没有合适的资源?快使用搜索试试~ 我知道了~
首页IBM DB2数据库证考试题库C2090-611
资源详情
资源评论
资源推荐

The safer , easier way to help you pass any IT exams.
1 / 28
Exam
: C2090-611
Title :
Version : V8.02
DB2 10.1 DBA for Linux,
UNIX, and Windows

The safer , easier way to help you pass any IT exams.
2 / 28
1.Due to a hardware failure, it appears that there may be some corruption in database DB_1 as DB2 is
reporting a "bad page". DB2DART is performed for the entire database and it appears that several bad
pages were detected in table space TBSP_1.
What command can be used to recover the database and repair the corruption in table space TBSP_1?
A. RESTART DATABASE
B. RECOVER DATABASE
C. RESTORE TABLESPACE
D. ROLLFORWARD DATABASE
Answer: B
2.If a single node database is actively being used by applications when a power failure occurs, what
method is used to bring the database back to a consistent state once power has been restored.?
A. Crash recovery
B. Version recovery
C. Disaster recovery
D. Roll-forward recovery
Answer: A
3.You have an High Availability and Disaster Recovery (HADR) environment set up and you want to read
from the standby database. What must you do?
A. Assign the value ON to the DB2_HADR_ROS registry variable.
B. Assign the value ON to the DB2_HADR_SNAP registry variable.
C. Execute the STOP HADR command to temporarily break the HADR connection to the standby.
D. Execute the TAKEOVER HADR command to instruct the standby database to takeover as the new
primary database.
Answer: A
4.Which command can be used to restore a corrupted database using only the recovery history file?
A. RESTART DATABASE
B. RECOVER DATABASE
C. RESTORE DATABASE
D. ROLLFORWARD DATABASE
Answer: B
5.What is the correct procedure for recovering a dropped table when DROPPED TABLE RECOVERY has
been enabled and the database must remain online?
A. Run the RECOVER DATABASE command with the RECOVER DROPPED TABLE option to restore the
database and recover the droppedtable.
B. Run the RECOVER DATABASE command with the RECOVER DROPPED TABLE option to restore the
appropriate table space and recover thedropped table.
C. Restore the database from a backup image that was taken before the table was dropped; run the
ROLLFORWARD DATABASE command withthe RECOVER DROPPED TABLE option to restore the
database and recover the dropped table.
D. Restore the appropriate table space from a backup image that was taken before the table was dropped;

The safer , easier way to help you pass any IT exams.
3 / 28
run the ROLLFORWARD DATABASEcommand with the RECOVER DROPPED TABLE option to restore
the appropriate table space and recover the dropped table.
Answer: D
6.Which command will define the alternate diagnostic data directory path as /db2data/db2dump2?
A. db2set ALT_DIAGPATH=/db2data/db2dump2
B. db2set SECONDARY_DIAGPATH=/db2data/db2dump2
C. UPDATE DBM CFG USING ALT_DIAGPATH /db2data/db2dump2
D. UPDATE DBM CFG USING SECONDARY_DIAGPATH /db2data/db2dump2
Answer: C
7.What is the MAX_LOG database configuration parameter used for?
A. To limit how many log files a single transaction can span.
B. To limit the percentage of primary log space a running transaction can consume.
C. To limit the total number of primary and secondary log files a database can consume.
D. To limit the total number of secondary log files a transaction can consume before infinite logging is
enabled.
Answer: B
8.What unit of measurement is used to represent the cumulative total cost of a node in a Visual Explain
access plan diagram?
A. CPU cycles
B. Elapsed time, in milliseconds
C. Processing instructions performed
D. Timerons
Answer: D
9.In IBM Data Studio, where can you schedule script-based jobs?
A. Job Console
B. Job Manager
C. Task Manager
D. Utilities Console
Answer: B
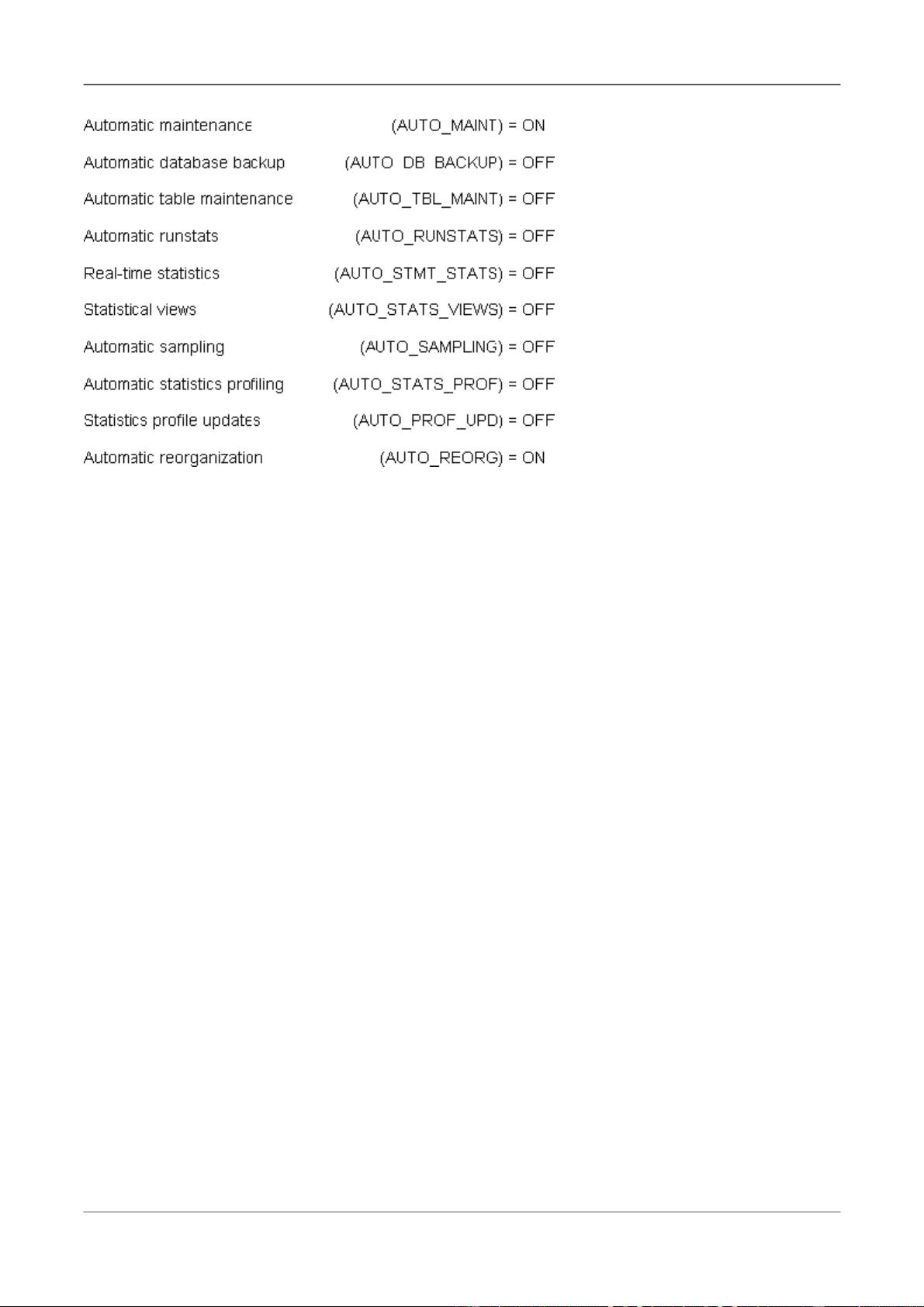
10.The values of the automatic maintenance database configuration parameters for a database named
SAMPLE are as follows:
The safer , easier way to help you pass any IT exams.
4 / 28
What commands must be run to enable real-time statistics collection on the SAMPLE database?
A. UPDATE DB CFG FOR sample USING AUTO_RUNSTATS ON; UPDATE DB CFG FOR sample
USING AUTO_STMT_STATS ON;
B. UPDATE DB CFG FOR sample USING AUTO_TBL_MAINT ON; UPDATE DB CFG FOR sample
USING AUTO_RUNSTATS ON; UPDATE DB CFG FOR sample USING AUTO_STMT_STATS ON;
C. UPDATE DB CFG FOR sample USING AUTO_TBL_MAINT ON; UPDATE DB CFG FOR sample
USING AUTO_RUNSTATS ON; UPDATE DB CFG FOR sample USING AUTO_STATS_VIEWS ON;
D. UPDATE DB CFG FOR sample USING AUTO_RUNSTATS ON; UPDATE DB CFG FOR sample
USING AUTO_STATS_VIEWS ON;
Answer: B
11.If the current value for self-tuning memory is: Self Tuning Memory (SELF_TUNING_MEM) = ON
(Inactive)
Which statement is true?
A. Self-tuning is occurring only on the instance memory area.
B. The memory tuner is actively tuning the memory on the system.
C. Self-tuning is not occurring because it is waiting for the database to be recycled.
D. Self-tuning is not occurring because there are less than two memory consumers enabled.
Answer: D
12.What are two types of security label components that can be used with Label-Based Access Control
(LBAC)? (Choose two).
A. Set
B. Tree
C. Group
D. Range
E. Hierarchy
Answer: A,B
The safer , easier way to help you pass any IT exams.
5 / 28
13.Where are column mask definitions stored?
A. In the table definition
B. In the system catalog
C. In the table space metadata
D. In the database configuration file
Answer: B
14.Which statement is correct when describing trusted contexts?
A. A trusted context defines a trust relationship for a connection between the database and an external
entity.
B. A trusted context promotes the authorization level of the connection initiator and grants them DBADM
authority.
C. A trusted context defines a trust relationship between a user and a table allowing that user additional
capabilities.
D. A trusted context gives the database connection the ability to bypass auditing since authentication has
already occurred.
Answer: A
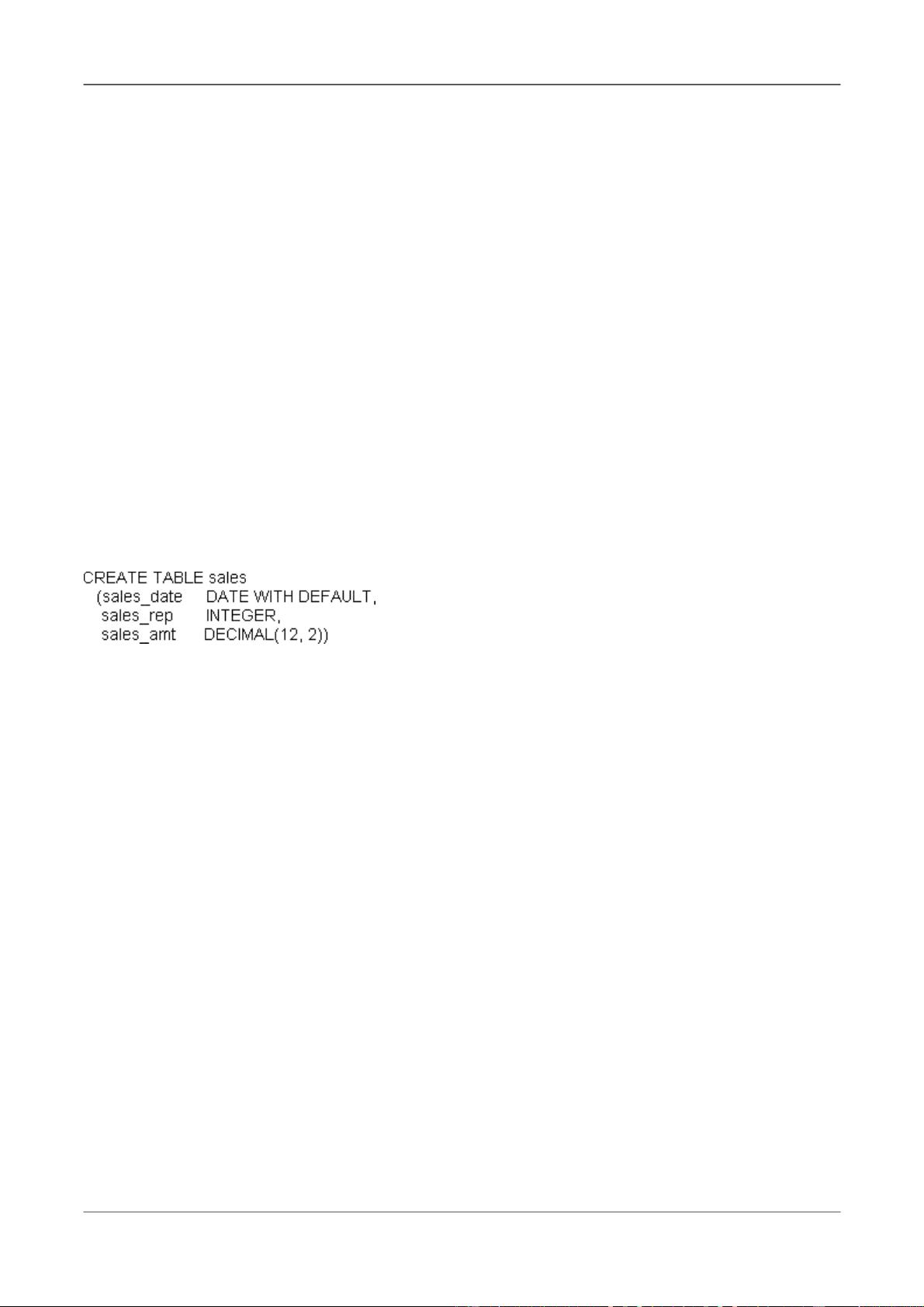
15.A table named SALES was created as follows:
If management wants to use Label-Based Access Control (LBAC) to protect individual rows in the SALES
table, and the security policy needed (SEC_POLICY) has already been created, what must be done to
protect the table as desired?
A. Associate the SEC_POLICY security policy with the SALES table.
B. Add a column with the DB2SECURITYLABEL data type to the SALES table.
C. Add a column with the DB2SECURITYLABEL data type to the SALES table and then associate the
SEC_POLICY security policy with the table.
D. Add a SECURED WITH clause to every column in the SALES table and then associate the
SEC_POLICY security policy with the SALES table.
Answer: C
16.Which authorities can be audited with the AUDIT statement?
A. SECADM, DBADM, SYSMAINT, and SYSCTRL can be audited, but SYSADM cannot.
B. SYSADM, DBADM, SYSMAINT, and SYSCTRL can be audited, but SECADM cannot.
C. SYSADM, SECADM, DBADM, SQLADM, ACCESSCTRL, and DATAACCESS can be audited.
D. DBADM, SYSMAINT, ACCESSCTRL, and DATAACCESS can be audited, but SYSADM and SECADM
cannot.
Answer: C
17.Which authority is required to revoke SECADM authority?
A. DBADM
B. SECADM
剩余27页未读,继续阅读
「已注销」
- 粉丝: 1
- 资源: 2
上传资源 快速赚钱
 我的内容管理
收起
我的内容管理
收起
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

会员权益专享
最新资源
- c++校园超市商品信息管理系统课程设计说明书(含源代码) (2).pdf
- 建筑供配电系统相关课件.pptx
- 企业管理规章制度及管理模式.doc
- vb打开摄像头.doc
- 云计算-可信计算中认证协议改进方案.pdf
- [详细完整版]单片机编程4.ppt
- c语言常用算法.pdf
- c++经典程序代码大全.pdf
- 单片机数字时钟资料.doc
- 11项目管理前沿1.0.pptx
- 基于ssm的“魅力”繁峙宣传网站的设计与实现论文.doc
- 智慧交通综合解决方案.pptx
- 建筑防潮设计-PowerPointPresentati.pptx
- SPC统计过程控制程序.pptx
- SPC统计方法基础知识.pptx
- MW全能培训汽轮机调节保安系统PPT教学课件.pptx
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
评论0