的远程视频会议系统开发教程
- Change-OEM: 用Java修改Windows OEM信息与Logo
- cmnd:文本到远程API的桥接平台开发
- 解决BIOS刷写错误28:PRR.exe的应用与效果
- 深度学习对抗攻击库:adversarial_robustness_toolbox 1.10.0
- Win7系统CP2102驱动下载与安装指南
- 深入理解Java中的函数式编程技巧
- GY-906 MLX90614ESF传感器模块温度采集应用资料
- Adversarial Robustness Toolbox 1.15.1 工具包安装教程
- GNU Radio的供应商中立SDR开发包:gr-sdr介绍