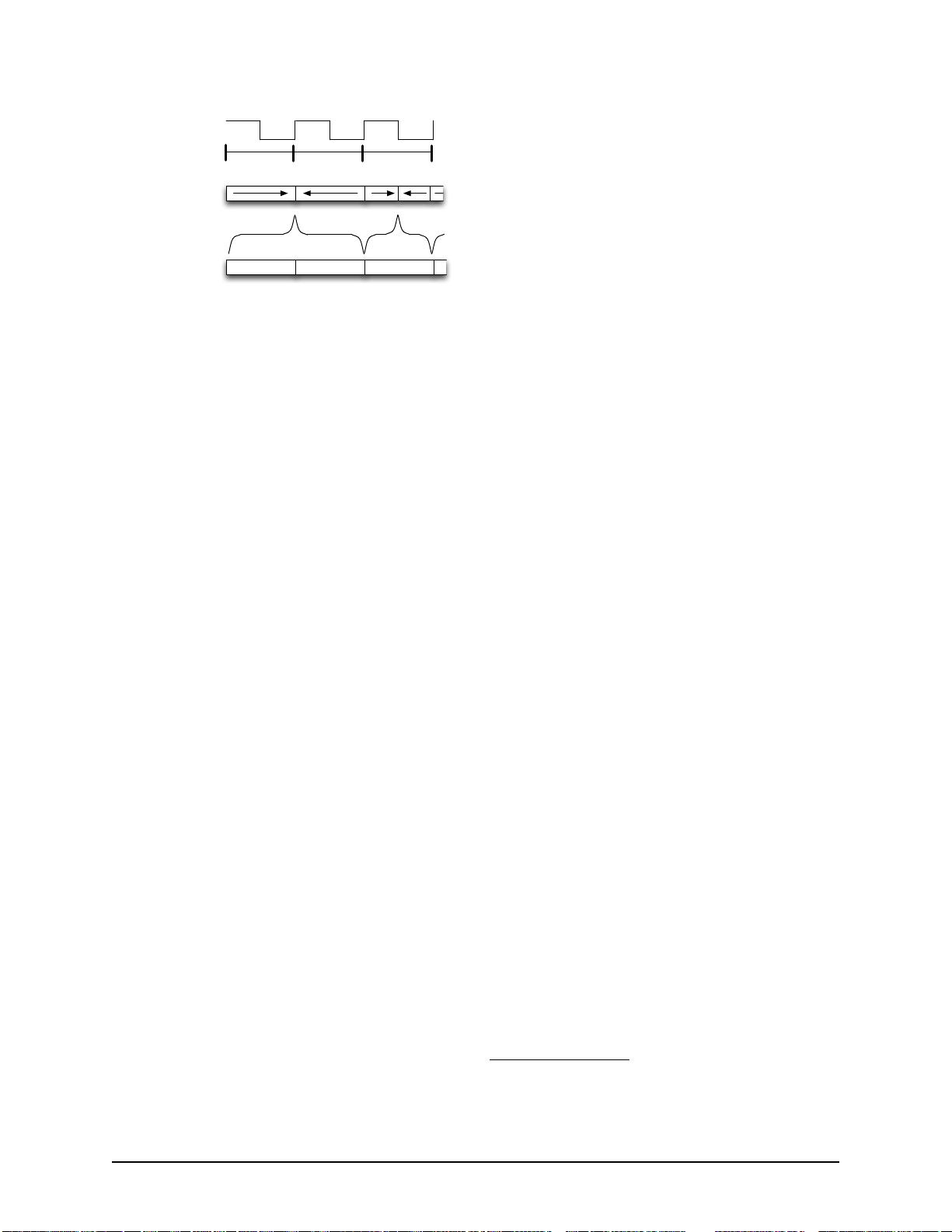
0 1 0
Magnetic Stripe
Polarity
Signal
Decoded Binary
Clock Ticks
NN SS S
Figure 1: F2F Encoding: A polarity transition per clock
cycle encodes a 0, whereas two encode a 1.
conspicuous 3D-printed skimmer. We then use 10
real-world skimmers to show that our system is ro-
bust against a wide variety of skimmer form factors.
The security of payment systems in general, and
ATMs in specific, has long been studied in Computer Se-
curity [11]. Many members of the public even argued
that such devices were already secure enough to use for
national elections (although significant research in that
space disagreed with such an assertion [32, 47, 45]). Un-
fortunately, these systems remain significantly vulnera-
ble and require continued attention.
The remainder of the paper is organized as follows:
Section 2 offers a primer on payment card readers and
fraud against those devices; Section 3 analyzes and cate-
gorizes the skimming devices found by the NYPD’s Fi-
nancial Crimes Task Force in 2017; Section 4 details the
design of the “Skim Reaper” detector; Section 5 pro-
vides experimental results against real recovered skim-
ming devices; Section 6 discusses countermeasures and
other insights; Section 7 examines related research; and
Section 8 gives our concluding remarks.
2 Fundamentals of Card Reading & Fraud
2.1 Magnetic Stripe Encoding
Magnetic stripes store small amounts of data using fre-
quency/double frequency (F2F) encoding. F2F stores
both the clock and the data, allowing a reader to quickly
synchronize and read the data when the card moves at
an inconsistent speed (such as when being swiped). Fig-
ure 1 shows how decoding is performed: when the mag-
netic polarity change occurs within a clock cycle, the
bit is a 1. Otherwise, it is a 0. Finally, the bitstream
is decoded into plaintext characters containing the card
data (e.g., name, account number, and expiration date).
Data is stored on up to three adjacent tracks on a single
stripe [29, 30], each having its own standard for character
encoding and density.
2.2 Fraud
Magnetic stripe cards offer no inherent protection from
duplication. All data contained on a card’s tracks are
written as plaintext, and an adversary with access to the
magnetic stripe (e.g., with a skimmer) can create a legit-
imate card. These cloned cards, while magnetically dis-
tinguishable from the originals [4, 48], contain the same
data as the originals.
To prevent the use of counterfeit cards, banks and pay-
ment networks added Card Verification Values (CVVs).
CVV1 codes are part of the data on the magnetic stripe.
This code prevents the card from being cloned with only
knowledge of data printed on the physical card (e.g., the
account number). However, if the adversary has access
to read the card’s magnetic stripe, the CVV1 code is eas-
ily cloned along with the rest of the stripe data. CVV2
codes are printed on the physical card and are often re-
quested when making phone or online purchases (known
as “card not present transactions”). This code is intended
to prove possession of the original card. Adversaries can
either acquire this code by recording PIN entry with a
camera
1
, through sites that sell card data with codes, and
with compromised web browsers [35].
Once the adversary has obtained data and created a
counterfeit card, the cards are “cashed out.” When cash-
ing out, counterfeit cards are used to either purchase
goods (to be resold later) or to retrieve cash from an
ATM. Once purchases for a given card are declined, the
cards are discarded.
In the remainder of this paper, we focus on the prob-
lem of detecting acquisition of payment card data. With-
out this data, adversaries will be unable to perform card
fraud.
2.3 Common Advice
Card skimming is a well-known crime, and advice aimed
at protecting consumers is widespread. The most com-
mon suggestions are:
1. Look for signs of a skimmer.
2. Pull on the card reader.
3. Use a smartphone app to scan for skimmers with
Bluetooth radios.
4. Use an EMV (Chip) card.
5. Use cash.
While seemingly helpful on their surface, many of
these tips offer little in terms of specific steps. Beyond
common sense, Tips 1 and 2 suggest that users know how
payment devices should look and feel.
1
Some credit and debit cards have the CVV2 printed on the face of
the card and (for cards with the code on the back) some card acceptors
allow the card to be inserted face down, allowing a camera with a view
of the card to capture the code.
2 27th USENIX Security Symposium USENIX Association



 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助 


 信息提交成功
信息提交成功