G. Loukas et al.: Cloud-Based Cyber-Physical Intrusion Detection for Vehicles Using Deep Learning
ad hoc networks for the communication between driverless
automobiles, raising the question of what happens when one
of the vehicles misbehaves and launches a cyber attack on
other vehicles on the same network. In this initial work, they
have used NS-2 and mobility simulation tools to evaluate
the performance of an intrusion detection system based on
artificial neural networks. Its input features were some of the
ones typically used in standard network intrusion detection
systems, such as payload sizes, hop counts etc. The same
authors have extended their work to take into account magne-
tometer sensors [32] and gyroscopes [33], and address grey
hole attacks [34].
A common characteristic of all detection mechanisms pro-
vided above, whether local or distributed across multiple
vehicles, is a focus on minimising the processing load, either
by applying lightweight techniques from statistics or by pre-
defining simple behavioural rules that are easy to monitor.
This is because they are all limited by the onboard capabil-
ities of the vehicle at hand. As a result, they usually can-
not leverage modern classification techniques, such as those
currently developed in the field of deep learning. In effect,
the stronger the detection algorithm, the greater the energy
consumption, and in turn the less attractive a solution is for
a resource-constrained vehicle. To overcome this limitation,
we turn to the emerging field of cloud robotics [35]. Our
proposal is to offload the bulk of the processing required to
benefit from deep learning to a more powerful infrastructure
(whether a single server, cloudlet or cloud). By computa-
tion offloading, we refer to the process of executing certain
computational tasks on more resourceful computers which
are not in the user’s immediate computing environment. The
concept has similarities with the online forensics techniques
used for cloud-based detection of malware and tainted data
on Android smartphones [36], [37]. However, instead of
crowd-sourcing detection, we focus on utilising computa-
tional offloading to allow access to deep learning based tech-
niques without the processing and energy cost which would
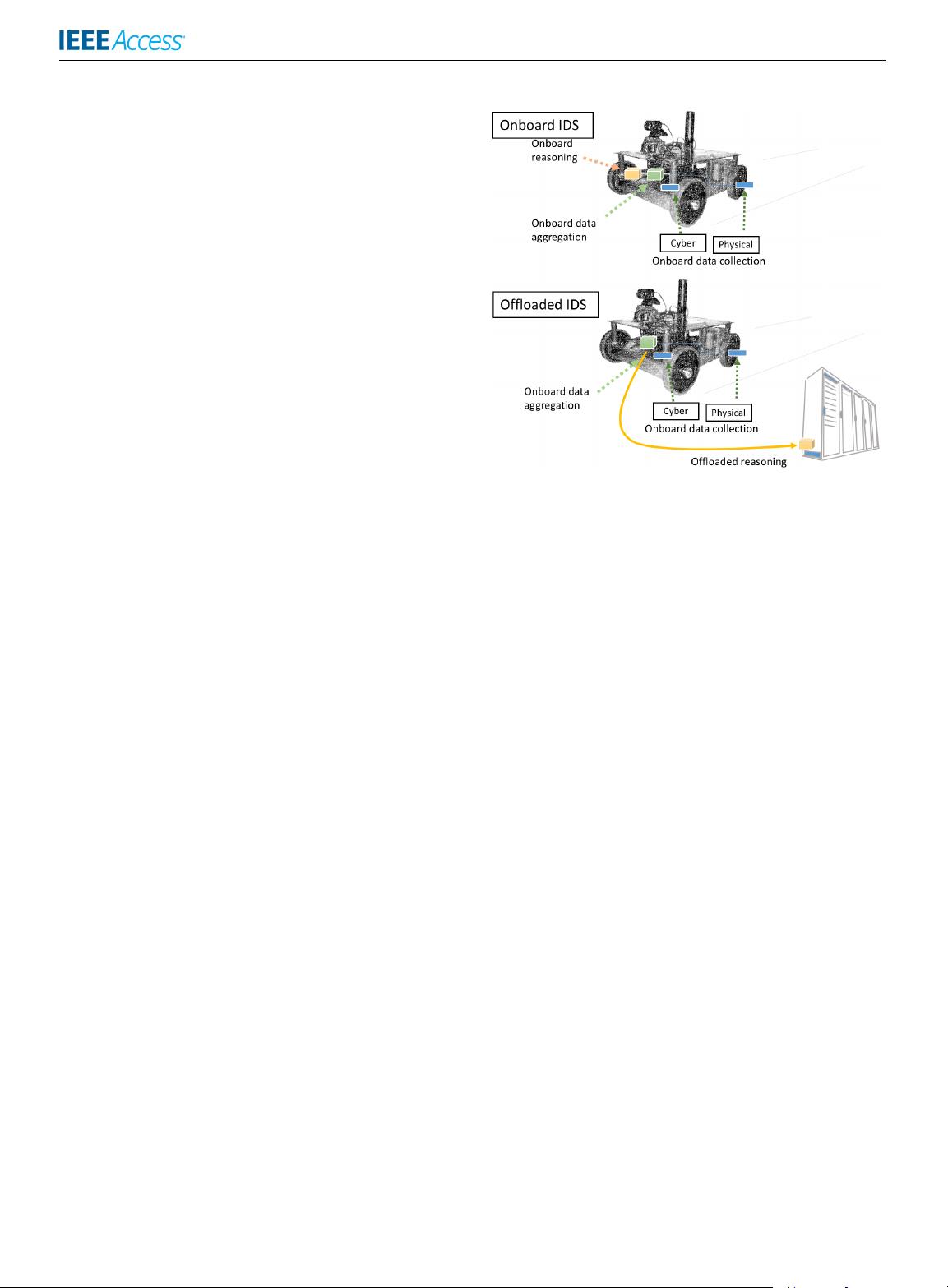
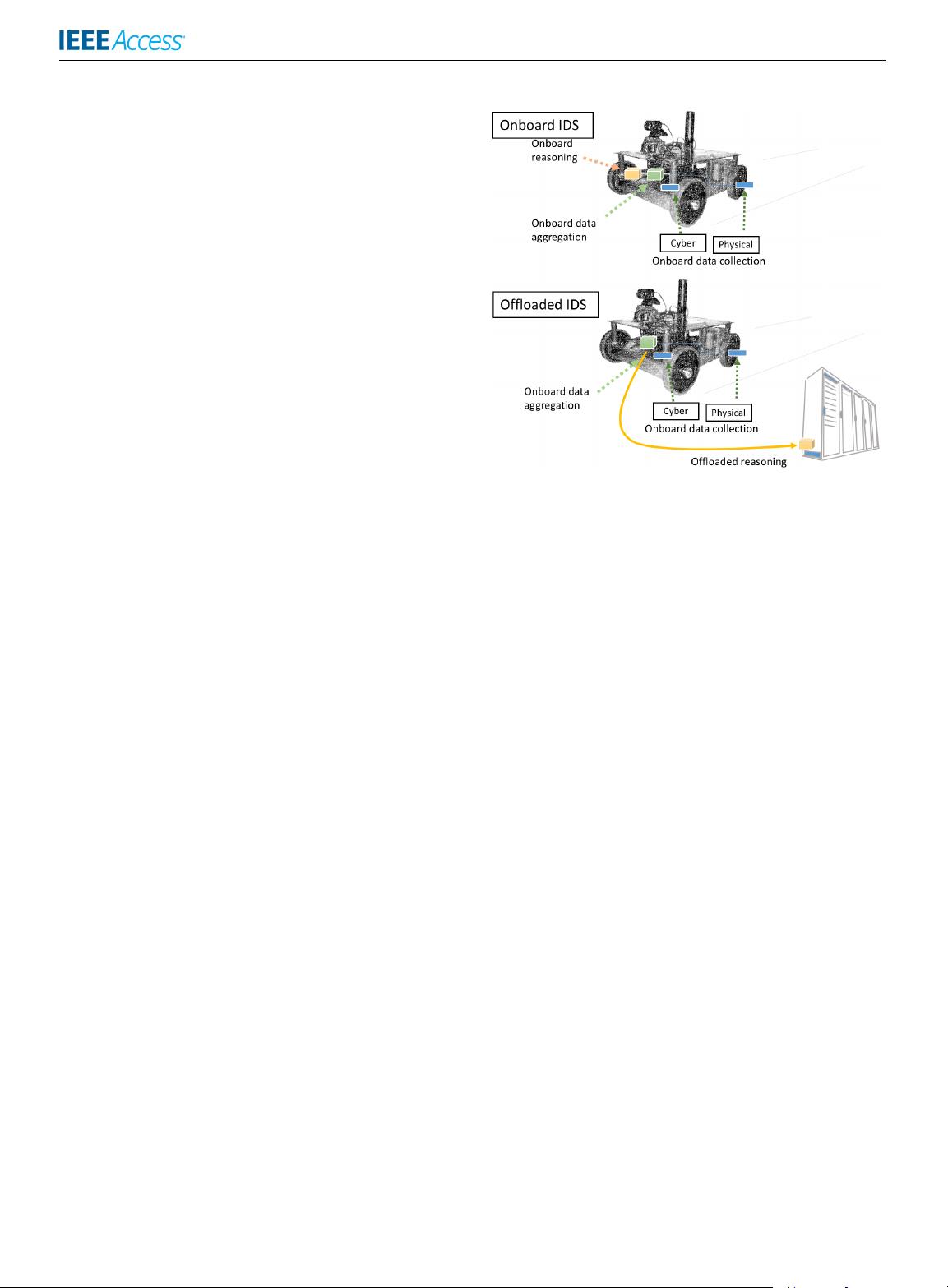
otherwise be prohibitive for a vehicle. Figure 1 illustrates
the conceptual difference between onboard and offloaded
intrusion detection for a vehicle. In both cases, data collec-
tion and aggregation occurs on the vehicle. In the onboard
case, the reasoning (the analysis of the data to determine
whether there is an attack or not) is also on the vehicle. In the
offloaded case, the data aggregated onboard are sent via a
network to a cloud infrastructure or equivalent to perform the
reasoning.
Over the past couple of years, the growing maturity in
deep learning algorithms has led to wider use outside of
its traditional applications in image and natural language
processing, e.g. in detecting malware [38] or rogue certifi-
cates from trusted certificate authorities [39]. It has also been
used to improve intrusion detection accuracy in traditional
computer networks [40], [41], but not for cyber-physical
systems, such as vehicles. An exception is the recent work by
Kang et al. [42], which is geared towards the automotive
industry and detection of attacks on CAN bus. While a
FIGURE 1. Conceptual comparison between onboard and offloaded
intrusion detection for a vehicle.
promising start, the particular work is limited to a generic
command injection attack, which is detected by monitoring
a single type of data source and using a simple and generalist
deep neural network architecture, which does not account for
the overall state of the vehicle through multiple features or for
temporal information (the fact that the impact of the attack
changes over time during the attack). Also, it has been evalu-
ated only in simulation.
III. CONTRIBUTIONS
Here, we progress considerably beyond the state of the art
with the following key contributions:
• We design and evaluate two neural network architectures
for the real-time analysis of multiple sources of data col-
lected periodically onboard the vehicle and representing
both its cyber and physical processes.
• We produce a prototype implementation of deep learn-
ing based intrusion detection for cyber-physical attacks
on a real robotic vehicle, tested for three different types
of attacks and compared against the best-performing
generalist machine learning techniques typically used in
intrusion detection.
• We evaluate both experimentally and using a mathemat-
ical model the practicality of a computational offload-
ing configuration for providing resource-constrained
cyber-physical systems with access to high-end intru-
sion detection.
Note that an early version of this work has been included in
the second author’s PhD dissertation [43]. Here, we expand
through evaluation of two deep learning approaches, a more
practical setup with a single deep learning model for all
attacks rather than individual for each attack, as well as eval-
uation on an unseen attack and an updated literature review.
3494 VOLUME 6, 2018