3
A
d
0
r
d
0
A
d
1
r
d
1
A
d
2
k
−1
r
d
2
k
−1
2
k
: 1 MUX
A
s
0
A
s
1
A
s
k−1
o
c
k
n
r
s
(a) (n,k)-MPUF
A
d
0
0
A
d
1
1
A
s
0
A
d
2
0
A
d
3
1
A
s
0
A
d
4
0
A
d
5
1
A
s
0
A
d
6
0
A
d
7
1
A
s
0
0
1
0
1
0
1
A
s
1
A
s
1
A
s
2
o
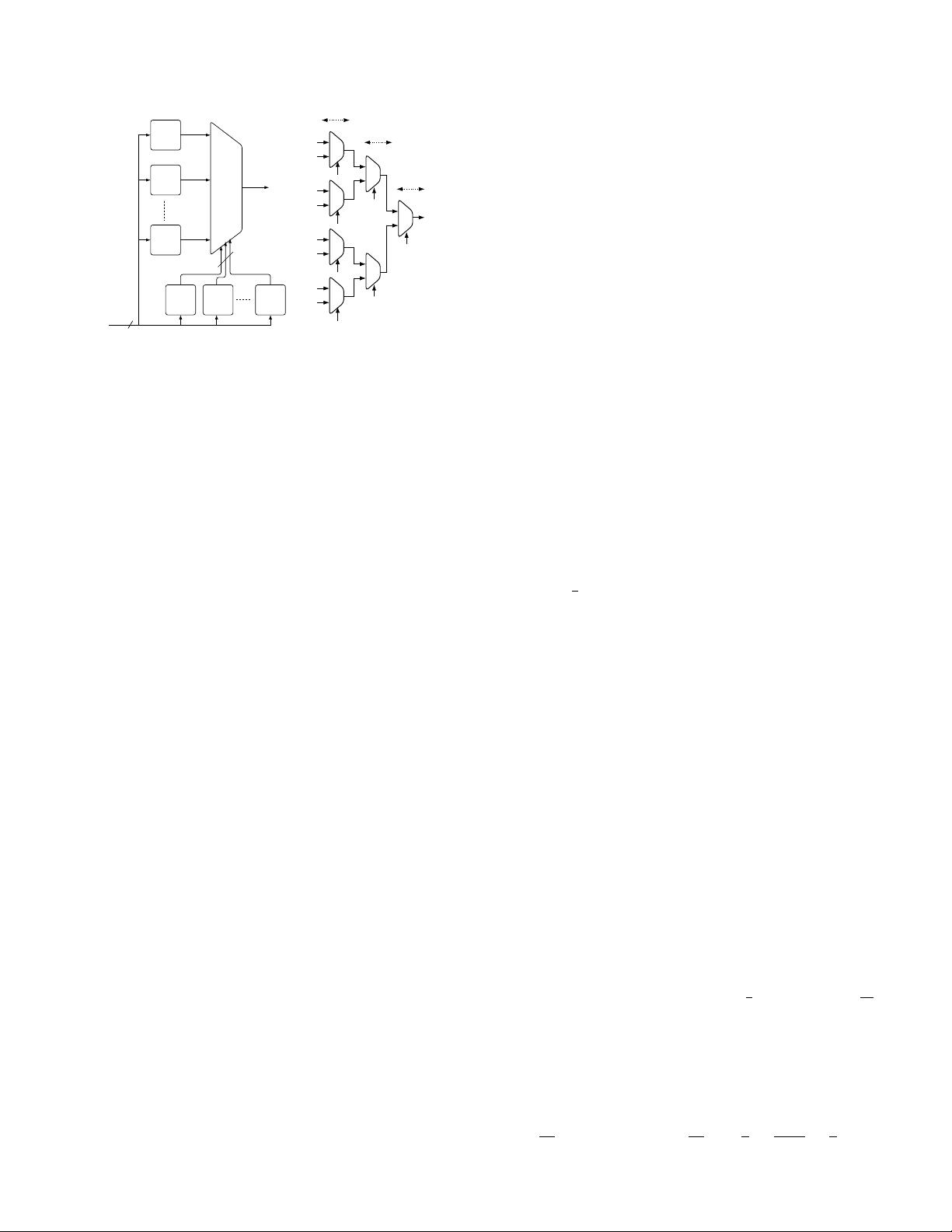
Stage-1
Stage-2
Stage-3
(b) (n,3)-MPUF using 2:1
MUXes
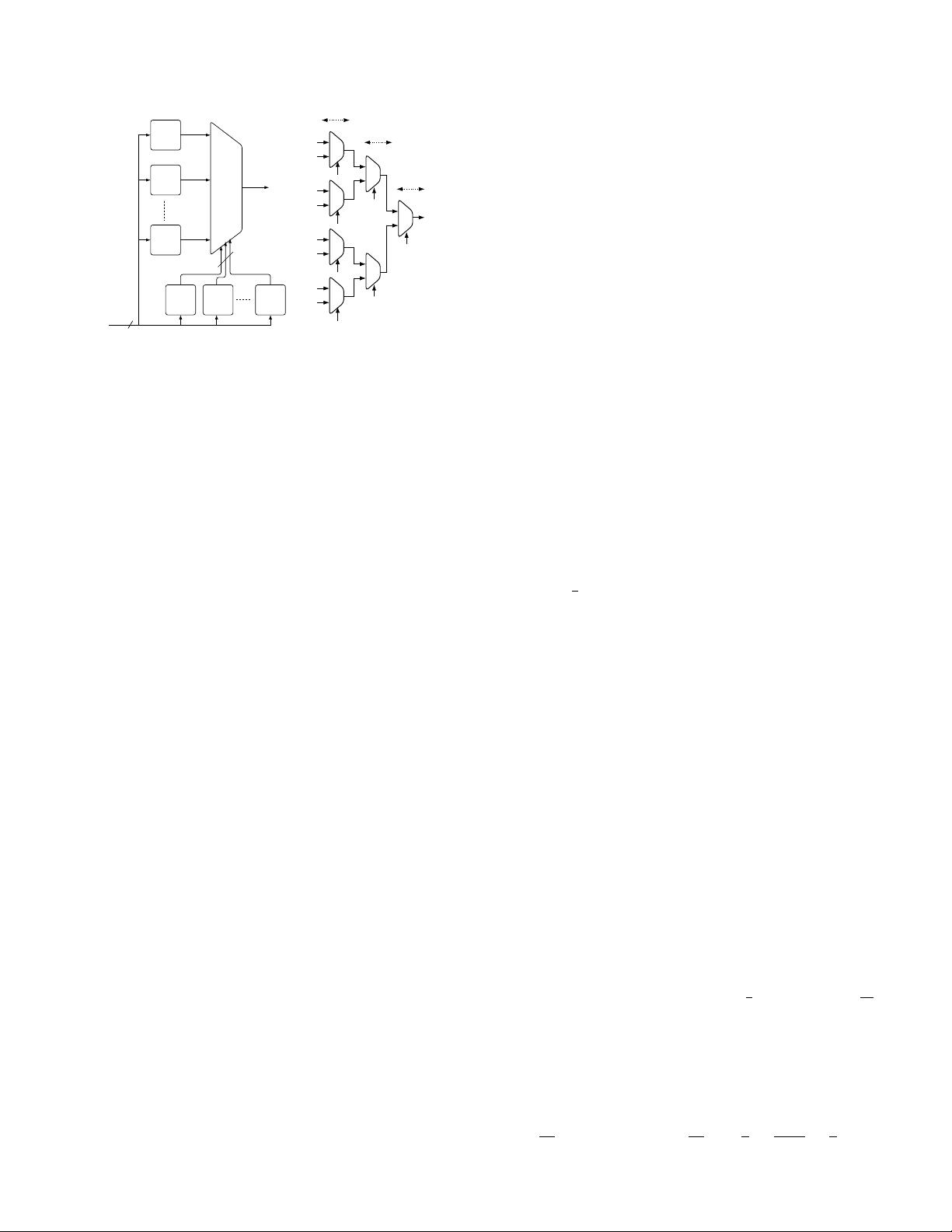
Fig. 1: (a) Architectural overview of an (n, k)-MPUF. It
generates a 1-bit response o to an n-bit challenge c. The
APUF instances A
d
i
, 0 ≤ i ≤ 2
k
− 1 are connected to the
data inputs of MUX, and k-bit selection inputs of MUX
are generated by k APUF instances A
s
j
, 0 ≤ j ≤ k − 1. (b)
An example of (n, 3)-MPUF using 2:1 MUXes.
2) n. this parameter denotes the challenge size of
primitive APUFs as well as MPUF, and all prim-
itive APUFs receive n-bit challenge.
We use the notation (n, k)-MPUF (cf. Fig. 1a) to repre-
sent an MPUF with n-bit challenge and a MUX with k
selection inputs. Let X be a set of 2
k
+k primitive APUFs
used in (n, k)-MPUF, and we partition this set into two
disjoint sets D and S, depending on their usage purpose.
The sets D = {A
d
0
, . . . , A
d
2
k
−1
} and S = {A
s
0
, . . . , A
s
k−1
}
represent the primitive APUFs connected to data inputs
and selection inputs of MUX, respectively. The 1-bit
responses of A
d
i
∈ D and A
s
j
∈ S are denoted by r
d
i
and r
s
j
, respectively.
Since, for a given challenge c, response of MPUF is the
same as response of an APUF in D, we can use a control
circuitry to activate the corresponding data input APUF
only, instead of activating all APUFs in D. Selection of
an APUF from D depends on the concatenated responses
of APUFs in S. We denote the concatenated cumulative
response bits of A
s
j
∈ S by r
s
= r
s
0
| · · · |r
s
k−1
. By the
statement “r
s
= i”, let us denote that i is an unsigned
integer corresponding to binary vector r
s
.
An (k, n)-MPUF instance generates 1-bit response to
an n-bit challenge c, and size of challenge-response space
is 2
n
. There are 2
k
APUFs connected to MUX data
inputs, and their challenge-response pairs (CRPs) form
CRP space C of (n, k)-MPUF. Note that all CRPs of an
individual A
d
i
, i ∈ [0, 2
k
− 1] do not belong to C. Ideally,
data input APUFs A
d
i
, i ∈ [0, 2
k
− 1] contribute equally
to C, and under such conditions, the number of CRPs
of each A
d
i
, i ∈ [0, 2
k
− 1] belonging to C is 2
n
/2
k
. In
practice, we might observe bias in selection of APUFs
A
d
i
, i ∈ [0, 2
k
− 1] due to non-uniform distribution of k-
bit selection inputs generated by A
s
j
∈ S. Hence, data
input APUF instances might not contribute equally to C.
The modeling robustness of an MPUF instance heavily
relies on the fact that an adversary does not have access
to responses of primitive APUFs used in composition,
i.e., all inputs (data and control inputs) of MUX in
MPUF are secret. This security assumption about the
“opaqueness” of design, that denies an adversary the
opportunity to directly observe the internal nodes of a
PUF circuit, is also made for XOR APUF and LSPUF
designs.
4 ADVANTAGES OF MUX BASED COMPOSI-
TION
In light of Section 2.2 on the desirable properties of
an effective composition function, we are in a position
to explain the reasons behind the choice of MUX as
composition operator. Let k be the number of selection
inputs of a MUX; then total number of inputs of a MUX
is m = 2
k
+ k.
4.1 Balancedness
As depicted in Fig. 1a that MPUF instance produces 1-bit
response o to a given n-bit challenge c. This composition
is said to be a balanced composition if distributions of 0’s
and 1’s in response string are uniform, i.e., Pr(o = 0) =
Pr(o = 1) =
1
2
.
We now estimate the probability Pr(o = 0) for (n, k)-
MPUF. Let us consider the response of each APUF
instance A
d
i
, i ∈ [1 : 2
k
−1] to be a binary random variable
A
d
i
. The Pr(A
d
i
= 0) and Pr(A
d
i
= 1) denote the probabili-
ties that PUF instance A
d
i
generates 0 and 1, respectively,
with the obvious constraint Pr(A
d
i
= 0)+Pr(A
d
i
= 1) = 1.
The random variable A
s
corresponds to PUF instance
A
s
= A
s
0
| · · · |A
s
k−1
, and it takes values in [0 : 2
k
−1]. Since
A
d
i
and A
s
are statistically independent, we compute
Pr(o = 0) for (n, k)-MPUF as:
Pr(o = 0) =
2
k
−1
X
i=0
Pr(A
s
= i)Pr(A
d
i
= 0|A
s
= i)
=
2
k
−1
X
i=0
Pr(A
s
= i)Pr(A
d
i
= 0), (1)
where Pr(A
d
i
= 0) = Pr(A
d
i
= 0|A
s
= i) and Pr(A
d
i
=
1) = Pr(A
d
i
= 1|A
s
= i) always hold. Let us assume that
the random variable corresponding to each APUF in-
stance used in composition follows uniform distribution,
and thus Pr(A
d
i
= 0) = Pr(A
d
i
= 1) =
1
2
, Pr(A
s
= j) =
1
2
k
for j ∈ [0 : 2
k
− 1]. Based on these assumptions, we can
rewrite Eq. (1) as follows:
Pr(o = 0) =
2
k
−1
X
i=0
Pr(A
s
= i)Pr(A
d
i
= 0) (2)
=
1
2
k
2
k
−1
X
i=0
Pr(A
d
i
= 0) =
1
2
k
2
k
−1
X
i=0
1
2
=
2
k−1
2
k
=
1
2
.
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助 


 信息提交成功
信息提交成功