没有合适的资源?快使用搜索试试~ 我知道了~
首页cisco_n3k 接口配置
资源详情
资源评论
资源推荐

Configuring Q-in-Q VLAN Tunnels
This chapter contains the following sections:
•
Information About Q-in-Q Tunnels, page 1
•
Information About Layer 2 Protocol Tunneling, page 4
•
Licensing Requirements for Q-in-Q Tunnels, page 7
•
Guidelines and Limitations for Q-in-Q Tunneling, page 7
•
Configuring Q-in-Q Tunnels and Layer 2 Protocol Tunneling, page 8
•
Verifying the Q-in-Q Configuration, page 11
•
Configuration Example for Q-in-Q and Layer 2 Protocol Tunneling, page 11
•
Feature History for Q-in-Q Tunnels and Layer 2 Protocol Tunneling, page 12
Information About Q-in-Q Tunnels
A Q-in-Q VLAN tunnel enables a service provider to segregate the traffic of different customers in their
infrastructure, while still giving the customer a full range of VLANs for their internal use by adding a second
802.1Q tag to an already tagged frame.
Business customers of service providers often have specific requirements for VLAN IDs and the number of
VLANs to be supported. The VLAN ranges required by different customers in the same service-provider
network might overlap, and traffic of customers through the infrastructure might be mixed. Assigning a unique
range of VLAN IDs to each customer would restrict customer configurations and could easily exceed the
VLAN limit of 4096 of the 802.1Q specification.
Q-in-Q is supported on port channels. To configure a port channel as an asymmetrical link, all ports in
the port channel must have the same tunneling configuration.
Note
Using the 802.1Q tunneling feature, service providers can use a single VLAN to support customers who have
multiple VLANs. Customer VLAN IDs are preserved and traffic from different customers is segregated within
the service-provider infrastructure even when they appear to be on the same VLAN. The 802.1Q tunneling
expands VLAN space by using a VLAN-in-VLAN hierarchy and tagging the tagged packets. A port configured
to support 802.1Q tunneling is called a tunnel port. When you configure tunneling, you assign a tunnel port
Cisco Nexus 3000 Series NX-OS Interfaces Configuration Guide, Release 6.x
1

to a VLAN that is dedicated to tunneling. Each customer requires a separate VLAN, but that VLAN supports
all of the customer’s VLANs.
Customer traffic tagged in the normal way with appropriate VLAN IDs come from an 802.1Q trunk port on
the customer device and into a tunnel port on the service-provider edge switch. The link between the customer
device and the edge switch is an asymmetric link because one end is configured as an 802.1Q trunk port and
the other end is configured as a tunnel port. You assign the tunnel port interface to an access VLAN ID that
is unique to each customer.
Selective Q-in-Q tunneling is not supported. All frames entering the tunnel port are subjected to Q-in-Q
tagging.
Note
Figure 1: 802.1Q-in-Q Tunnel Ports
Packets that enter the tunnel port on the service-provider edge switch, which are already 802.1Q-tagged with
the appropriate VLAN IDs, are encapsulated with another layer of an 802.1Q tag that contains a VLAN ID
that is unique to the customer. The original 802.1Q tag from the customer is preserved in the encapsulated
packet. Therefore, packets that enter the service-provider infrastructure are double-tagged.
The outer tag contains the customer’s access VLAN ID (as assigned by the service provider), and the inner
VLAN ID is the VLAN of the incoming traffic (as assigned by the customer). This double tagging is called
tag stacking, Double-Q, or Q-in-Q.
Cisco Nexus 3000 Series NX-OS Interfaces Configuration Guide, Release 6.x
2
Configuring Q-in-Q VLAN Tunnels
Information About Q-in-Q Tunnels
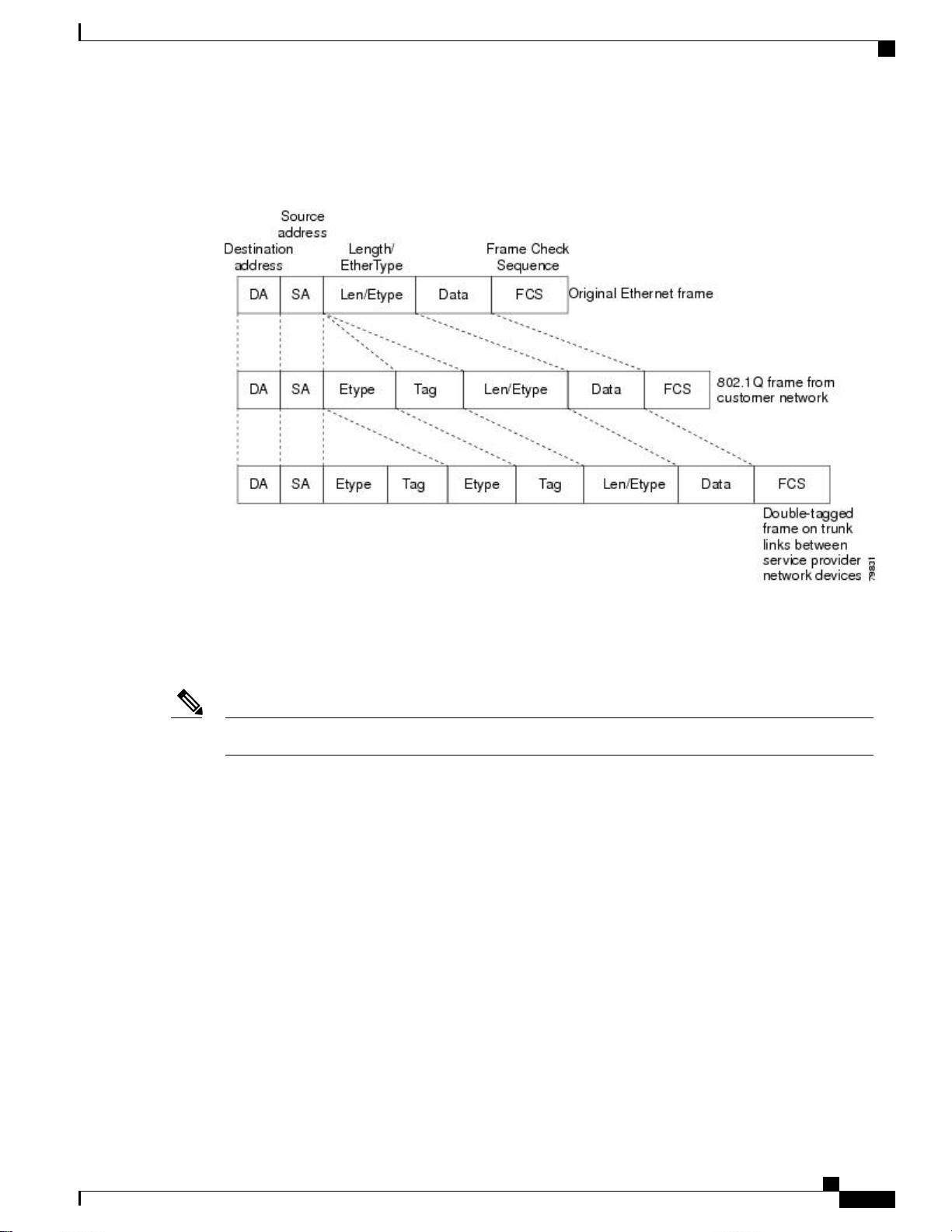
The following figure shows the differences between the untagged, tagged and double-tagged ethernet frames.
Figure 2: Untagged, 802.1Q-Tagged, and Double-Tagged Ethernet Frames
By using this method, the VLAN ID space of the outer tag is independent of the VLAN ID space of the inner
tag. A single outer VLAN ID can represent the entire VLAN ID space for an individual customer. This
technique allows the customer’s Layer 2 network to extend across the service provider network, potentially
creating a virtual LAN infrastructure over multiple sites.
Hierarchical tagging, that is multi-level dot1q tagging Q-in-Q, is not supported.Note
Native VLAN Hazard
When configuring 802.1Q tunneling on an edge switch, you must use 802.1Q trunk ports for sending out
packets into the service-provider network. However, packets that go through the core of the service-provider
network might be carried through 802.1Q trunks, ISL trunks, or nontrunking links. When 802.1Q trunks are
used in these core switches, the native VLANs of the 802.1Q trunks must not match any native VLAN of the
dot1q-tunnel port on the same switch because traffic on the native VLAN is not tagged on the 802.1Q
transmitting trunk port.
VLAN 40 is configured as the native VLAN for the 802.1Q trunk port from Customer X at the ingress edge
switch in the service-provider network (Switch B). Switch A of Customer X sends a tagged packet on VLAN
30 to the ingress tunnel port of Switch B in the service-provider network that belongs to access VLAN 40.
Because the access VLAN of the tunnel port (VLAN 40) is the same as the native VLAN of the edge-switch
trunk port (VLAN 40), the 802.1Q tag is not added to the tagged packets that are received from the tunnel
port. The packet carries only the VLAN 30 tag through the service-provider network to the trunk port of the
egress-edge switch (Switch C) and is misdirected through the egress switch tunnel port to Customer Y.
Cisco Nexus 3000 Series NX-OS Interfaces Configuration Guide, Release 6.x
3
Configuring Q-in-Q VLAN Tunnels
Native VLAN Hazard
剩余11页未读,继续阅读
豆逗乐
- 粉丝: 0
- 资源: 3
上传资源 快速赚钱
 我的内容管理
收起
我的内容管理
收起
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

会员权益专享
最新资源
- zigbee-cluster-library-specification
- JSBSim Reference Manual
- c++校园超市商品信息管理系统课程设计说明书(含源代码) (2).pdf
- 建筑供配电系统相关课件.pptx
- 企业管理规章制度及管理模式.doc
- vb打开摄像头.doc
- 云计算-可信计算中认证协议改进方案.pdf
- [详细完整版]单片机编程4.ppt
- c语言常用算法.pdf
- c++经典程序代码大全.pdf
- 单片机数字时钟资料.doc
- 11项目管理前沿1.0.pptx
- 基于ssm的“魅力”繁峙宣传网站的设计与实现论文.doc
- 智慧交通综合解决方案.pptx
- 建筑防潮设计-PowerPointPresentati.pptx
- SPC统计过程控制程序.pptx
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
评论0