Multi-)actor $uthentication 0odeling
LiborDostálek
Department of Applied Informatics,
Faculty of Science, University of South Bohemia,
Ceske Budejovice, Czech Republic,
dostalek@prf.jcu.cz
Abstract—The work defines a multi-factor
authentication model in case the application supports
multiple authentication factors. The aim of this modeling
is to find acceptable authentication methods sufficient to
access specifically qualified information.
The core of the proposed model is risk-based
authentication. Results of simulations of some key
scenarios often used in practice are also presented.
Keywords—authentication, multifactor authentication,
risk-based authentication, omnifactor authentication, fraud
detection system, password, digital fingerprint.
I. I
NTRODUCTION
The principle of authentication fall into one of three well
known authentication factors: knowledge, ownership and
inheritance.
More recently, authentication by external providers is
being as well used (e.g. Google). External authentication often
uses OAuth 2.0 and OpenID Connect protocols. In the case of
this external authentication, we will not investigate what
factors it is based on. We will look at external authentication
as a black box, and for the purposes of the model described
below we will consider it as a separate forth authentication
factor.
Why compare authentication methods?
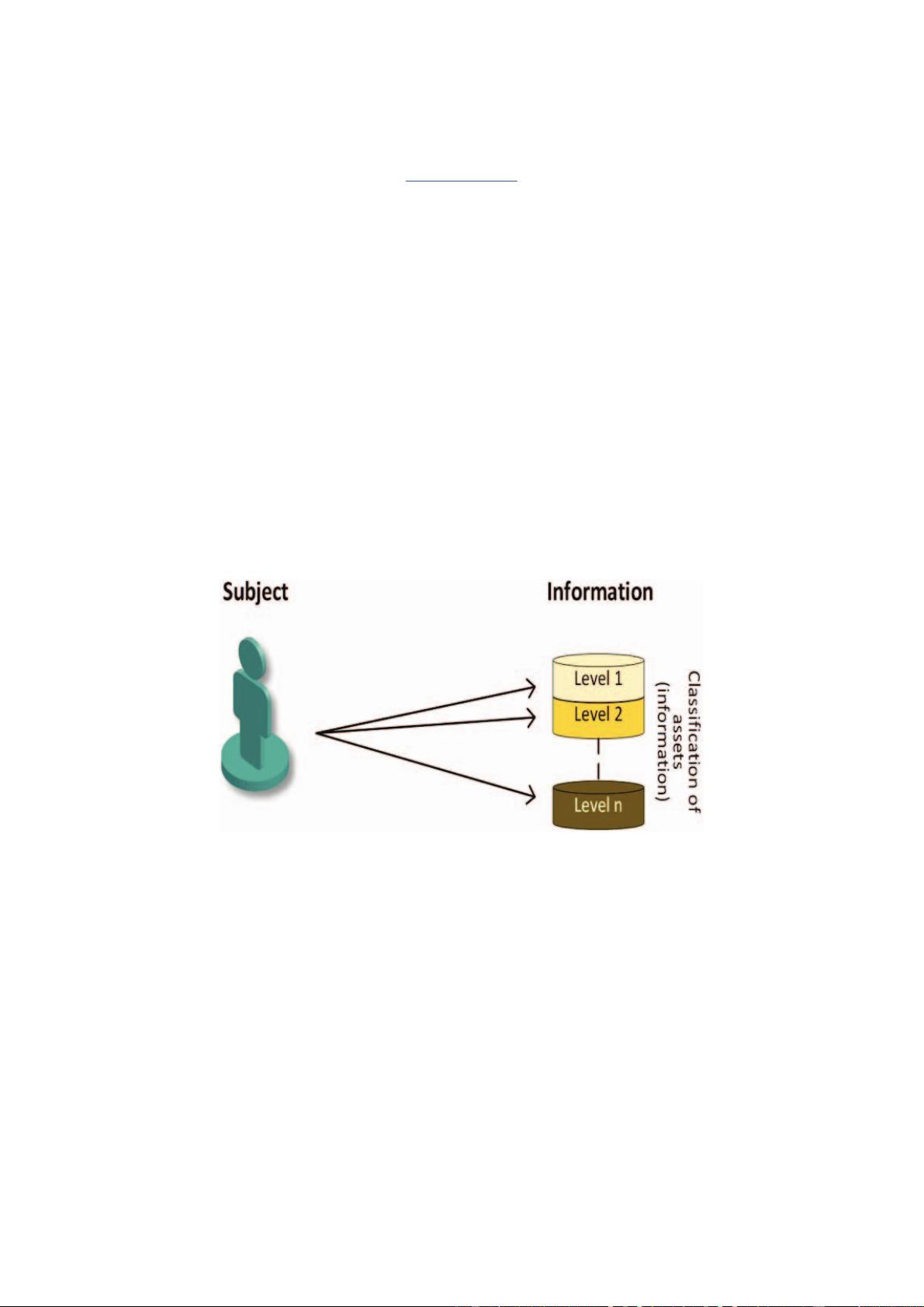
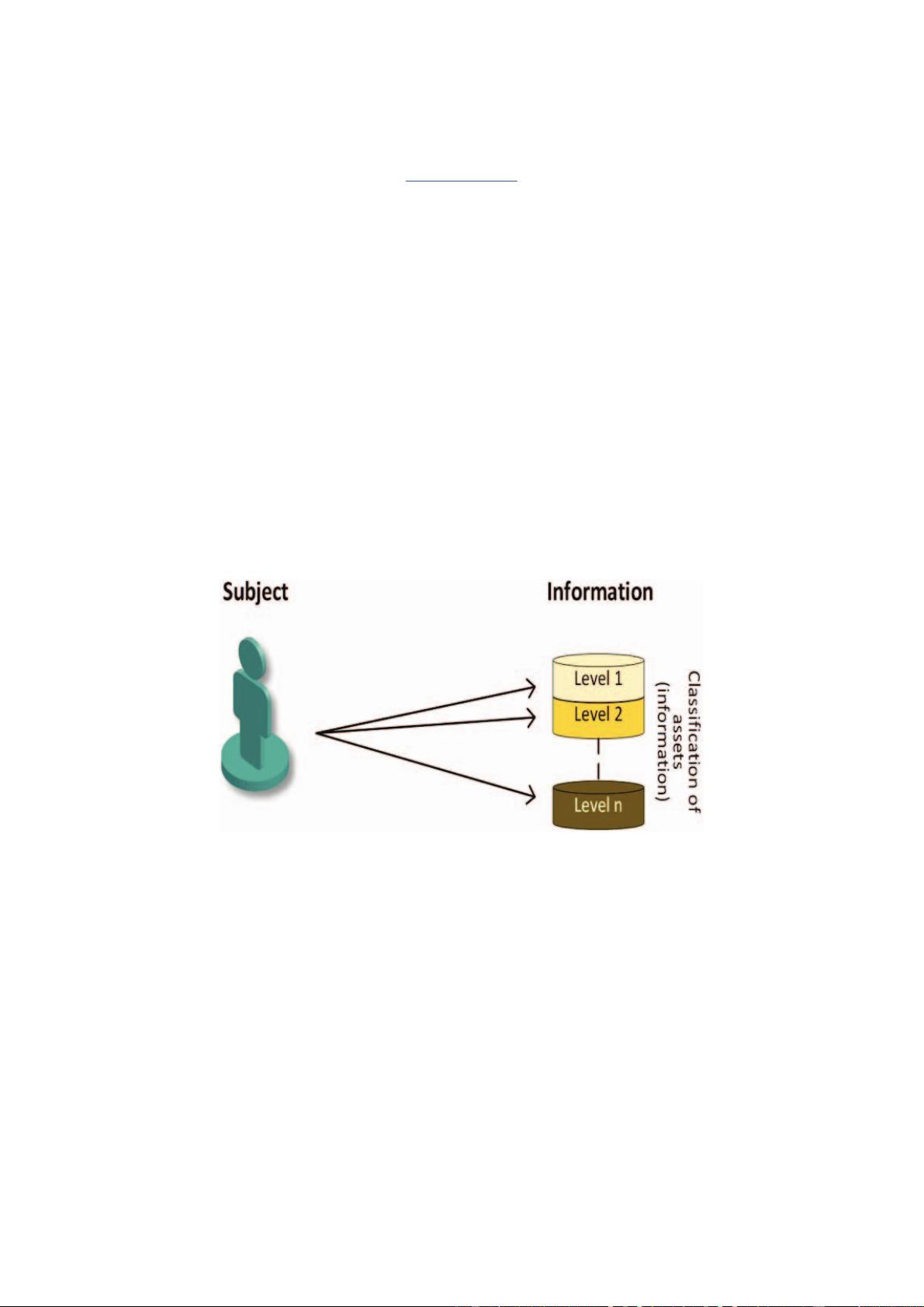
The subject uses authentication to gain access to assets (e.g.
information assets) that will be classified to levels 1 to ݊ for
the needs of our model. Assets can be classified, for example,
by the asset's carrying amount. However, it is more likely to
be based on the risk analysis mentioned below. The question
is, what authentication method is sufficient to access the
classification level information ݅, where ݅ =1,…݊. The
solution described below is to use the Risk Based
Authentication principle. The work introduces an
authentication model that determines whether the
authentication is sufficient for a specified level of
classification based on the input parameters.
Fig. 1. An subject wants to access information (assets) classified to level information ݅, where ݅ =1,…݊
II. BACKGROUND AND RELATED WORK
Device Fingerprinting
Device Fingerprinting means collecting information about
a computing system and its communication that may lead to
device identification or at least partial identification. In
practice, however, the device fingerprint typically detects a
user communicating from a specific device. I.e. gathering
information not only about the hardware and software
installed on the device, but also about its user configuration
and, if applicable, the behavior of a particular user.
The server can collect a wide range of client
communication information based on various methods that
can characterize a particular device, and therefore assume that
the device is being used by a specific user. Individual methods
are referred to as device fingerprinting vectors. Such
fingerprinting vectors can be, for example, information about
the device SW, operating system version including its version,
or information provided by the browser (e.g., cookie) or the
time zone set, etc. E.g. [1] defines 29 fingerprinting vectors
that classify into four categories: Browser provided
information, Inference based on device behavior, Extensions
and plugins and Network and protocol techniques. It also
states five basic types of attacks on device fingerprinting. The
article [2] uses fingerprinting vectors based on motion
Sensors. There are a number of such articles. Their deficiency
is that they identify individual authentication factors, but they
do not specify to qualify their strength somehow in order to be
somehow comparable.
Fraud Detection Systems (FDS)
The FDS principle is the opposite of authentication. FDS
calculates the likelihood of a successful attack against
authentication. It's not a whole new approach. Patent [3] has
already applied this idea to Internet applications.
978-1-7281-0450-8/19/$31.00 ©2019 IEEE
4
43
Authorized licensed use limited to: Civil Aviation University of China. Downloaded on March 02,2021 at 15:26:36 UTC from IEEE Xplore. Restrictions apply.
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助 


 信息提交成功
信息提交成功