Power State Coordination Interface
Page 18 of 92 Copyright © 2012, 2013, 2015, 2017 - 2022 Arm Limited or its affiliates. All rights reserved. DEN0022E
Non-Confidential
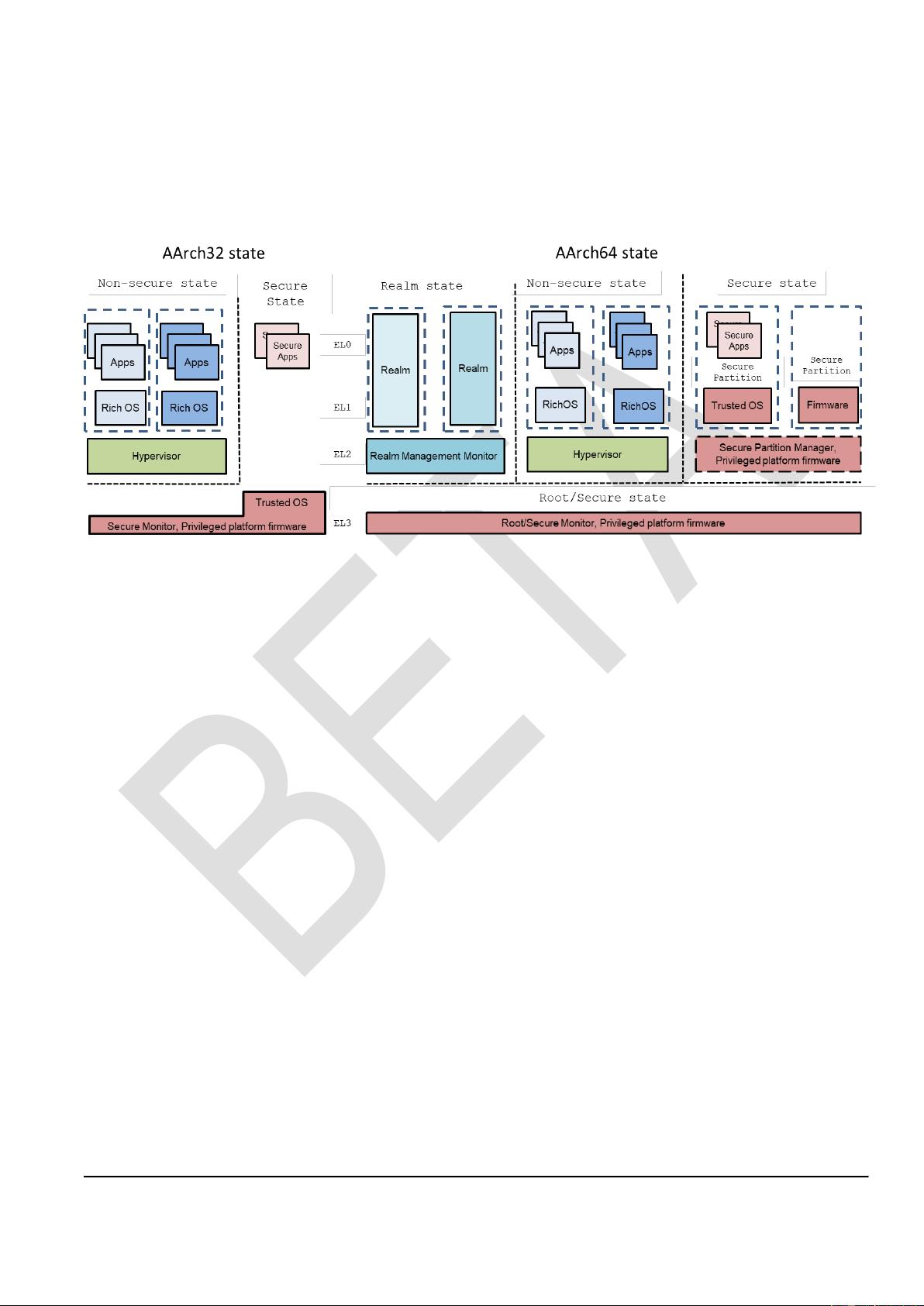
Note: While the Arm Architecture Reference Manuals [1, 5] define Secure and Non-secure Security
states, and the Arm processor documentation uses these state names. Arm software documentation
often refers to these states as Secure and Normal world, respectively. This reflects the fact that
software normally executes in Non-secure state.
The PSCI specification focuses on the interface between Security states for power management. It
provides a method for issuing power management requests. To deal with the requests, the PPF must
include a PSCI implementation. A PSCI implementation might require communication between the PPF
and a Trusted OS or SP. Currently, how this communication is handled is specific to individual vendors.
Arm recommends using the Firmware Framework for Arm v8-A [10] to handle this communication.
Although the PSCI specification focuses on power management requests between Security states, the
interface can also be reused easily at the junction between Rich OS kernels and hypervisors, or Realms
and Realm Management Monitor (RMM).
3.4 Conduits
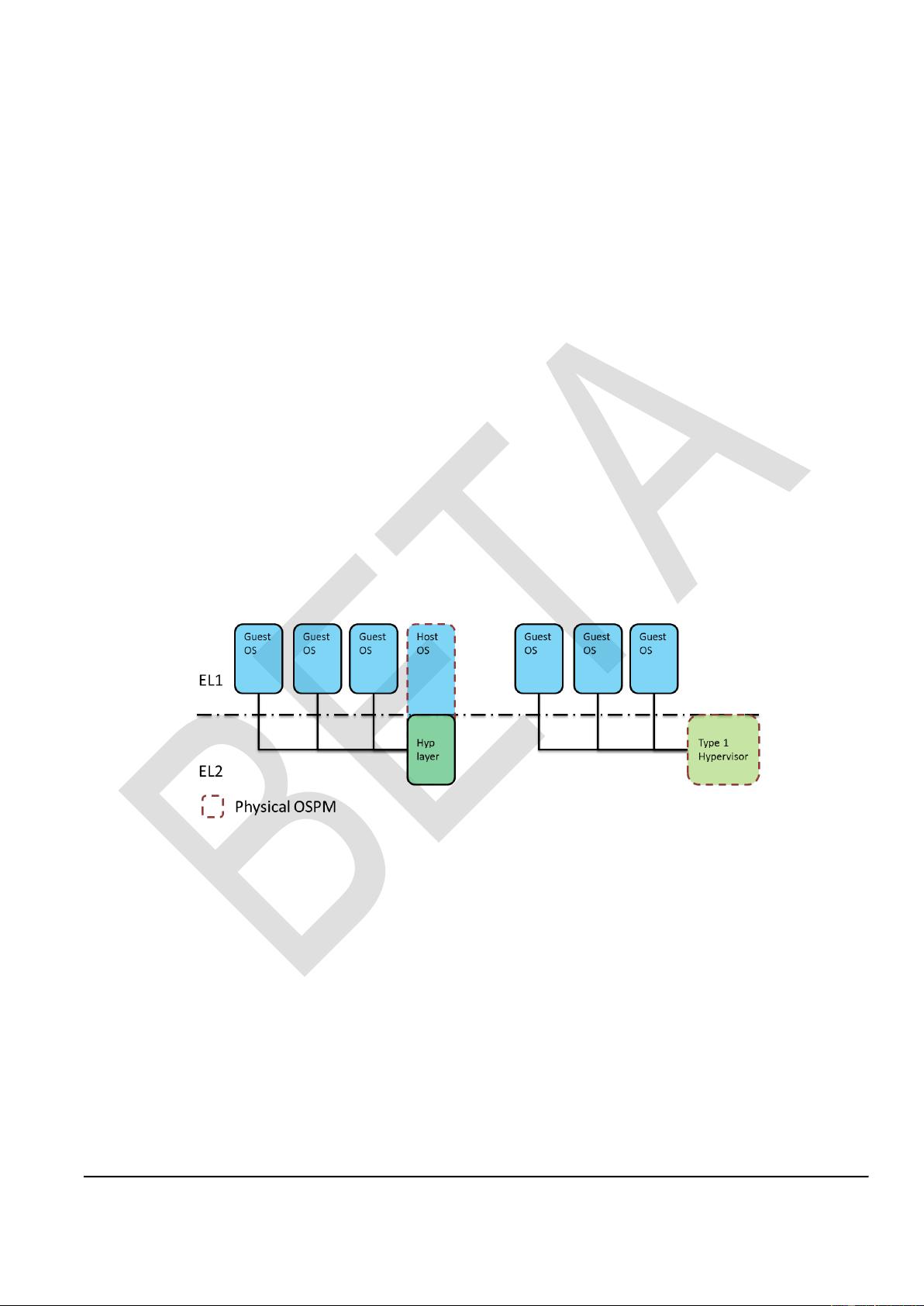
The PSCI interface must support interaction at all levels of execution implemented on the device, where
multiple levels of supervisory software might be executing. For the caller operating in the Normal world,
the interface must forward a message to the PPF. In a system that implements EL2, it must be possible
to trap interface calls made by the EL1 kernel context to the hypervisor (EL2). In a system that
implements Arm RME, it must be possible to trap interface calls made by the Realm executing at R-
EL1, to the RMM executing at R-EL2. The RMM can then decide to forward the call to the Hypervisor
executing at NS-EL2 [14]. If the hypervisor determines that a change of physical power state is
required, it must then be able to use the PSCI interface to inform the PPF.
The conduits available to transfer a message from one Exception level to another depend on the
implemented Exception levels and Security states. For further information on the description of possible
conduits, see [4] and [14].
3.5 Secure world software and power management
Many Trusted OS implementations are not SMP-capable. When running on MP devices, they are tied to
a single core. Secure Monitor Calls destined for the Trusted OS are only expected to come from that
core. The lack of MP support in the OS helps to keep Trusted code simple and small, which in turn aids
certification. Trusted OS services are invoked from the Normal world through Rich OS drivers or
daemons that are provided with the Trusted OS implementations. The threads associated with these
drivers and daemons are normally affinitized to the core used by the Trusted OS.
Arm systems generally include a power controller, or control logic, that can manage core power. This
normally provides interfaces that support several power management functions. Often these include
support for transitioning cores, clusters, or a superset into low-power states. In the low-power state, the
cores are either fully switched off or in quiescent states where they are not executing code. Arm
strongly recommends that the EL3 is responsible for the control of these states. Otherwise,
cleanup of the Root and Secure state, including cache clean, is not possible prior to entering the low-
power state. Other forms of power management, such as dynamic performance management through
voltage and frequency scaling, are not covered by this interface. Arm strongly recommends that all
policy in power and performance management is performed in the Normal world. The Normal
world has greater visibility of the current use and purpose of a given device. Where the Secure world
has performance requirements, Arm recommends that IMPLEMENTATION DEFINED mechanisms are
used to communicate those requirements to the Normal world.