没有合适的资源?快使用搜索试试~ 我知道了~
首页TLS & SSLv3 renegotiation
TLS & SSLv3 renegotiation
需积分: 49 19 下载量 130 浏览量
更新于2023-07-03
收藏 815KB PDF 举报
ssl漏洞This paper explains the vulnerability for a broader audience and summarizes the information that is currently available. The document is prone to updates and is believed to be accurate by the time of writing
资源详情
资源推荐
Thierry ZOLLER
Principal Security Consultant
contact@g-sec.lu
http://www.g-sec.lu
G-SEC™ is a vendor independent Luxemburgish led
security consulting group that offers IT Security
consulting services on an organizational and
technical level. Our work has been featured in New
York Times, eWeek, ct', SAT1, Washington Post and
at conferences ranging from Hack.lu to Cansecwest.
Draft

Draft: TLS & SSLv3 renegotiation vulnerability
2009
2
Table of Contents
Synopsis ......................................................................................................................................................... 3
Generic TLS renegotiation prefix injection vulnerability ............................................................................... 5
Details ........................................................................................................................................................ 6
HTTPS ............................................................................................................................................................. 7
1 Attack method - Injecting commands into an HTTPS session (using X-:\n) ........................................... 8
Details ........................................................................................................................................................ 9
2 Attack method - HTTPS to HTTP downgrade attack ............................................................................. 10
Details ...................................................................................................................................................... 11
3 Attack method - Injecting custom responses through the use of TRACE............................................. 13
Details ...................................................................................................................................................... 14
SMTPS .......................................................................................................................................................... 15
Protocol vulnerability matrix ................................................................................................................... 15
The attacker does NOT have an account on the SMTP server ............................................................ 15
The Attacker has an account on the SMTP server .............................................................................. 15
Attack scenario - SMTP STARTTLS (110) .................................................................................................. 16
Details ...................................................................................................................................................... 17
Client side attack detection ..................................................................................................................... 18
Important Note........................................................................................................................................ 18
FTPS ............................................................................................................................................................. 19
Client certificate based authentication (Control Channel)...................................................................... 20
Renegotiations due to NAT support (Data Channel) ............................................................................... 20
Resetting the TCP connection and injecting in mid transfer ................................................................... 20
The Impact on other protocols using TLS .................................................................................................... 21
Summary ................................................................................................................................................. 21
EAP-TLS .................................................................................................................................................... 22
Solutions ...................................................................................................................................................... 23
Proposed IETF solution ............................................................................................................................ 23
Patching TLS ............................................................................................................................................. 23
Client .................................................................................................................................................... 23
Server................................................................................................................................................... 23
Patching SSLv3 ......................................................................................................................................... 23
Draft: TLS & SSLv3 renegotiation vulnerability
2009
3
Testing for a renegotiation vulnerability ..................................................................................................... 24
Vulnerability requirements ..................................................................................................................... 24
Generic Example ...................................................................................................................................... 24
Patched server with disabled renegotiation ........................................................................................... 24
Conclusions .................................................................................................................................................. 25
Servers ..................................................................................................................................................... 25
Clients ...................................................................................................................................................... 25
Sources ........................................................................................................................................................ 25
Thanks ......................................................................................................................................................... 25
Disclaimer .................................................................................................................................................... 25
Synopsis
Around the 09/11/2009 Marsh Ray, Steve Dispensa and Martin Rex published details
1
about a
vulnerability affecting the TLS and the SSLv3 protocol. The vulnerability is being tracked under
CVE-2009-3555
2
| VU#120541
3
and affects a multitude of platforms and protocols, the impact
of this vulnerability varies from protocol to protocol and from application to application. There
is extensive research required in order to assess
When speaking of a “Man in the Middle” attack, it is often assumed that data can be altered or
changed. Indeed an attacker that sits in the middle of a connection (hence it’s name) is often
able to do so. In this particular case however the attacker piggybacks an existing authenticated
and encrypted TLS sessions in order to (prefix) inject arbitrary text of its choice. The attacker
may not read/alter the other TLS session between the “client” and the “server”. See Chapter 3 -
“Example of an attack scenario...” for more details
This paper explains the vulnerability for a broader audience and summarizes the information
that is currently available. The document is prone to updates and is believed to be accurate by
the time of writing.
Important: This vulnerability is not limited to HTTPS, this vulnerability potentially affects every
application/protocol that implements TLS or SSLv3.
1
http://www.extendedsubset.com/
2
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-3555
3
http://www.kb.cert.org/vuls/id/120541
Draft: TLS & SSLv3 renegotiation vulnerability
2009
4
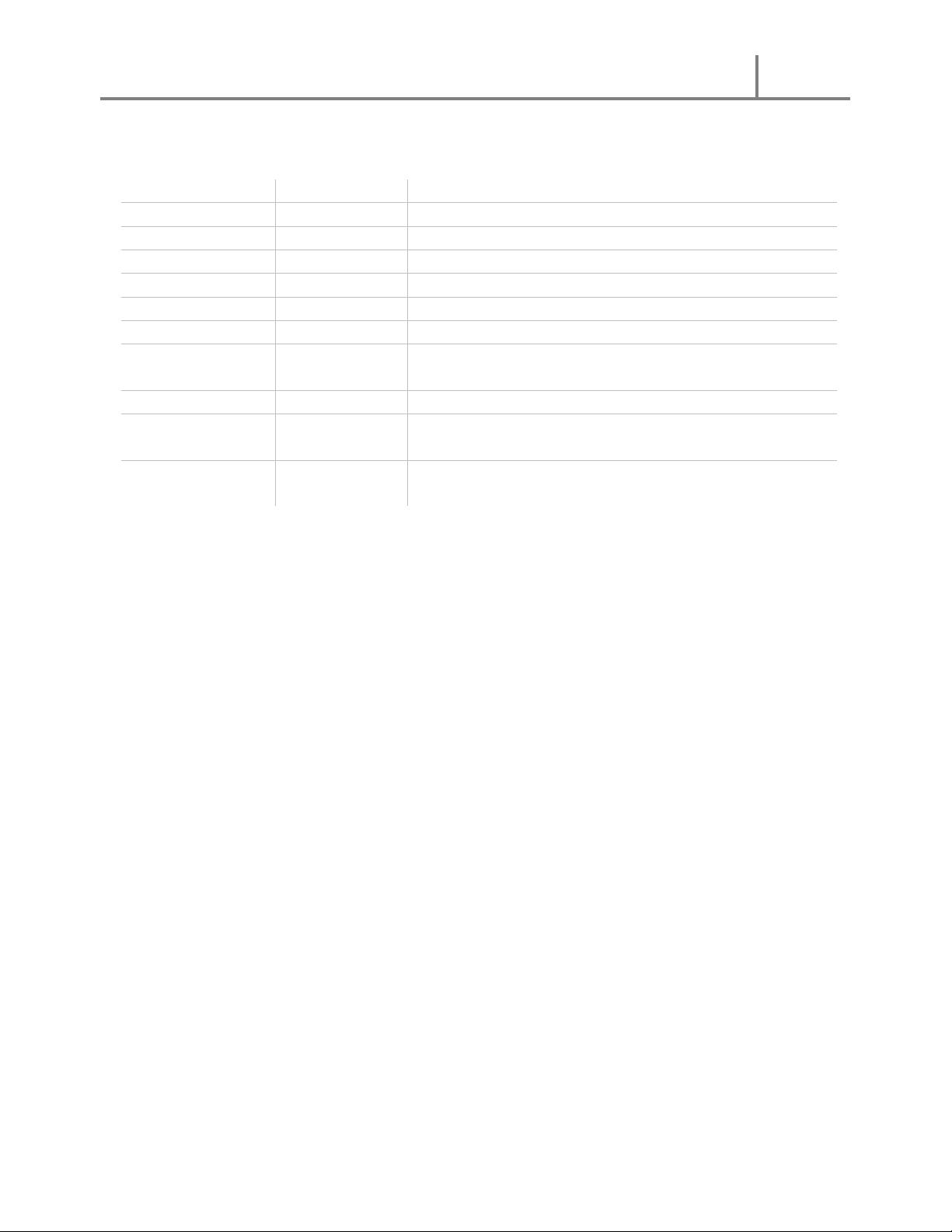
Revisions
Version
Date
Annotations
0.8
09.11.2009
Initial draft
0.81
10.11.2009
Adding general and specific example
0.9
12.11.2009
Added vulnerability requirements, protocol overview
0.91
12.11.2009
Initial public draft release at http://www.g-sec.lu/
0.92
13.11.2009
Corrected few errors
0.93
17.11.2009
Added test cases and SMTP over TLS details
0.95
24.11.2009
Added FTPS details, fixed syntax and formatting
errors, added IIS7 clarifications
0.96
25.11.2009
New test cases
0.97
27.11.2009
Added HTTPS TRACE and HTTPS to HTTP downgrade
attack
0.98
29.11.2009
Added 2 POC files for the TRACE and HTTPS to HTTP
downgrade attack
Draft: TLS & SSLv3 renegotiation vulnerability
2009
5
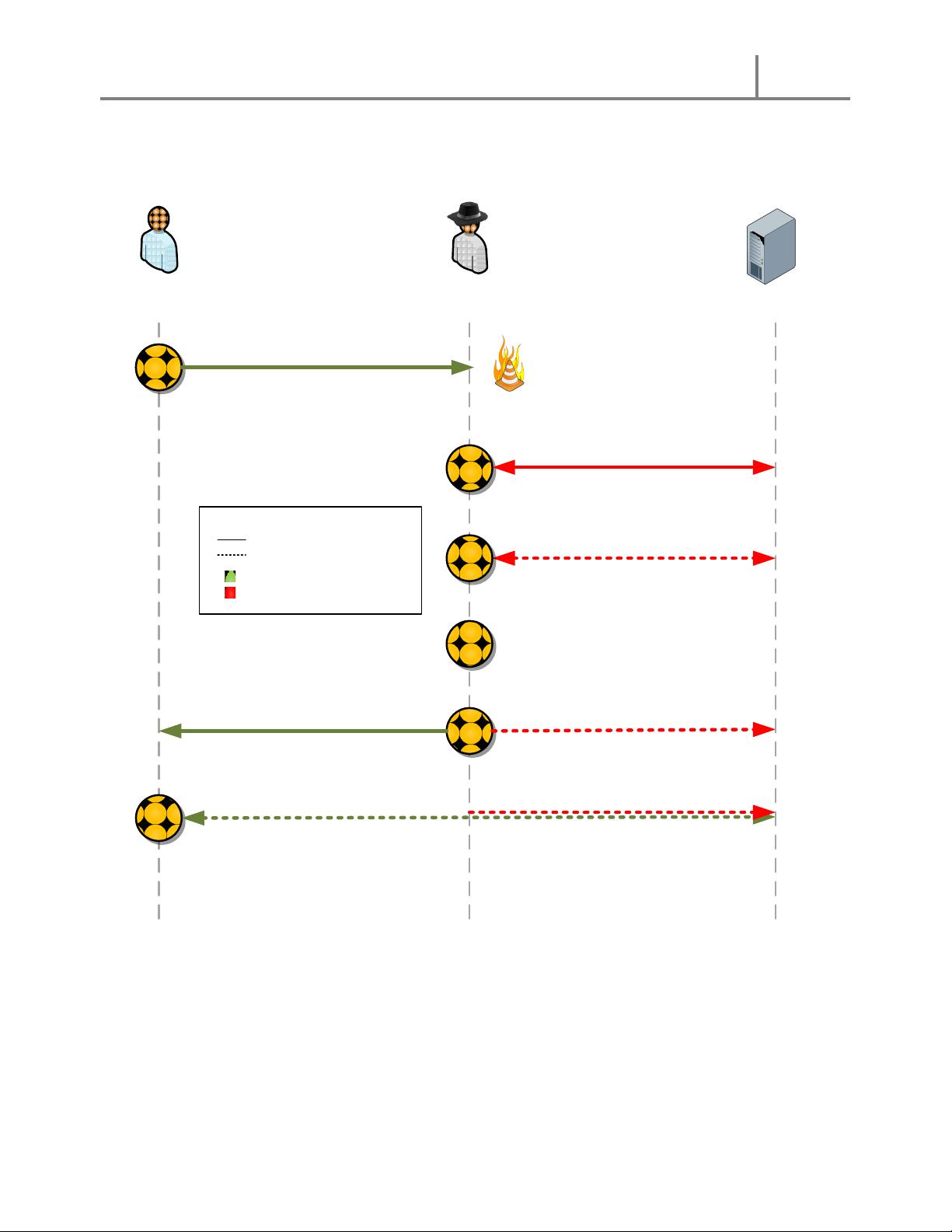
Generic TLS renegotiation prefix injection vulnerability
Client
Server (HTTPS)
2
1.1
3
1
TLS Handshake session #1
(client <> server)
TLS Handshake sesson #1 continued (client-server)
within the encrypted session #2 (attacker-server)
TLS Handshake session #2
(attacker <> server)
4
Attacker holds
the packets
Attacker
1.2
2
Renegotiation is triggered
Attacker sends application layer
commands of his choice
Client data is encrypted within session #1 (Green) (The attacker cannot read/
manipulate this data), previous data (1.2) prefixed to newly sent client-data
Straight line : Clear text communication
Dotted line : Encrypted communication
Green : Client communication
Red : Attacker data
Legend
剩余24页未读,继续阅读
安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功









