没有合适的资源?快使用搜索试试~ 我知道了~
首页PCI_PTS_PO__DTRs_v5-1.pdf
资源详情
资源推荐

Payment Card Industry (PCI)
PIN Transaction Security (PTS)
Point of Interaction (POI)
Modular Derived Test Requirements
Version 5.1
March 2018

Payment Card Industry PTS POI Derived Test Requirements, v5.1 March 2018
© Copyright 2010-2018 PCI Security Standards Council, LLC. All Rights Reserved. Page ii
© PCI Security Standards Council LLC 2010-2018
This document and its contents may not be used, copied, disclosed, or distributed for any purpose except
in accordance with the terms and conditions of the Non-Disclosure Agreement executed between the PCI
Security Standards Council LLC and your company. Please review the Non-Disclosure Agreement before
reading this document.
Payment Card Industry PTS POI Derived Test Requirements, v5.1 March 2018
© Copyright 2010-2018 PCI Security Standards Council, LLC. All Rights Reserved. Page iii
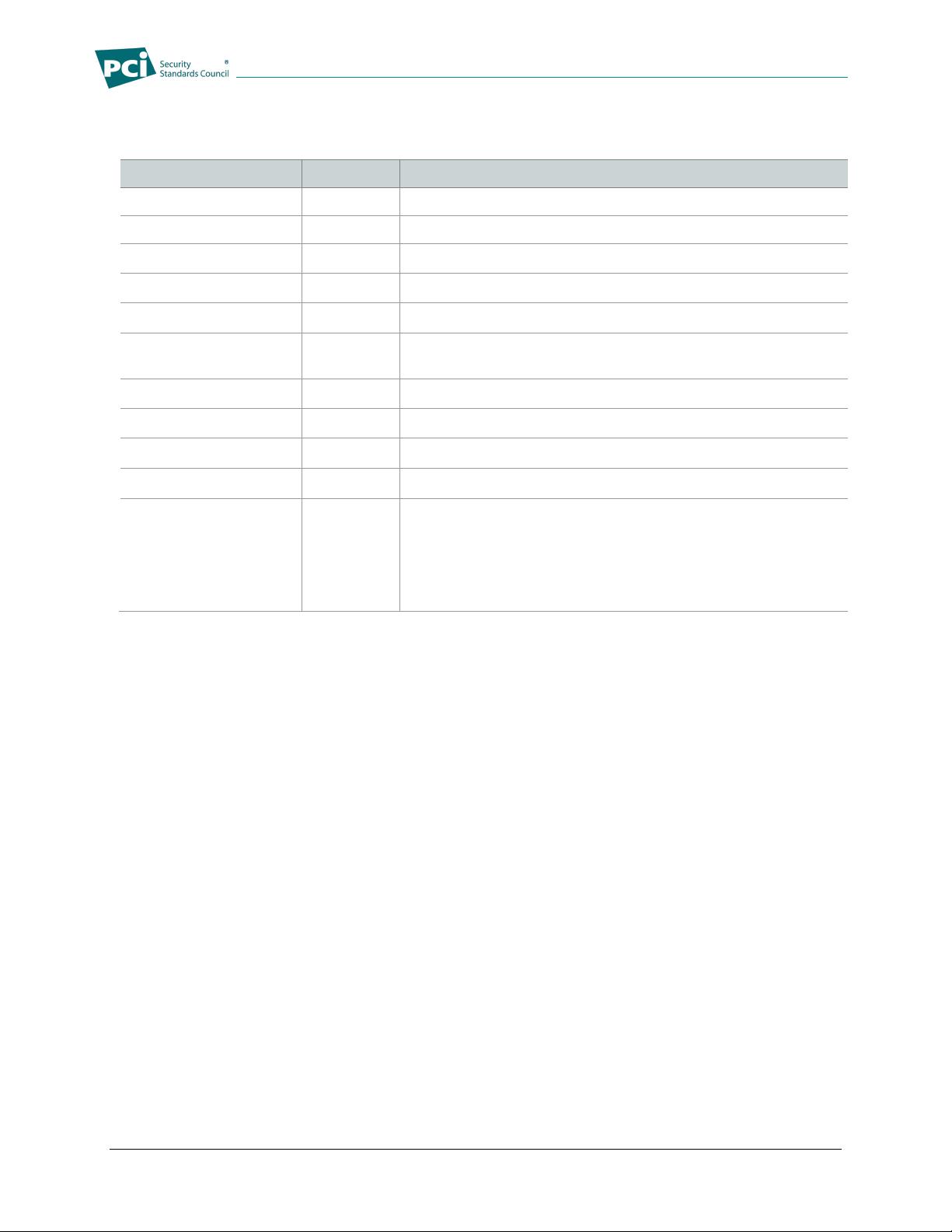
Document Changes
Date
Version
Description
February 2010
3.x
Initial Request-for-Comment Version
April 2010
3.0
Initial public release
October 2011
3.1
Clarifications and errata, updates for non-PIN POIs
February 2013
4.x
RFC version and combining of DTRs and DTPs
June 2013
4.0
Public release
June 2015
4.1
Updates for errata and new Core Section J. Added Device
Management.
July 2015
4.1a
Minor errata
September 2015
4.1b
Section J updates
June 2016
5.x
RFC version
September 2016
5.0
Public release
March 2018
5.1
Modified B4, B9, B12, D1, D4, K1, K4, K12, and K16, and
added K24 for SCRP approval class. Modified A1, A4, A5, A8,
B2, F1, K1.1, and K11.2. Reorganized B20 and added
reference to example of Security Policy layout in Appendix H.
Modified side-channel testing appendix. Errata.

Payment Card Industry PTS POI Derived Test Requirements, v5.1 March 2018
© Copyright 2010-2018 PCI Security Standards Council, LLC. All Rights Reserved. Page iv
Contents
Document Changes iii
Introduction 1
DTR Module 1: Core Requirements .........................................................................................................................4
A – Core Physical Security Derived Test Requirements ...........................................................................................4
DTR A1 Tamper-Detection Mechanisms ................................................................................................... 4
DTR A2 Robustness Under Changing Environmental and Operational Conditions ................................... 9
DTR A3 Protection of Sensitive Functions or Information ........................................................................ 11
DTR A4 Monitoring During PIN Entry ...................................................................................................... 14
DTR A5 Determining Keys Analysis ........................................................................................................ 16
DTR A6 Physical Security of Display Prompts......................................................................................... 19
DTR A7 Visual Observation Deterrents ................................................................................................... 21
DTR A8 Magnetic-Stripe Reader ............................................................................................................. 23
DTR A9 Component Protections against Removal .................................................................................. 25
DTR A10 Audible Tones During PIN Entry ................................................................................................ 27
B – Core Logical Security Derived Test Requirements ......................................................................... 28
DTR B1 Self-Test .................................................................................................................................... 28
DTR B2 Logical Anomalies ...................................................................................................................... 31
DTR B3 Firmware Certification ................................................................................................................ 34
DTR B4 Firmware Updates ..................................................................................................................... 37
DTR B4.1 Software Authenticity ................................................................................................................. 40
DTR B4.2 Signing ....................................................................................................................................... 42
DTR B5 Differentiation of Entered PIN .................................................................................................... 43
DTR B6 Clearing of Internal Buffers ........................................................................................................ 44
DTR B7 Protection of Sensitive Services ................................................................................................ 46
DTR B8 Sensitive Services Limits ........................................................................................................... 49
DTR B9 Random Numbers ...................................................................................................................... 51
DTR B10 Exhaustive PIN Determination ................................................................................................... 53
DTR B11 Key Management ....................................................................................................................... 55
DTR B12 Encryption Algorithm Test .......................................................................................................... 65
DTR B13 Encryption or Decryption of Arbitrary Data Within the Device .................................................... 67
DTR B14 Clear-Text Key Security ............................................................................................................. 69
DTR B15 Transaction Controls .................................................................................................................. 70
DTR B16 Logical Management of Display Prompts................................................................................... 71
DTR B17 Application Separation ............................................................................................................... 74
DTR B18 Minimal Configuration ................................................................................................................ 77
DTR B19 Component Integration Documentation ..................................................................................... 79
DTR B20 Security Policy ........................................................................................................................... 80
C – Online PIN Security Derived Test Requirements ............................................................................ 84
DTR C1 Key Substitution ......................................................................................................................... 84
D – Offline PIN Security Derived Test Requirements ............................................................................ 85
DTR D1 Penetration Protection ............................................................................................................... 85
DTR D2 ICC Reader Slot Visibility ........................................................................................................... 88
DTR D3 ICC Reader Construction (Wires) .............................................................................................. 89
DTR D4 PIN Protection During Transmission Between Device and ICC Reader .................................... 90
DTR Module 2: POS Terminal Integration Requirements ...................................................................... 92
E – POS Terminal Integration Derived Test Requirements ................................................................... 92
DTR E1 Target of Evaluation (TOE) Identification ................................................................................... 92
DTR E2.1 Integration of PIN Entry Functions ............................................................................................. 93
DTR E2.2 Overlay Attack Protection .......................................................................................................... 94
DTR E3.1 Integration Vulnerabilities ........................................................................................................... 95
DTR E3.2 Protection Against Card Trapping .............................................................................................. 96

Payment Card Industry PTS POI Derived Test Requirements, v5.1 March 2018
© Copyright 2010-2018 PCI Security Standards Council, LLC. All Rights Reserved. Page v
DTR E3.3 PIN Entry Interface Segregation ................................................................................................ 97
DTR E3.4 User Interface Consistency ........................................................................................................ 98
DTR E3.5 Control of any Numeric Interface ............................................................................................. 100
DTR E4.1 Protection against Removal ..................................................................................................... 101
DTR E4.2 Unauthorized Removal – Integration Documentation .............................................................. 103
DTR E4.3 Unauthorized Removal – Embedded Devices .......................................................................... 104
DTR Module 3: Open Protocols Requirements .................................................................................... 105
F – Discovery and Definition of Protocols and Interfaces .................................................................. 105
DTR F1 Identification of Interfaces ........................................................................................................ 105
DTR G1 Vendor Vulnerability Assessment Procedures ......................................................................... 107
DTR G2 Vulnerability Assessment of all Interfaces ................................................................................ 108
DTR G3 Vulnerability Disclosure............................................................................................................ 109
H – Vendor Guidance .............................................................................................................................. 110
DTR H1 Security Guidance for the Protocols and Interfaces ................................................................. 110
DTR H2 Default Configuration of the Interfaces..................................................................................... 111
DTR H3 Key Management Security Guidance....................................................................................... 112
I – Operational Testing ............................................................................................................................ 113
DTR I1 Use of Secure Protocols .......................................................................................................... 113
DTR I2 Secure Protocols to Provide Data Confidentiality .................................................................... 114
DTR I3 Secure Protocols to Provide Data Integrity .............................................................................. 115
DTR I5 Secure Protocols to Provide Exception Handling and Replay Detection ................................. 117
DTR I6 Session Management .............................................................................................................. 118
Evaluation Module (Core): Configuration and Maintenance Security ............................................ 119
J – Configuration and Maintenance Security ....................................................................................... 119
DTR J1 Security Guidance for Configuration Management .................................................................. 119
DTR J2 Security Maintenance .............................................................................................................. 120
DTR J3 Security Guidance for Terminal Updates ................................................................................. 121
DTR J4 Securing Configuration and Software Updates ........................................................................ 122
DTR Module 4: Secure Reading and Exchange of Data ...................................................................... 123
K – Account Data Protection Derived Test Requirements .................................................................. 123
DTR K1 Account Data Processing ......................................................................................................... 123
DTR K1.1 Account Data Protection .......................................................................................................... 124
DTR K2 Account Data Protection – Integration...................................................................................... 126
DTR K3 Determining Keys Analysis ...................................................................................................... 127
DTR K3.1 Public Key Protection ............................................................................................................... 130
DTR K4 Encryption Mechanisms ........................................................................................................... 131
DTR K5 Remote Key Distribution .......................................................................................................... 133
DTR K6 Data Origin Authentication ....................................................................................................... 134
DTR K7 Unique Secret and Private Keys Per Device ............................................................................ 135
DTR K8 Encryption/Decryption of Arbitrary Data Within a Device ......................................................... 136
DTR K9 Remote Access ........................................................................................................................ 138
DTR K10 Firmware Certification .............................................................................................................. 139
DTR K11.1 Software Authenticity ............................................................................................................... 142
DTR K11.2 Software Guidance .................................................................................................................. 144
DTR K12 Firmware Updates ................................................................................................................... 145
DTR K13 Logical Anomalies .................................................................................................................... 148
DTR K14 Open Protocols and Services .................................................................................................. 151
DTR K15 Output of Clear-text Account Data ........................................................................................... 152
DTR K15.1 Protection of Clear-text Data .................................................................................................... 154
DTR K15.2 Clearing of Internal Buffers ...................................................................................................... 155
DTR K16 Surrogate PAN Values ............................................................................................................. 157
DTR K16.1 Salt Generation ........................................................................................................................ 158
DTR K16.2 Salt Storage ............................................................................................................................. 159
剩余257页未读,继续阅读
安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功









