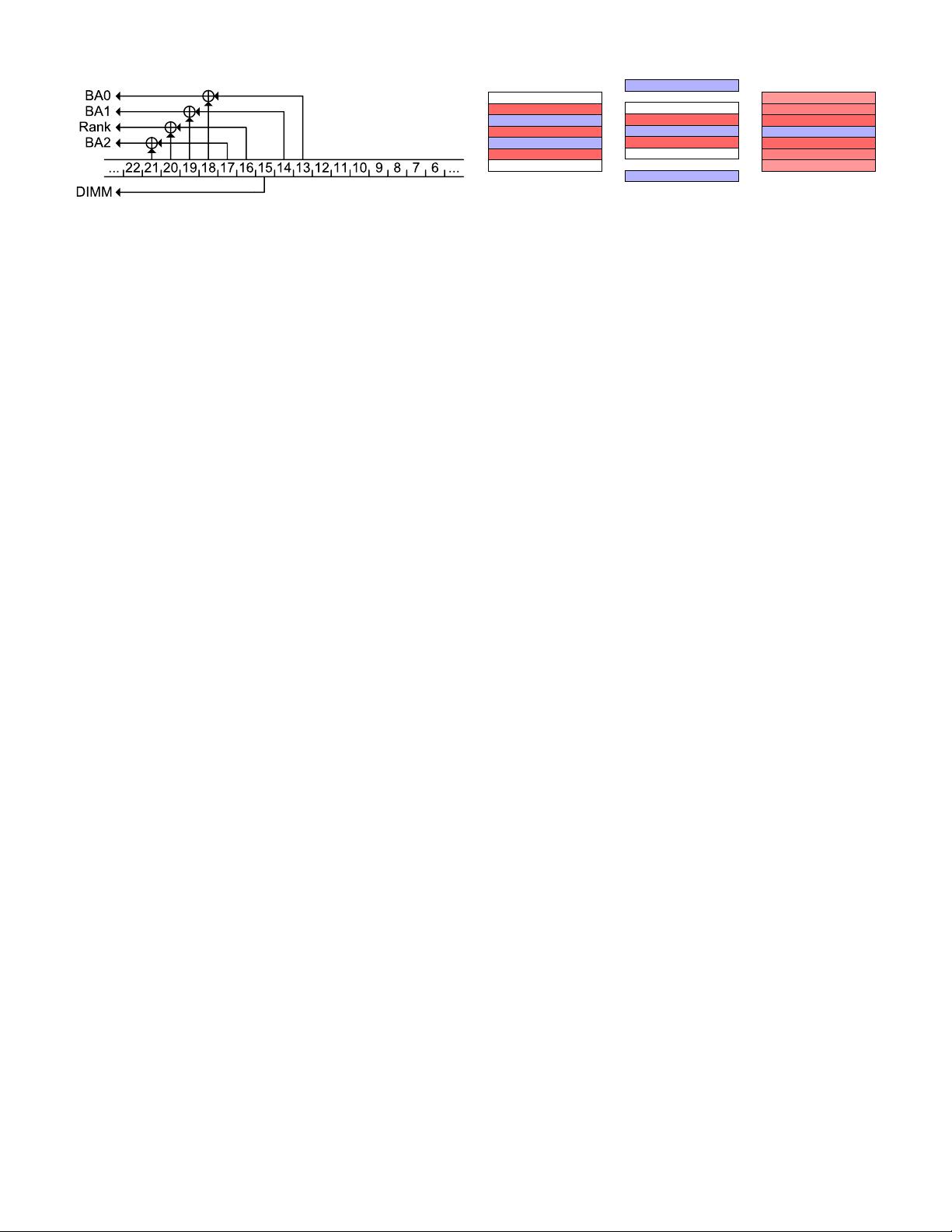
Fig. 1: Reverse engineered DDR3 single channel mapping (2
DIMM per channel) for Ivy Bridge / Haswell (from [49]).
engineered through both software- and hardware-based tech-
niques [49]. For example, Section II-A shows the DRAM
mapping for a typical configuration found in Ivy Bridge and
Haswell systems. As the figure shows, the bank and the rank
are determined based on bits 13–21 of the physical address. We
have verified that the mapping matches the Haswell processor
we use in our experiments.
Row Addressing. As discussed above, DRAM rows have a
fixed size of typically 8 KiB. However, from the implementa-
tion side, it is usually more important to know what amount of
memory has the same row index. This is sometimes referred to
as same-row [19, 55]. If the address goes to the same row and
the same bank, it is called same-row same-bank; if it goes
to different banks but has the same row index, it is called
same-row different-bank [55].
In our experimental setup, we have a total of 32 DRAM
banks, and thus an aligned block of 256 KiB = 2
18
B of
memory has the same row index. In other words, the row
index on our system is directly determined by bits 18 and
above of the physical address. Pessl et al. [49] provide a more
extensive discussion.
B. Row-Buffer Timing Side Channel
Opening a row and loading its contents into the row buffer
results in a measurable latency. Even more so, repeatedly
alternating accesses to two uncached memory locations will
be significantly slower if these two memory locations happen
to be mapped to different rows of the same bank [49]. In
Section V, we use this timing difference to identify virtual
addresses whose contents lie within the same bank, and
also uncover the lower 22 physical addressing bits, thereby
enabling double-sided Rowhammer attacks.
C. Rowhammer
The trend towards increasing DRAM cell density and de-
creasing capacitor size over the past decades has given rise to
a reliability issue known as Rowhammer. Specifically, repeated
accesses to rows in DRAM can lead to bit flips in neighboring
rows (not only the direct neighbors), even if these neighboring
rows are not accessed [34].
The Root Cause of Rowhammer. Due to the proximity of
word lines in DRAMs, when a word line is activated, crosstalk
effects on neighboring rows result in partial activation, which
leads to increased charge leakage from cells in neighboring
rows. Consequently, when a row is repeatedly opened, some
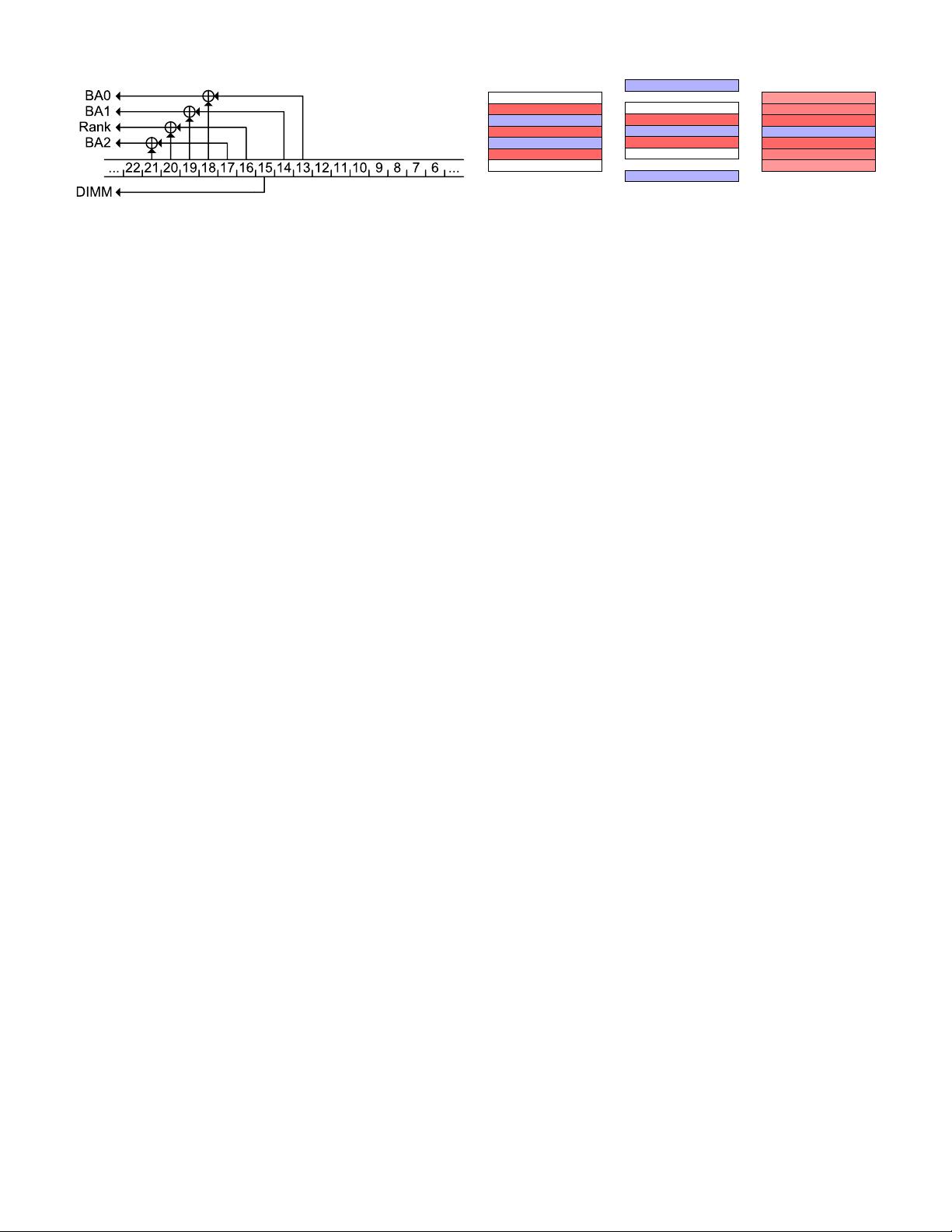
· · ·
· · ·
expect flip
hammer
expect flip
hammer
expect flip
(a) Double-sided
· · ·
· · ·
hammer
hammer
expect flip
hammer
expect flip
(b) Single-sided
· · ·
· · ·
expect flip
expect flip
expect flip
hammer
expect flip
expect flip
expect flip
(c) One-location
Fig. 2: Different hammering techniques as presented by [21].
cells lose enough charge before being refreshed to drop to an
uncharged state, resulting in bit flips in memory.
Performing Uncached Memory Accesses. A central re-
quirement for triggering Rowhammer bit flips is the capability
to make the memory controller open and close DRAM rows
rapidly. For this, the adversary needs to generate a sequence
of memory accesses to alternating DRAM rows that bypass
the CPU cache. Several approaches have been suggested for
bypassing the cache.
• Manually Flush Cache Lines. The x86 instruction
set provides the CLFLUSH instruction, which flushes the
cache line containing its destination address from all of
the levels of the cache hierarchy. Crucially, CLFLUSH only
requires read access to the flushed address, facilitating
Rowhammer attacks from unprivileged user-level code. On
ARM platforms, prior to ARMv8, the equivalent cache line
flush instruction could only be executed in kernel mode;
ARMv8 does, however, offers operating systems the option
to enable an unprivileged cache line flush operation.
• Cache Eviction. In cases where the CLFLUSH instruction
is not available (e.g. in the browser), an attacker can force
contention on cache sets to cause cache eviction [2, 19].
• Uncached DMA Memory. Van Der Veen et al. [61] report
that the cache eviction method above is not fast enough to
cause bit flips on contemporary ARM-based smartphones.
Instead, they used the Android ION feature to allocate
uncacheable memory to unprivileged userspace applications.
• Non-temporal instructions. Non-temporal load and store
instructions direct the CPU not to cache their results. Avoid-
ing caching means that subsequent accesses to the same
address bypass the cache and are served from memory [50].
Another important distinction between Rowhammer attacks is
the strategy in which DRAM rows are activated, i.e., how
aggressor rows are selected. See Figure 2.
Double-sided Rowhammer. The highest amount of
Rowhammer-induced bit flips occur when the attacker ham-
mers, that is repeatedly opens and closes, the two rows
adjacent to a target row. This approach maximizes the number
of neighboring row activations, and consequently the charge
leakage from the target row (Figure 2a). However, for double-
sided hammering, the attacker needs to locate addresses in the
two adjacent rows, which may be difficult without knowledge
of the physical addresses and their mapping to rows. Previous
attacks exploited the Linux pagemap interface, which maps
virtual to physical addresses. However, to mitigate the Seaborn
In Proceedings of the 41st Annual IEEE Symposium on Security & Privacy, May 2020 Page 4