没有合适的资源?快使用搜索试试~ 我知道了~
首页Wi-Fi Simple Configuration (WPS) Technical Specification v2.0.5
资源详情
资源评论
资源推荐

© 2014 Wi-Fi Alliance. All Rights Reserved.
Used with the permission of Wi-Fi Alliance under the terms as stated in this document.
Wi-Fi Simple Configuration
Technical Specification
Version 2.0.5
This document contains a specification for easy, secure setup and introduction of devices into WPA2-
enabled 802.11 networks. It is intended to meet the requirements determined by the Wi-Fi Protected
Setup working group in Wi-Fi Alliance.
WI-FI ALLIANCE PROPRIETARY – SUBJECT TO CHANGE WITHOUT NOTICE
This document may be used with the permission of Wi-Fi Alliance under the terms set forth herein.
By your use of the document, you are agreeing to these terms. Unless this document is clearly designated as an approved
specification, this document is a work in process and is not an approved Wi-Fi Alliance specification. This document is subject to
revision or removal at any time without notice. Information contained in this document may be used at your sole risk. Wi-Fi Alliance
assumes no responsibility for errors or omissions in this document. This copyright permission does not constitute an endorsement of
the products or services. Wi-Fi Alliance trademarks and certification marks may not be used unless specifically allowed by Wi-Fi
Alliance.
Wi-Fi Alliance has not conducted an independent intellectual property rights ("IPR") review of this document and the information
contained herein, and makes no representations or warranties regarding IPR, including without limitation patents, copyrights or trade
secret rights. This document may contain inventions for which you must obtain licenses from third parties before making, using or
selling the inventions.
Wi-Fi Alliance owns the copyright in this document and reserves all rights therein. A user of this document may duplicate and
distribute copies of the document in connection with the authorized uses described herein, provided any duplication in whole or in
part includes the copyright notice and the disclaimer text set forth herein. Unless prior written permission has been received from
Wi-Fi Alliance, any other use of this document and all other duplication and distribution of this document are prohibited.
Unauthorized use, duplication, or distribution is an infringement of Wi-Fi Alliance’s copyright.
NO REPRESENTATIONS OR WARRANTIES (WHETHER EXPRESS OR IMPLIED) ARE MADE BY WI-FI ALLIANCE AND WI-FI
ALLIANCE IS NOT LIABLE FOR AND HEREBY DISCLAIMS ANY DIRECT, INDIRECT, PUNITIVE, SPECIAL, INCIDENTAL,
CONSEQUENTIAL, OR EXEMPLARY DAMAGES ARISING OUT OF OR IN CONNECTION WITH THE USE OF THIS
DOCUMENT AND ANY INFORMATION CONTAINED IN THIS DOCUMENT.
Wi-Fi Simple Configuration Technical Specification v2.0.5
© 2014 Wi-Fi Alliance. All Rights Reserved.
Used with the permission of Wi-Fi Alliance under the terms as stated in this document.
Page 2 of 155
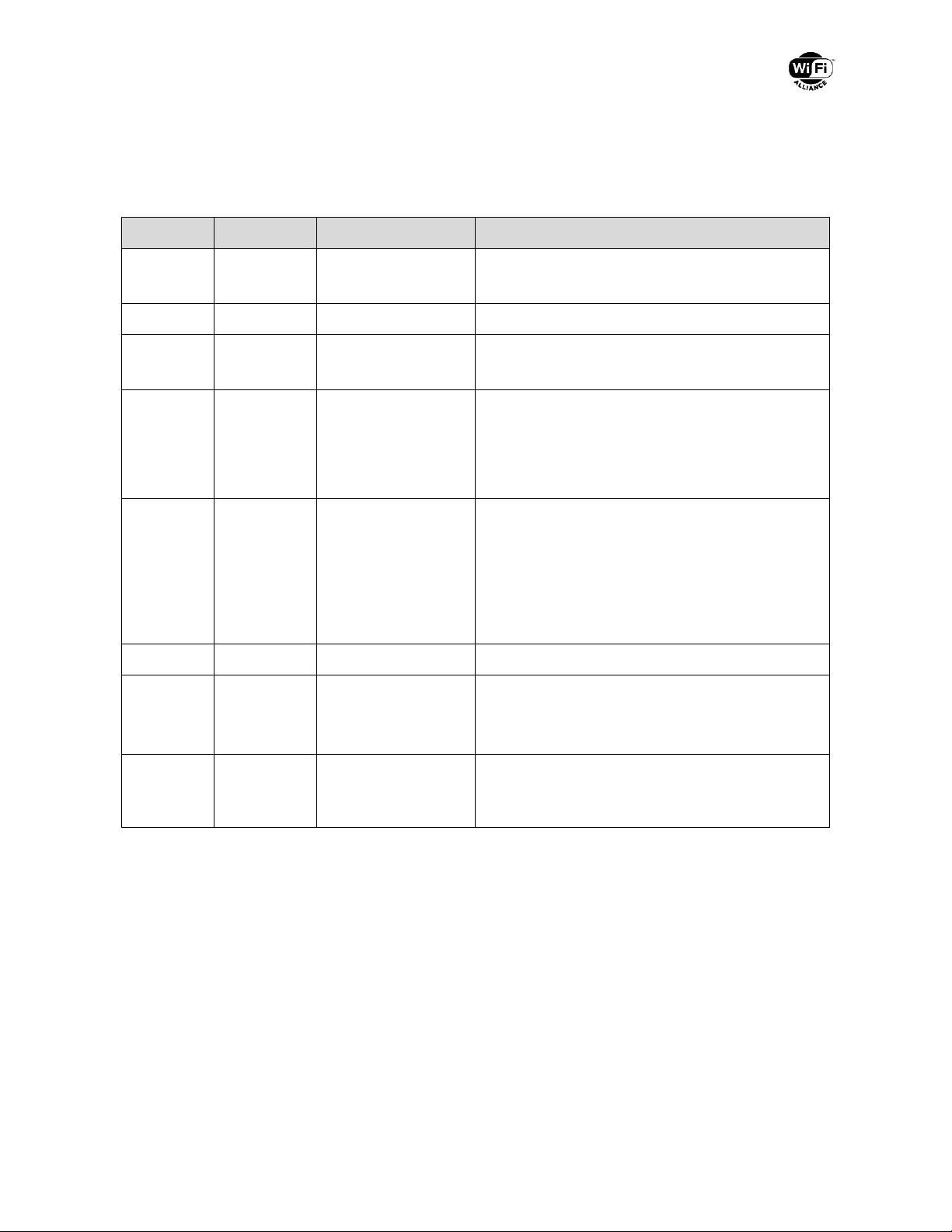
Document History
Version
Date
Status
Comments
2.0.0.51
2010-09-01
Draft
Draft release version to public
2.0.0
2010-12-20
Final
Public release version
2.0.1
2011-08-11
Final
Public release version
- Added tablet PC to table 41
2.0.2
2012-01-30
Final
Public release version
- Change Headless Devices section to mandate
implementation of strong mitigation against a
brute force attack on the AP that uses a static
PIN.
2.0.2.1.21
2014-01-27
Draft
Draft release version to public
- Updated to support NFC
- Updated to incorporate the Wi-Fi Peer-to-Peer
Services default configuration method
- Updated to incorporate 60GHz_WPS_SRD_1.0
- Minor editorial corrections/clarifications
2.0.3
Draft
Internal Draft, not publicly released
2.0.4
2014-03-21
Final
Public release version
- Clarifications on NFC sections
- Minor editorial corrections/clarifications
2.0.5
2014-08-04
Final
Public release version
- Editorial updates to clarify references to Wi-Fi
Peer-to-Peer Services (P2Ps) Specification

Wi-Fi Simple Configuration Technical Specification v2.0.4
© 2014 Wi-Fi Alliance. All Rights Reserved.
Used with the permission of the Wi-Fi Alliance under the terms as stated in this document.
Page 3 of 155
Table of Contents
1 Introduction ............................................................................................................ 11
1.1 Purpose ................................................................................................... 11
1.2 Scope....................................................................................................... 11
1.3 Supported Usage Models ........................................................................ 11
1.3.1 Primary Usage Models............................................................................. 11
1.3.2 Secondary Usage Models ........................................................................ 11
1.4 Design Approach ..................................................................................... 12
1.5 Solution Flexibility .................................................................................... 12
1.6 User Experience ...................................................................................... 13
1.6.1 In-band Setup .......................................................................................... 13
1.6.2 Out-of-Band Setup ................................................................................... 14
2 References ............................................................................................................. 15
3 Definitions .............................................................................................................. 16
4 Core Architecture ................................................................................................... 18
4.1 Components and Interfaces ..................................................................... 18
4.1.1 Architectural Overview ............................................................................. 18
4.1.2 Interface E ............................................................................................... 19
4.1.3 Interface M ............................................................................................... 20
4.1.4 Interface A ............................................................................................... 21
4.2 Registration Protocol................................................................................ 21
4.3 Security Overview .................................................................................... 23
4.3.1 In-band Configuration .............................................................................. 24
4.3.2 Guidelines and Requirements for PIN values .......................................... 26
4.3.3 Out-of-Band Configuration ....................................................................... 27
5 Initial WLAN Setup ................................................................................................. 28
5.1 Standalone AP ......................................................................................... 28
5.2 AP With an External Registrar ................................................................. 29
5.2.1 EAP-based Setup of External Registrar ................................................... 31
5.2.2 Ethernet-based Setup of External Registrar ............................................ 33
6 Adding Member Devices ........................................................................................ 34
6.1 In-band Setup Using a Standalone AP/Registrar ..................................... 35
6.2 In-band Setup Using an External Registrar .............................................. 36

Wi-Fi Simple Configuration Technical Specification v2.0.4
© 2014 Wi-Fi Alliance. All Rights Reserved.
Used with the permission of the Wi-Fi Alliance under the terms as stated in this document.
Page 4 of 155
6.2.1 PIN based setup - External Registrar trigger first ..................................... 36
6.2.2 PBC based setup – External Registrar trigger first .................................. 38
6.2.3 PIN based setup – Enrollee trigger first ................................................... 39
6.2.4 PBC based setup – Enrollee trigger first .................................................. 41
6.3 In-band Setup Using Multiple External Registrars ................................... 42
6.4 Secure Setup with Legacy Enrollee ......................................................... 45
6.4.1 Mental model mapping............................................................................. 45
7 Registration Protocol Definition .............................................................................. 46
7.1 Registration Protocol Initiation ................................................................. 46
7.2 Registration Protocol Messages .............................................................. 48
7.2.1 Optional Parameters ................................................................................ 50
7.2.2 Validation of Configuration Data .............................................................. 51
7.3 Key Derivation ......................................................................................... 51
7.4 Proof-of-possession of Device Password ................................................ 53
7.4.1 PIN Checksums ....................................................................................... 54
7.4.2 Device Password Splitting ....................................................................... 55
7.4.3 Device Password Usage in M1 and M2 ................................................... 55
7.5 Key Wrap Algorithm ................................................................................. 57
7.6 Key Summary and Classification ............................................................. 57
7.7 EAP Transport of Registration Protocol ................................................... 58
7.7.1 EAP Message Framing ............................................................................ 59
7.7.2 EAP Messages ........................................................................................ 61
7.7.3 EAP State Machine for Enrollee Registration .......................................... 63
7.7.4 EAP State Machine for Adding an External Registrar .............................. 64
7.8 UPnP Transport of Registration Protocol ................................................. 65
7.9 Version Negotiation ................................................................................. 66
8 Message Encoding ................................................................................................. 67
8.1 Wi-Fi Simple Configuration TLV Data Format .......................................... 67
8.2 802.11 Management Frames ................................................................... 68
8.2.1 Beacon Frame (C) ................................................................................... 69
8.2.2 Association Request and Reassociation Request ................................... 70
8.2.3 Association Response and Reassociation Response .............................. 71
8.2.4 Probe Request (D-E or D-R) .................................................................... 71

Wi-Fi Simple Configuration Technical Specification v2.0.4
© 2014 Wi-Fi Alliance. All Rights Reserved.
Used with the permission of the Wi-Fi Alliance under the terms as stated in this document.
Page 5 of 155
8.2.5 Probe Response (D-AP/Registrar) ........................................................... 72
8.3 Registration Protocol Message Definitions .............................................. 73
8.3.1 Message M1 ............................................................................................ 74
8.3.2 Message M2 ............................................................................................ 75
8.3.3 Message M2D .......................................................................................... 76
8.3.4 Message M3 ............................................................................................ 77
8.3.5 Message M4 ............................................................................................ 77
8.3.6 Message M5 ............................................................................................ 78
8.3.7 Message M6 ............................................................................................ 78
8.3.8 Message M7 ............................................................................................ 79
8.3.9 Message M8 ............................................................................................ 80
8.3.10 WSC_ACK Message................................................................................ 82
8.3.11 WSC_NACK Message ............................................................................. 82
8.3.12 WSC_Done Message .............................................................................. 83
8.4 AP Settings Message Definitions ............................................................. 83
8.4.1 SetSelectedRegistrar Message ............................................................... 83
9 Security Configuration Requirements ..................................................................... 85
10 NFC Out-of-Band Interface Specification ............................................................... 86
10.1 NFC Usage Models ................................................................................. 86
10.1.1 Password Token ...................................................................................... 86
10.1.2 Configuration Token ................................................................................ 87
10.1.3 Connection Handover .............................................................................. 88
10.2 Requirements for NFC Out-of-Band Support ........................................... 91
10.2.1 Enrollee Requirements ............................................................................ 91
10.2.2 Registrar Requirements ........................................................................... 92
10.2.3 P2P Registrar Requirements ................................................................... 92
11 Push Button Configuration ..................................................................................... 93
11.1 Introduction .............................................................................................. 93
11.2 User Experience ...................................................................................... 93
11.3 PBC Technical Description ...................................................................... 95
11.4 PBC Security Considerations ................................................................... 98
12 Data Element Definitions ...................................................................................... 100
13 Protocol Implementation Conformance Specification (PICS) .............................. 132
剩余154页未读,继续阅读
zphjita
- 粉丝: 1
- 资源: 4
上传资源 快速赚钱
 我的内容管理
收起
我的内容管理
收起
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

会员权益专享
最新资源
- c++校园超市商品信息管理系统课程设计说明书(含源代码) (2).pdf
- 建筑供配电系统相关课件.pptx
- 企业管理规章制度及管理模式.doc
- vb打开摄像头.doc
- 云计算-可信计算中认证协议改进方案.pdf
- [详细完整版]单片机编程4.ppt
- c语言常用算法.pdf
- c++经典程序代码大全.pdf
- 单片机数字时钟资料.doc
- 11项目管理前沿1.0.pptx
- 基于ssm的“魅力”繁峙宣传网站的设计与实现论文.doc
- 智慧交通综合解决方案.pptx
- 建筑防潮设计-PowerPointPresentati.pptx
- SPC统计过程控制程序.pptx
- SPC统计方法基础知识.pptx
- MW全能培训汽轮机调节保安系统PPT教学课件.pptx
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
评论0