TPM支持的可信网络通信技术规范(TNC_CESP_v1.0r14)
需积分: 1 60 浏览量
更新于2024-06-22
收藏 574KB PDF 举报
本资源为《TNC_CESP_v1.0r14.pdf》,即Trusted Network Communications (TNC) 客户端无需支持 profile 的版本1.0修订版14,发布日期为2009年5月18日。该文档由 Trusted Computing Group (TCG) 出品,旨在提供基于TPM(Trusted Platform Module)的可信网络连接技术规范。TPM 是一种高度安全的硬件组件,用于确保计算机平台的可信度,通过加密、身份验证和数据保护功能来增强系统的安全性。
该规格书中涉及的主要知识点包括:
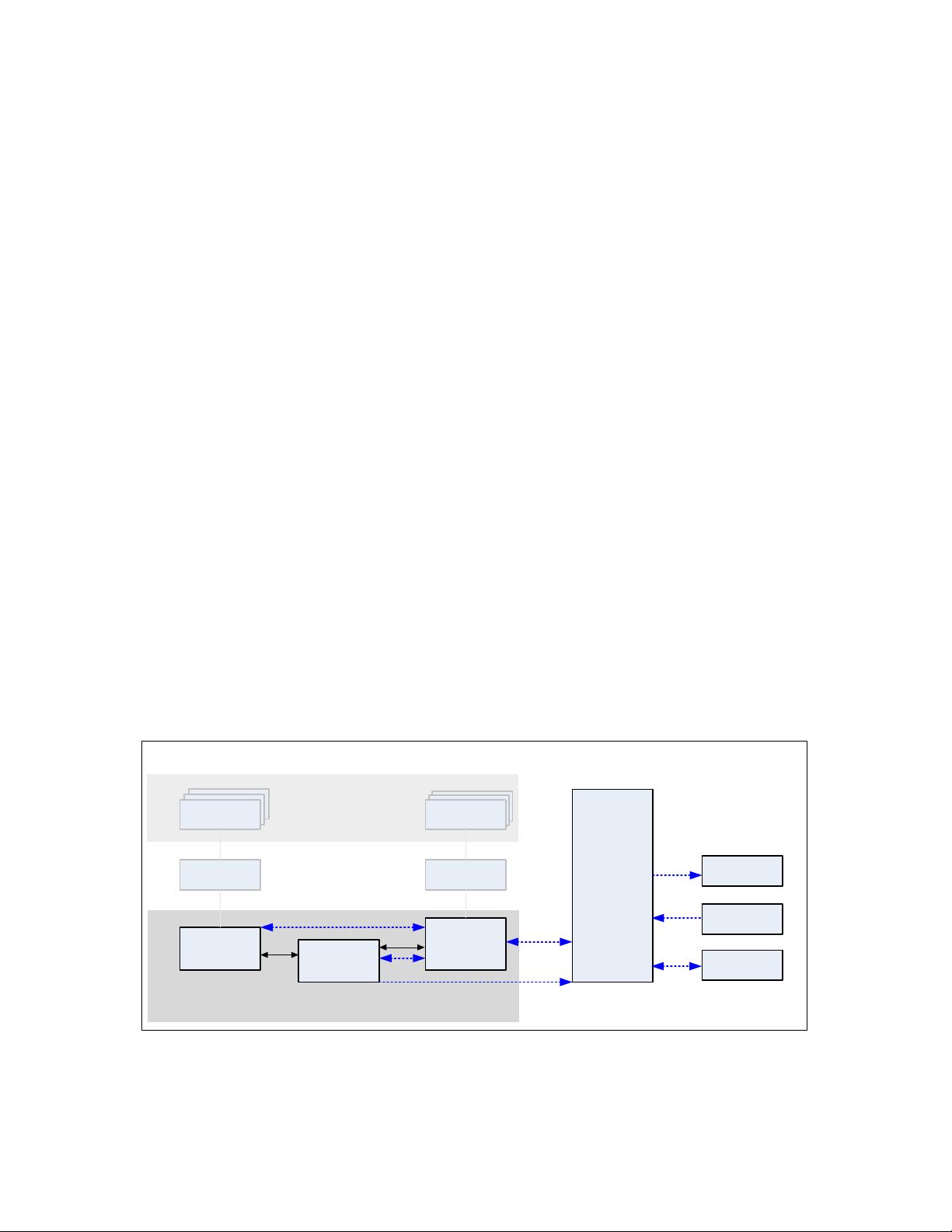
1. **TCG Trusted Network**:这是一个概念,强调了利用TPM技术来构建安全、可信的网络环境,其中所有通信和数据交换都是在保证隐私和完整性的情况下进行。
2. **Clientless Endpoint Support Profile**:这是一个针对无客户端终端设备的安全模型,意味着系统可以在没有预装特定软件或应用程序的情况下实现信任关系。这在移动设备或者轻量级设备中特别有用,它们可能无法承载完整的安全软件栈。
3. **Specification Version 1.0 Revision 14**:这是技术规范的最新版本,可能包含了对先前版本的改进、新功能添加以及对TPM在网络安全中的最佳实践更新。
4. **Copyright and Disclaimer**:文档声明版权属于TCG,且提供“原样”无保证,即不保证适合任何特定目的,包括但不限于非侵权性、适销性、无错误或符合用户预期。同时,TCG对使用规范中信息导致的任何损失或损害不负责任,包括间接或附带损害。
5. **Liability Disclaimers**:TCG明确排除了所有法律责任,包括但不限于侵犯知识产权的责任,以及因遵循规范或实施规范而产生的费用或损失,不论责任基础为何。
这份文档是关于如何在基于TPM的环境下设计和实现无客户端终端支持的可信网络通信的技术指南,适用于那些追求高安全性的网络服务提供商、设备制造商以及系统集成商,他们需要理解和遵守这些标准以确保网络连接的安全性和可靠性。
点击了解资源详情
点击了解资源详情
点击了解资源详情
2023-07-21 上传
2023-07-21 上传
2023-07-21 上传
2023-07-21 上传
2023-07-21 上传
2023-07-21 上传

书香度年华
- 粉丝: 1w+
- 资源: 385
最新资源
- Elasticsearch核心改进:实现Translog与索引线程分离
- 分享个人Vim与Git配置文件管理经验
- 文本动画新体验:textillate插件功能介绍
- Python图像处理库Pillow 2.5.2版本发布
- DeepClassifier:简化文本分类任务的深度学习库
- Java领域恩舒技术深度解析
- 渲染jquery-mentions的markdown-it-jquery-mention插件
- CompbuildREDUX:探索Minecraft的现实主义纹理包
- Nest框架的入门教程与部署指南
- Slack黑暗主题脚本教程:简易安装指南
- JavaScript开发进阶:探索develop-it-master项目
- SafeStbImageSharp:提升安全性与代码重构的图像处理库
- Python图像处理库Pillow 2.5.0版本发布
- mytest仓库功能测试与HTML实践
- MATLAB与Python对比分析——cw-09-jareod源代码探究
- KeyGenerator工具:自动化部署节点密钥生成