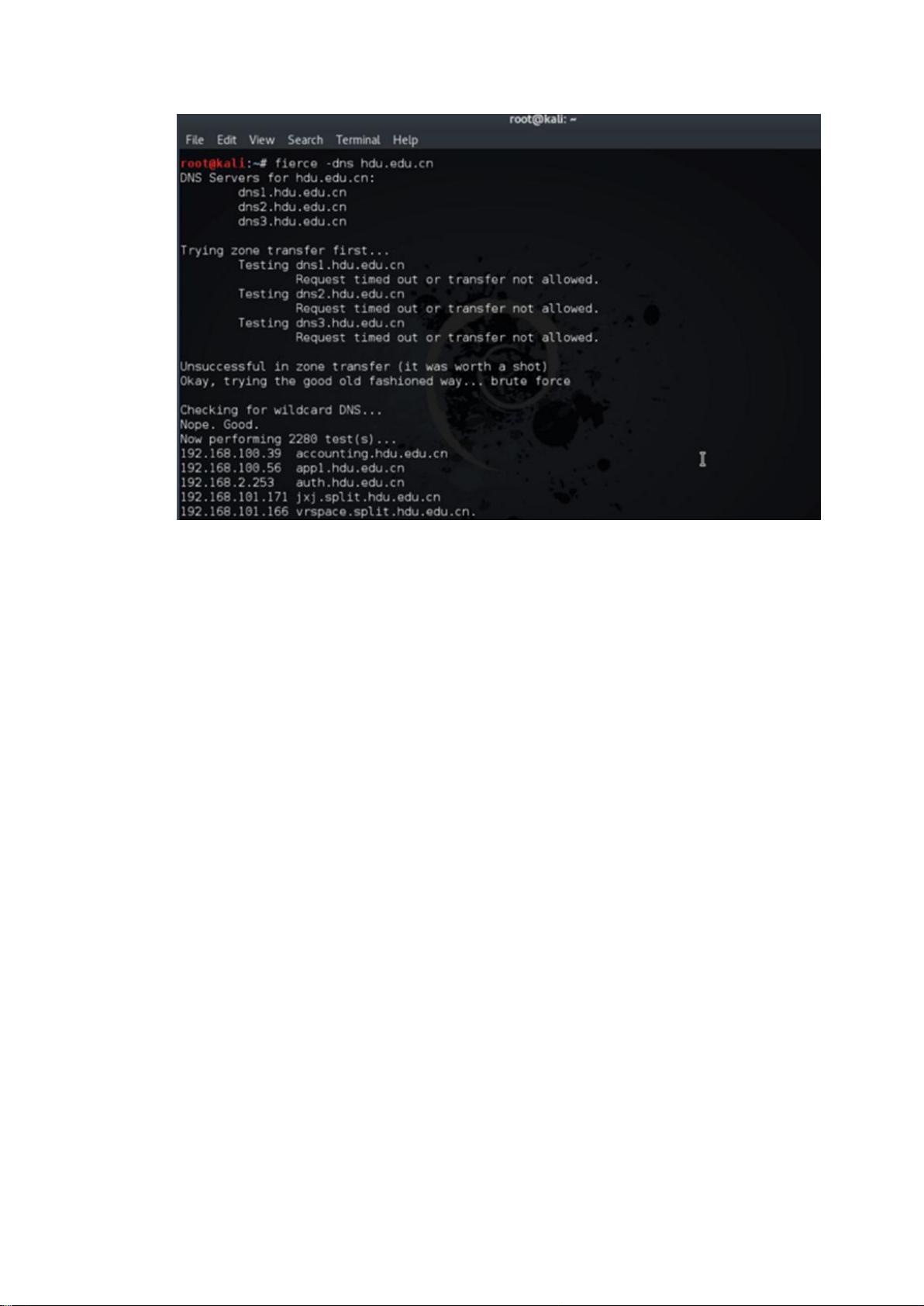
Kali Linux is a popular penetration testing and ethical hacking operating system. It is widely used by security professionals and hackers to test and secure computer systems and networks. The Kali Linux Penetration Testing Basics PDF provides an overview of the basics of penetration testing with Kali Linux, including information gathering, website and server information, Google hacking, social media, and third-party data. One of the most important stages in penetration testing is information gathering, as collecting useful information can greatly increase the success of the test. Information gathering involves analyzing the target system, scanning and detecting services, scanning for vulnerabilities, finding the target system's IP, and sometimes using social engineering techniques. Testers make every effort to collect information about the target system's configuration, security defenses, and firewall. Whois is a protocol used to query domain names for IP and owner information. It is a database used to query whether a domain name has been registered, as well as detailed information about the registered domain (such as the domain owner and registrar). DNS server queries are also important in information gathering. In addition to whois and DNS queries, the Kali Linux Penetration Testing Basics PDF covers the basics of scanning, enumeration, and vulnerability analysis. This provides a comprehensive overview of the information gathering phase in penetration testing with Kali Linux, highlighting its importance and providing practical examples of techniques and tools that can be used. Overall, the Kali Linux Penetration Testing Basics PDF serves as a valuable resource for security professionals, hackers, and anyone interested in learning about the basics of penetration testing with Kali Linux.













评论5