没有合适的资源?快使用搜索试试~ 我知道了~
首页论文研究 - 僵尸网络检测机器学习算法及其集成的比较研究
僵尸网络是由受感染的设备组成的网络,这些设备由恶意的“僵尸网络管理员”控制,以执行各种任务,例如执行DoS攻击,发送垃圾邮件和获取个人数据等。僵尸网络管理员在与僵尸网络通信时生成网络流量,分析网络用于检测僵尸网络流量的流量可能是入侵检测系统的一项有前途的功能。 尽管这样的系统已经应用了各种机器学习技术,但是尚未弄清机器算法,包括它们在僵尸网络检测中的集成。 在这项研究中,不仅评估了三种最流行的分类机器学习算法(朴素贝叶斯,决策树和神经网络),而且还测试了用于增强分类器的集成方法,以查看它们是否确实提供了对僵尸网络检测的增强预测。 该评估是使用CTU-13公共数据集进行的,测量每个分类器的训练时间及其F量度和MCC得分。
资源详情
资源评论
资源推荐

Journal of Computer and Communications, 2018, 6, 119-129
http://www.scirp.org/journal/jcc
ISSN Online: 2327-5227
ISSN Print: 2327-5219
DOI:
10.4236/jcc.2018.65010 May 31, 2018 119 Journal of Computer and Communications
A Comparative Study of Machine Learning
Algorithms and Their Ensembles for Botnet
Detection
Songhui Ryu, Baijian Yang
Purdue University, West Lafayette, USA
Abstract
A Botnet is a network of compromised devices that are controlled by mal
i-
cious “botmaster”
in order to perform various tasks, such as executing DoS
attack, sending SPAM and obtaining personal data etc. As botmasters gene
r-
ate network traffic while communicating with their bots, analyzing network
traffic to detect Botnet traffic can be a promising feature of Intrusion Dete
c-
tion System. Although such system has been applying various machine lear
n-
ing techniques, comparison of machine algorith
ms including their ensembles
on botnet detection has not been figured out. In this study, not only the three
most popular classification machine learning algorithms—Naive Bayes, Dec
i-
sion tree, and Neural network are evaluated, but also the ensemble methods
known to strengthen classifier are tested to see if they indeed provide e
n-
hanced predictions on Botnet detec
tion. This evaluation is conducted with the
CTU-13 public dataset, measuring the training time of each classifier and its F
measure and
MCC
score.
Keywords
Machine Learning, Ensemble Method, Botnet, CTU-13
1. Introduction
As a network of compromised devices called bots, a botnet executes malicious
tasks under the control of the attacker, a botmaster. A botnet has been a threat to
cybersecurity [1] [2]. According to Ref. [3], the primary goals of botnets are as
follows:
•
Information dispersion: sending SPAM, executing Denial of Service (DoS)
attack, distributing false information from illegal sources.
How to cite this paper:
Ryu, S. and Yang
,
B
. (2018)
A Comparative Study of Machine
Learning Algorithms and Their Ensembles
for Botnet Detection
.
Journal of Computer
and Communications
,
6
, 119-129.
https://doi.org/10.4236/jcc.2018.65010
Received:
April 13, 2018
Accepted:
May 28, 2018
Published:
May 31, 2018
Copyright © 201
8 by authors and
Scientific
Research Publishing Inc.
This work is licensed under the Creative
Commons Attribution
International
License (CC BY
4.0).
http://creativecommons.org/licenses/by/4.0/
Open Access

S. Ryu, B. Yang
DOI:
10.4236/jcc.2018.65010 120 Journal of Computer and Communications
• Information harvesting: obtaining identity, password and financial data.
•
Information processing: processing data to crack the password for access to
additional hosts.
A botnet has been grown as a menace since the first botnet. EggDrop was re-
ported in 1993 [1]. For example, [4] it was reported that the Necurs botnet was
one of the most active distributors of malware in 2016. More than 2.3 million
spam emails carrying JavaScript downloaders, VBS, and WSF attachments were
sent out by Necurs in just one day on November 24, 2016.
The Mirai botnet, according to the same report [4], drove the largest DDoS
attack ever recorded in 2016 on the French hosting company OVH peaking at
1Tbps mostly targeting IoT devices, such as home routers and IP cameras. As
Gartner predicted that there would be more than 20 billion IoT devices by 2020
[5], it is important that botnets like Mirai should be addressed.
The speed of growth of botnet threat is also rapid. According to the report
from Spamhaus [6], the number of IP addresses that was figured out as a Con-
trol and Command (C & C) server hosted by Amazon in 2017 increased 6 times
against that of 2016.
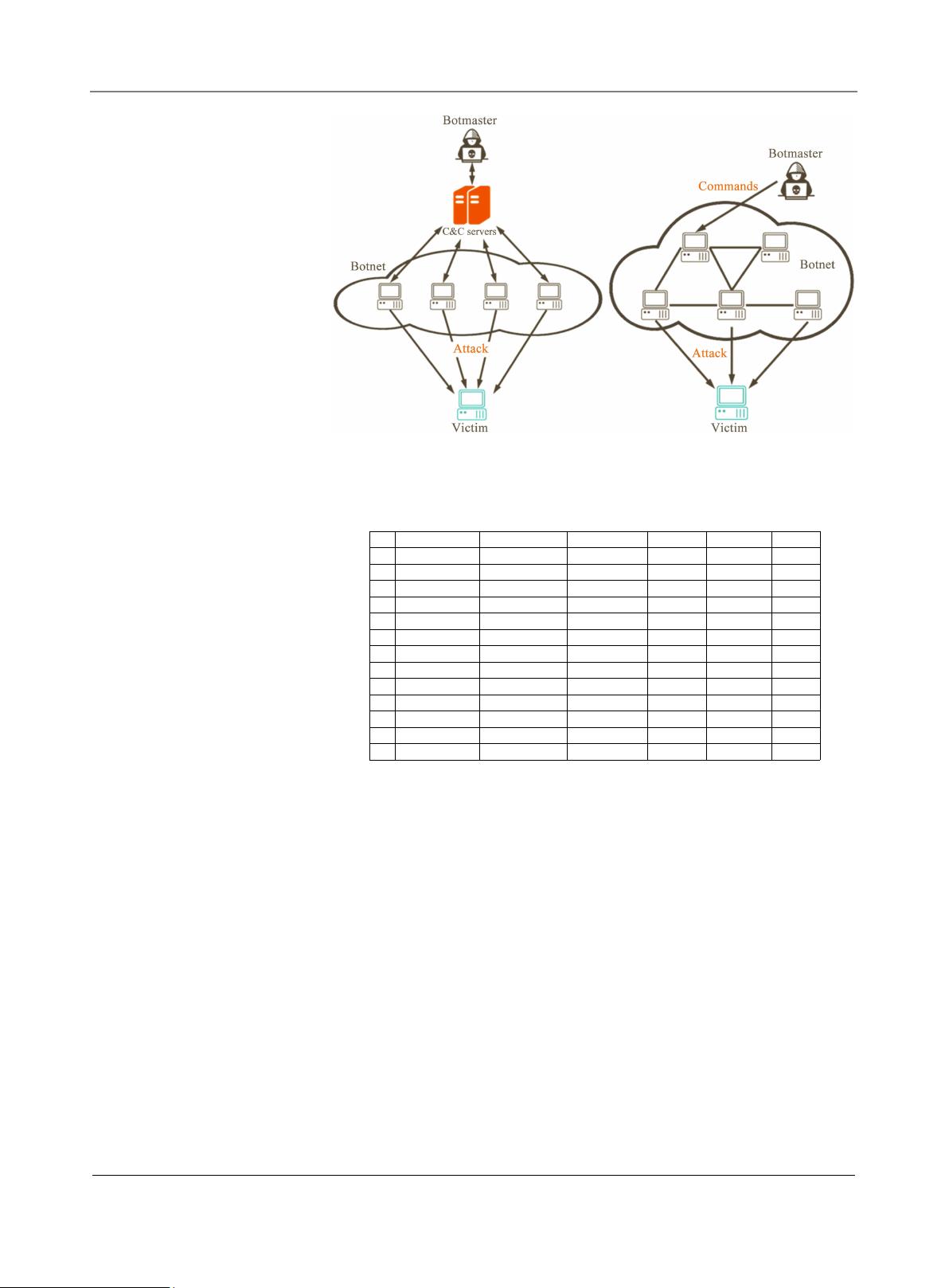
A botnet usually has distinguishable architecture features [7]. A botmaster
usually sets up a Control and Command server to easily communicate with his
bots. For this type of centralized architecture, IRC protocol has been the most
popular, but HTTP or POP3 have been used as well. The centralized botnets like
Rxbot, Festi, and Bobax using IRC, HTTP, TCP can be depicted as
Figure 1. On
the other hand, a botnet can feature a Peer-to-peer architecture. In a P2P botnet,
a bot can bypass connections to other bots in case there are firewalls in some of
the connections. The decentralized botnets like TDL-4 utilizing P2P protocol
can be depicted in
Figure 2.
To detect botnet, approaches focusing on anomalies in bot(net)s’ network be-
havior with or without temporal behavior have been proposed. Most of the pre-
vious studies adopted machine learning technologies along with heuristic rules
[1] [2]. Even though the previously proposed detection systems utilized both
supervised and unsupervised machine learning algorithms, the ensemble me-
thods have not been discussed yet.
In this paper, focusing on the ensemble methods, supervised machine learning
algorithms popularly used in previous studies were evaluated with their ensem-
bles. As the ensemble methods were designed to strengthen weak classifiers, it
would be meaningful to figure it out if the ensemble methods are indeed benefi-
cial when it comes to botnet detection.
In the following chapter, popular classification algorithms that have been used
in serval botnet detection proposals and the ensemble technology are explained.
2. Related Works
2.1. Machine Learning for Botnet Detection
In the previous studies where they used supervised machine learning algorithms,
S. Ryu, B. Yang
DOI:
10.4236/jcc.2018.65010 121 Journal of Computer and Communications
(a) (b)
Figure 1. Examples of botnet architecture. (a) Centralized C & C architecture; (b)
Decentralized P2P C & C architecture.
Figure 2. Amount of data on each botnet scenario [17].
three algorithms—Naive Bayes, decision tree, and (artificial) neural networks
were popularly adopted [8] [9] [10] [11].
2.1.1. Naive Bayes
Naive Bayes algorithm is a simple and intuitive classification technique based on
the Bayes theorem assuming each feature contributes independently to the
probability of an event [12]. Specifically in machine learning, Naive Bayes clas-
sifier calculates all the probability for all classes for a target feature and selects
one with the highest probability. Furthermore, Gaussian Naive Bayes (GNB) as-
sumes that the values associated with each class of each feature follow a Gaussian
distribution. Although those assumptions do not happen often in real life, Naive
Bayes shows relatively better results than other models like logistic regression.
Also, it can generate models very quickly with very little computation overhead .
It is therefore a popular choice for SPAM filters and other real-time anomaly
detection algorithms [13].
Id
Duration(hrs)
# Packets
# NetFlows
Size
Bot
# Bots
1
6.15
71,971,482
2,824,637
52GB
Neris
1
2
4.21
71,851,300
1,808,123
60GB
Neris
1
3
66.85
167,730,395
4,710,639
121GB
Rbot
1
4
4.21
62,089,135
1,121,077
53GB
Rbot
1
5
11.63
4,481,167
129,833
37.6GB
Virut
1
6
2.18
38,764,,357
558,920
30GB
Menti
1
7
0.38
7,467,139
114,078
5.8GB
Sogou
1
8
19.5
155,207,799
2,954,231
123GB
Murlo
1
9
5.18
115,415,321
2,753,885
94GB
Neris
10
10
4.75
90,389,782
1,309,792
73GB
Rbot
10
11
0.26
6,337,202
107,252
5.2GB
Rbot
3
12
1.21
13,212,268
325,472
8.3GB
NSIS.ay
3
13
16.26
50,888,256
1,925,150
34GB
Virut
1
剩余10页未读,继续阅读
weixin_38675506
- 粉丝: 4
- 资源: 931
上传资源 快速赚钱
 我的内容管理
收起
我的内容管理
收起
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

会员权益专享
最新资源
- zigbee-cluster-library-specification
- JSBSim Reference Manual
- c++校园超市商品信息管理系统课程设计说明书(含源代码) (2).pdf
- 建筑供配电系统相关课件.pptx
- 企业管理规章制度及管理模式.doc
- vb打开摄像头.doc
- 云计算-可信计算中认证协议改进方案.pdf
- [详细完整版]单片机编程4.ppt
- c语言常用算法.pdf
- c++经典程序代码大全.pdf
- 单片机数字时钟资料.doc
- 11项目管理前沿1.0.pptx
- 基于ssm的“魅力”繁峙宣传网站的设计与实现论文.doc
- 智慧交通综合解决方案.pptx
- 建筑防潮设计-PowerPointPresentati.pptx
- SPC统计过程控制程序.pptx
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
评论0