PSCI Use Cases and Use Case Requirements
16 Copyright
2012, 2013, 2015 ARM. All rights reserved. ARM DEN 0022C
Non-Confidential
Power-down: In this state the core is powered off. Software on the device needs to save
all core state, so that it can be preserved over the powerdown. Changing from
powerdown to running operation must include:
A reset of the core, after the power has been restored.
Restoring the saved core state.
The defining characteristic of powerdown states is that they are destructive of context. This
affects all the components that are switched off in a given state, including the core, and in
deeper states other components of the system such as the GIC or platform-specific IP.
Depending on how debug and trace power domains are organized, in some power-down
states one or both of debug and trace context might be lost. Mechanisms must be provided
to enable the OS to perform the relevant context saving and restoring for each given state.
Resumption of execution starts at the reset vector, after which each OS must restore its
context.
To an OS that is managing power, a standby state is mostly indistinguishable from a
retention state. The difference is evident to an external debugger, and in hardware
implementation, but not evident to the idle management subsystem of an OS.
Consequently, unless otherwise stated, this document uses the term standby to refer to
both standby and retention states.
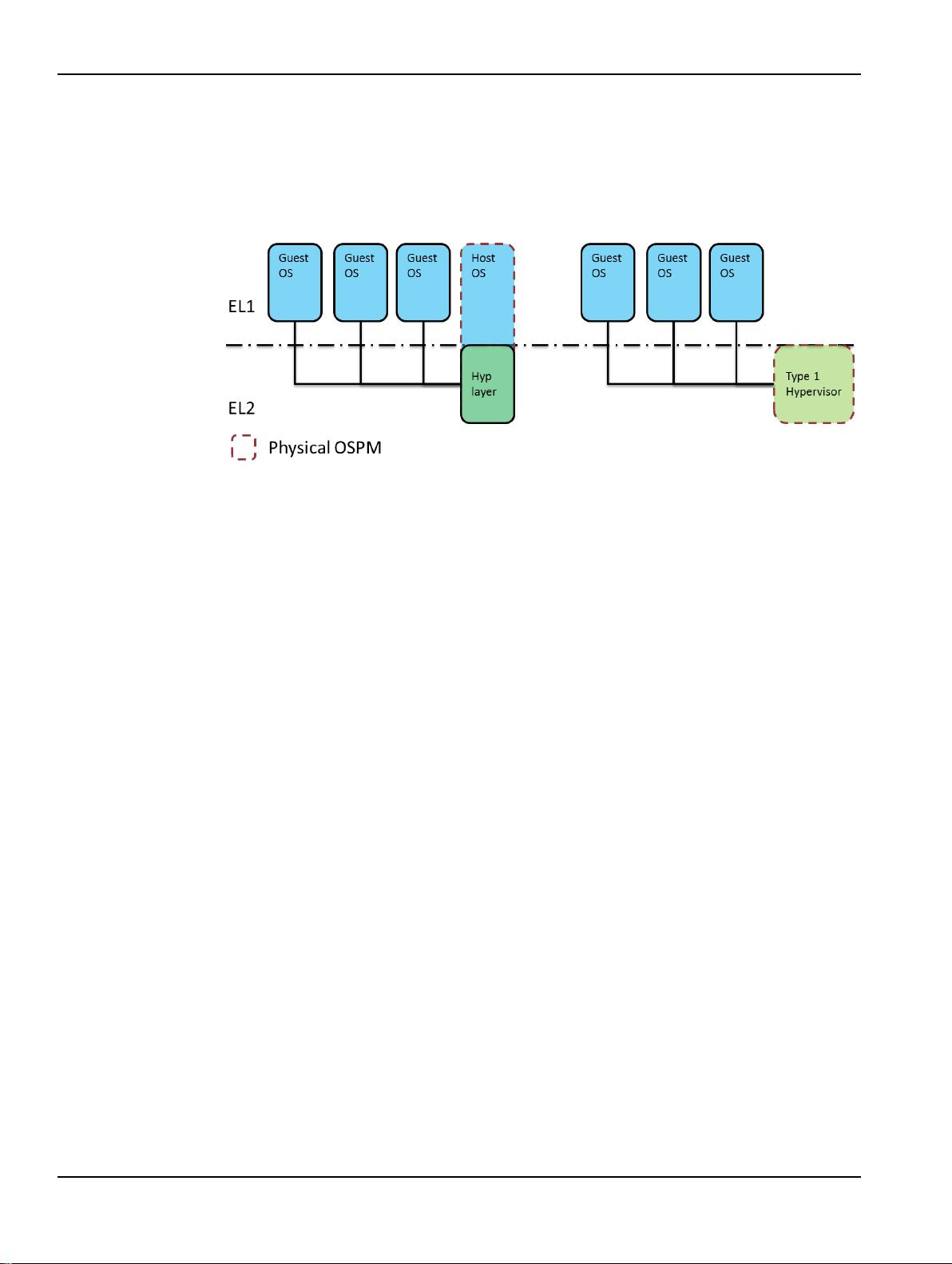
An interface is required so that the OSPM can place a core into a low-power state when it
has no work for it. The messages sent through this interface must be received by all
relevant levels of execution. That is, if EL2 and EL3 are implemented, a message sent by a
Rich OS should be received by a hypervisor and the Secure world. Within the Secure world
the message needs to be seen by a Trusted OS, if present, and by any secure platform
firmware. This means that each level of supervisory software can determine whether it
must perform context saving.
ARM expects that the Exception level with the highest privilege, as defined in section 3.2,
to be the component that can program the power controller to enter an idle state. Typically,
this is the secure platform firmware. PSCI provides a mechanism for the OSPM to pass the
desired idle state to the next Exception level.
For standby states that do not require any explicit programming of the power controller, no
specific interface is required. The OSPM can use WFI or WFE instructions directly.
However, for deeper standby or retention states that require programming a power
controller, PSCI provides an interface that can hide the platform-specific code that
accesses the power controller.
Power-down states require an interface so that each level of execution can save and
restore its context appropriately. For power-down states, the interface requires a return
address. This is the address at which the calling OS expects resumption of execution on
wakeup at its Exception level. From a powered-down state, the core restarts at the reset
vector, in Secure state if the implementation includes EL3. After initializing, the Secure
world must re-start execution of the OS that called the power down interface, at the
required return address. PSCI provide a method of specifying return addresses, and
cookies that can be used for pointers to saved context.
4.2 Power state system topologies and coordination
Multiprocessor systems can have a number of different power domains to power different
elements of the system. Each power domain might contain a combination of one or more
processing elements (such as cores, co-processors, or GPUs), memories (caches,
DRAMs), and fabric (for example inter and intra cluster coherency fabric).
Each component in a power domain has a set of power states that affect the components
in the domain. Although physically the power domains are not necessarily built in a
hierarchical fashion, from a software control point of view, they are arranged in a logical
hierarchy. The hierarchy arises out of ordering dependencies that are required when