nent communicates with www.tarot.com and has no
access to user data. Another component has access to
user’s birthday, but does not communicate with any ex-
ternal entity.
From an end user’s perspective, the applications are
monolithic as the user does not know about the compo-
nents. At the time of adding a particular application, the
user is presented with a manifest that states what user
profile data is needed by the application and which ex-
ternal entity will it be sharing this data with. For exam-
ple, horoscope’s manifest would specify that it does not
share any information with any external entity. Note that
the horoscope application does not need to reveal that it
communicates with www.tarot.com as no user infor-
mation is being sent to www.tarot.com. The user can
now make a more informed decision before adding the ap-
plication. Admittedly, the user will need to make a trust
decision with respect to the parties with which the appli-
cation shares user data, but these external parties can be
expected to be larger and better branded entities providing
internet services, such as Google for ads, Yahoo for maps,
etc.
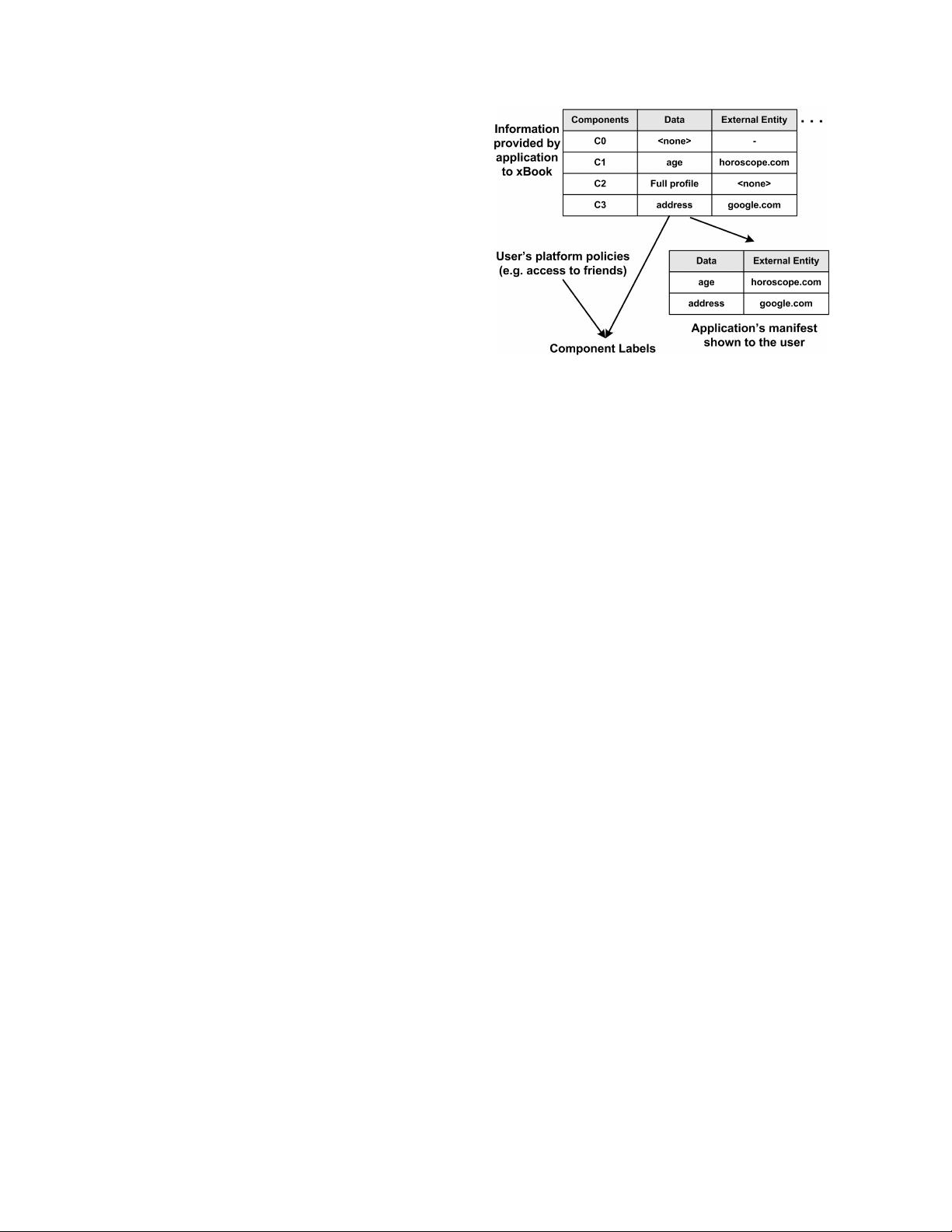
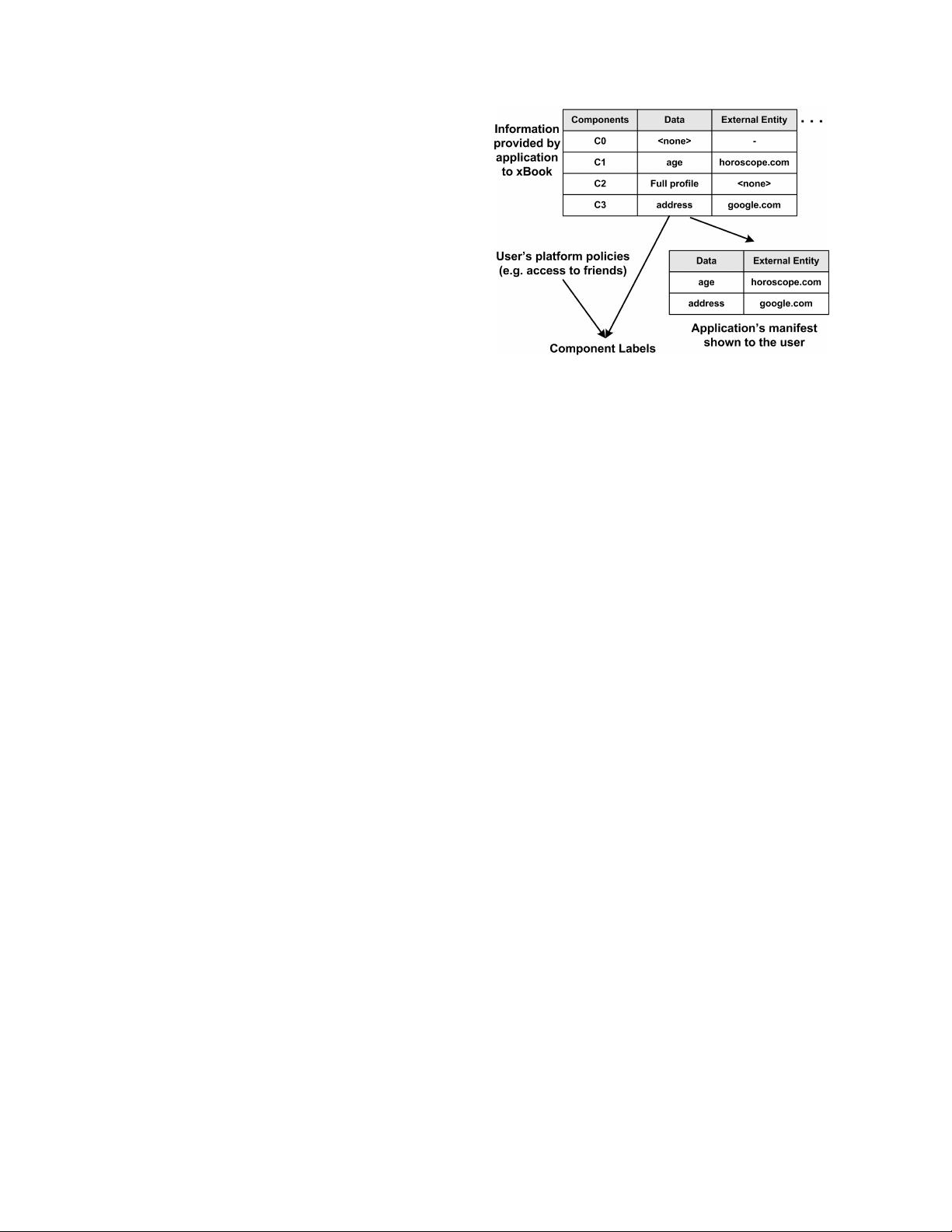
Figure 2 shows a typical life cycle of an application.
The developer of an application decides on the structure of
the components for that application and during the appli-
cation’s deployment on xBook, he specifies the informa-
tion required by each component and the external entity a
particular component needs to communicate with. xBook
uses this information to generate the manifest for the ap-
plication. As shown in the figure, a manifest is basically a
set that specifies all of the application’s external commu-
nications (irrespective of the components) along with the
user’s profile data that is shared for each communication.
Additionally, the xBook platform ensures that all of the
application’s components comply with the user’s privacy
policy and the manifest approved by the user. We discuss
this further using the case study of an example application
in Section 6.3.
The division of an application into multiple compo-
nents allows the application writer to develop different
functionality within an application that rely on different
pieces of the user profile. For example, let us consider
an application that requires a user’s information to gen-
erate a customized profile for the user. It also requires
his address information to be passed to Google to gener-
ate a map showing the address. In the application design
of current social networks, the application would be able
to pass all information about the user to Google. In the
xBook framework, the application would be split into two
components: the first component presents the customized
profile of the user, has full access to the user’s data and
is not allowed to communicate with Google; the second
component encapsulates the user’s address (with no map-
ping to the user’s profile) that is passed to Google to gen-
Figure 2: Typical life cycle of an application in xBook.
erate the map. We discuss some example applications in
Section 7.1.
Figure 3 shows a high-level design of our xBook frame-
work. There are two parts of the xBook platform, one that
runs on the server-side and another that executes on the
client-side in the user’s browser (Figure 3). The applica-
tion components, in turn, are also split into client-side and
server-side components. The components are written in a
safe subset of javascript, called ADsafe [1], which facili-
tates confinement of these components in our xBook im-
plementation. Any communication to and from the com-
ponents occurs by using xBook APIs, thereby allowing
all such communication to be mediated by xBook. Each
component is associated with a privilege level or label that
is derived from the application’s manifest. The platform
mediates the information flow between the components
based on these labels (Section 6).
Both client-side and server-side components commu-
nicate with server-side storage to retrieve data. There
are two types of storage in xBook system: one for stor-
ing xBook data that includes user profiles, and second for
the data stored by the application. While the structure of
xBook data is known, the semantic of the application data
is internal to the application and hence unknown to the
platform. All data fields are labeled to control access by
application components. These labels are assigned based
on high-level user-defined policies, such as a policy al-
lowing access to only the user’s friends, and the manifest
approved by the user (Figure 2).
To store application data with unknown structure and
semantics, xBook contains a group of storage pools,
where data is stored as a set of name-value pairs. An ap-
plication can have multiple storage pools, which could be
for each user or for user-independent data.
3.1 Leakage Prevention by xBook Design
In the current platform designs, a user’s information
can be leaked in three major ways: (1) applications can