NSX-T与Horizon 7设计指南:构筑安全的云桌面架构
需积分: 0 15 浏览量
更新于2024-06-21
收藏 4.95MB PDF 举报
本指南是VMware NSXT End User Computing (NSX-T) 设计指南的第1.0版本,专注于NSX-T与Horizon 7.9 Data Center环境的集成设计。NSX-T是VMware的下一代软件定义网络和安全平台,而Horizon则是其统一接入管理和虚拟桌面基础设施(VDI)解决方案。该文档旨在为IT专业人士提供详细的指导,帮助他们理解如何在NSX-T环境中优化和部署Horizon服务,确保高效、安全的用户体验。
**1. 目标受众**
本指南主要针对负责设计、实施和管理NSX-T与Horizon集成的网络和安全架构的系统管理员、网络工程师和安全专家。它适合那些希望利用NSX-T的强大功能来提升企业网络性能、微分段安全以及优化VDI环境的团队。
**2. 引言**
- **Horizon 7参考架构**:指南首先概述了Horizon 7的架构,强调其组件和部署模型,以便读者理解基础环境。
- **NSX-T设计指南**:接着介绍了NSX-T的核心原则和设计思想,确保读者对其在整体架构中的角色有清晰的认识。
**3. NSX-T与Horizon架构及组件**
- **NSX-T组件定义**:这部分详细解释了NSX-T的架构,包括控制器、分布式防火墙、逻辑网关等,以及它们如何协同工作以支持Horizon。
- **Horizon核心组件定义**:讲解了Horizon的Pod和Block结构,以及它们在NSX-T网络中的定位。
**4. NSX-T与Horizon用例**
- 通过实际场景,展示了NSX-T如何应用于不同类型的VDI场景,如远程办公、混合云环境等,以满足多样化的需求。
**5. NSX-T对Horizon的功能支持**
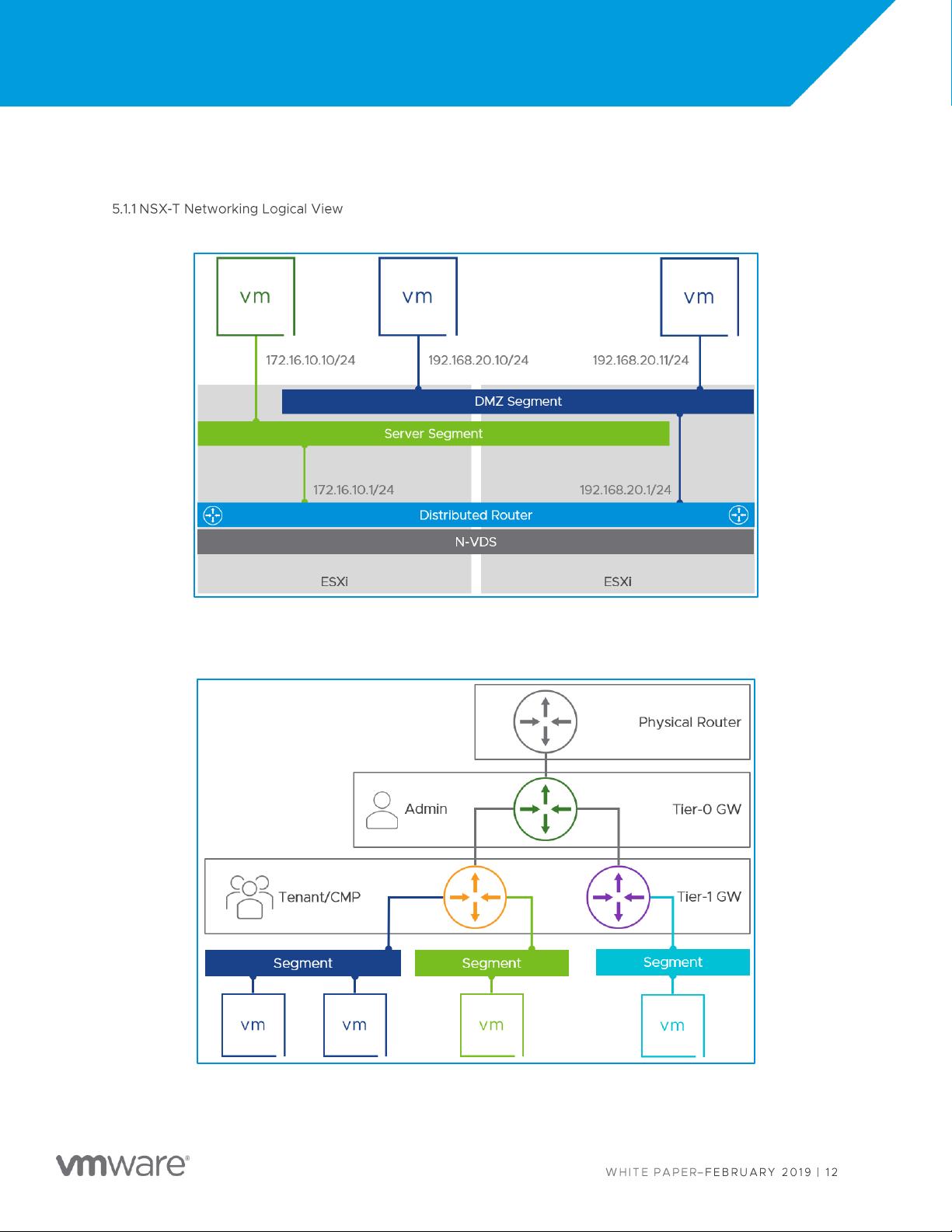
- **虚拟网络**:NSX-T提供了灵活的虚拟网络解决方案,包括逻辑视图的设计,确保桌面流量的安全和性能。
- **安全**:
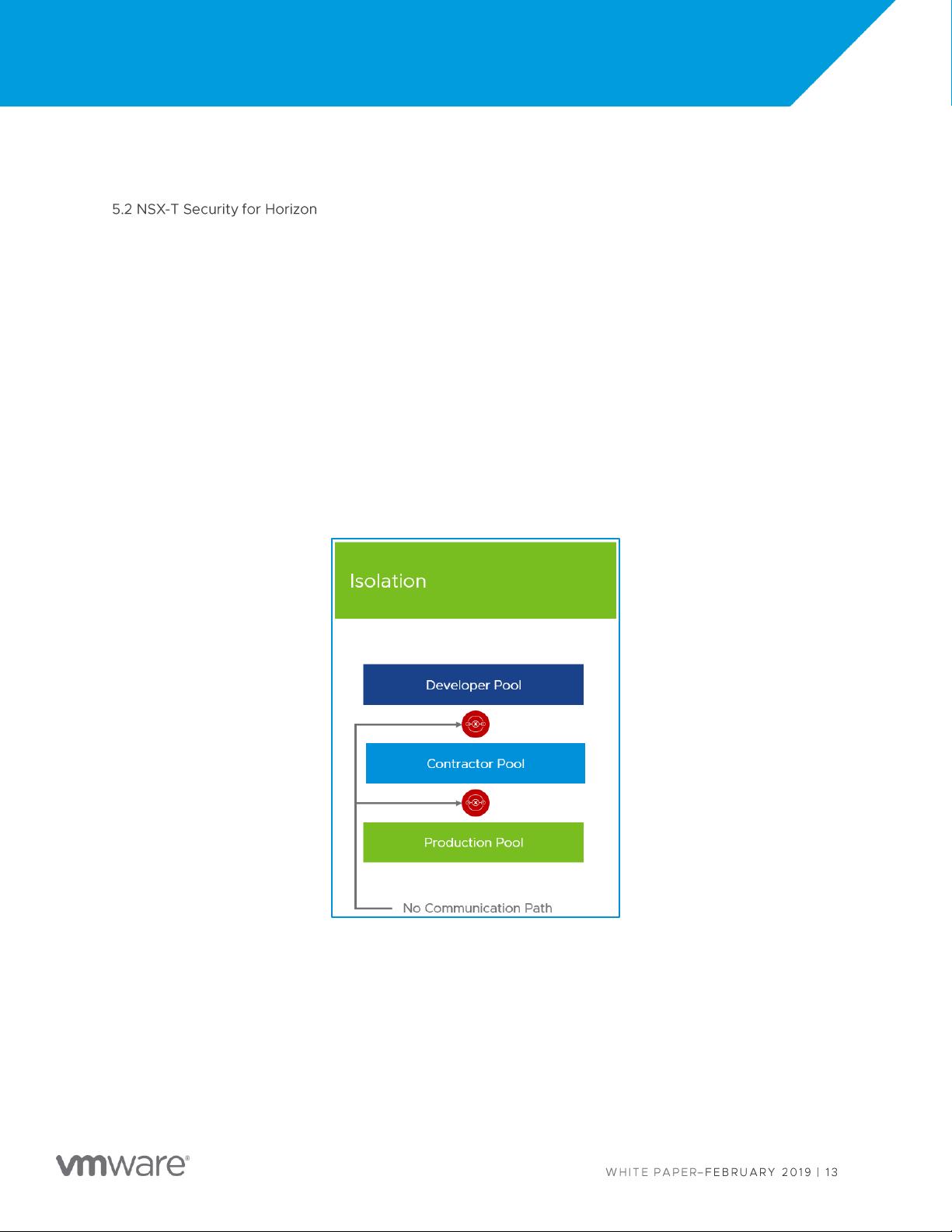
- **微分段**:Context Micro-segmentation被用来加强虚拟桌面之间的隔离和安全性。
- **分布式防火墙**:包括策略定义、连接策略和执行机制,确保细粒度的安全控制。
- **身份防火墙**:基于用户和组的身份进行访问控制。
- **安全消费**:指南说明如何有效地利用NSX-T的安全功能来满足企业安全策略。
- **边缘服务**:NSX-T Gateway Routing和负载均衡技术在提供高速、可靠的服务时发挥关键作用。
**6. NSX-T边缘和合作伙伴服务**
这部分深入探讨了NSX-T如何与其他服务和外部合作伙伴集成,以实现无缝的网络和安全扩展。
NSXT-EUC-DESIGN-GUIDE-v1.0提供了全面的指导,让IT团队能够根据VMware NSX-T和Horizon 7.9的特性,设计出适应现代企业需求的高效、安全的网络架构。无论是网络配置、安全策略还是服务优化,这份指南都是不可或缺的参考资料。
2022-02-17 上传
2021-03-31 上传
2021-02-05 上传
2021-03-08 上传
2022-01-06 上传
2021-02-04 上传
2022-05-15 上传
2022-05-15 上传
2020-11-20 上传
routetable
- 粉丝: 0
- 资源: 6
最新资源
- 全国江河水系图层shp文件包下载
- 点云二值化测试数据集的详细解读
- JDiskCat:跨平台开源磁盘目录工具
- 加密FS模块:实现动态文件加密的Node.js包
- 宠物小精灵记忆配对游戏:强化你的命名记忆
- React入门教程:创建React应用与脚本使用指南
- Linux和Unix文件标记解决方案:贝岭的matlab代码
- Unity射击游戏UI套件:支持C#与多种屏幕布局
- MapboxGL Draw自定义模式:高效切割多边形方法
- C语言课程设计:计算机程序编辑语言的应用与优势
- 吴恩达课程手写实现Python优化器和网络模型
- PFT_2019项目:ft_printf测试器的新版测试规范
- MySQL数据库备份Shell脚本使用指南
- Ohbug扩展实现屏幕录像功能
- Ember CLI 插件:ember-cli-i18n-lazy-lookup 实现高效国际化
- Wireshark网络调试工具:中文支持的网口发包与分析