Hacking Linux - Privilege Escalation [Detailed]
Before reading this, you should know that Privilege Escalation on Linux system is
dependent on its different versions.So this information may not work on all Linux
distributions, But it will give a general overview of how to carry out the whole process.
Note that, I am not the sole writer of this tut, I compiled it from three different
sources and merged them into one
Lets start
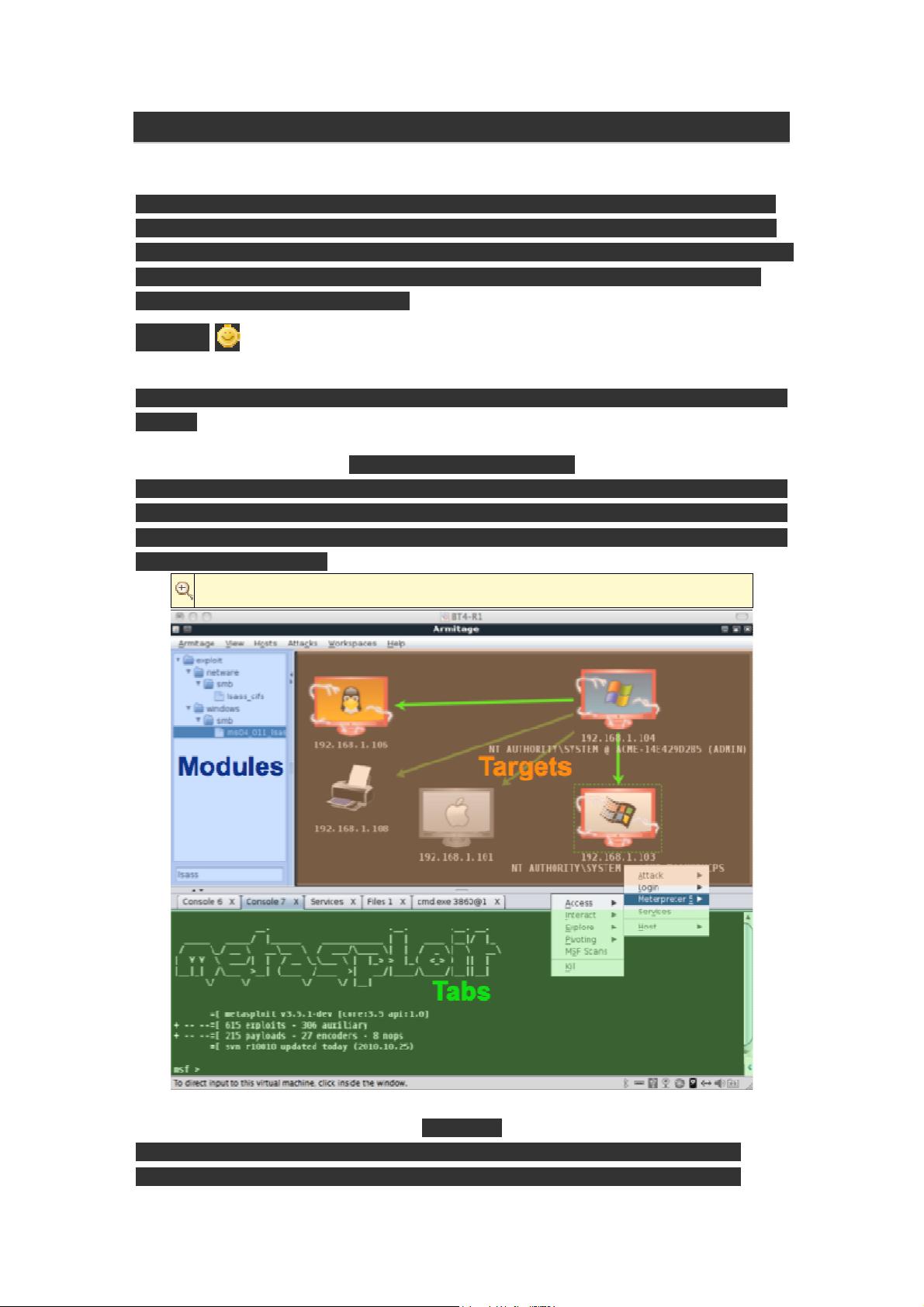
In this tuto I am using Armitage which is GUI verion for metasploit to exploit a linux
system.
Armitage's User Interface
The Armitage user interface has three parts. The modules area lets you search and
launch any of Metasploit's modules. The targets area displays your active targets and
sessions. Below the modules and targets are the tabs. Each dialog, shell, and console
is opened in its own tab.
Click this bar to view the original image of 555x458px.
Scanning
Before we can attack a host, we must first perform our reconnaissance step.
Armitage provides several tools for this in the Hosts menu. You can import a