168
is noted that some of the operations involve malicious tam-
pering, while some do not change the contents of the image,
e.g., color and contrast adjustment, etc. However, some op-
erations may be confusing. Take double JPEG compression,
for example. Double JPEG-compressed images often result
from forgeries when a part of the original image is replaced
by another part from the same (region-duplication) or an-
other (splicing) image and then resaved. On the other hand,
a user may resave a high-quality JPEG image to a lower-
quality one to save storage space. Therefore, detection of
image alteration does not necessarily prove malicious tam-
pering in some situations. But it can make us doubt about
the contents of the image and help us with further analysis.
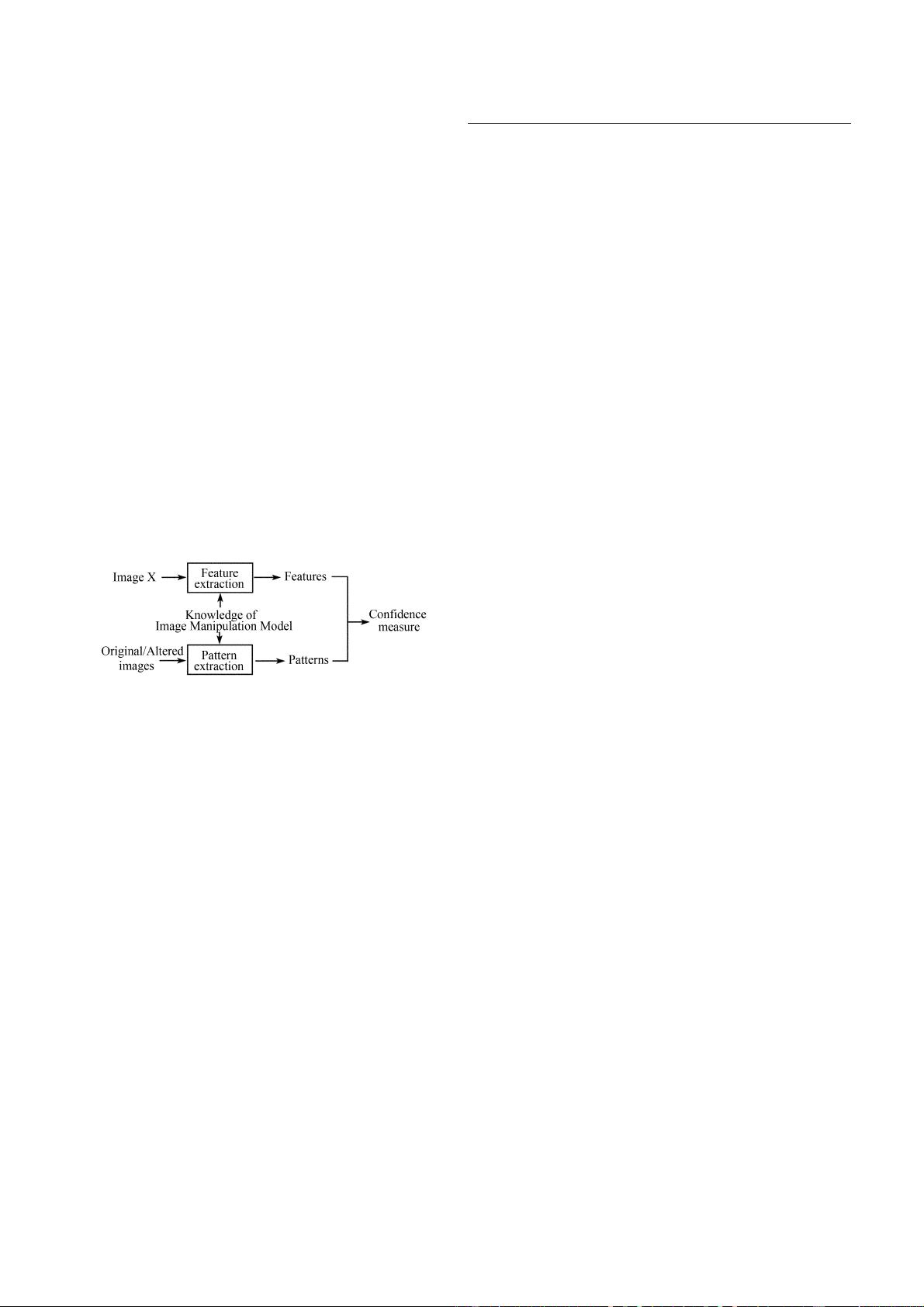
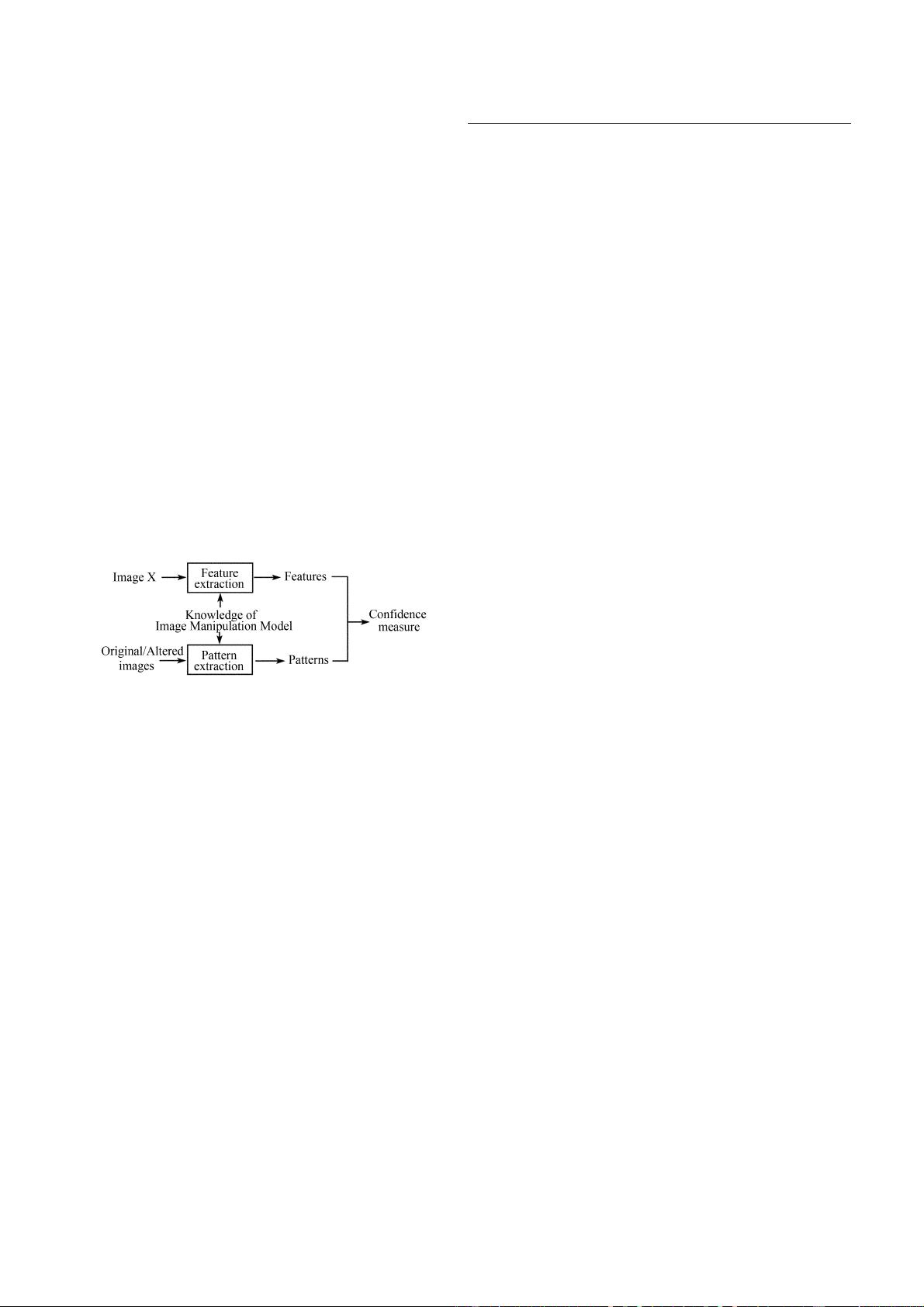
Figure 4 shows the generic image alteration detection
scheme. The test image X may be an original image, or may
be altered by a certain operation. Similarly as shown in Fig.3,
we first extract the features from X and obtain the origi-
nal/altered patterns mainly using the knowledge of the im-
age manipulation model, or sometimes combining with the
statistical characteristic in nature scenes, and the image ac-
quisition model, etc. Then we compare the distance between
the features and the patterns to decide whether or not image
X has been altered.
Fig. 4 Generic image alteration detection
In brief, comparing with signature-based and watermark-
based methods, passive technology need not use any extra
embedded information in advance. We can identify the
source or detect the alteration of the image just by using the
patterns of the digital images themselves. From another
viewpoint, the images have some inherent “watermarks”
(patterns). The “watermarks” are introduced not by our in-
trusive operations, but by the various imaging devices or
constrained by some statistical characteristics in the nature
scenes. The “watermarks” would be altered after some
post-processing. These different “watermarks” can be used
as evidence for image forensics.
In most cases, passive forensics can be converted to a
problem of pattern recognition. The solution to the problem
is finding the different patterns according to the knowledge
from various imaging devices or the manipulations or the
nature scene constraints, etc. The selected patterns with
distinguishing ability are crucial for this new technology.
In the following section, we will give a detailed overview
of some prior typical works in this new area, and show
which exact inherent patterns can be applied to digital im-
age forensics.
3 Techniques of passive forensics
As mentioned above, image-source identification and im-
age-alternation detection are the two main issues in passive
forensics technology. In this section, we will discuss these
two issues.
3.1 Identification of image source
Digital images can be captured by various imaging devices
such as digital cameras, scanners, and so on. These imaging
devices are available to our average users. In many applica-
tions, we must deal with problems about the source of the
digital images. In a court case involving child pornography,
for example, if a suspect camera has been found, is it possi-
ble to determine whether the images have been captured by
the same camera? In other cases, images can also be gener-
ated entirely by computer. As computer graphics technology
progresses, it becomes difficult to distinguish by sight the
photographic images from the computer-generated images.
Recently, some digital forgeries mixing the real scene and
computer-generated virtual scene together have been re-
ported. Is it possible to identify and distinguish these two
kinds of images?
3.1.1 Identification of digital camera
High-resolution and low-cost digital cameras have been
rapidly replacing the typical film cameras. Now, most im-
ages in our daily life are acquired by various brands of digi-
tal cameras, such as Canon, Nikon, Sony, Olympus, etc. One
of the main problems related to source identification is the
classification of the different camera models or individuals
for a given image.
The most straightforward solution for camera identi fica-
tion is to check the EXIF (Exchangeable Image File, most
digital cameras now use the EXIF format [8]) header of the
output image (Raw, Tiff or JPEG format file, and most digi-
tal cameras export images in the JPEG format). Some set-
tings of an image are stored in the headers, and the settings
are constrained by a given camera, such as the manufacturer,
the model of the camera, image size, exposure time, and the
quantization matrix used in JPEG compression [9], etc. If
the given image settings are out of the range of the given
camera, it can be concluded that the image did not come
from the camera or it was not the original one at least.
However, we cannot distinguish among the cameras of the
same or similar model whose images contain the same
header information. Furthermore, the header information can
be easily replaced or made consistent by JPEG recompres-
sion or other operations. Can we find other features that
cannot be easily removed by average users? In the following,
we describe briefly the operations inside a typical digital
camera first, and then analyze which knowledge can be used
as reliable evidence for camera identification.
Figure 5 shows the operations inside a typical digital
camera. The light coming from the scene passes through the