LU DECOMPOSITION-BASED ON KEY PPREDISTRIBUTIONSCHEME FOR HETEROGENEOUS
WIRELESS SENSOR NETWORKS
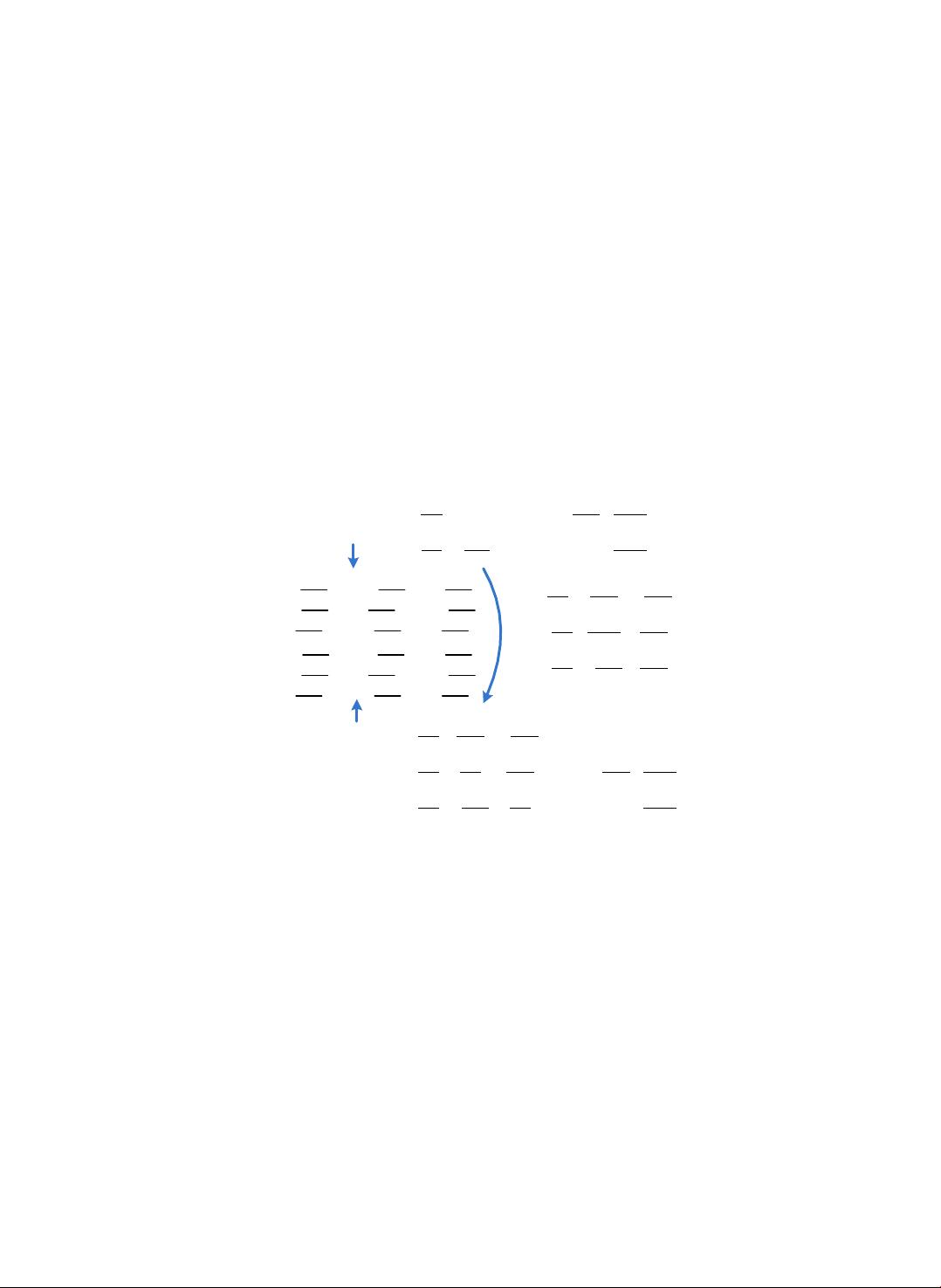
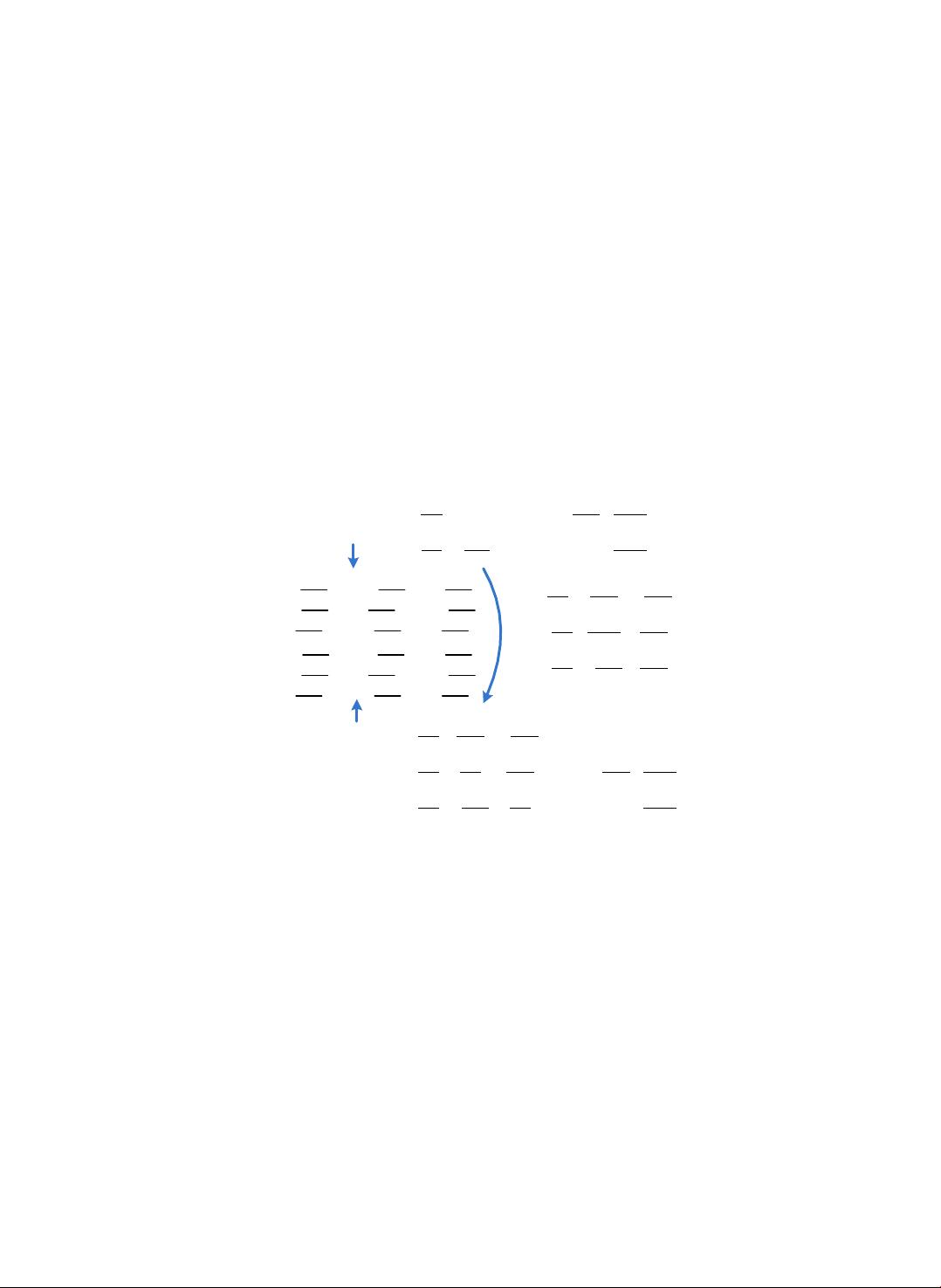
and U to increase the difficulty of exposing secret row vectors. Perturbation technology
can help us to achieve this goal which will change two equal numbers into two different
ones, but keeping them sharing a common part. However, if improper perturbation is
applied, either additional computational or communication overhead is needed to extract
common information. Furthermore, we try to weaken the dependence of shared key on
row vector
by randomly cutting out a part of the common information to establish
shared key, so that the impact of LU attack on our scheme can be weakened too.
Assume that only m sensor nodes
try to establish pairwise key. K, L, U
are three
matrices, K = LU is a symmetric matrix, L is a lower triangular matrix and
U is an upper triangular matrix. If we could find another matrix
whose ele-
ments are as same as K except the last r bits, then any two node,
with key materi-
al
and
with key material
, can extract a common bit-string from
and
. An example is given in Fig.1.
1 0 0 834 573 222
834 573 222
191 6842 12459
573 120 464 1 0 * 0
278 25 40
222 464 76
37 1401 17827
1 0 0
139 1231 48
LU
K
5 119 261
834 2619 3527
2 116 93
417 25361 6124
1 136 85
278 9165 3749
ns
839 119 261
834 573 222
834 2619 3527
839 564 210
569 659 93 6842 12459
569 116 470 * 0
834 656 6124 25 40
219 466 79
73 4591 857 17827
00
278 3982 838 48
W
U
K
1101000010 1000111101 11011110
1000111101 1111000 111010000
11011110 111010000 1001100
1101000111 1000110100 11010010
1000111001 1110100 111010110
11011011 111010010 1001111
Fig. 1. Perturbation Example, r = 4, m = 3
Let
be a function of positive integer k and r, and it will change the last r bits
of k’s binary representation. For example,
could be one of 101100, 101110 and
101111. Parameter r is called noise factor. In Fig.1, K is an initial symmetric matrix.
Elements of
equal to
. Because
and the inverse matrix of U always
exists, it’s easy to get
and
. Matrix ns is referred to as noise matrix,
and its row vector
is called noise vector. It can be found from Fig.1 that
,
when
is transmit public, an adversary could immediately get pairwise keys between
node
and
by ask for exchanging
with
. Hence, the first row of K, L and U
will be discarded by default.
Considering node
and
, if materials assigned to them are
and
respectively, after exchanging their column vector,
can launch LU attack and calculate
and
,
exposed. If materials assigned to these two
nodes are
and
respectively, calculating
can’t help
to