没有合适的资源?快使用搜索试试~ 我知道了~
首页智能平台管理接口(IPMI)
智能平台管理接口(IPMI)
(Intelligent Platform Management Interface)智能平台管理接口 (IPMI) 是一种开放标准的硬件管理接口规格,定义了嵌入式管理子系统进行通信的特定方法。本文档是IPMI v2.0标准。
资源详情
资源评论
资源推荐

- IPMI -
Intelligent Platform Management
Interface Specification
Second Generation
v2.0
Document Revision 1.0
February 12, 2004
Intel Hewlett-Packard NEC Dell
Intelligent Platform Management Interface Specification
ii
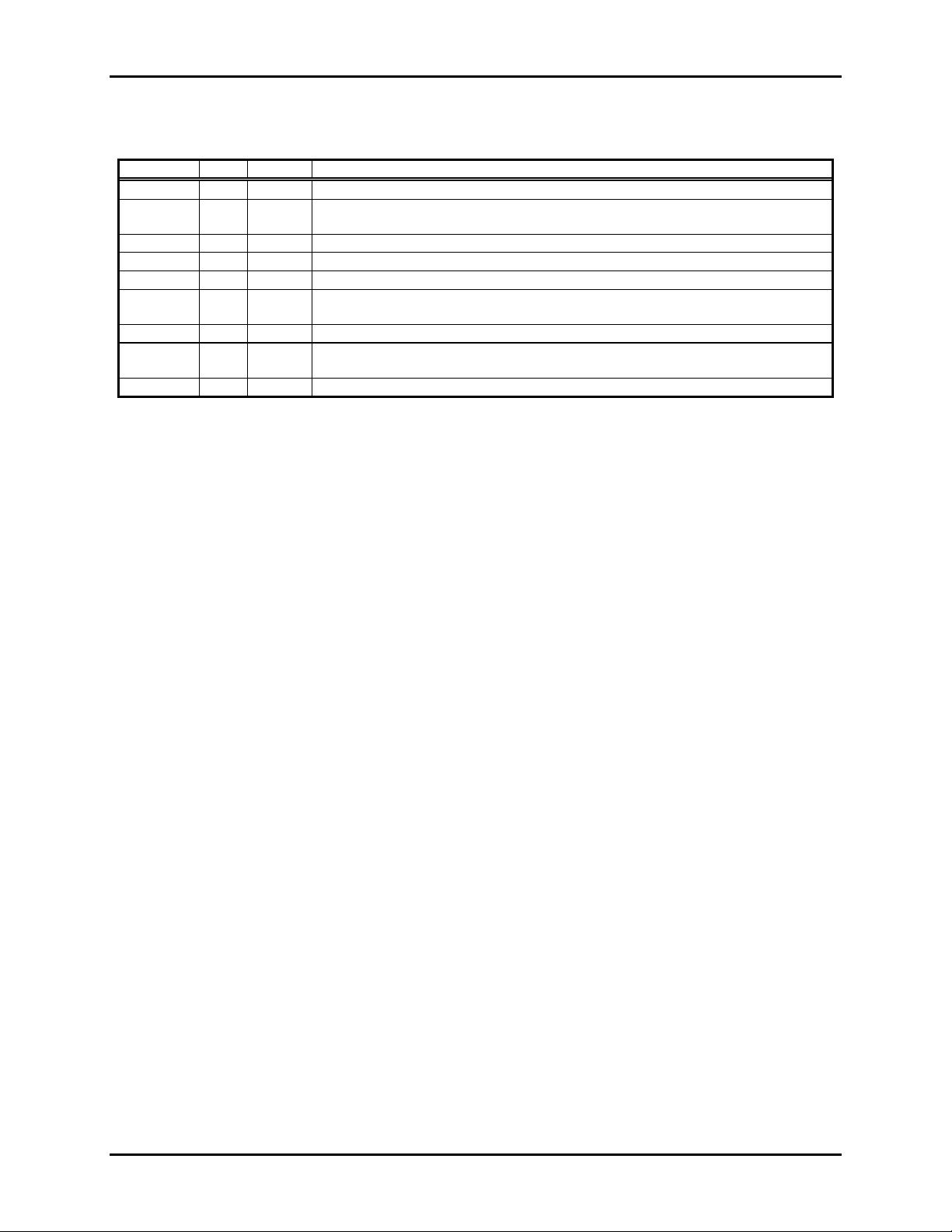
Revision History
Date Ver Rev Modifications
9/16/98 1.0 1.0 IPMI v1.0 Initial release
8/26/99 1.0 1.1 Errata Revision. Incorporated errata from revision 1 or the Errata and
Clarifications for the IPMI v1.0 specification.
2/21/01 1.5 1.0 IPMI v1.5 Initial release
2/20/02 1.5 1.1 Updated to include addenda and errata
9/12/03 1.5 1.1 Markup to include 9/12/03 addenda and errata
9/26/03 1.5 1.1 Markup updated to include missing optional 5th byte on Get Chassis Status
command, per errata E317
1/27/04 1.5 1.1 Markup updated per errata document version 5
See v1.5
spec
1.5 1.2 IPMI 1.5 updated per errata document version 5
2/12/04 2.0 1.0 IPMI Second Generation document. Initial release.
Copyright © 2004 Intel Corporation, Hewlett-Packard Company, NEC Corporation,
Dell Computer Corporation, All rights reserved.
INTELLECTUAL PROPERTY DISCLAIMER
THIS SPECIFICATION IS PROVIDED “AS IS” WITH NO WARRANTIES WHATSOEVER INCLUDING ANY
WARRANTY OF MERCHANTABILITY, FITNESS FOR ANY PARTICULAR PURPOSE, OR ANY WARRANTY
OTHERWISE ARISING OUT OF ANY PROPOSAL, SPECIFICATION, OR SAMPLE.
NO LICENSE, EXPRESS OR IMPLIED, BY ESTOPPEL OR OTHERWISE, TO ANY INTELLECTUAL PROPERTY
RIGHTS IS GRANTED OR INTENDED HEREBY.
INTEL, HEWLETT-PACKARD, NEC, AND DELL DISCLAIM ALL LIABILITY, INCLUDING LIABILITY FOR
INFRINGEMENT OF PROPRIETARY RIGHTS, RELATING TO IMPLEMENTATION OF INFORMATION IN THIS
SPECIFICATION. INTEL, HEWLETT-PACKARD, NEC, AND DELL, DO NOT WARRANT OR REPRESENT THAT
SUCH IMPLEMENTATION(S) WILL NOT INFRINGE SUCH RIGHTS.
I
P
2
P
C is a trademark of Philips Semiconductors. All other product names are trademarks, registered trademarks, or servicemarks of
their respective owners.
I
P
2
P
C is a two-wire communications bus/protocol developed by Philips. IPMB is a subset of the IP
2
P
C bus/protocol and was
developed by Intel. Implementations of the I
P
2
P
C bus/protocol or the IPMB bus/protocol may require licenses from various
entities, including Philips Electronics N.V. and North American Philips Corporation.
Intel, Hewlett-Packard, NEC, and Dell retain the right to make changes to this document at any time, without notice. Intel,
Hewlett-Packard, NEC, and Dell make no warranty for the use of this document and assume no responsibility for any error
which may appear in the document nor does it make a commitment to update the information contained herein.

Intelligent Platform Management Interface Specification
iii
IPMI NON-DISCLOSURE AGREEMENT
DO NOT download these files (collectively, the “Confidential Information”) until you have carefully read the
following terms and conditions. By downloading the Confidential Information you agree to the terms of this
Agreement. If you do not wish to so agree, do not download the Confidential Information.
1.
UConfidential InformationU. The confidential, proprietary and trade secret information being disclosed ("Confidential
Information"), is that information marked with a "confidential", "proprietary", or similar legend, and is described as:
Confidential Information:
UIntelligent Platform Management Interface Specification Second Generation (v2.0),
Intelligent Platform Management Bus Bridge Specification (v1.0), Intelligent Chassis Management Bus Bridge
Specification (v1.0)
CONFIDENTIAL INFORMATION IS PROVIDED SOLELY FOR YOUR INTERNAL EVALUATION AND
REVIEW TO DETERMINE WHETHER TO ADOPT THE SPECIFICATIONS BY SIGNING A SEPARATE
ADOPTER’S AGREEMENT. THE RECEIVING PARTY IS NOT LICENSED TO IMPLEMENT THE
SPECIFICATIONS UNLESS OR UNTIL AN ADOPTER’S AGREEMENT IS EXECUTED.
Disclosing party’s representatives for disclosing Confidential Information is: Fadi Zuhayri (fadi.zuhayri@intel.com)
2.
UObligations of Receiving PartyU. The receiving party will maintain the confidentiality of the Confidential Information of
the disclosing party with at least the same degree of care that it uses to protect its own confidential and proprietary
information, but no less than a reasonable degree of care under the circumstances. The receiving party will not
disclose any of the disclosing party’s Confidential Information to employees or to any third parties except to the
receiving party’s employees, parent company and
U majority-owned subsidiariesU who have a need to know and who
agree to abide by nondisclosure terms at least as comprehensive as those set forth herein; provided that the receiving
party will be liable for breach by any such entity. The receiving party will not make any copies of Confidential
Information received from the disclosing party except as necessary for its employees, parent company and majority-
owned subsidiaries with a need to know. Any copies which are made will be identified as belonging to the disclosing
party and marked "confidential", "proprietary" or with a similar legend.
3.
UPeriod of Non-AssertionU. Unless a shorter period is indicated below, the disclosing party will not assert any claims for
breach of this Agreement or misappropriation of trade secrets against the receiving party arising out of the receiving
party’s disclosure of disclosing party’s Confidential Information made more than five (5) years from the date of receipt
of the Confidential Information by the receiving party. However, unless at least one of the exceptions set forth in
Section 4 below has occurred, the receiving party will continue to treat such Confidential Information as the
confidential information of the disclosing party and only disclose any such Confidential Information to third parties
under the terms of a non-disclosure agreement.
4.
UTermination of Obligation of ConfidentialityU. The receiving party will not be liable for the disclosure of any Confidential
Information which is: (a) rightfully in the public domain other than by a breach of this Agreement of a duty to the
disclosing party; (b) rightfully received from a third party without any obligation of confidentiality; (c) rightfully known to
the receiving party without any limitation on use or disclosure prior to its receipt from the disclosing party;
(d) independently developed by employees of the receiving party; or (e) generally made available to third parties by
the disclosing party without restriction on disclosure.
5.
UTitleU. Title or the right to possess Confidential Information as between the parties will remain in the disclosing party.
6. UNo Obligation of Disclosure; Termination UThe disclosing party may terminate this Agreement at any time without
cause upon written notice to the other party; provided that the receiving party’s obligations with respect to information
disclosed during the term of this Agreement will survive any such termination. The disclosing party may, at any time:
(a) cease giving Confidential Information to the other party without any liability, and/or (b) request in writing the return
or destruction of all or part of its Confidential Information previously disclosed, and all copies thereof, and the
receiving party will promptly comply with such request, and certify in writing its compliance.
7.
UGeneralU.
(a) This Agreement is neither intended to nor will it be construed as creating a joint venture, partnership or other form
of business association between the parties, nor an obligation to buy or sell products using or incorporating the
Confidential Information.
(b) No license under any patent, copyright, trade secret or other intellectual property right is granted to or conferred
upon either party in this Agreement or by the transfer of any information by one party to the other party as
contemplated hereunder, either expressly, by implication, inducement, estoppel or otherwise, and that any
license under any such intellectual property rights must be express and in writing.
(c) The failure of either party to enforce any right resulting from breach of any provision of this Agreement will not be
deemed a waiver of any right relating to a subsequent breach of such provision or of any other right hereunder.
(d) This Agreement will be governed by the laws of the State of Delaware without reference to conflict of laws
principles.
(e) This Agreement constitutes the entire agreement between the parties with respect to the disclosure(s) of
Confidential Information described herein, and may not be amended except in a writing signed by a duly authorized
representative of the respective parties. Any other agreements between the parties, including non-disclosure
agreements, will not be affected by this Agreement.

Intelligent Platform Management Interface Specification
iv
Table of Contents
TU1.UT TUIntroductionUT .......................................................................................................................................... 1
TU1.1UT TUAudienceUT .........................................................................................................................................................1
TU1.2UT TUReference DocumentsUT .....................................................................................................................................1
TU1.3UT TUConventions and TerminologyUT ........................................................................................................................5
TU1.4UT TUBackground - Architectural GoalsUT...................................................................................................................6
TU1.5UT TUNew for IPMI v1.5UT ..........................................................................................................................................7
TU1.6UT TUNew for IPMI v2.0UT ..........................................................................................................................................9
TU1.7UT TUIPMI OverviewUT..............................................................................................................................................11
TU1.7.1UT TUIntelligent Platform ManagementUT...........................................................................................................11
TU1.7.2UT TUIPMI Relationship to other Management StandardsUT ..............................................................................11
TU1.7.3UT TUManagement Controllers and the IPMBUT.................................................................................................12
TU1.7.4UT TUIPMI MessagingUT .....................................................................................................................................13
TU1.7.5UT TUSensor ModelUT .........................................................................................................................................13
TU1.7.6UT TUSystem Event Log and Event MessagesUT .................................................................................................13
TU1.7.7UT TUSensor Data Records & Capabilities CommandsUT ...................................................................................14
TU1.7.8UT TUInitialization AgentUT ................................................................................................................................15
TU1.7.9UT TUSensor Data Record RepositoryUT .............................................................................................................15
TU1.7.10UT TUPrivate Management BussesUT ..................................................................................................................15
TU1.7.11UT TUFRU InformationUT ....................................................................................................................................15
TU1.7.12UT TUFRU DevicesUT ..........................................................................................................................................16
TU1.7.13UT TUEntity Association RecordsUT ....................................................................................................................16
TU1.7.14UT TULinkage between Events and FRU InformationUT .....................................................................................16
TU1.7.15UT TUDifferentiation and Feature ExtensibilityUT ...............................................................................................16
TU1.7.16UT TUSystem InterfacesUT ...................................................................................................................................17
TU1.7.17UT TUOther Messaging InterfacesUT...................................................................................................................17
TU1.7.18UT TUSerial/Modem InterfaceUT ..........................................................................................................................17
TU1.7.19UT TULAN InterfaceUT ........................................................................................................................................18
TU1.7.19.1UT TUPayloadsUT ............................................................................................................................................18
TU1.7.20UT TUSerial Over LAN (SOL)UT .........................................................................................................................18
TU1.7.21UT TUIPMI and ASFUT ........................................................................................................................................19
TU1.7.22UT TULAN AlertingUT .........................................................................................................................................19
TU1.7.23UT TUSerial/Modem Alerting and PagingUT ........................................................................................................19
TU1.7.24UT TUPlatform Event Filtering (PEF)UT ..............................................................................................................20
TU1.7.25UT TUCall Down Lists and Alert PoliciesUT ........................................................................................................20
TU1.7.26UT TUChannel Model, Authentication, Sessions, and UsersUT ............................................................................20
TU1.7.27UT TUStandardized Watchdog TimerUT ...............................................................................................................21
TU1.7.28UT TUStandardized POH CounterUT ....................................................................................................................21
TU1.7.29UT TUFirmware FirewallUT ..................................................................................................................................21
TU1.7.30UT TUCommand and Function DiscoveryUT ........................................................................................................21
TU1.7.31UT TUIPMI Hardware ComponentsUT .................................................................................................................22
TU1.7.32UT TUConfiguration InterfacesUT ........................................................................................................................22
TU1.8UT TUIPMI and BIOSUT .............................................................................................................................................22
TU1.9UT TUSystem Management Software (SMS)UT ..........................................................................................................23
TU1.10UT TUSMI HandlerUT ..................................................................................................................................................23
TU1.11UT TUOverview of Changes from IPMI v1.0UT ..........................................................................................................25
TU2.UT TULogical Management Device TypesUT ................................................................................................. 26
TU3.UT TUBaseboard Management Controller (BMC)UT ..................................................................................... 29
TU3.1UT TURequired BMC FunctionsUT..............................................................................................................................32
TU4.UT TUGeneral Mgmt. Controller Required FunctionsUT............................................................................... 35
TU5.UT TUMessage Interface DescriptionUT ......................................................................................................... 37

Intelligent Platform Management Interface Specification
v
TU5.1UT TUNetwork Function CodesUT...............................................................................................................................37
TU5.2UT TUCompletion CodesUT .........................................................................................................................................39
TU5.3UT TUCompletion Code RequirementsUT ...................................................................................................................41
TU5.3.1UT TUResponse Field Truncation on non-zero Generic Completion CodesUT ....................................................41
TU5.3.2UT TUSummary of Completion Code UseUT .......................................................................................................41
TU5.4UT TUSensor Owner IdentificationUT..........................................................................................................................42
TU5.5UT TUSoftware IDs (SWIDs)UT ..................................................................................................................................42
TU5.6UT TUIsolation from Message ContentUT....................................................................................................................43
TU6.UT TUIPMI Messaging InterfacesUT ................................................................................................................ 44
TU6.1UT TUTerminologyUT ..................................................................................................................................................44
TU6.2UT TUChannel ModelUT ..............................................................................................................................................44
TU6.3UT TUChannel NumbersUT ..........................................................................................................................................45
TU6.4UT TUChannel Protocol TypeUT ..................................................................................................................................45
TU6.5UT TUChannel Medium TypeUT ..................................................................................................................................46
TU6.6UT TUChannel Access ModesUT .................................................................................................................................47
TU6.7UT TULogical ChannelsUT ...........................................................................................................................................48
TU6.8UT TUChannel Privilege LevelsUT ..............................................................................................................................48
TU6.9UT TUUsers & Password SupportUT............................................................................................................................49
TU6.9.1UT TU‘Anonymous Login’ ConventionUT ...........................................................................................................49
TU6.9.2UT TUAnonymous Login StatusUT .......................................................................................................................49
TU6.10UT TUSystem Interface MessagingUT ..........................................................................................................................50
TU6.10.1UT TUBMC Channels and Receive Message QueueUT ........................................................................................50
TU6.10.2UT TUEvent Message BufferUT ............................................................................................................................50
TU6.11UT TUSystem Interface Discovery and Multiple InterfacesUT ....................................................................................51
TU6.12UT TUIPMI SessionsUT................................................................................................................................................52
TU6.12.1UT TUSession-less ConnectionsUT .......................................................................................................................52
TU6.12.2UT TUSingle-session ConnectionsUT ....................................................................................................................52
TU6.12.3UT TUMulti-session ConnectionsUT .....................................................................................................................52
TU6.12.4UT TUPer-Message and User Level Authentication DisablesUT ..........................................................................53
TU6.12.5UT TULink AuthenticationUT ...............................................................................................................................53
TU6.12.6UT TUSummary of Connection CharacteristicsUT ................................................................................................54
TU6.12.7UT TUSession Activation and IPMI Challenge-ResponseUT ................................................................................55
TU6.12.8UT TUSession Sequence NumbersUT....................................................................................................................56
TU6.12.9UT TUSession Sequence Number GenerationUT ..................................................................................................56
TU6.12.10UT TUInbound Session Sequence Number Tracking and HandlingUT .................................................................56
TU6.12.11UT TUOut-of-order Packet HandlingUT ................................................................................................................57
TU6.12.12UT TUOutbound Session Sequence Number Tracking and HandlingUT ..............................................................57
TU6.12.13UT TUSession Inactivity TimeoutsUT ...................................................................................................................57
TU6.12.13.1UT TUAvoiding ‘Slot Stealing’UT ..............................................................................................................58
TU6.12.14UT TUAdditional Session Specifications and CharacteristicsUT ..........................................................................58
TU6.13UT TUBMC Message BridgingUT ................................................................................................................................59
TU6.13.1UT TUBMC LUN 10b RoutingUT .........................................................................................................................60
TU6.13.2UT TUSend Message Command From System InterfaceUT ..................................................................................60
TU6.13.3UT TUSend Message Command with Response TrackingUT ...............................................................................61
TU6.13.4UT TUBridged Request ExampleUT ......................................................................................................................62
TU6.14UT TUMessage Size & Private Bus Transaction Size RequirementsUT .......................................................................64
TU7.UT TUIPMB InterfaceUT .................................................................................................................................... 67
TU7.1UT TUIPMB Access via Master Write-Read commandUT...........................................................................................67
TU7.2UT TUBMC IPMB LUNsUT ........................................................................................................................................67
TU7.3UT TUSending Messages to IPMB from System SoftwareUT......................................................................................67
TU7.4UT TUSending IPMB Messages to System SoftwareUT ..............................................................................................68
TU7.5UT TUTesting for Event Message Buffer SupportUT ...................................................................................................69
TU8.UT TUICMB InterfaceUT .................................................................................................................................... 71
剩余589页未读,继续阅读
netcard5
- 粉丝: 1
- 资源: 4
上传资源 快速赚钱
 我的内容管理
收起
我的内容管理
收起
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

会员权益专享
最新资源
- RTL8188FU-Linux-v5.7.4.2-36687.20200602.tar(20765).gz
- c++校园超市商品信息管理系统课程设计说明书(含源代码) (2).pdf
- 建筑供配电系统相关课件.pptx
- 企业管理规章制度及管理模式.doc
- vb打开摄像头.doc
- 云计算-可信计算中认证协议改进方案.pdf
- [详细完整版]单片机编程4.ppt
- c语言常用算法.pdf
- c++经典程序代码大全.pdf
- 单片机数字时钟资料.doc
- 11项目管理前沿1.0.pptx
- 基于ssm的“魅力”繁峙宣传网站的设计与实现论文.doc
- 智慧交通综合解决方案.pptx
- 建筑防潮设计-PowerPointPresentati.pptx
- SPC统计过程控制程序.pptx
- SPC统计方法基础知识.pptx
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
评论4