BACHIR et al.: MAC ESSENTIALS FOR WIRELESS SENSOR NETWORKS 227
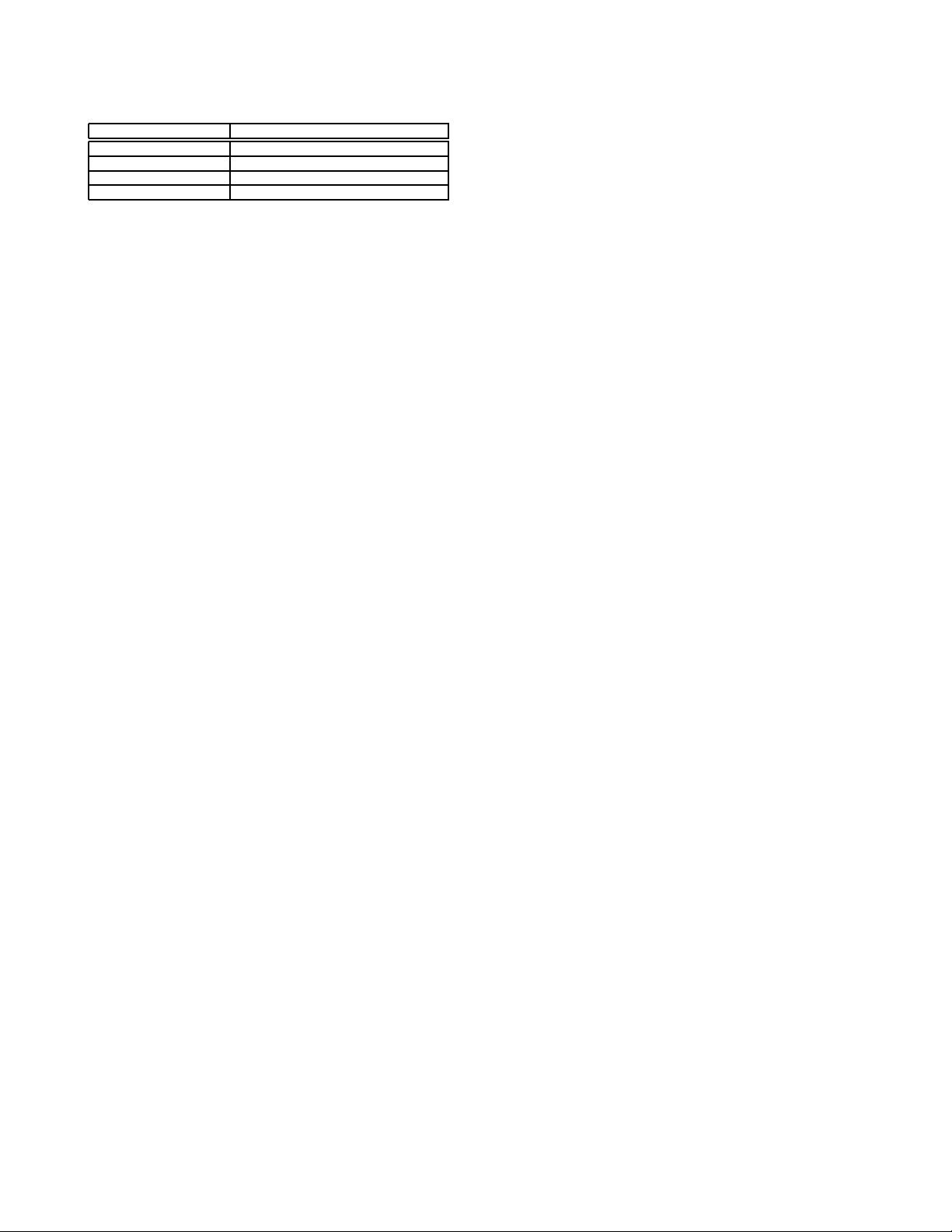
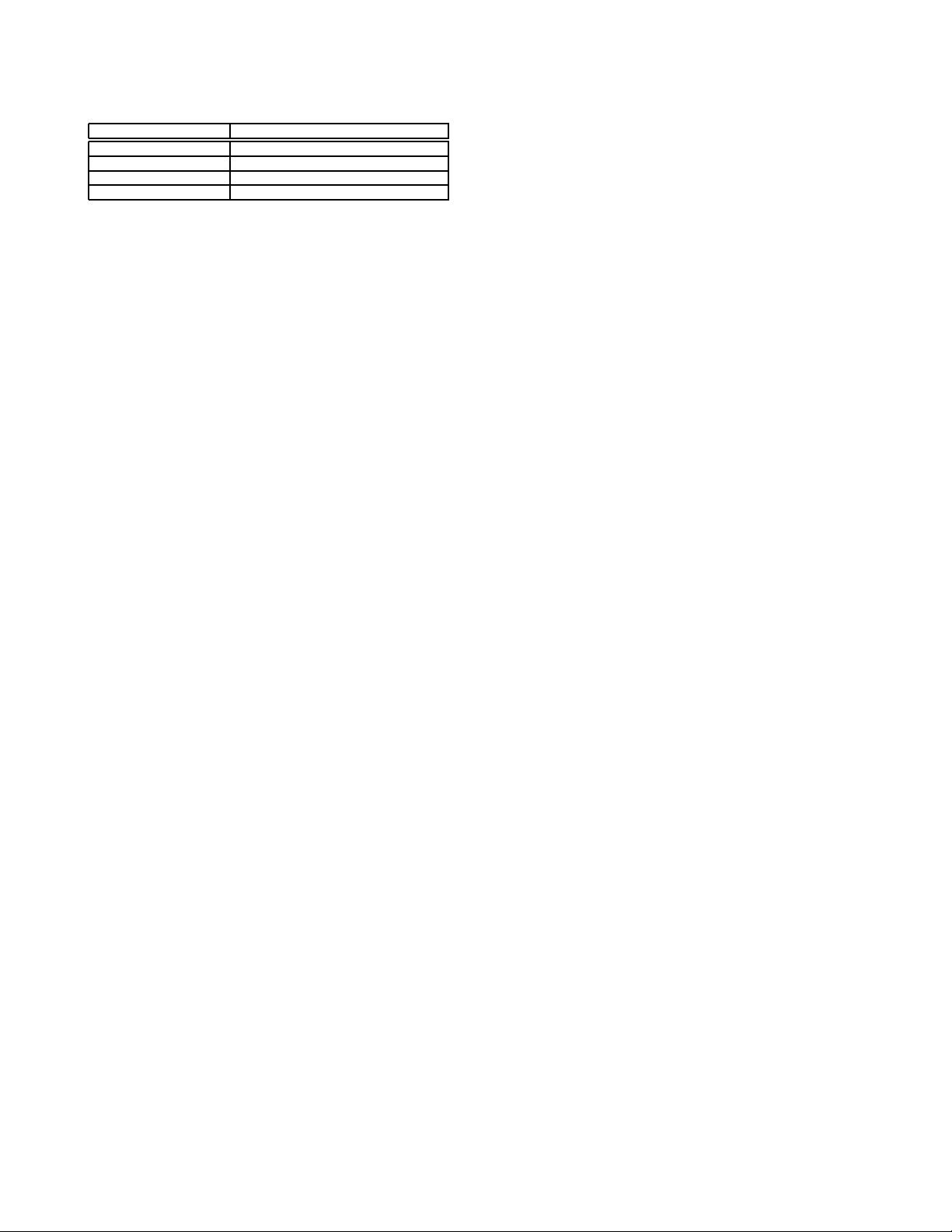
TABLE I
S
UMMARY OF MAC IMPROVEMENTS FOR CANONICAL SOLUTIONS.
Function Protocols
Reducing Collisions CSMA/CA [17], MACA [22], Sift [24]
Reducing Overhead CSMA/ARC [19]
Reducing Overhearing PAMAS [25]
Reducing Idle Listening PSM [26]
the traffic exchange. Note that the latency issue can be
alleviated because the node can switch to normal mode
when it expects high activity periods.
In multihop ad hoc networks with no infrastructure, there is
no central node being active in permanence to coordinate and
manage sleeping periods of the other nodes. This complicates
the task o f letting nodes sleep without causing deafness.
From the above discussed protocols, which have been sum-
marized in Table I, it becomes clear that WSNs require very
specific MAC protocols that ought to be designed taking their
peculiarities into account. In the reminder of the paper, we
explore the key ideas and the main energy efficient protocols
available in the literature. Since WSNs are highly a pplica-
tion tailored [7], we first dwell on Scheduled Protocols in
Section III wh ich are optimized for periodic high-load traffic
(typical to e.g. multimedia applications); second, we deal with
Protocols with Common Active Periods in Section IV that are
well suited for medium-load traffic scenarios (typical to e.g.
industrial applications); third, we discuss Preamble Sampling
Protocols that are the most convenient for rare reporting events
in Section V (typical to e.g. metering application s); and finally
we will also expose some hybrid protocols in Section VI which
combine the benefits of several protocols. Since we divert from
the typical MAC taxonomy, we also expose switching points
between these protocols according to our traffic-dependent
taxonomy in Section VI-B6.
III. S
CHEDULED PROTOCOLS
A. Basic Idea
Periodic and high-load traffic is most suitably accommo-
dated by means of reservation-based protocols, i.e. those
which build a specific schedule. Generally, in the context of
WSNs, such protocols are variants of TDMA (Time Division
Multiple Access) combined with FDMA (Frequency Division
Multiple Access) where different time slots and frequency
channels can be used by different nodes. TDMA is attractive
because - onc e the schedule is set up - there are no collisions,
no overhearing, and minimized idle listening. In addition,
TDMA offers bounded latency, fairness and good throughput
in loaded (but not saturated) traffic conditions.
The central concern of TDMA type protocols is how to set
up and maintain a specific schedule. To this end, three methods
are u sed in the context of WSNs:
• Scheduling of communication links: This fairly tra-
ditional approach sets up a unique slot dedicated to a
specific sender and specific receiver, thereby minimizing
idle listening and eliminating collisions and overhearing.
Since transmitter and receiver know exactly when to wake
up, this is the most energy efficient solution given the
schedule is set up and that packets need to be transmitted;
however, varying traffic conditions, imprecise clocks and
network dynamics require new schedules to be set up
which incurs large overheads.
• Scheduling of senders: In this approach the slot is
specified which is used by the sender which requires
all receiving nodes to listen. It hence minimizes idle
listening, eliminates collisions and r educes overheads to
a certain extend (since any changes at the receiving side
remain transparent to the established schedule); however,
overhearing remains a problem of such an approach.
A node, however, m ay minimize overhearing further
through header filtering, i.e. when the packet is destined
to another node, the receiver goes back sleeping during
that slot.
• Scheduling of receivers: Here, the receiving slots are
specified. Overhearing is elim inated, idle listening mini-
mized and overheads are reduced (since network dynam-
ics at th e transmitting side are transparent to the sched-
ule). However, collisions between various transmissions
can potentially occur if more than one transmitter wishes
to reach a specific receiver; suitable contention resolution
methods are hence needed.
The first two variants of TDMA are suited to periodic, delay
sensitive and fairly high-load traffic, the third to periodic and
medium-load traffic. Whilst many variants of above protocols
exist, such as the beacon-enabled guaranteed time slot trans-
mission during the collision free period of the IEEE 802.15.4
MAC to be exposed in Section VI, we shall discuss the
recently emerged Time Synchronized Mesh Protocol (TSMP)
[27] to exemplify its functioning.
TSMP is TDMA-based and hence requires network-wide
synchronization. Access is controlled b y means of a tunable
amount of timeslots which form a frame. The protocol is
designed such that a node can participate in multiple frames
at once allowing it to have multiple refresh rates for different
tasks. TSMP employs in addition FDMA and frequency hop-
ping, i.e. different links use differing frequency slots and the
same link hops during its life time across different frequency
slots. This yields high robustness against interference and
other channel impairments.
A traditional approach to facilitate synchron ization is bea-
coning, where longer frame lengths decrease the refresh rate
at which synchronization is performed and hence power
consumption and shorter frame lengths conversely invoke the
opposite. TSMP does refrain from doing so because it requires
long listening windows which consume power. Instead, TSMP
nodes maintain a precise sense of time and exchange only
offset information with neighbors to ensure alignment. These
offset values are exchanged during active periods together with
the usual data and acknowledgement packets hence invoking
negligible overhead. TSMP nodes are active in three states:
1) sending a packet to a neighbor; 2 ) listening for a neighbor
to talk; and 3) interfacing with an embedded hardware com-
ponent. The duration of active periods, i.e. the duty cycling,
is very flexible in TDMA; typical applications require duty
cycles of less than 1%.
When applied, the sink typically retrieves the list of nodes,
their neighbors and their requirements in terms of traffic gener-
ation. From this information, it constructs a scheduling table
Authorized licensed use limited to: Nanchang University. Downloaded on June 23,2010 at 05:15:26 UTC from IEEE Xplore. Restrictions apply.