没有合适的资源?快使用搜索试试~ 我知道了~
首页破解能力系统误区:安全模型解析与对比
破解能力系统误区:安全模型解析与对比
需积分: 7 0 下载量 125 浏览量
更新于2024-07-18
收藏 906KB PDF 举报
"《能力神话的破灭》(Capability Myths Demolished)是一篇探讨计算机安全领域内关于能力系统存在的三大误解的专业论文。作者Mark S. Miller、Ka-Ping Yee和Jonathan Shapiro针对学生们、研究人员以及实践者中普遍存在的三个误解进行了深入剖析:等价神话(认为访问控制系统与能力系统在形式上等同)、囚禁神话(认为能力系统无法实现严格的限制)以及不可撤销神话(认为基于能力的访问控制无法撤销)。这些误解往往源于对能力安全模型的不同理解。 首先,等价神话模糊了能力系统相对于访问控制系统的优势。实际上,能力模型强调的是细粒度的权限分配和不可篡改性,而访问控制模型则更侧重于预设的权限集。能力系统的优越性在于它们能提供更为灵活且难以被滥用的安全机制。 其次,囚禁神话源于对能力系统能力边界的误解。能力系统并非不能实现隔离或限制,而是通过设计巧妙地将权力分解到最小单元,确保每个主体只能执行其被赋予的任务,从而实现了有效的边界管理。 最后,不可撤销神话源于对能力模型动态性的误解。能力系统中的权限授予通常是可逆的,可以根据需要进行更新和撤销,这与固定不变的访问控制列表形成了鲜明对比。 为了澄清这些误区,论文作者分析了三种不同的能力模型,并定义了一套包含七项安全属性的框架。通过这些属性的考察,他们揭示了纯粹的能力系统在安全性、灵活性和可控性方面的显著优势。通过比较和实证分析,本文旨在促进对能力系统本质的理解,消除误解,推动更有效和安全的信息技术应用。"
资源详情
资源推荐
A Shift in Perspective
Switching from a column-based to a row-based
organization of the access matrix results in at least three
real differences between the models. Visualizing the
access matrix in another way will help make these
differences apparent.
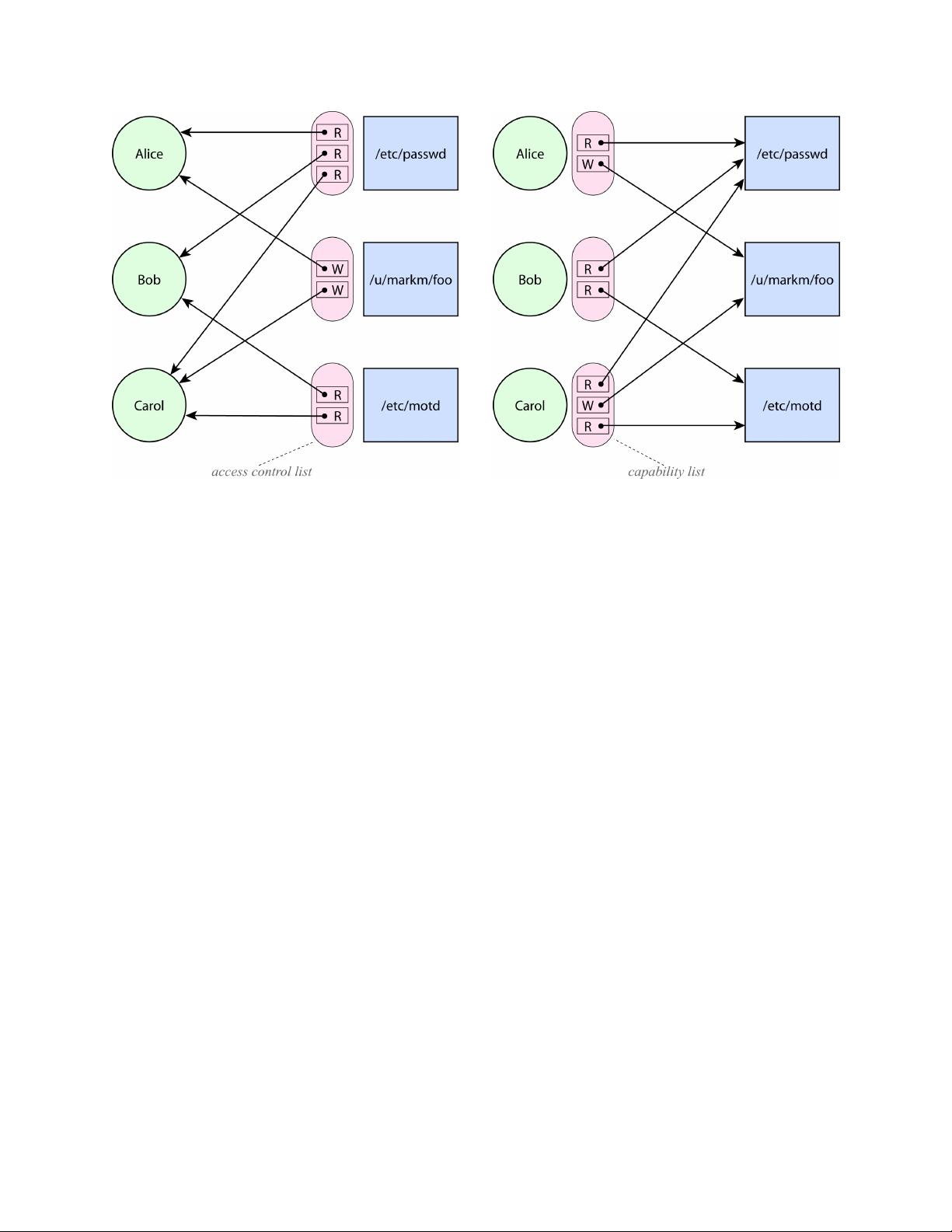
Figure 3 depicts the ACL-as-columns model, this time
explicitly identifying the access control lists. The
circles on the left are subjects, and the boxes on the far
right are resources. Each access control list is shown as
a tall oval next to its corresponding resource. When
access control lists are stored with the resources, they
must contain references to subjects, which are shown as
the leftward-pointing arrows.
Now let us compare this to Figure 4, a depiction of the
capabilities-as-rows model in the same style. Here,
each subject on the left carries a C-list containing
capabilities. Each capability has a reference to a
resource, which we depict as a rightward-pointing
arrow.
By shifting to this new visualization, where the
references are explicitly visible, we see a difference
between the models that was previously obscured: the
direction of the arrows. To see why this matters, let us
consider how subjects and resources refer to each other.
Designation and Authority
First, let us look at the arrows from the subject side.
The ACL model presumes some namespace, such as the
space of filenames, that subjects use to designate
resources. This namespace must necessarily be separate
from the representation of authority in an ACL system,
since the arrows representing authorities point in the
opposite direction. Looking only at the matrix without
considering the direction of the arrows assumes away
the designation problem, which is arguably one of the
deepest problems in computer security. In order to use
a resource designator, subjects must not only come to
know the designator in some fashion; they must also
understand their relationship to the designated resource
in order to determine what actions they should perform
on the resource.
In a capability system, each capability points from a
subject to a resource. Consequently every capability
can serve both to designate which resource to access,
and to provide the authority to perform that access.
This change provides us with the option to avoid
introducing a shared namespace into the foundations of
the model, and thereby avoid the complex issues
involved in managing a shared namespace – issues
rarely acknowledged as a cost of non-capability
models.
We will refer to this distinction as Property A: No
Designation Without Authority. As we have explained,
no ACL system can possibly have this property,
whereas a system described by the row-based view of
the access matrix may or may not have this property.
This property will be relevant to the issue of confused
deputy problems [10], which we will discuss later in
this paper.
Figure 3. The ACLs-as-
columns model, with
references drawn as arrows.
Figure 4. The capabilities-as-
rows model, with
references drawn as arrows.
剩余14页未读,继续阅读
chen3feng
- 粉丝: 3
- 资源: 7
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

最新资源
- C语言快速排序算法的实现与应用
- KityFormula 编辑器压缩包功能解析
- 离线搭建Kubernetes 1.17.0集群教程与资源包分享
- Java毕业设计教学平台完整教程与源码
- 综合数据集汇总:浏览记录与市场研究分析
- STM32智能家居控制系统:创新设计与无线通讯
- 深入浅出C++20标准:四大新特性解析
- Real-ESRGAN: 开源项目提升图像超分辨率技术
- 植物大战僵尸杂交版v2.0.88:新元素新挑战
- 掌握数据分析核心模型,预测未来不是梦
- Android平台蓝牙HC-06/08模块数据交互技巧
- Python源码分享:计算100至200之间的所有素数
- 免费视频修复利器:Digital Video Repair
- Chrome浏览器新版本Adblock Plus插件发布
- GifSplitter:Linux下GIF转BMP的核心工具
- Vue.js开发教程:全面学习资源指南
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功