没有合适的资源?快使用搜索试试~ 我知道了~
首页Handbook of Applied Cryptography.pdf
资源详情
资源评论
资源推荐

HANDBOOK of
APPLIED
CRYPTOGRAPHY
Alfred J. Menezes
Paul C. van Oorschot
Scott A. Vanstone

Foreword
by R.L. Rivest
As we draw near to closing out the twentieth century, we see quite clearly that the
information-processing and telecommunications revolutions now underway will
continue vigorously into the twenty-first. We interact and transact by directing flocks
of digital packets towards each other through cyberspace, carrying love notes, digital
cash, and secret corporate documents. Our personal and economic lives rely more and
more on our ability to let such ethereal carrier pigeons mediate at a distance what we
used to do with face-to-face meetings, paper documents, and a firm handshake.
Unfortunately, the technical wizardry enabling remote collaborations is founded on
broadcasting everything as sequences of zeros and ones that one's own dog wouldn't
recognize. What is to distinguish a digital dollar when it is as easily reproducible as the
spoken word? How do we converse privately when every syllable is bounced off a
satellite and smeared over an entire continent? How should a bank know that it really is
Bill Gates requesting from his laptop in Fiji a transfer of $10,000,000,000 to another
bank? Fortunately, the magical mathematics of cryptography can help. Cryptography
provides techniques for keeping information secret, for determining that information
has not been tampered with, and for determining who authored pieces of information.
Cryptography is fascinating because of the close ties it forges between theory and
practice, and because today's practical applications of cryptography are pervasive and
critical components of our information-based society. Information-protection protocols
designed on theoretical foundations one year appear in products and standards
documents the next. Conversely, new theoretical developments sometimes mean that
last year's proposal has a previously unsuspected weakness. While the theory is
advancing vigorously, there are as yet few true guarantees; the security of many
proposals depends on unproven (if plausible) assumptions. The theoretical work refines
and improves the practice, while the practice challenges and inspires the theoretical
work. When a system is "broken," our knowledge improves, and next year's system is
improved to repair the defect. (One is reminded of the long and intriguing battle
between the designers of bank vaults and their opponents.)
Cryptography is also fascinating because of its game-like adversarial nature. A good
cryptographer rapidly changes sides back and forth in his or her thinking, from attacker
to defender and back. Just as in a game of chess, sequences of moves and counter-
moves must be considered until the current situation is understood. Unlike chess
players, cryptographers must also consider all the ways an adversary might try to gain
by breaking the rules or violating expectations. (Does it matter if she measures how
long I am computing? Does it matter if her "random" number isn't one?)
The current volume is a major contribution to the field of cryptography. It is a rigorous
encyclopedia of known techniques, with an emphasis on those that are both (believed to
be) secure and practically useful. It presents in a coherent manner most of the important
cryptographic tools one needs to implement secure cryptographic systems, and explains
many of the cryptographic principles and protocols of existing systems. The topics
covered range from low-level considerations such as random-number generation and
efficient modular exponentiation algorithms and medium-level items such as public-
key signature techniques, to higher-level topics such as zero-knowledge protocols. This
book's excellent organization and style allow it to serve well as both a self-contained
tutorial and an indispensable desk reference.
In documenting the state of a fast-moving field, the authors have done incredibly well
at providing error-free comprehensive content that is up-to-date. Indeed, many of the
chapters, such as those on hash functions or key-establishment protocols, break new
ground in both their content and their unified presentations. In the trade-off between
comprehensive coverage and exhaustive treatment of individual items, the authors have
chosen to write simply and directly, and thus efficiently, allowing each element to be
explained together with their important details, caveats, and comparisons.
While motivated by practical applications, the authors have clearly written a book that
will be of as much interest to researchers and students as it is to practitioners, by
including ample discussion of the underlying mathematics and associated theoretical
considerations. The essential mathematical techniques and requisite notions are
presented crisply and clearly, with illustrative examples. The insightful historical notes
and extensive bibliography make this book a superb stepping-stone to the literature. (I
was very pleasantly surprised to find an appendix with complete programs for the
CRYPTO and EUROCRYPT conferences!)
It is a pleasure to have been asked to provide the foreword for this book. I am happy to
congratulate the authors on their accomplishment, and to inform the reader that he/she
is looking at a landmark in the development of the field.
Ronald L. Rivest
Webster Professor of Electrical Engineering and Computer Science
Massachusetts Institute of Technology
June 1996

Preface
This book is intended as a reference for professional cryptographers, presenting the
techniques and algorithms of greatest interest to the current practitioner, along with the sup-
portingmotivationand background material. It also provides a comprehensive source from
which to learn cryptography, serving both students and instructors. In addition, the rigor-
ous treatment, breadth, and extensive bibliographic material should make it an important
reference for research professionals.
Our goal was to assimilate the existing cryptographic knowledge of industrial interest
into one consistent, self-contained volume accessible to engineers in practice, to computer
scientists and mathematicians in academia, and to motivated non-specialists with a strong
desire to learn cryptography. Such a task is beyond the scope of each of the following: re-
search papers, which by nature focus on narrow topics using very specialized (and often
non-standard) terminology; survey papers, which typically address, at most, a small num-
ber of major topics at a high level; and (regretably also) most books, due to the fact that
many book authors lack either practical experience or familiarity with the research litera-
ture or both. Our intent was to provide a detailed presentation of those areas of cryptogra-
phy which we have found to be of greatest practical utilityin our own industrialexperience,
while maintaining a sufficiently formal approach to be suitable both as a trustworthyrefer-
ence for those whose primary interest is further research, and to provide a solid foundation
for students and others first learning the subject.
Throughout each chapter, we emphasize the relationship between various aspects of
cryptography. Background sections commence most chapters, providing a framework and
perspective for the techniques which follow. Computer source code (e.g. C code) for algo-
rithms has been intentionallyomitted, in favor of algorithmsspecified in sufficient detail to
allow direct implementation withoutconsultingsecondary references. We believe this style
of presentation allows a better understanding of how algorithmsactually work, while at the
same time avoiding low-level implementation-specific constructs (which some readers will
invariably be unfamiliar with) of various currently-popular programming languages.
The presentation also strongly delineates what has been established as fact (by math-
ematical arguments) from what is simply current conjecture. To avoid obscuring the very
applied nature of the subject, rigorousproofs ofcorrectness are inmost cases omitted;how-
ever, references given in the Notes section at the end of each chapter indicate the original
or recommended sources for these results. The trailing Notes sections also provide infor-
mation (quite detailed in places) on various additionaltechniques not addressed in the main
text, and provide a survey of research activities and theoretical results; references again in-
dicate where readers may pursue particular aspects in greater depth. Needless to say, many
results, and indeed some entire research areas, have been given far less attention than they
warrant, or have been omitted entirely due to lack of space; we apologize in advance for
such major omissions, and hope that the most significant of these are brought to our atten-
tion.
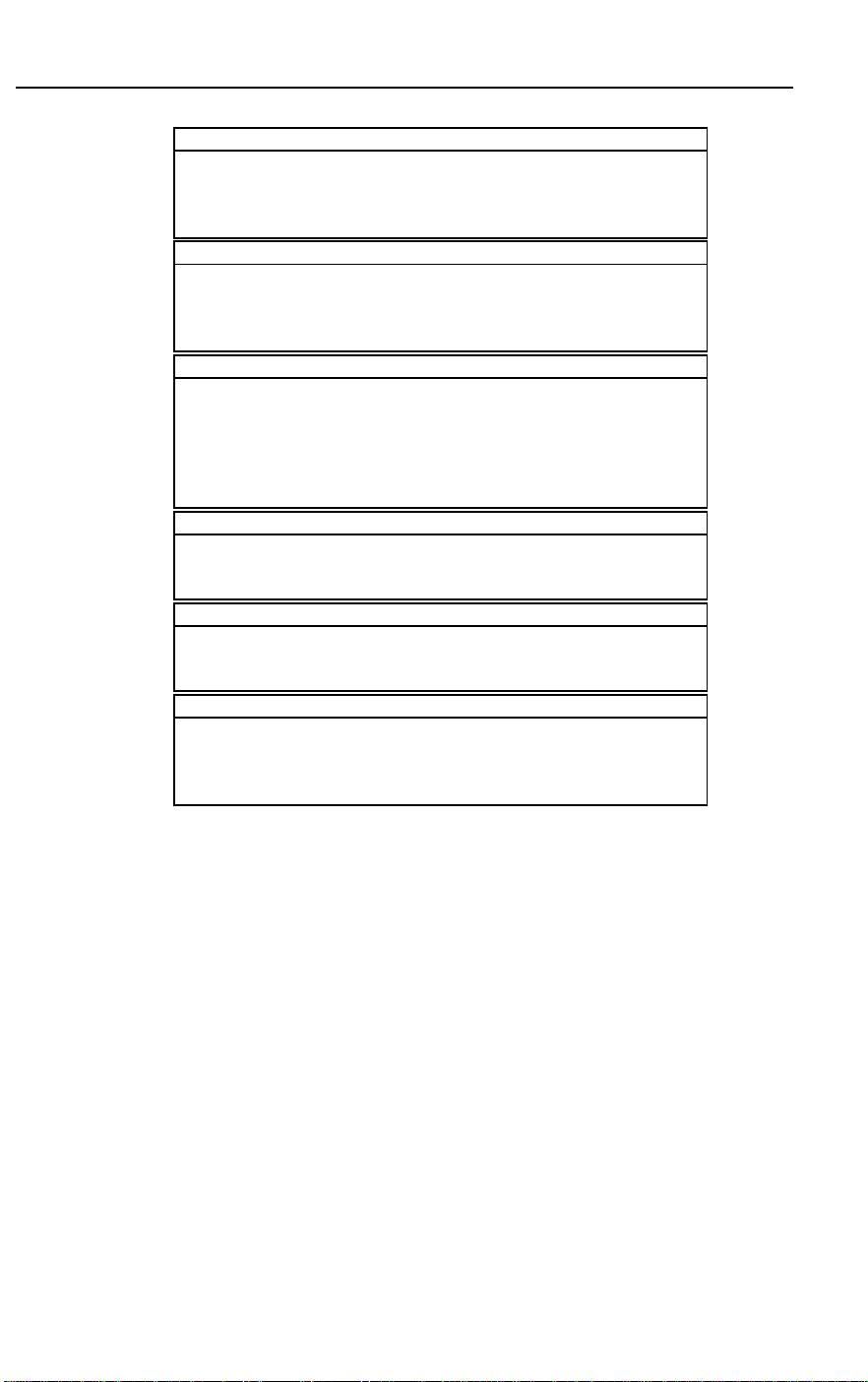
To provide an integrated treatment of cryptography spanning foundational motivation
through concrete implementation, it is useful to consider a hierarchy of thought ranging
from conceptual ideas and end-user services, down to the tools necessary to complete ac-
tual implementations. Table 1 depicts the hierarchical structure around which this book is
organized. Corresponding to this, Figure 1 illustrates how these hierarchical levels map
xxiii
xxiv Preface
Information Security Objectives
Confidentiality
Data integrity
Authentication (entity and data origin)
Non-repudiation
Cryptographic functions
Encryption Chapters 6, 7, 8
Message authentication and data integrity techniques Chapter 9
Identification/entity authentication techniques Chapter 10
Digital signatures Chapter 11
Cryptographic building blocks
Stream ciphers Chapter 6
Block ciphers (symmetric-key) Chapter 7
Public-key encryption Chapter 8
One-way hash functions (unkeyed) Chapter 9
Message authentication codes Chapter 9
Signature schemes (public-key, symmetric-key) Chapter 11
Utilities
Public-key parameter generation Chapter 4
Pseudorandombit generation Chapter 5
Efficient algorithms for discrete arithmetic Chapter 14
Foundations
Introduction to cryptography Chapter 1
Mathematical background Chapter 2
Complexity and analysis of underlying problems Chapter 3
Infrastructure techniques and commercial aspects
Key establishment protocols Chapter 12
Key installation and key management Chapter 13
Cryptographic patents Chapter 15
Cryptographic standards Chapter 15
Table 1: Hierarchical levels of applied cryptography.
onto the various chapters, and their inter-dependence.
Table 2 lists the chapters of the book, along with the primary author(s) of each who
should be contacted byreaders with comments on specific chapters. Each chapter was writ-
ten to provide a self-contained treatment of one major topic. Collectively, however, the
chapters have been designed and carefully integrated to be entirely complementary with
respect to definitions, terminology, and notation. Furthermore, there is essentially no du-
plication of material across chapters; instead, appropriate cross-chapter references are pro-
vided where relevant.
While it is not intended that this book be read linearly from front to back, the material
has been arranged so that doing so has some merit. Two primary goals motivated by the
“handbook” nature of this project were to allow easy access tostand-alone results, and to al-
low results and algorithms to be easily referenced (e.g., for discussion or subsequent cross-
reference). To facilitate the ease of accessing and referencing results, items have been cate-
gorizedand numbered to a largeextent, withthe followingclasses of items jointlynumbered
consecutively in each chapter: Definitions, Examples, Facts, Notes, Remarks, Algorithms,
Protocols, and Mechanisms. In more traditional treatments, Facts are usually identified as
propositions,lemmas, or theorems. We use numbered Notes for additionaltechnical points,
剩余793页未读,继续阅读
ieee802.11
- 粉丝: 6
- 资源: 1
上传资源 快速赚钱
 我的内容管理
收起
我的内容管理
收起
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

会员权益专享
最新资源
- RTL8188FU-Linux-v5.7.4.2-36687.20200602.tar(20765).gz
- c++校园超市商品信息管理系统课程设计说明书(含源代码) (2).pdf
- 建筑供配电系统相关课件.pptx
- 企业管理规章制度及管理模式.doc
- vb打开摄像头.doc
- 云计算-可信计算中认证协议改进方案.pdf
- [详细完整版]单片机编程4.ppt
- c语言常用算法.pdf
- c++经典程序代码大全.pdf
- 单片机数字时钟资料.doc
- 11项目管理前沿1.0.pptx
- 基于ssm的“魅力”繁峙宣传网站的设计与实现论文.doc
- 智慧交通综合解决方案.pptx
- 建筑防潮设计-PowerPointPresentati.pptx
- SPC统计过程控制程序.pptx
- SPC统计方法基础知识.pptx
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功
评论1