没有合适的资源?快使用搜索试试~ 我知道了~
首页Tanenbaum第四版:计算机网络基础与通信技术详解
《计算机网络》(Tanenbaum 4th Edition)是一本经典的计算机网络教材,由Andrew S. Tanenbaum撰写,以其全面且深入的讲解而闻名。该书覆盖了从基础到高级的主题,旨在帮助读者理解和掌握网络通信的基本原理和实践。
版权部分强调了作者对知识产权的尊重,同时提及其他畅销书籍,这表明Tanenbaum在计算机网络领域拥有丰富的经验和广泛的认可。关于作者部分,可能会介绍他的专业背景、学术贡献以及他在计算机科学教育领域的影响力。
在前言中,作者可能概述了写作这本书的目的,包括为何选择当前版本进行更新,以及如何针对读者群体进行内容组织和设计。前言还可能讨论了网络技术的最新发展趋势和本书的核心概念。
第一章“Introduction”涵盖了网络的广泛用途,从商务交流、信息共享到物联网应用,强调了网络在现代社会中的核心地位。随后,章节分别探讨了网络硬件,如路由器、交换机等设备;网络软件,涉及操作系统和协议的设计;以及参考模型,如OSI模型和TCP/IP模型,它们是理解网络运作的基础。
接下来的章节详细剖析了物理层,这是数据通信的底层,介绍了传输媒体如双绞线、光纤和无线通信技术,以及卫星通信的原理。此外,还涵盖了电话网络(如PSTN)和移动通信系统的演变,以及电缆电视网络的发展。
第二章“Data Link Layer”重点在于数据链路的设计问题,包括错误检测与纠正方法,以及各种数据链路层协议,如Ethernet和PPP。这部分深入解析了数据帧的传输和冲突解决机制。
第三章“Medium Access Control Sublayer”讨论的是介质访问控制子层,也就是网络中多个设备如何共享资源的问题,特别是如何避免数据包冲突。这一章涵盖的主要内容有信道分配策略和竞争性访问协议。
每一章最后都有一个总结,回顾本章的关键概念和重要技术,方便读者复习和消化所学知识。《Computer Networks Tanenbaum 4ed.pdf》是一本详尽且实用的教材,适合计算机网络学习者从入门到进阶,同时也适合专业人士查阅和更新知识。
On the other hand, maybe the killer application will not be video on demand. Maybe it will be game playing.
Already we have multiperson real-time simulation games, like hide-and-seek in a virtual dungeon, and flight
simulators with the players on one team trying to shoot down the players on the opposing team. If games are
played with goggles and three-dimensional real-time, photographic-quality moving images, we have a kind of
worldwide shared virtual reality.
Our fourth category is electronic commerce in the broadest sense of the term. Home shopping is already popular
and enables users to inspect the on-line catalogs of thousands of companies. Some of these catalogs will soon
provide the ability to get an instant video on any product by just clicking on the product's name. After the
customer buys a product electronically but cannot figure out how to use it, on-line technical support may be
consulted.
Another area in which e-commerce is already happening is access to financial institutions. Many people already
pay their bills, manage their bank accounts, and handle their investments electronically. This will surely grow as
networks become more secure.
One area that virtually nobody foresaw is electronic flea markets (e-flea?). On-line auctions of second-hand
goods have become a massive industry. Unlike traditional e-commerce, which follows the client-server model,
on-line auctions are more of a peer-to-peer system, sort of consumer-to-consumer. Some of these forms of e-
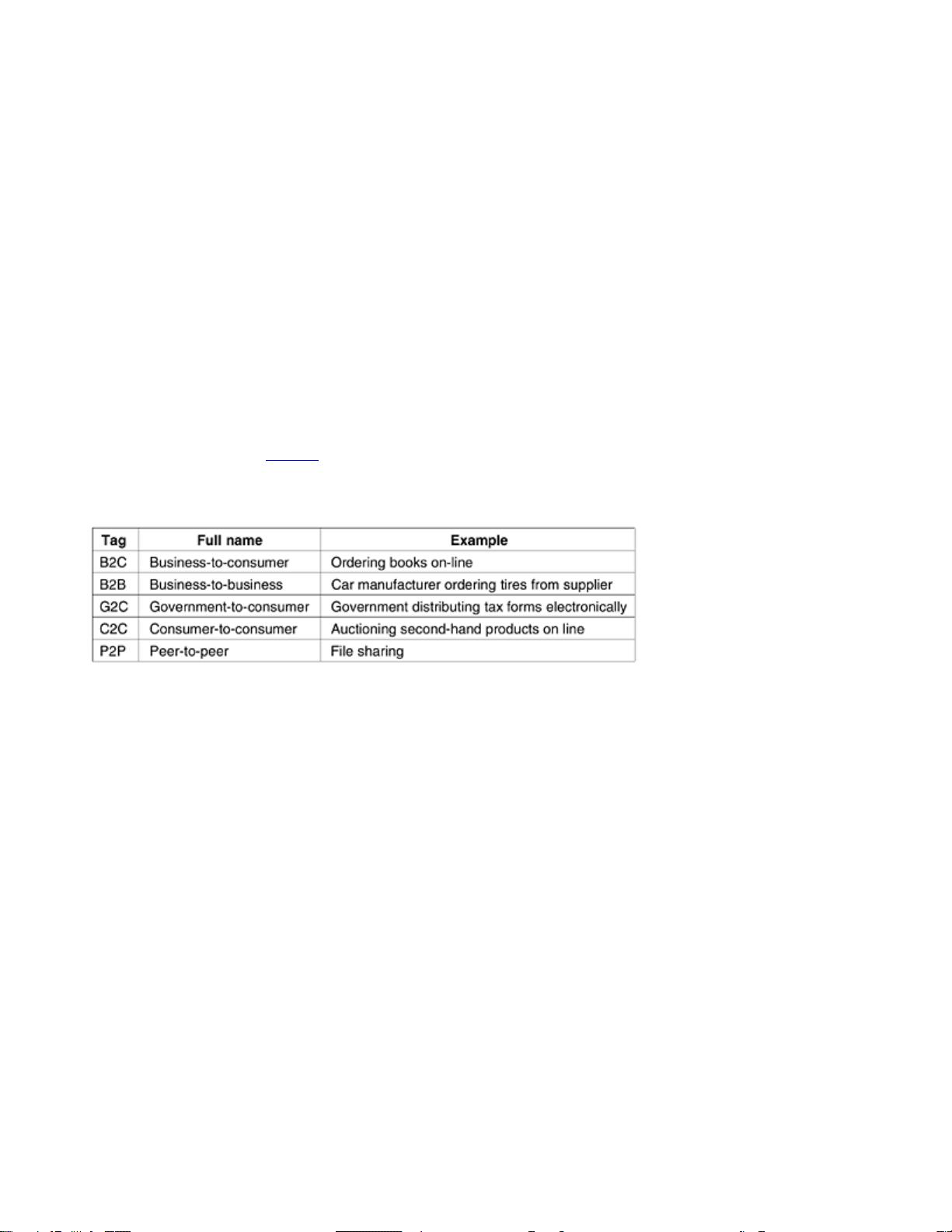
commerce have acquired cute little tags based on the fact that ''to'' and ''2'' are pronounced the same. The most
popular ones are listed in
Fig. 1-4.
Figure 1-4. Some forms of e-commerce.
No doubt the range of uses of computer networks will grow rapidly in the future, and probably in ways no one
can now foresee. After all, how many people in 1990 predicted that teenagers tediously typing short text
messages on mobile phones while riding buses would be an immense money maker for telephone companies in
10 years? But short message service is very profitable.
Computer networks may become hugely important to people who are geographically challenged, giving them the
same access to services as people living in the middle of a big city. Telelearning may radically affect education;
universities may go national or international. Telemedicine is only now starting to catch on (e.g., remote patient
monitoring) but may become much more important. But the killer application may be something mundane, like
using the webcam in your refrigerator to see if you have to buy milk on the way home from work.
1.1.3 Mobile Users
Mobile computers, such as notebook computers and personal digital assistants (PDAs), are one of the fastest-
growing segments of the computer industry. Many owners of these computers have desktop machines back at
the office and want to be connected to their home base even when away from home or en route. Since having a
wired connection is impossible in cars and airplanes, there is a lot of interest in wireless networks. In this section
we will briefly look at some of the uses of wireless networks.
Why would anyone want one? A common reason is the portable office. People on the road often want to use
their portable electronic equipment to send and receive telephone calls, faxes, and electronic mail, surf the Web,
access remote files, and log on to remote machines. And they want to do this from anywhere on land, sea, or air.
For example, at computer conferences these days, the organizers often set up a wireless network in the
conference area. Anyone with a notebook computer and a wireless modem can just turn the computer on and be
connected to the Internet, as though the computer were plugged into a wired network. Similarly, some
16
universities have installed wireless networks on campus so students can sit under the trees and consult the
library's card catalog or read their e-mail.
Wireless networks are of great value to fleets of trucks, taxis, delivery vehicles, and repairpersons for keeping in
contact with home. For example, in many cities, taxi drivers are independent businessmen, rather than being
employees of a taxi company. In some of these cities, the taxis have a display the driver can see. When a
customer calls up, a central dispatcher types in the pickup and destination points. This information is displayed
on the drivers' displays and a beep sounds. The first driver to hit a button on the display gets the call.
Wireless networks are also important to the military. If you have to be able to fight a war anywhere on earth on
short notice, counting on using the local networking infrastructure is probably not a good idea. It is better to bring
your own.
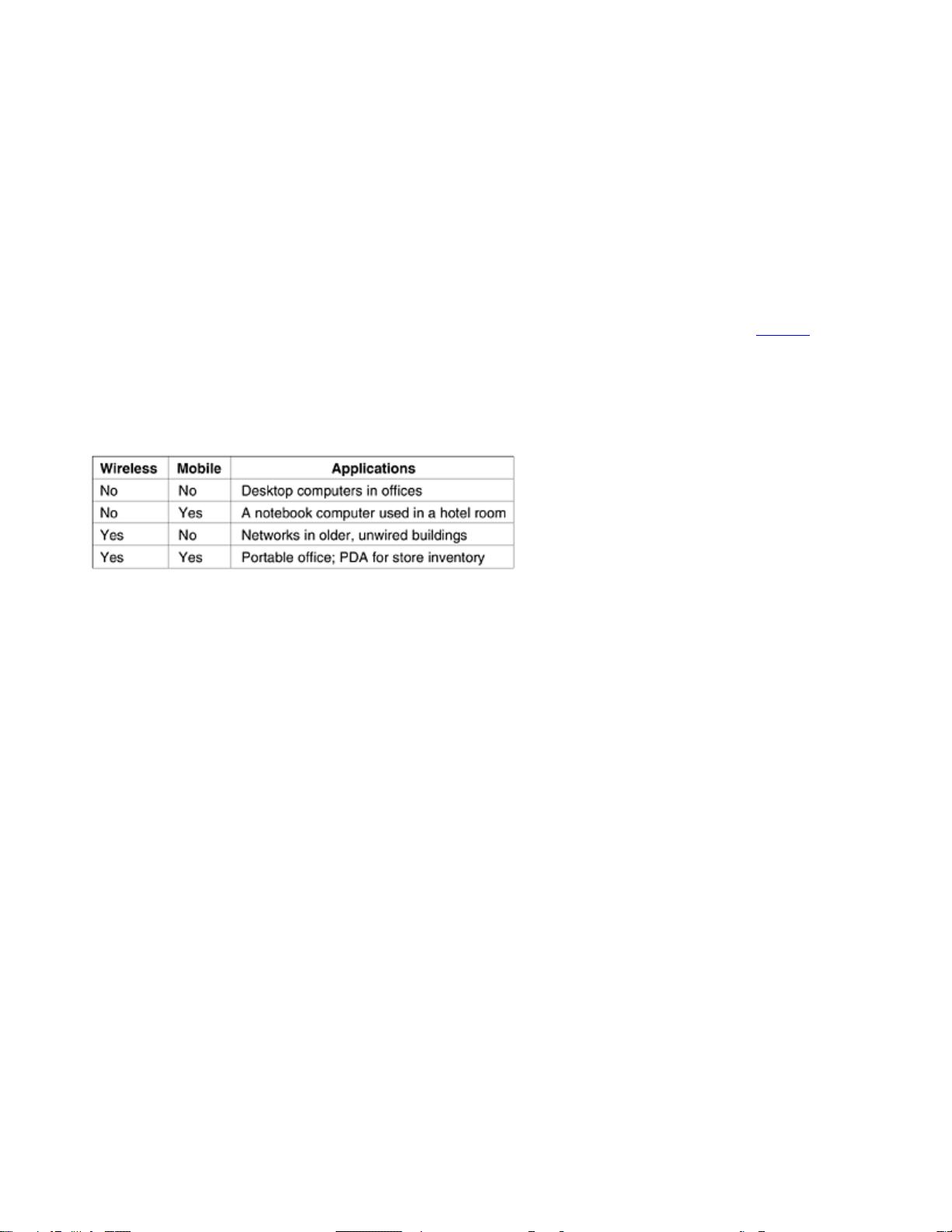
Although wireless networking and mobile computing are often related, they are not identical, as
Fig. 1-5 shows.
Here we see a distinction between
fixed wireless and mobile wireless. Even notebook computers are sometimes
wired. For example, if a traveler plugs a notebook computer into the telephone jack in a hotel room, he has
mobility without a wireless network.
Figure 1-5. Combinations of wireless networks and mobile computing.
On the other hand, some wireless computers are not mobile. An important example is a company that owns an
older building lacking network cabling, and which wants to connect its computers. Installing a wireless network
may require little more than buying a small box with some electronics, unpacking it, and plugging it in. This
solution may be far cheaper than having workmen put in cable ducts to wire the building.
But of course, there are also the true mobile, wireless applications, ranging from the portable office to people
walking around a store with a PDA doing inventory. At many busy airports, car rental return clerks work in the
parking lot with wireless portable computers. They type in the license plate number of returning cars, and their
portable, which has a built-in printer, calls the main computer, gets the rental information, and prints out the bill
on the spot.
As wireless technology becomes more widespread, numerous other applications are likely to emerge. Let us
take a quick look at some of the possibilities. Wireless parking meters have advantages for both users and city
governments. The meters could accept credit or debit cards with instant verification over the wireless link. When
a meter expires, it could check for the presence of a car (by bouncing a signal off it) and report the expiration to
the police. It has been estimated that city governments in the U.S. alone could collect an additional $10 billion
this way (Harte et al., 2000). Furthermore, better parking enforcement would help the environment, as drivers
who knew their illegal parking was sure to be caught might use public transport instead.
Food, drink, and other vending machines are found everywhere. However, the food does not get into the
machines by magic. Periodically, someone comes by with a truck to fill them. If the vending machines issued a
wireless report once a day announcing their current inventories, the truck driver would know which machines
needed servicing and how much of which product to bring. This information could lead to more efficient route
planning. Of course, this information could be sent over a standard telephone line as well, but giving every
vending machine a fixed telephone connection for one call a day is expensive on account of the fixed monthly
charge.
Another area in which wireless could save money is utility meter reading. If electricity, gas, water, and other
meters in people's homes were to report usage over a wireless network, there would be no need to send out
meter readers. Similarly, wireless smoke detectors could call the fire department instead of making a big noise
17

(which has little value if no one is home). As the cost of both the radio devices and the air time drops, more and
more measurement and reporting will be done with wireless networks.
A whole different application area for wireless networks is the expected merger of cell phones and PDAs into tiny
wireless computers. A first attempt was tiny wireless PDAs that could display stripped-down Web pages on their
even tinier screens. This system, called
WAP 1.0 (Wireless Application Protocol) failed, mostly due to the
microscopic screens, low bandwidth, and poor service. But newer devices and services will be better with WAP
2.0.
One area in which these devices may excel is called
m-commerce (mobile-commerce) (Senn, 2000). The driving
force behind this phenomenon consists of an amalgam of wireless PDA manufacturers and network operators
who are trying hard to figure out how to get a piece of the e-commerce pie. One of their hopes is to use wireless
PDAs for banking and shopping. One idea is to use the wireless PDAs as a kind of electronic wallet, authorizing
payments in stores, as a replacement for cash and credit cards. The charge then appears on the mobile phone
bill. From the store's point of view, this scheme may save them most of the credit card company's fee, which can
be several percent. Of course, this plan may backfire, since customers in a store might use their PDAs to check
out competitors' prices before buying. Worse yet, telephone companies might offer PDAs with bar code readers
that allow a customer to scan a product in a store and then instantaneously get a detailed report on where else it
can be purchased and at what price.
Since the network operator knows where the user is, some services are intentionally location dependent. For
example, it may be possible to ask for a nearby bookstore or Chinese restaurant. Mobile maps are another
candidate. So are very local weather forecasts (''When is it going to stop raining in my backyard?''). No doubt
many other applications appear as these devices become more widespread.
One huge thing that m-commerce has going for it is that mobile phone users are accustomed to paying for
everything (in contrast to Internet users, who expect everything to be free). If an Internet Web site charged a fee
to allow its customers to pay by credit card, there would be an immense howling noise from the users. If a mobile
phone operator allowed people to pay for items in a store by using the phone and then tacked on a fee for this
convenience, it would probably be accepted as normal. Time will tell.
A little further out in time are personal area networks and wearable computers. IBM has developed a watch that
runs Linux (including the X11 windowing system) and has wireless connectivity to the Internet for sending and
receiving e-mail (Narayanaswami et al., 2002). In the future, people may exchange business cards just by
exposing their watches to each other. Wearable wireless computers may give people access to secure rooms
the same way magnetic stripe cards do now (possibly in combination with a PIN code or biometric
measurement). These watches may also be able to retrieve information relevant to the user's current location
(e.g., local restaurants). The possibilities are endless.
Smart watches with radios have been part of our mental space since their appearance in the Dick Tracy comic
strip in 1946. But smart dust? Researchers at Berkeley have packed a wireless computer into a cube 1 mm on
edge (Warneke et al., 2001). Potential applications include tracking inventory, packages, and even small birds,
rodents, and insects.
1.1.4 Social Issues
The widespread introduction of networking has introduced new social, ethical, and political problems. Let us just
briefly mention a few of them; a thorough study would require a full book, at least. A popular feature of many
networks are newsgroups or bulletin boards whereby people can exchange messages with like-minded
individuals. As long as the subjects are restricted to technical topics or hobbies like gardening, not too many
problems will arise.
The trouble comes when newsgroups are set up on topics that people actually care about, like politics, religion,
or sex. Views posted to such groups may be deeply offensive to some people. Worse yet, they may not be
politically correct. Furthermore, messages need not be limited to text. High-resolution color photographs and
even short video clips can now easily be transmitted over computer networks. Some people take a live-and-let-
live view, but others feel that posting certain material (e.g., attacks on particular countries or religions,
18

pornography, etc.) is simply unacceptable and must be censored. Different countries have different and
conflicting laws in this area. Thus, the debate rages.
People have sued network operators, claiming that they are responsible for the contents of what they carry, just
as newspapers and magazines are. The inevitable response is that a network is like a telephone company or the
post office and cannot be expected to police what its users say. Stronger yet, were network operators to censor
messages, they would likely delete everything containing even the slightest possibility of them being sued, and
thus violate their users' rights to free speech. It is probably safe to say that this debate will go on for a while.
Another fun area is employee rights versus employer rights. Many people read and write e-mail at work. Many
employers have claimed the right to read and possibly censor employee messages, including messages sent
from a home computer after work. Not all employees agree with this.
Even if employers have power over employees, does this relationship also govern universities and students?
How about high schools and students? In 1994, Carnegie-Mellon University decided to turn off the incoming
message stream for several newsgroups dealing with sex because the university felt the material was
inappropriate for minors (i.e., those few students under 18). The fallout from this event took years to settle.
Another key topic is government versus citizen. The FBI has installed a system at many Internet service
providers to snoop on all incoming and outgoing e-mail for nuggets of interest to it (Blaze and Bellovin, 2000;
Sobel, 2001; and Zacks, 2001). The system was originally called
Carnivore but bad publicity caused it to be
renamed to the more innocent-sounding DCS1000. But its goal is still to spy on millions of people in the hope of
finding information about illegal activities. Unfortunately, the Fourth Amendment to the U.S. Constitution prohibits
government searches without a search warrant. Whether these 54 words, written in the 18th century, still carry
any weight in the 21st century is a matter that may keep the courts busy until the 22nd century.
The government does not have a monopoly on threatening people's privacy. The private sector does its bit too.
For example, small files called cookies that Web browsers store on users' computers allow companies to track
users' activities in cyberspace and also may allow credit card numbers, social security numbers, and other
confidential information to leak all over the Internet (Berghel, 2001).
Computer networks offer the potential for sending anonymous messages. In some situations, this capability may
be desirable. For example, it provides a way for students, soldiers, employees, and citizens to blow the whistle
on illegal behavior on the part of professors, officers, superiors, and politicians without fear of reprisals. On the
other hand, in the United States and most other democracies, the law specifically permits an accused person the
right to confront and challenge his accuser in court. Anonymous accusations cannot be used as evidence.
In short, computer networks, like the printing press 500 years ago, allow ordinary citizens to distribute their views
in different ways and to different audiences than were previously possible. This new-found freedom brings with it
many unsolved social, political, and moral issues.
Along with the good comes the bad. Life seems to be like that. The Internet makes it possible to find information
quickly, but a lot of it is ill-informed, misleading, or downright wrong. The medical advice you plucked from the
Internet may have come from a Nobel Prize winner or from a high school dropout. Computer networks have also
introduced new kinds of antisocial and criminal behavior. Electronic junk mail (spam) has become a part of life
because people have collected millions of e-mail addresses and sell them on CD-ROMs to would-be marketeers.
E-mail messages containing active content (basically programs or macros that execute on the receiver's
machine) can contain viruses that wreak havoc.
Identity theft is becoming a serious problem as thieves collect enough information about a victim to obtain get
credit cards and other documents in the victim's name. Finally, being able to transmit music and video digitally
has opened the door to massive copyright violations that are hard to catch and enforce.
A lot of these problems could be solved if the computer industry took computer security seriously. If all
messages were encrypted and authenticated, it would be harder to commit mischief. This technology is well
established and we will study it in detail in
Chap. 8. The problem is that hardware and software vendors know
that putting in security features costs money and their customers are not demanding such features. In addition, a
substantial number of the problems are caused by buggy software, which occurs because vendors keep adding
19

more and more features to their programs, which inevitably means more code and thus more bugs. A tax on new
features might help, but that is probably a tough sell in some quarters. A refund for defective software might be
nice, except it would bankrupt the entire software industry in the first year.
1.2 Network Hardware
It is now time to turn our attention from the applications and social aspects of networking (the fun stuff) to the
technical issues involved in network design (the work stuff). There is no generally accepted taxonomy into which
all computer networks fit, but two dimensions stand out as important: transmission technology and scale. We will
now examine each of these in turn.
Broadly speaking, there are two types of transmission technology that are in widespread use. They are as
follows:
1. Broadcast links.
2. Point-to-point links.
Broadcast networks have a single communication channel that is shared by all the machines on the network.
Short messages, called
packets in certain contexts, sent by any machine are received by all the others. An
address field within the packet specifies the intended recipient. Upon receiving a packet, a machine checks the
address field. If the packet is intended for the receiving machine, that machine processes the packet; if the
packet is intended for some other machine, it is just ignored.
As an analogy, consider someone standing at the end of a corridor with many rooms off it and shouting ''Watson,
come here. I want you.'' Although the packet may actually be received (heard) by many people, only Watson
responds. The others just ignore it. Another analogy is an airport announcement asking all flight 644 passengers
to report to gate 12 for immediate boarding.
Broadcast systems generally also allow the possibility of addressing a packet to all destinations by using a
special code in the address field. When a packet with this code is transmitted, it is received and processed by
every machine on the network. This mode of operation is called
broadcasting. Some broadcast systems also
support transmission to a subset of the machines, something known as
multicasting. One possible scheme is to
reserve one bit to indicate multicasting. The remaining
n - 1 address bits can hold a group number. Each
machine can ''subscribe'' to any or all of the groups. When a packet is sent to a certain group, it is delivered to all
machines subscribing to that group.
In contrast, point-to-point networks consist of many connections between individual pairs of machines. To go
from the source to the destination, a packet on this type of network may have to first visit one or more
intermediate machines. Often multiple routes, of different lengths, are possible, so finding good ones is important
in point-to-point networks. As a general rule (although there are many exceptions), smaller, geographically
localized networks tend to use broadcasting, whereas larger networks usually are point-to-point. Point-to-point
transmission with one sender and one receiver is sometimes called
unicasting.
An alternative criterion for classifying networks is their scale. In
Fig. 1-6 we classify multiple processor systems
by their physical size. At the top are the personal area networks, networks that are meant for one person. For
example, a wireless network connecting a computer with its mouse, keyboard, and printer is a personal area
network. Also, a PDA that controls the user's hearing aid or pacemaker fits in this category. Beyond the personal
area networks come longer-range networks. These can be divided into local, metropolitan, and wide area
networks. Finally, the connection of two or more networks is called an internetwork. The worldwide Internet is a
well-known example of an internetwork. Distance is important as a classification metric because different
techniques are used at different scales. In this book we will be concerned with networks at all these scales.
Below we give a brief introduction to network hardware.
Figure 1-6. Classification of interconnected processors by scale.
20
剩余673页未读,继续阅读
2023-06-22 上传
2023-05-26 上传
2023-06-10 上传
2024-07-13 上传
2023-09-02 上传
2023-09-29 上传
lololsss
- 粉丝: 0
- 资源: 1
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

最新资源
- 新型智能电加热器:触摸感应与自动温控技术
- 社区物流信息管理系统的毕业设计实现
- VB门诊管理系统设计与实现(附论文与源代码)
- 剪叉式高空作业平台稳定性研究与创新设计
- DAMA CDGA考试必备:真题模拟及章节重点解析
- TaskExplorer:全新升级的系统监控与任务管理工具
- 新型碎纸机进纸间隙调整技术解析
- 有腿移动机器人动作教学与技术存储介质的研究
- 基于遗传算法优化的RBF神经网络分析工具
- Visual Basic入门教程完整版PDF下载
- 海洋岸滩保洁与垃圾清运服务招标文件公示
- 触摸屏测量仪器与粘度测定方法
- PSO多目标优化问题求解代码详解
- 有机硅组合物及差异剥离纸或膜技术分析
- Win10快速关机技巧:去除关机阻止功能
- 创新打印机设计:速释打印头与压纸辊安装拆卸便捷性
安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功