1
Belfer Center for Science and International Aairs | Harvard Kennedy School
Summary
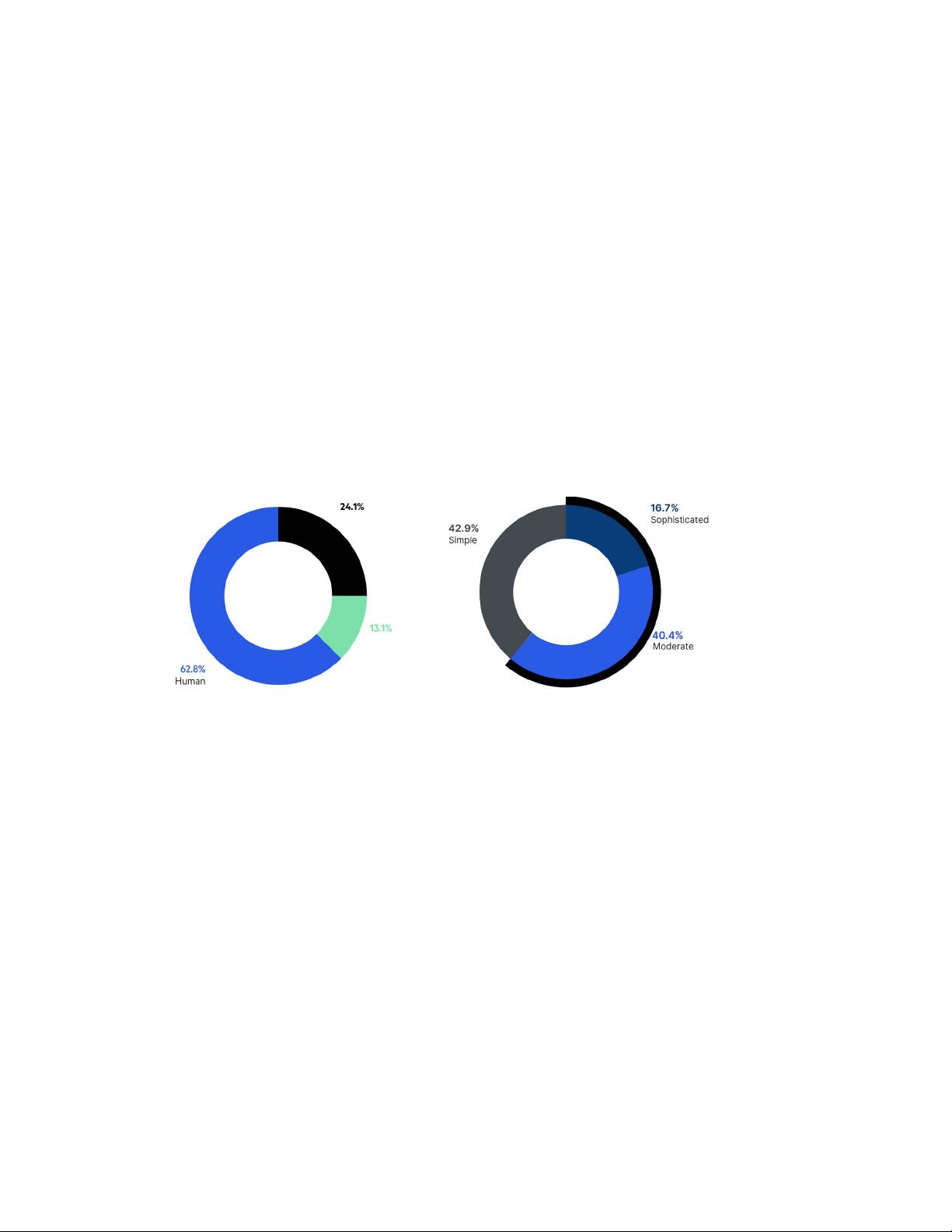
Adversarial Internet robots (botnets) represent a growing threat to
the safe use and stability of the Internet. Botnets can play a role in
launching adversary reconnaissance (scanning and phishing), inu-
ence operations (upvoting), and nancing operations (ransomware,
market manipulation, denial of service, spamming, and ad click fraud)
while obfuscating tailored tactical operations. Reducing the pres-
ence of botnets on the Internet, with the aspirational target of zero,
is a powerful vision for galvanizing policy action. Setting a global
goal, encouraging international cooperation, creating incentives for
improving networks, and supporting entities for botnet takedowns
are among several policies that could advance this goal. ese pol-
icies raise signicant questions regarding proper authorities/access
that cannot be answered in the abstract. Systems analysis has been
widely used in other domains to achieve sucient detail to enable
these questions to be dealt with in concrete terms. Defeating botnets
using an observe-pursue-counter architecture is analyzed, the tech-
nical feasibility is armed, and the authorities/access questions are
signicantly narrowed. Recommended next steps include: supporting
the international botnet takedown community, expanding network
observatories, enhancing the underlying network science at scale, con-
ducting detailed systems analysis, and developing appropriate policy
frameworks.
Physical World
Red (Adversary) Cyberspace
Blue (Friendly) Cyberspace
Gray (Neutral) Cyberspace
Public-private partnerships based on a shared
situational awareness, combined action, and
full support of governments in defense of the
private sector.
An international community that observes and
enforces norms of responsible state behavior.
30 Cyberspace Solarium Commission
STRATEGIC APPROACH: LAYERED CYBER DETERRENCE
Layered cyber deterrence is the blueprint that the
government and American public need to build bridges
across government agencies, international partners, and
most importantly the private sector in order to secure
American networks in cyberspace. It is the best way for
the government to implement new authorities and take
appropriate proportional action that builds national resil-
ience as well as disrupts, defeats, and deters active cyber
campaigns, including those targeting critical economic
and political institutions like election systems.
157
To translate layered deterrence into action requires three
lines of eort organized into six pillars and more than 75
supporting recommendations that enhance the ability
of the U.S. government to shape adversary behavior,
deny benets, and impose costs. Defend forward spans
all three lines of eort to identify, isolate, and counter
threats consistent with existing authorities and legal
frameworks.
Layered Cyber Deterrence
CURRENT STATE APPROACH PILLARS DESIRED END STATES
Adversaries are
conducting cyber
campaigns that tar-
get U.S. networks
in cyberspace and
threaten American
safety and security,
economic interests,
political institutions,
and ability to proj-
ect military power.
The U.S. gov-
ernment has the
authorities but
lacks the optimal
structure and
relationships with
the private sector
and other partners
to achieve a unity
of effort at the scale
required to defend
forward.
Shape
Behavior
Foundation:
Reform
the U.S.
Government
Structure
and
Organization
for
Cyberspace
Strengthen
Norms and Non-
military Tools
A digital environment that is safe and sta-
ble, promotes continued innovation and
economic growth, protects personal privacy,
ensures national security, and does so by
building:
• An international community that observes
and enforces norms of responsible state
behavior
• Critical elements of national power and
infrastructure that are secure, resilient,
and supported by a defensible digital
ecosystem
• Public-private partnerships based on a
shared situational awareness, combined
action, and full support of the U.S. govern-
ment in defense of the private sector
• An agile, proactive U.S. government
organized to rapidly and concurrently
employ every instrument of national power
in defense of cyberspace and to gener-
ate deterrent options tailored to each
adversary
• A cyber force equipped with the resources,
capabilities, and processes to maneuver
and rapidly engage adversaries in and
through cyberspace
Deny
Benefits
Promote National
Resilience
Reshape the
Cyber Ecosystem
toward Greater
Security
Operationalize
Cybersecurity
Collaboration
with the Private
Sector
Impose
Costs
Preserve
and Employ
the Military
Instrument of
Power
The proactive observing, pursuing, and countering of adversary operations and imposing of costs
in a day-to-day competition to disrupt and defeat ongoing malicious adversary cyber campaigns,
deter future campaigns, and reinforce favorable international norms of behavior.
Solarium Report [70]

 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助 


 信息提交成功
信息提交成功