没有合适的资源?快使用搜索试试~ 我知道了~
首页Oracle Solaris 9 - IPsec and IKE Administration Guide
Oracle Solaris 9 - IPsec and IKE Administration Guide
需积分: 5 1 下载量 40 浏览量
更新于2023-11-23
收藏 732KB PDF 举报
本文是关于Oracle Solaris 9 - IPsec和IKE管理指南的描述。该指南的编号为817-2694.pdf,出版商是Sun Microsystems, Inc.该指南提供了有关IPsec和IKE管理的详细说明。 本文提到,该指南提供了有关Oracle Solaris 9操作系统中IPsec和IKE管理的指导。这份指南的第一个版本是在2003年12月出版的,编号为817-2694-10。版权归Sun Microsystems, Inc.所有。 该指南的目的是帮助用户了解和使用Oracle Solaris 9中的IPsec和IKE功能。它包含了关于配置、管理和故障排除IPsec和IKE的详细信息。指南中描述了在使用IPsec和IKE过程中的不同方面,包括安全策略、密钥管理、网络配置等。它提供了使用命令行界面和图形界面来配置和管理IPsec和IKE的步骤。 此外,该指南还提到了版权保护措施。它指出,这份指南受版权保护,并受到许可限制其使用、复制、分发和反编译。未经Sun及其许可方事先书面授权,本产品或文档的任何部分都不能以任何形式复制。 最后,本文提到该产品可能包含第三方软件的版权和许可。其中包括字体技术,这些软件是从Sun的供应商处获得许可并受版权保护。此外,部分产品可能源自加州大学授权的伯克利BSD系统。UNIX是在美国和其他国家/地区的注册商标。 总之,本文总结了Oracle Solaris 9 - IPsec和IKE管理指南的一些重要信息。阅读这份指南可以帮助用户了解和管理Oracle Solaris 9中的IPsec和IKE功能。
资源详情
资源推荐
Protection Mechanisms
IPsec provides two mechanisms for protecting data:
■
Authentication Header (AH)
■
Encapsulating Security Payload (ESP)
Both mechanisms have their own Security Association Database (SADB).
Authentication Header
The authentication header provides data authentication, strong integrity, and replay
protection to IP datagrams. AH protects the greater part of the IP datagram. AH
cannot protect fields that change nondeterministically between sender and receiver.
For example, the IP TTL field is not a predictable field and, consequently, not protected
by AH. AH is inserted between the IP header and the transport header. The transport
header can be TCP, UDP, ICMP, or another IP header when tunnels are being used. See
the tun(7M) man page for details on tunneling.
Authentication Algorithms and the AH Module
IPsec implements AH as a module that is automatically pushed on top of IP. The
/dev/ipsecah entry tunes AH with the ndd command. Future authentication
algorithms can be loaded on top of AH. Current authentication algorithms include
HMAC-MD5 and HMAC-SHA-1. Each authentication algorithm has its own key size
and key format properties. See the authmd5h(7M) and authsha1(7M) man pages for
details. For tuning IP configuration parameters, see the ndd(1M) man page.
Security Considerations for AH
Replay attacks threaten an AH when an AH does not enable replay protection. An AH
does not protect against eavesdropping. Adversaries can still see data that is protected
with AH.
Encapsulating Security Payload
The encapsulating security payload (ESP) header provides confidentiality over what
the ESP encapsulates, as well as the services that AH provides. However, ESP only
provides its protections over the part of the datagram that ESP encapsulates. ESP’s
authentication services are optional. These services enable you to use ESP and AH
together on the same datagram without redundancy. Because ESP uses
encryption-enabling technology, ESP must conform to U.S. export control laws.
16 IPsec and IKE Administration Guide • December 2003

ESP encapsulates its data, so ESP only protects the data that follows its beginning in
the datagram. In a TCP packet, ESP encapsulates only the TCP header and its data. If
the packet is an IP-in-IP datagram, ESP protects the inner IP datagram. Per-socket
policy allows self-encapsulation, so ESP can encapsulate IP options when ESP needs to.
Unlike the authentication header (AH), ESP allows multiple kinds of datagram
protection. Using only a single form of datagram protection can make the datagram
vulnerable. For example, if you use ESP to provide confidentiality only, the datagram
is still vulnerable to replay attacks and cut-and-paste attacks. Similarly, if ESP protects
only integrity, ESP could provide weaker protection than AH. The datagram would be
vulnerable to eavesdropping.
Algorithms and the ESP Module
IPsec ESP implements ESP as a module that is automatically pushed on top of IP. The
/dev/ipsecesp entry tunes ESP with the ndd command. ESP allows encryption
algorithms to be pushed on top of ESP, in addition to the authentication algorithms
that are used in AH. Encryption algorithms include Data Encryption Standard (DES),
Triple-DES (3DES), Blowfish, and AES. Each encryption algorithm has its own key size
and key format properties. Because of export laws in the United States and import
laws in other countries, not all encryption algorithms are available outside of the
United States. For tuning IP configuration parameters, see the ndd(1M) man page.
Security Considerations for ESP
An ESP without authentication is vulnerable to cut-and-paste cryptographic attacks
and to replay attacks. When you use ESP without confidentiality, ESP is as vulnerable
to eavesdropping as AH is.
Authentication and Encryption Algorithms
IPsec uses two types of algorithms, authentication and encryption. The authentication
algorithms and the DES encryption algorithms are part of core Solaris installation. If
you plan to use other algorithms that are supported for IPsec, you must install the
Solaris Encryption Kit. The Solaris Encryption Kit is provided on a separate CD.
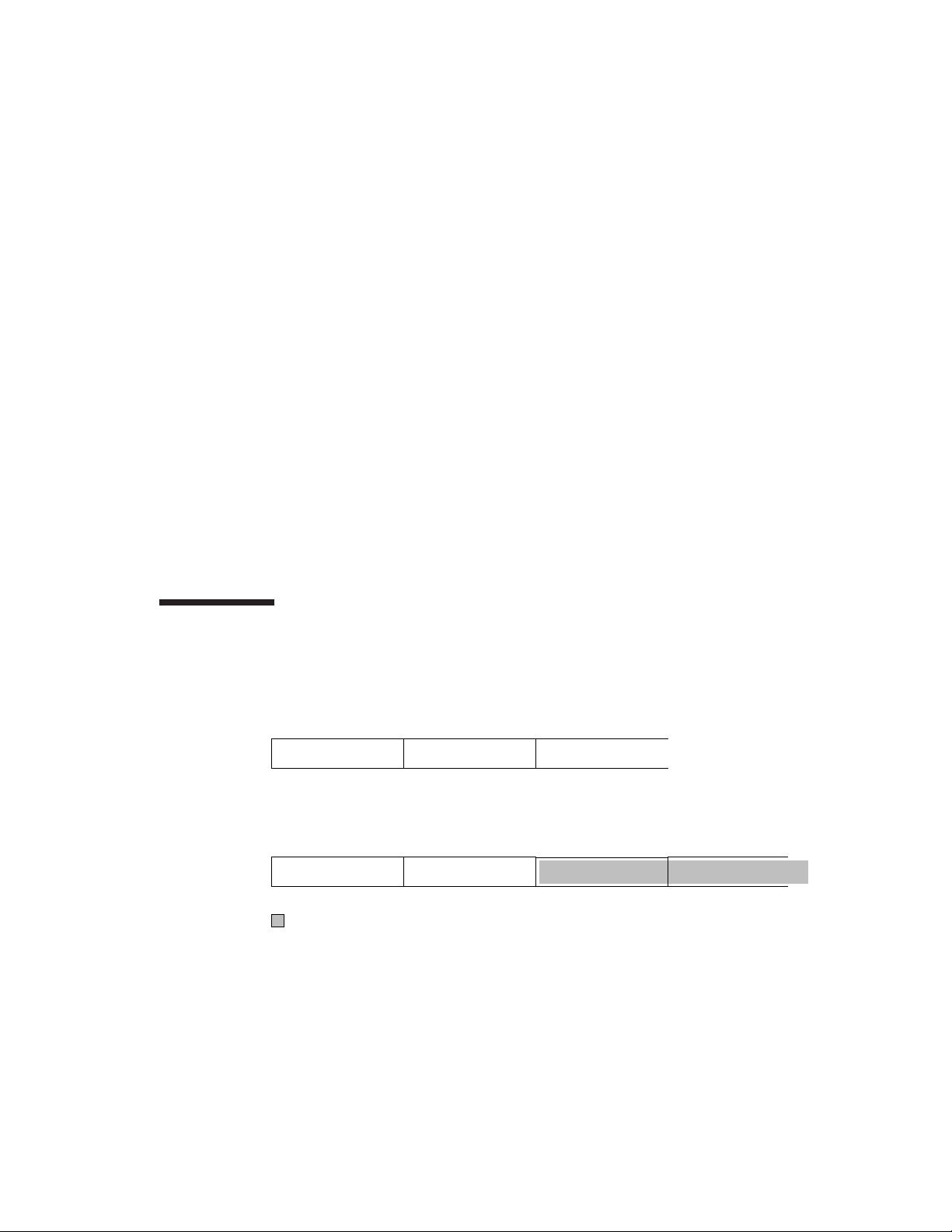
Authentication Algorithms
Authentication algorithms produce an integrity checksum value or digest that is based
on the data and a key. The man pages for authentication algorithms describe the size
of both the digest and key. The following table lists the authentication algorithms that
are supported in the Solaris operating environment. The table also lists the format of
the algorithms when the algorithms are used as security options to the IPsec utilities
and their man page names.
Chapter 1 • IP Security Architecture (Overview) 17
TABLE 1–1 Supported Authentication Algorithms
Algorithm Name Security Option Format Man Page
HMAC-MD5 md5, hmac-md5 authmd5h(7M)
HMAC-SHA-1 sha, sha1, hmac-sha, hmac-sha1 authsha1(7M)
Encryption Algorithms
Encryption algorithms encrypt data with a key. The algorithms operate on data in
units of a block size. The man pages for encryption algorithms describe the block size
and the key size for each algorithm. By default, the DES–CBC and 3DES-CBC
algorithms are installed.
The AES and Blowfish algorithms are available to IPsec when you install the Solaris
Encryption Kit. The kit is available on a separate CD that is not part of the Solaris 9
installation box. The Solaris 9 Encryption Kit Installation Guide describes how to install
the Solaris Encryption Kit.
The following table lists the encryption algorithms that are supported in the Solaris
operating environment. The table lists the format of the algorithms when the
algorithms are used as security options to the IPsec utilities. The table also lists their
man page names, and lists the package that contains the algorithm.
TABLE 1–2 Supported Encryption Algorithms
Algorithm Name Security Option Format Man Page Package
DES-CBC des, des-cbc encrdes(7M) SUNWcsr,
SUNWcarx.u
3DES–CBC or
Triple-DES
3des, 3des-cbc encr3des(7M) SUNWcsr,
SUNWcarx.u
Blowfish blowfish, blowfish-cbc encrbfsh(7M) SUNWcryr,
SUNWcryrx
AES-CBC aes, aes-cbc encraes(7M) SUNWcryr,
SUNWcryrx
Protection Policy and Enforcement
Mechanisms
IPsec separates its protection policy from its enforcement mechanisms. You can enforce
IPsec policies in the following places:
18 IPsec and IKE Administration Guide • December 2003
■
On a system-wide level
■
On a per-socket level
You use the ipsecconf command to configure the system-wide policy. See the
ipsecconf(1M) man page.
IPsec applies the system-wide policy to incoming datagrams and outgoing datagrams.
You can apply some additional rules to outgoing datagrams, because of the additional
data that is known by the system. Inbound datagrams can be either accepted or
dropped. The decision to drop or accept an inbound datagram is based on several
criteria, which sometimes overlap or conflict. Conflicts are resolved by determining
which rule is parsed first. Except when a policy entry states that traffic should bypass
all other policy, the traffic is automatically accepted. Outbound datagrams are either
sent with protection or without protection. If protection is applied, the algorithms are
either specific or non-specific.
The policy that normally protects a datagram can be bypassed. You can either specify
an exception in the system-wide policy, or you can request a bypass in the per-socket
policy. For intra-system traffic, policies are enforced, but actual security mechanisms
are not applied. Instead, the outbound policy on an intra-system packet translates into
an inbound packet that has had those mechanisms applied.
Transport and Tunnel Modes
When you invoke ESP or AH after the IP header to protect a datagram, you are using
transport mode. An example follows. A packet starts off with the following header:
IP Hdr TCP Hdr
ESP, in transport mode, protects the data as follows:
IP Hdr
Encrypted
ESP TCP Hdr
AH, in transport mode, protects the data as follows:
Chapter 1 • IP Security Architecture (Overview) 19
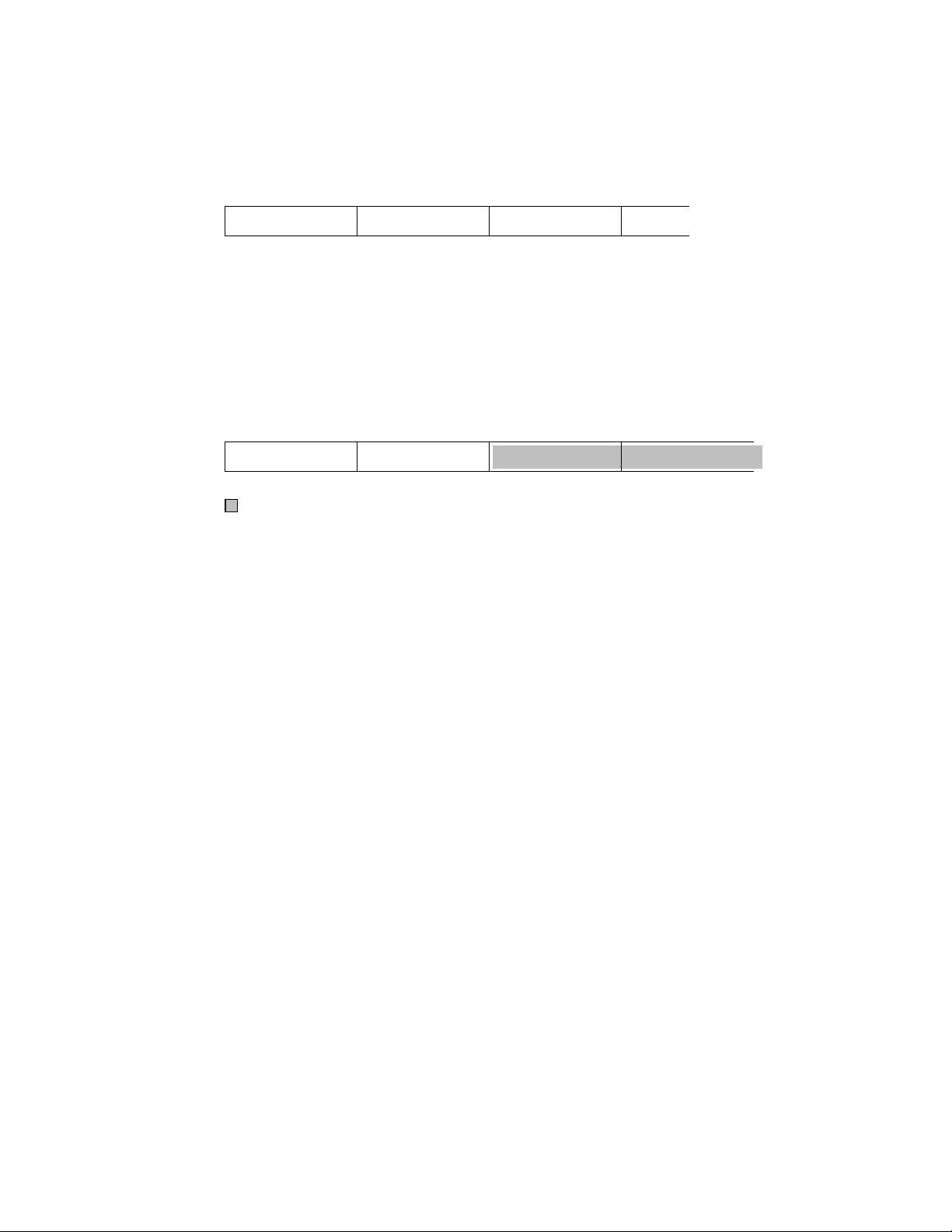
IP Hdr AH TCP Hdr
AH actually covers the data before the data appears in the datagram. Consequently,
the protection that is provided by AH, even in transport mode, covers some of the IP
header.
When an entire datagram is inside the protection of an IPsec header, IPsec is protecting
the datagram in tunnel mode. Because AH covers most of its preceding IP header,
tunnel mode is usually performed only on ESP. The previous example datagram
would be protected in tunnel mode as follows:
IP Hdr
Encrypted
ESP IP Hdr TCP Hdr
In tunnel mode, the inner header is protected, while the outer IP header is
unprotected. Often, the outer IP header has different source and different destination
addresses from the inner IP header. The inner and outer IP headers can match if, for
example, an IPsec-aware network program uses self-encapsulation with ESP.
Self-encapsulation with ESP protects an IP header option.
The Solaris implementation of IPsec is primarily an implementation of IPsec in
transport mode. Tunnel mode is implemented as a special instance of the transport
mode. The implementation treats IP-in-IP tunnels as a special transport provider. The
ifconfig configuration options to set tunnels are nearly identical to the options that
are available to socket programmers when enabling per-socket IPsec. Also, tunnel
mode can be enabled in per-socket IPsec. In per-socket tunnel mode, the inner packet
IP header has the same addresses as the outer IP header. For details on per-socket
policy, see the ipsec(7P) man page. For configuring tunnels, see the ifconfig(1M)
man page.
Trusted Tunnels
A configured tunnel is a point-to-point interface. The tunnel enables an IP packet to be
encapsulated within an IP packet. A correctly configured tunnel requires both a tunnel
source and a tunnel destination. For more information, see the tun(7M) man page and
“Solaris Tunneling Interfaces for IPv6” in System Administration Guide: IP Services.
20 IPsec and IKE Administration Guide • December 2003
剩余101页未读,继续阅读
weixin_40191861_zj
- 粉丝: 67
- 资源: 1万+
上传资源 快速赚钱
 我的内容管理
收起
我的内容管理
收起
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

会员权益专享
最新资源
- 利用迪杰斯特拉算法的全国交通咨询系统设计与实现
- 全国交通咨询系统C++实现源码解析
- DFT与FFT应用:信号频谱分析实验
- MATLAB图论算法实现:最小费用最大流
- MATLAB常用命令完全指南
- 共创智慧灯杆数据运营公司——抢占5G市场
- 中山农情统计分析系统项目实施与管理策略
- XX省中小学智慧校园建设实施方案
- 中山农情统计分析系统项目实施方案
- MATLAB函数详解:从Text到Size的实用指南
- 考虑速度与加速度限制的工业机器人轨迹规划与实时补偿算法
- Matlab进行统计回归分析:从单因素到双因素方差分析
- 智慧灯杆数据运营公司策划书:抢占5G市场,打造智慧城市新载体
- Photoshop基础与色彩知识:信息时代的PS认证考试全攻略
- Photoshop技能测试:核心概念与操作
- Photoshop试题与答案详解
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功