6
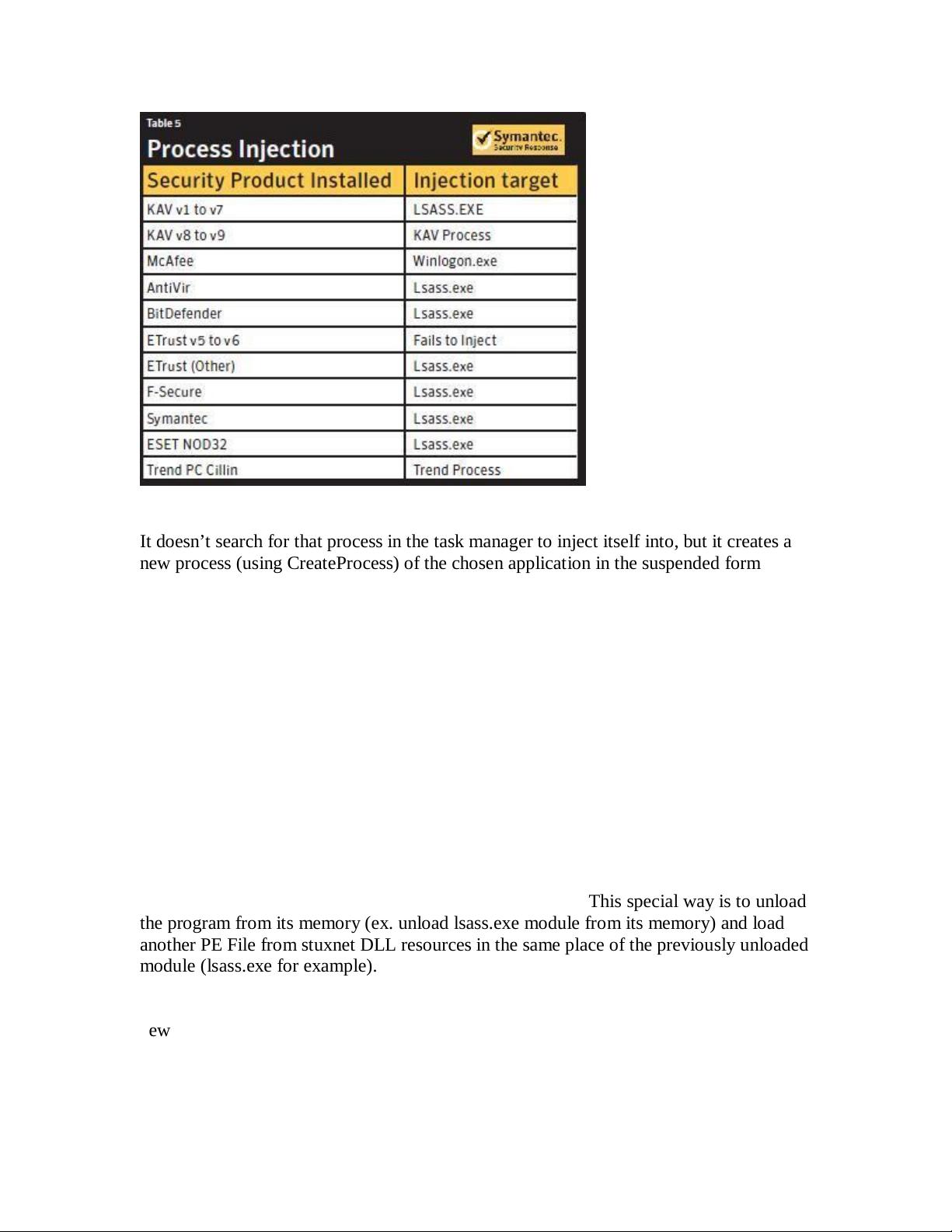
It doesn’t search for that process in the task manager to inject itself into, but it creates a
new process (using CreateProcess) of the chosen application in the suspended form like
that:
ESP ==> > 0006F4F8 |ModuleFileName =
"C:\WINDOWS\\system32\\lsass.exe"
ESP+4 > 00000000 |CommandLine = NULL
ESP+8 > 00000000 |pProcessSecurity = NULL
ESP+C > 00000000 |pThreadSecurity = NULL
ESP+10 > 00000001 |InheritHandles = TRUE
ESP+14 > 0800000C |CreationFlags =
CREATE_SUSPENDED|DETACHED_PROCESS|CREATE_NO_WINDOW
ESP+18 > 00000000 |pEnvironment = NULL
ESP+1C > 00000000 |CurrentDir = NULL
ESP+20 > 0006F13C |pStartupInfo = 0006F13C
ESP+24 > 0006F730 \pProcessInfo = 0006F730.
After creating this process, it injects itself by a special way. This special way is to unload
the program from its memory (ex. unload lsass.exe module from its memory) and load
another PE File from stuxnet DLL resources in the same place of the previously unloaded
module (lsass.exe for example).
Before loading this new PE File, stuxnet makes some modifications to the file by adding
new section (in the beginning) named “.verif”. This section makes the PE File’s size
equal to the size of the previously unloaded module. And at the place of the entrypoint of
the unloaded module, stuxnet writes a “jmp” instruction to the entrypoint of this PE File.