程序员必修:免费加密基础课程Crypto101简介
需积分: 9 62 浏览量
更新于2024-07-15
收藏 15.53MB PDF 举报
"Crypto101.pdf"是一份面向编程者,特别是初学者的入门级加密学教程。该课程由Laurens Van Houtven在2013年至2017年间创作,并遵循Creative Commons Attribution-NonCommercial 4.0 International (CC BY-NC 4.0) 许可协议。这个许可允许用户在以下条件下自由分享和使用:
1. 分享:可以在任何媒体或格式下复制和分发材料,无需事先申请许可。
2. 适应与创新:你可以根据需要对材料进行改编、混合和扩展,但必须保留原作者的署名和链接,并明确指出是否进行了修改。对于适应性使用,只要不暗示许可方支持或认可你的具体应用即可。
3. 非商业用途:重要的一点是,这份材料不能用于商业目的,这意味着它主要用于教育和研究,而不是用于盈利活动。
4. 无附加限制:除了上述规定的条件外,你不应施加任何法律条款或技术措施来限制其他人按照许可条款合法进行的行为。
值得注意的是,这些权利仅适用于版权受保护的部分,公共领域的内容以及许可允许的使用情况。如果你发现材料中的某些部分已经进入公共领域,或者你的使用得到了额外许可,那么这些限制可能不再适用。
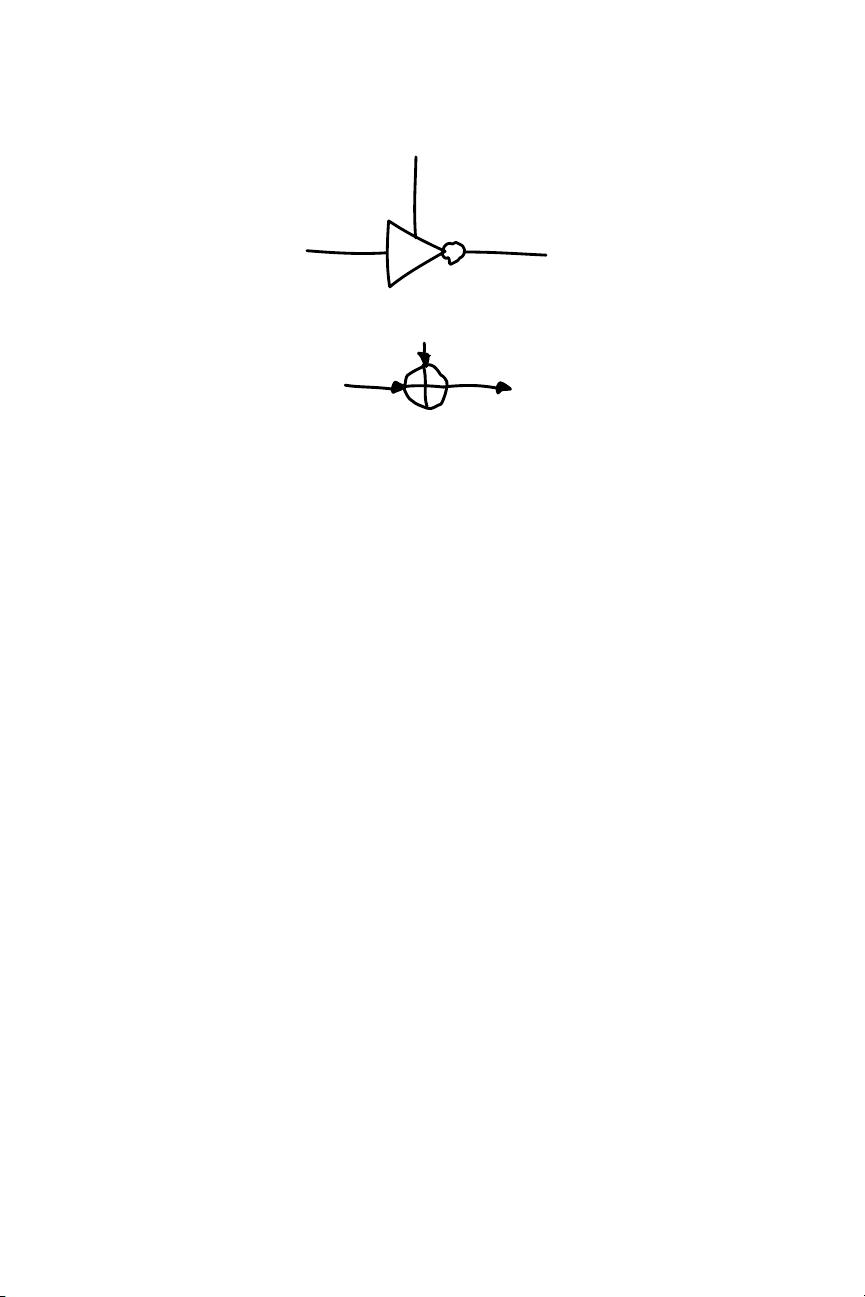
Crypto101.pdf教程为学习者提供了一个基础平台,帮助他们理解加密和解密的基本概念,包括但不限于密码学原理、加密算法(如对称加密、非对称加密、哈希函数等)、数字签名和安全通信协议。通过这门课程,学员可以掌握核心加密技术,为日常编程和信息安全实践打下坚实的基础。同时,理解并尊重版权规则,确保在分享和利用这些教育资源时符合法律要求。
2024-02-03 上传
135 浏览量
2021-08-22 上传
2019-11-25 上传
162 浏览量
2020-05-04 上传
2021-11-16 上传
367 浏览量
Joelhy
- 粉丝: 0
- 资源: 13
最新资源
- Web-projekat:Projekat iz predmeta Web程序
- TDD论坛
- noisia:PostgreSQL有害的工作负载生成器
- dgcabkwu.zip_三维数据分析_三维连通域_时域数据图
- Torpedo
- C#MFC串口通信实现
- speedyplane2247csgo.github.io
- TMP117_51.zip
- opengels2.0颜色混合.zip
- WebLogReader网站日志阅读器 v1.0
- 设备方向:用于检测设备方向和运动的Web组件(带有Polymer)
- 安卓Android图书馆座位占座app设计可导入AndroidStudio
- KSEM 2018 proceedings.zip
- ansoft link(1)
- ArcfaceDemo_CSharp:Arcface2.0 的 C# Demo
- asp.net+sqlserver住哪儿酒店预订网站设计基于html5设计