Tse and Viswanath: Fundamentals of Wireless Communication 3
=
2α sin [2πf (t − d/c)] sin [2πf (r(t) − d) /c]
2d − r(t)
+
2α [d − r(t)] cos [2πf (t − r(t)/c)]
r(t)[2d − r(t)]
(2.1)
where we applied the identity
cos x − cos y = 2 sin
µ
x + y
2
¶
sin
µ
y − x
2
¶
We observe that the first term of (2.1) is similar in form to equation (2.13) in the
notes. The second term of (2.1) goes to 0 as r(t) → d and is due to the difference in
propagation losses in the 2 paths.
Exercise 2.3. If the wall is on the other side, both components arrive at the mobile
from the left and experience the same Doppler shift.
E
r
(f, t) =
<[α exp{j2π[f(1 − v/c)t − fr
0
/c]}]
r
0
+ vt
−
<[α exp{j2π[f(1 − v/c)t − f(r
0
+ 2d)/c]}]
r
0
+ 2d + vt
We have the interaction of 2 sinusoidal waves of the same frequency and different
amplitude.
Over time, we observe the composition of these 2 waves into a single sinusoidal
signal of frequency f (1−v/c ) and constant amplitude that depends on the attenuations
(r
0
+ vt) and (r
0
+ 2d + vt) and also on the phase difference f2d/c.
Over frequency, we observe that when f2d/c is an integer both waves interfere
destructively resulting in a small received signal. When f2d/c = (2k + 1)/2, k ∈ Z
these waves interfere constructively resulting in a larger received signal. So when f
is varied by c/4d the amplitude of the received signal varies from a minimum to a
maximum.
The variation over frequency is similar in nature to that of section 2.1.3, but since
the delay spread is different the coherence bandwidth is also different.
However there is no variation over time because the Doppler spread is zero.
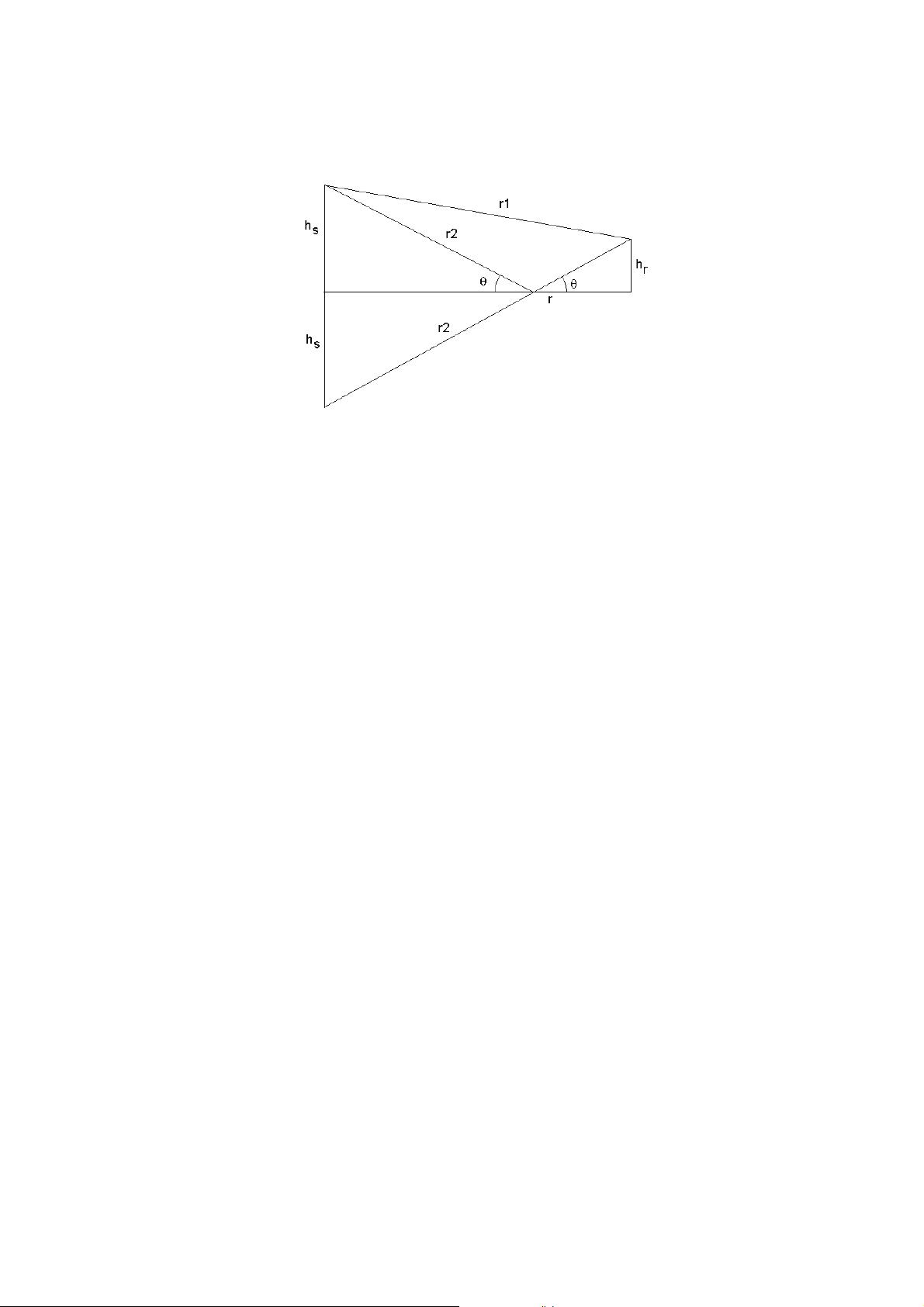
Exercise 2.4. 1. i) With the given information we can compute the Doppler spread:
D
s
= |f
1
− f
2
| =
fv
c
|cos θ
1
− cos θ
2
|
from which we can compute the coherence time
T
c
=
1
4D
s
=
c
4fv|cos θ
1
− cos θ
2
|
ii) There is not enough information to compute the coherence bandwidth, as it
depends on the delay spread which is not given. We would need to know the
difference in path length to compute the delay spread T
d
and use it to compute
W
c
.