TONG et al.: A DIVERSITY METRIC BASED STUDY ON THE CORRELATION BETWEEN DIVERSITY AND SECURITY
1995
specific attacking scenario. The correlation between diver-
sity and security is demonstrated in a specific attack graph
of the network.
The ultimate goal of diversity measurement is to better
create, maintain, and utilize the diversity to serve the devel-
opment and utilization of security benefits of diversity [2].
However, through the existing work it is difficult to answer
the question of how much diversity is enough to achieve se-
curity, and whether the increase in security is consistent with
the increase in diversity. What’s more, there is a lack of
methods and guidelines for the construction of a diversified
system, especially in face of the limited existing diversity.
In this paper, we focus on the study of the correlation
between the diversity and the security. Through the design
of diversity metrics, we present a diversity measurement for
the diversified systems that use the voting strategy, and then
verifies the effectiveness of the measurement. To study how
the security varies with the diversity, we propose a model
to simulate the attack-defense process for zero-day vulnera-
bilities and diversified systems, in which we also design the
attack failure rate as the indicator of the security. Through
the theoretical analysis and simulations, the correlation of
diversity and security is analyzed in sufficient sample space,
and the causes of the special cases and influences of other
factors are discussed in detail. According to the conclusions
and findings, we provide some suggestions on how to con-
struct a more diversified and securer system.
3. Diversity Metrics Based on Attribute Matrix
When measuring the diversity, we mainly follow the method
from biodiversity as the previous researches did with some
supplements.
The main idea of biodiversity measurement is to mea-
sure the richness of the species, quantity and distribution
of the objects in a certain time and space [25]. Similarly,
the diversity of hardware and software can be divided into
temporal diversity and spatial diversity according to the di-
mensions of time and space. The diversity of an MTD sys-
tem belongs to the temporal diversity, which is achieved in
time dimension, and the use of spatial diversity is reflected
in the intrusion tolerant system represented by systems us-
ing voting strategy, in which the Shannon-Wiener index can
be used as a metric.
To simplify the research, we start the analysis from the
spatial diversity, and leave the temporal diversity for t he fu-
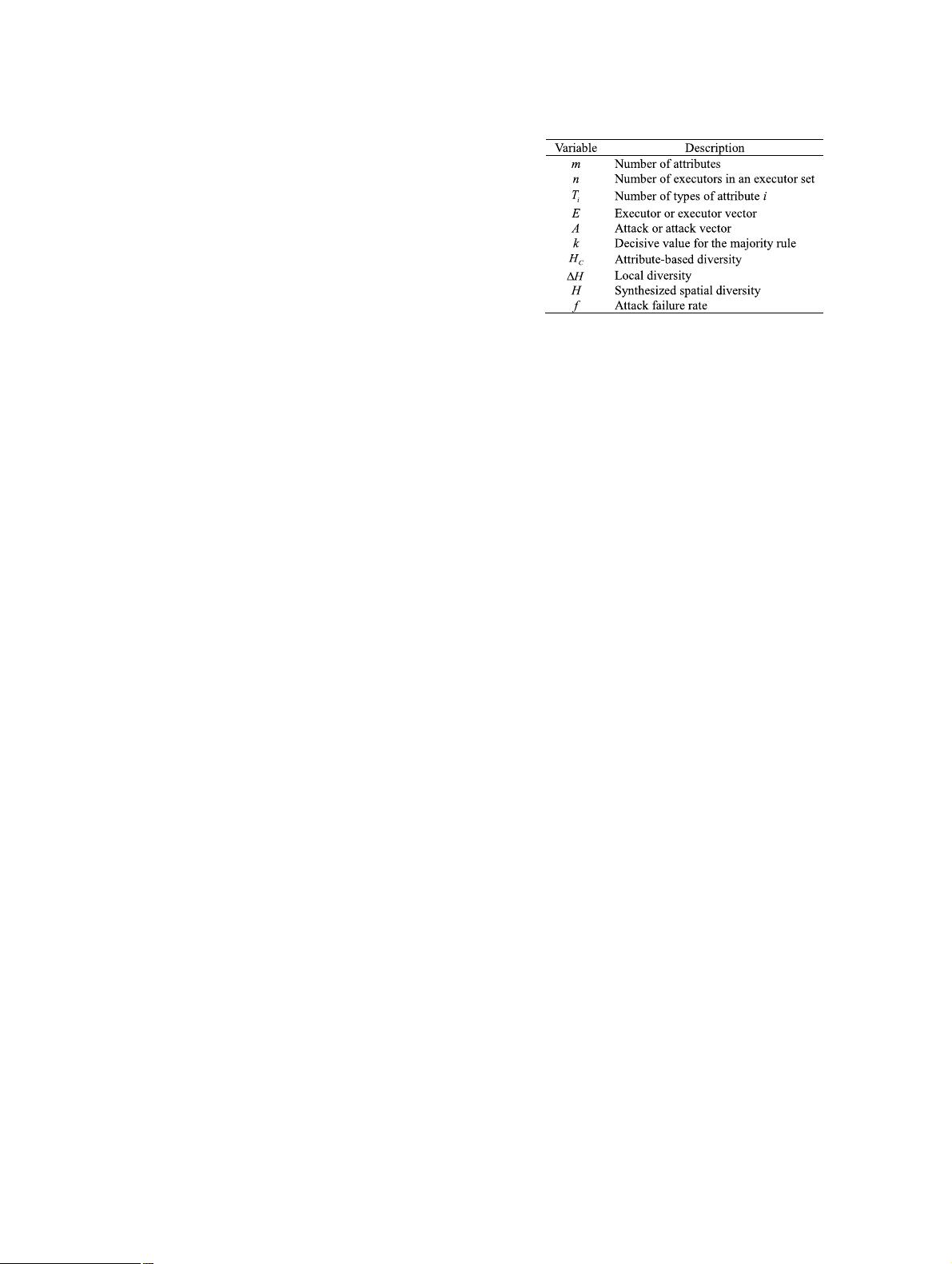
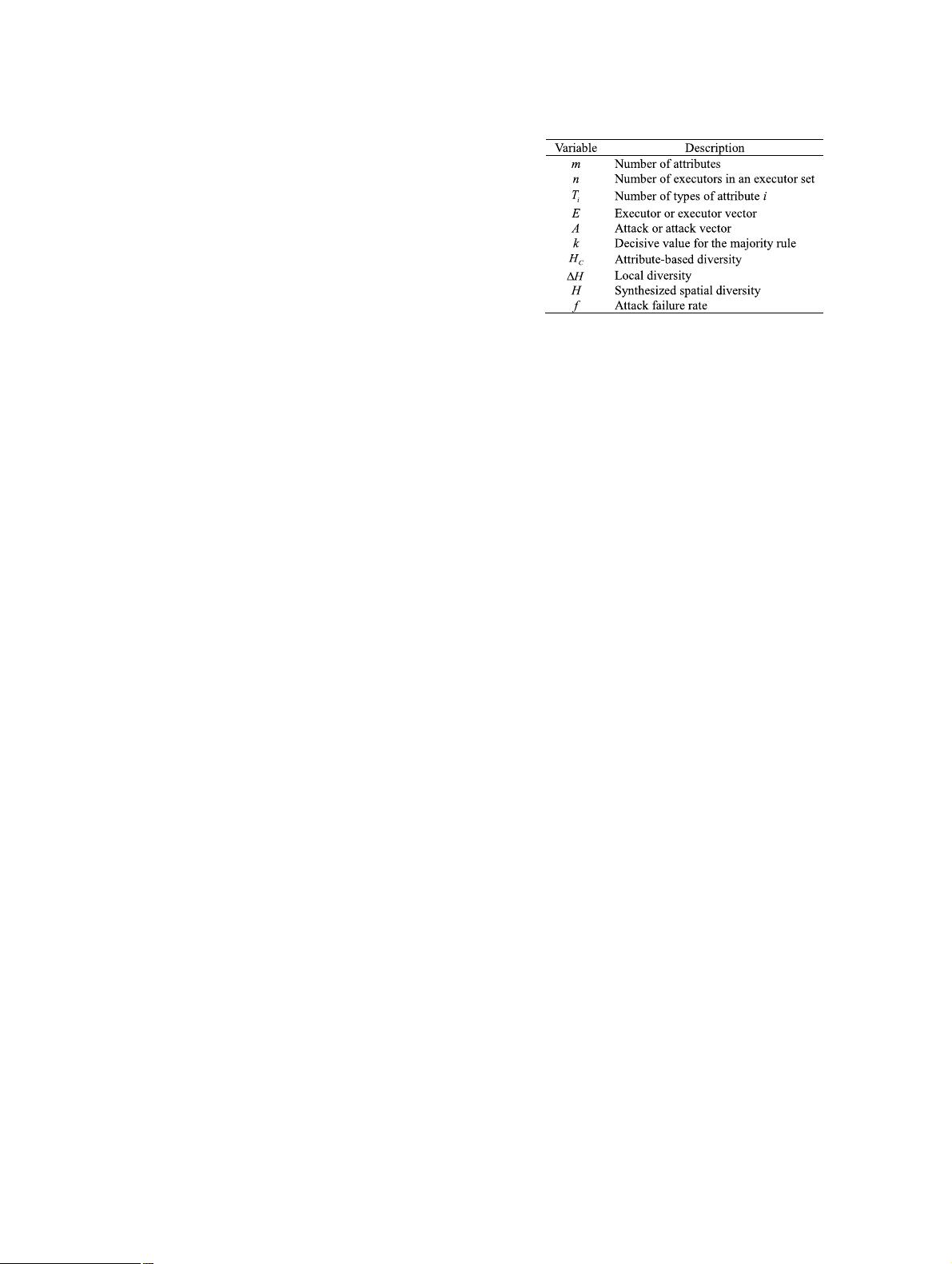
ture work. Table 1 summarizes the names and descriptions
of the main variables defined in this paper.
3.1 Diversified System Attribute Matrix
To abstract the question, we first represent a diversi-
fied system with an attribute matrix. A diversified sys-
tem usually contains redundant, heterogeneous and func-
tionally equivalent components, which are named as ex-
ecutors. For an executor, s ome representative attributes
can be used to distinguish the executor from other
Tab le 1 Summary of the main variable names and descriptions.
functionally equivalent executors, which can form a vector
to represent the executor. For example, if a web server A
is represented by the three attributes of CPU chip, operat-
ing system and server software, then the server’s attribute
vector can be expressed as ( Intel Xeon , CentOS, Apache)
T
.
Further, if another server B is different from A on the op-
erating system, the attribute vector of B can be expressed
as (Intel Xeon, Windows Server, Apache)
T
. Using numbers
to represent different attribute types of the same attribute,
the attribute vectors of server A and B can be expressed
as (1 1 1)
T
and (1 2 1)
T
. In the vectors, different
numbers, which are called as attribute type, are only non-
numerical symbols representing different types of one at-
tribute without the mathematical meaning of size or dis-
tance. The same number may appear in different attribute,
but it is only meaningful under its own attribute, namely, the
same numbers in different attributes have no relationship.
The attributes as well as the types for each attribute rep-
resenting the executors can be chosen according to different
measurement goals by the researchers. As for how to define
two different types, it’s another question to be settled down
in the future research. And the distinguishing of different
types of one attribute is beyond a problem of the computer
science area, which will certainly involve subjective factors.
In this paper, we assume the types of attribute chosen in the
analysis and simulation are different in face of the zero-day
attacks.
Select m attributes to represent the executor set S con-
sisting of n executors, with the type of attribute i of executor
j denoted by c
ij
, then S can be expressed as
⎛
⎜
⎜
⎜
⎜
⎜
⎜
⎜
⎜
⎜
⎜
⎜
⎜
⎜
⎜
⎜
⎝
c
11
c
12
··· c
1n
c
21
c
22
··· c
2n
.
.
.
.
.
.
.
.
.
.
.
.
c
m1
c
m2
··· c
mn
⎞
⎟
⎟
⎟
⎟
⎟
⎟
⎟
⎟
⎟
⎟
⎟
⎟
⎟
⎟
⎟
⎠
.
3.2 Diversity Metrics
Because of the lack of definition and related standards for
the diversity, the proposed metrics and expressions are only
one kind of methods to approximate to the real diversity,
which will be an objective representative in the following
analysis. In addition, the metrics are designed to measure
the differences in the attribute matrix according to some in-