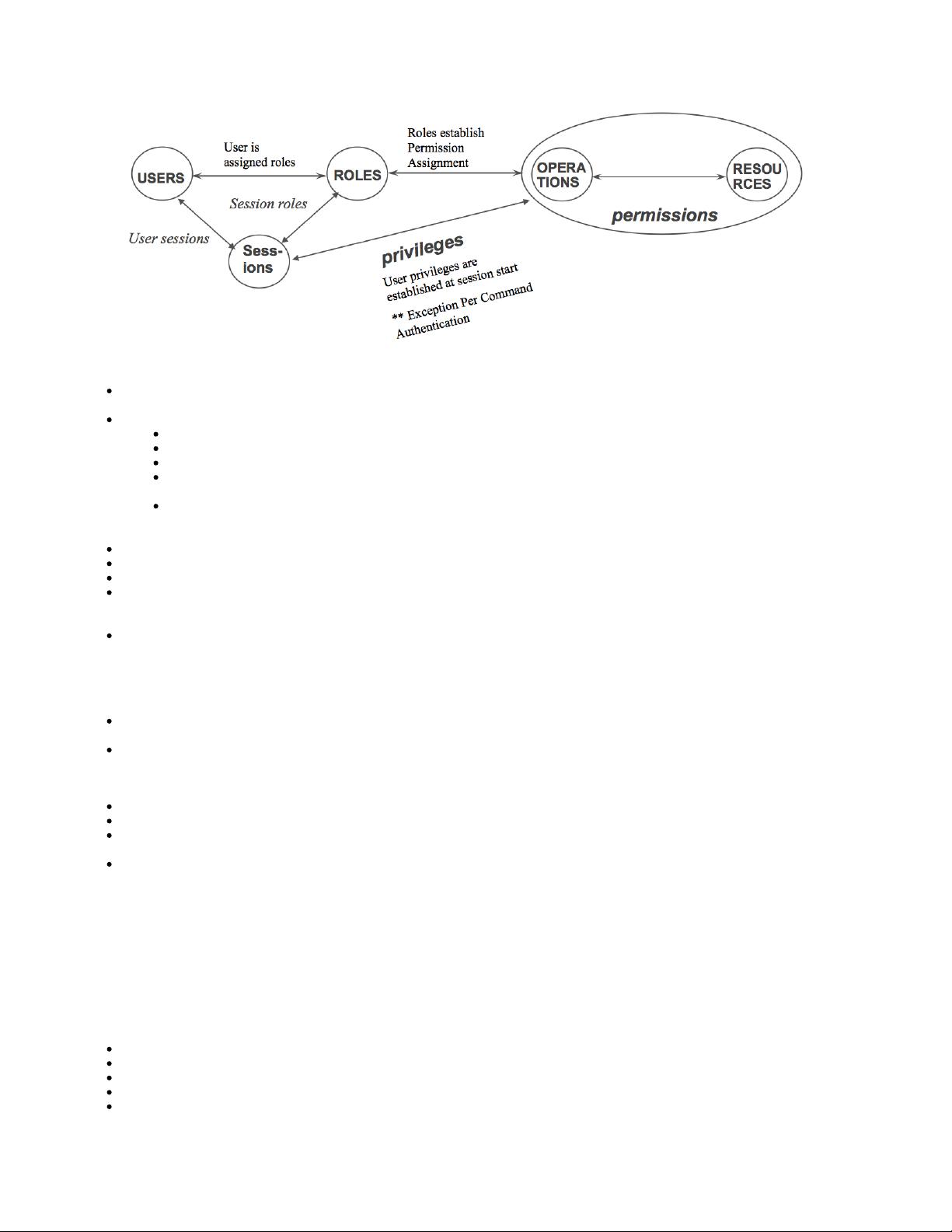
Role: A defined set of permissions required to perform a job function with a clear definition of responsibility and authority in the AXOS
system. Roles promote the notions of least privilege, separation of duties, and abstraction
Permission: A defined access right associated with an operation on a resource in the AXOS system.
Permissions have a name, and description.
Each permission maps to one or more objects in the containment model as defined in YANG
CLI operations define the set of permissions they require.
Permissions are defined hierarchically within AXOS. Permissions can group other permissions or permissions can be leafs in the
hierarchy.
Permissions can be allowed or denied to a role at any level of the hierarchy. The more specific the level of permission assigned,
the higher the precedence. So assigning permissions at the root of the hierarchy is of lower precedence then assigning
permissions at a leaf in the hierarchy of permissions.
Operation: A behavior defined to be on a resource in the AXOS system
Resource: An object in the AXOS system data model. Equipment, interface, service etc…
User: Represents a person with one or more roles that may be authenticated and authorized on the AXOS system
Session: a period of time during which a user is actively connected, authenticated and authorized with an AXOS system. During this
time, the user is granted privileges as defined by the set of permissions associated with his assigned roles and/or as specified during
authorization with TACACS+
Privilege: A right to perform a defined operation on one or more resource(s) in the AXOS system. A privilege is the realization of a
permission when applied to a user. If a user does not have a privilege on some function, they can not see that function in the CLI nor can
they retrieve it or operate on it via NETCONF.
All users who can log in to the AXOS system must have at least one role. With a role, you define the following:
Access privileges that users have when they are logged in to the AXOS device. One or more Permissions are assigned to a role. One or
more roles are assigned to an user or group of users.
Commands and statements that users can and cannot specify via user agents
AXOS systems contains a few predefined roles. The predefined roles cannot be modified.
System Administrator (admin): Create, read, write, delete and execute permissions.
Security Administrator (secadmin): Create, read, write, delete and execute permissions for all device management plane AAA aspects.
Network Administrator (networkadmin): Create, read, write, delete and execute permissions, with the exception of configuring
Authentication and Authorization.
Operator (oper): Read-only permissions
Users with privileges (i.e. security administrator) can further define additional roles as a part of role engineering and supporting notions of least
privilege, separation of duties, and abstraction.
Authentication is a process of identifying the user and verifying that the user is allowed to login. A user may login into the CLI (via SSH and
Telnet) or NETCONF (via SSH).
Authorization is a process of identifying if an authenticated user has the privilege to execute a command. The authorization process via
TACACS+ involves returning the roles and permissions a user has as configure for the user in the Tacacs+ server.
User accounts provide one way for users to access the AXOS system.User accounts associate:
the username - a name that uniquely identifies the user.
the roles associated with the user with each role specifying a set of permissions
a account profile specifying account aging, failed login behavior (invalid login attempts, lockout period) idle-timeout, locking,
a password profile specifying password complexity rules, aging, consecutive unique passwords, behavior on initial login
An AXOS user with a local user account or TACACS+ based user account can change their own password or a security admin (or a user
with the appropriate role with permissions to do so) can change their password for them.
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助 


 信息提交成功
信息提交成功