没有合适的资源?快使用搜索试试~ 我知道了~
首页TCP/IP协议详解:从理论到实战
TCP/IP协议详解:从理论到实战
需积分: 1 0 下载量 126 浏览量
更新于2024-07-31
收藏 11.96MB PDF 举报
"TCP/IP卷1:《TCP/IP详解》是由W. Richard Stevens所著的一本详尽的TCP/IP协议套件指南,首次出版于1993年12月15日,由Addison Wesley出版社发行,ISBN号为0201633469,共600页。本书的独特之处在于它不仅描述了RFC文档中规定这些协议应该如何工作,而且引入了流行诊断工具,让读者能够实际观察协议在不同场景下的行为。 作者通过设计实验,如连接建立、超时重传、数据分片等,然后展示实际结果,使得读者对TCP/IP协议的工作原理和机制有更深入的理解,而不仅仅是理论知识。无论是对于TCP/IP的新手,还是已经有一定基础的读者,这本书都能提供丰富的实践经验和提升应用开发技能的机会。全书分为多个章节,组织有序,适合系统地学习和研究。 《TCP/IP详解》的第一部分——《协议》,旨在引导读者逐步探索TCP/IP的各个组成部分,包括TCP(传输控制协议)和IP(网际协议),以及与其相关的子协议,如ICMP(互联网控制报文协议)、UDP(用户数据报协议)等。书中的介绍不仅涵盖了理论知识,还包含了大量的实例和案例分析,使读者能够在实践中掌握TCP/IP的精髓。 该书的前言部分概述了编写目的和预期读者群体,强调了本书与其他同类书籍的区别,以及它在帮助读者理解和优化基于TCP/IP的应用程序方面的价值。此外,书中还提到了用于测试的系统环境,确保读者能够在一个真实或模拟的环境中验证所学内容。 《TCP/IP详解,卷1:The Protocols》是一本实用且深入的TCP/IP学习宝典,无论你是希望入门还是深化理解,都将从中受益匪浅。"
资源详情
资源推荐

Introduction
This book describes the TCP/IP protocol suite, but from a different perspective than other texts on TCP/IP. Instead
of just describing the protocols and what they do, we'll use a popular diagnostic tool to watch the protocols in
action. Seeing how the protocols operate in varying circumstances provides a greater understanding of how they
work and why certain design decisions were made. It also provides a look into the implementation of the protocols,
without having to wade through thousands of lines of source code.
When networking protocols were being developed in the 1960s through the 1980s, expensive, dedicated hardware
was required to see the packets going "across the wire." Extreme familiarity with the protocols was also required
to comprehend the packets displayed by the hardware. Functionality of the hardware analyzers was limited to that
built in by the hardware designers.
Today this has changed dramatically with the ability of the ubiquitous workstation to monitor a local area network
[Mogul 1990]. Just attach a workstation to your network, run some publicly available software (described in
Appendix A), and watch what goes by on the wire. While many people consider this a tool to be used for
diagnosing network problems, it is also a powerful tool for understanding how the network protocols operate,
which is the goal of this book.
This book is intended for anyone wishing to understand how the TCP/IP protocols operate: programmers writing
network applications, system administrators responsible for maintaining computer systems and networks utilizing
TCP/IP, and users who deal with TCP/IP applications on a daily basis.
Organization of the Book
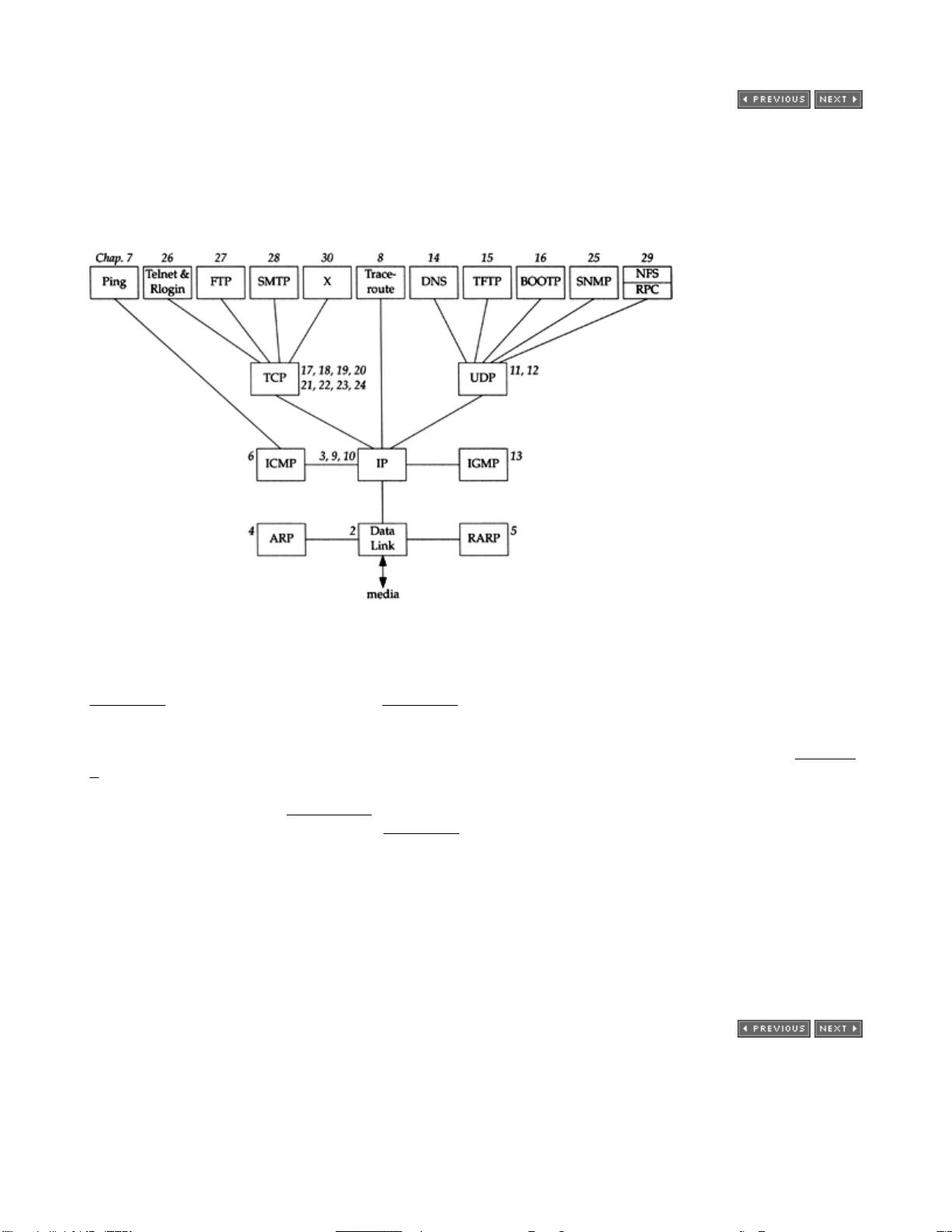
The following figure shows the various protocols and applications that are covered. The italic number by each box
indicates the chapter in which that protocol or application is described.
(Numerous fine points are missing from this figure that will be discussed in the appropriate chapter. For example,
both the DNS and RFC use TCP, which we don't show.)
We take a bottom-up approach to the TCP/IP protocol suite. After providing a basic introduction to TCP/IP in
Chapter 1, we will start at the link layer in Chapter 2 and work our way up the protocol stack. This provides the
required background for later chapters for readers who aren't familiar with TCP/IP or networking in general.
This book also uses a functional approach instead of following a strict bottom-to-top order. For example, Chapter
3 describes the IP layer and the IP header. But there are numerous fields in the IP header that are best described
in the context of an application that uses or is affected by a particular field. Fragmentation, for example, is best
understood in terms of UDP (Chapter 11), the protocol often affected by it. The time-to-live field is fully described
when we look at the Traceroute program in Chapter 8, because this field is the basis for the operation of the
program. Similarly, many features of ICMP are described in the later chapters, in terms of how a particular ICMP
message is used by a protocol or an application.
We also don't want to save all the good stuff until the end, so we describe TCP/IP applications as soon as we
have the foundation to understand them. Ping and Traceroute are described after IP and ICMP have been
discussed. The applications built on UDP (multicasting, the DNS, TFTP, and BOOTP) are described after UDP has
been examined. The TCP applications, however, along with network management, must be saved until the end,
after we've thoroughly described TCP. This text focuses on how these applications use the TCP/IP protocols. We
do not provide all the details on running these applications.
Readers
This book is self-contained and assumes no specific knowledge of networking or TCP/IP. Numerous references
are provided for readers interested in additional details on specific topics.
This book can be used in many ways. It can be used as a self-study reference and covered from start to finish by
someone interested in all the details on the TCP/IP protocol suite. Readers with some TCP/IP background might
want to skip ahead and start with Chapter 7, and then focus on the specific chapters in which they're interested.
Exercises are provided at the end of the chapters, and most solutions are in Appendix D. This is to maximize the
usefulness of the text as a self-study reference.
When used as part of a one- or two-semester course in computer networking, the focus should be on IP
(Chapters 3 and 9), UDP (Chapter 11), and TCP (Chapters 17–24), along with some of the application
chapters.
Many forward and backward references are provided throughout the text, along with a thorough index, to allow
individual chapters to be studied by themselves. A list of all the acronyms used throughout the text, along with the
compound term for the acronym, appears on the inside back covers.
If you have access to a network you are encouraged to obtain the software used in this book (Appendix F) and
experiment on your own. Hands-on experimentation with the protocols will provide the greatest knowledge (and
make it more fun).
Systems Used for Testing
Every example in the book was run on an actual network and the resulting output saved in a file for inclusion in the
text. Figure 1.11 shows a diagram of the different hosts, routers, and networks that are used. (This figure is also
duplicated on the inside front cover for easy reference while reading the book.) This collection of networks is
simple enough that the topology doesn't confuse the examples, and with four systems acting as routers, we can
see the error messages generated by routers.
Most of the systems have a name that indicates the type of software being used: bsdi, svr4, sun, Solaris,
aix, slip, and so on. In this way we can identify the type of software that we're dealing with by looking at the
system name in the printed output.
A wide range of different operating systems and TCP/IP implementations are used:
BSD/386 Version 1.0 from Berkeley Software Design, Inc., on the hosts named bsdi and slip. This
system is derived from the BSD Networking Software, Release 2.0. (We show the lineage of the various
BSD releases in Figure 1.10.)
Unix System V/386 Release 4.0 Version 2.0 from U.H. Corporation, on the host named svr4. This is vanilla
SVR4 and contains the standard implementation of TCP/IP from Lachman Associates used with most
versions of SVR4.
SunOS 4.1.3 from Sun Microsystems, on the host named sun. The SunOS 4.1.x systems are probably the
most widely used TCP/IP implementations. The TCP/IP code is derived from 4.2BSD and 4.3BSD.
Solaris 2.2 from Sun Microsystems, on the host named Solaris. The Solaris 2.x systems have a different
implementation of TCP/IP from the earlier SunOS 4.1.x systems, and from SVR4. (This operating system is
really SunOS 5.2, but is commonly called Solaris 2.2.)
AIX 3.2.2 from IBM on the host named aix. The TCP/IP implementation is based on the 4.3BSD Reno
release.
4.4BSD from the Computer Systems Research Group at the University of California at Berkeley, on the host
vangogh.cs.berkeley.edu. This system has the latest release of TCP/IP from Berkeley. (This system
isn't shown in the figure on the inside front cover, but is reachable across the Internet.)
Although these are all Unix systems, TCP/IP is operating system independent, and is available on almost every
popular non-Unix system. Most of this text also applies to these non-Unix implementations, although some
programs (such as Traceroute) may not be provided on all systems.

Typographical Conventions
When we display interactive input and output we'll show our typed input in a bold font, and the computer
output like this. Comments are added in italics.
bsdi % telnet svr4 discard connect to the discard server
Trying 140.252.13.34... this line and next output by Telnet client
Connected to svr4.
Also, we always include the name of the system as part of the shell prompt ( bsdi in this example) to show on
which host the command was run.
Throughout the text we'll use indented, parenthetical notes such as this to describe historical points or
implementation details.
We sometimes refer to the complete description of a command in the Unix manual as in ifconfig(8). This
notation, the name of the command followed by a number in parentheses, is the normal way of referring to Unix
commands. The number in parentheses is the section number in the Unix manual of the "manual page" for the
command, where additional information can be located. Unfortunately not all Unix systems organize their manuals
the same, with regard to the section numbers used for various groupings of commands. We'll use the BSD-style
section numbers (which is the same for BSD-derived systems such as SunOS 4.1.3), but your manuals may be
organized differently.
剩余846页未读,继续阅读
shuzailiangcang
- 粉丝: 1
- 资源: 2
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

最新资源
- 十种常见电感线圈电感量计算公式详解
- 军用车辆:CAN总线的集成与优势
- CAN总线在汽车智能换档系统中的作用与实现
- CAN总线数据超载问题及解决策略
- 汽车车身系统CAN总线设计与应用
- SAP企业需求深度剖析:财务会计与供应链的关键流程与改进策略
- CAN总线在发动机电控系统中的通信设计实践
- Spring与iBATIS整合:快速开发与比较分析
- CAN总线驱动的整车管理系统硬件设计详解
- CAN总线通讯智能节点设计与实现
- DSP实现电动汽车CAN总线通讯技术
- CAN协议网关设计:自动位速率检测与互连
- Xcode免证书调试iPad程序开发指南
- 分布式数据库查询优化算法探讨
- Win7安装VC++6.0完全指南:解决兼容性与Office冲突
- MFC实现学生信息管理系统:登录与数据库操作
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功