iPod高级控制协议详解与实用命令
iPod超级协议是一种专为开发与iPod交互的外部设备而设计的通信规范,它允许通过串口进行高级控制和数据传输。这个协议的核心是基于二进制命令和参数的结构化通讯,确保了设备间的稳定连接和数据交换。
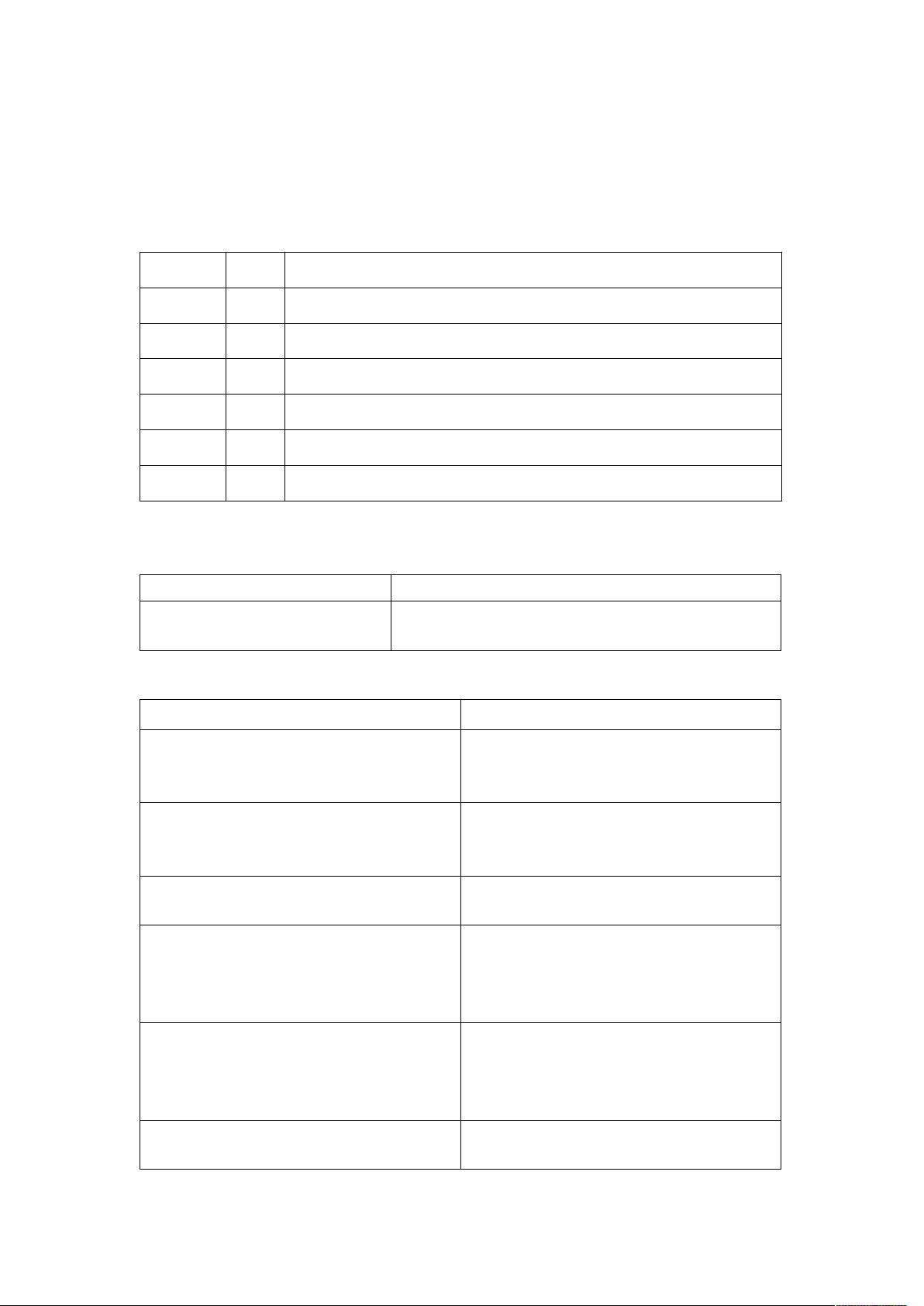
1. **通讯格式**:
- 每个消息由固定的头部(0xff0x55)、长度、模式、命令、可选参数和校验码组成。头部用于识别消息的起始,长度字段指示后续数据的总大小,包括模式、命令和参数。
- 校验码是通过对所有长度、模式、命令和参数字节求和后,再取反减去100,最后对1取模得到的结果。
2. **具体命令说明**:
- **打开高级控制模式**: 使用命令0xff0x550x030x000x01,这会开启iPod的串口连接并进入可以执行复杂操作的模式。
- **ping指令**: 发送0xFF0x550x030x040x00,若连接正常,会返回0xFF0x550x0B0x04,表示成功连接。
- **成功连接确认**: 成功连接时,返回信息可能包含0x0B040003FFFFFFFF0000,其中0000F2表示连接状态为成功。
- **错误处理**: 如果命令未被理解,会返回0x000x01加上结果码,如0x000x01表示命令未成功执行,0x000x03表示超出范围。
3. **命令解析**:
- 命令0x040xf8可能是用于检查或确认某个操作的状态,而0xFF表示可能的结果0x04。
- 0xFF0x550x030x000x01后的0x000x01表示命令未被正确执行,可能是命令格式不正确或不在支持范围内。
- 当设置特定标志(例如track-change flag)时,可能会改变返回值,比如0x0b可能是某种状态指示,但具体内容需根据上下文解析。
掌握iPod超级协议对于开发兼容的外部设备至关重要,因为它规定了如何安全地请求和接收数据,以及如何处理可能的错误和反馈。通过理解和遵循这些规则,开发者能够创建出与iPod无缝集成的设备,提升用户体验。
2021-05-30 上传
点击了解资源详情
2021-05-30 上传
2024-11-07 上传
mcu_mouse
- 粉丝: 2
- 资源: 5
最新资源
- 探索数据转换实验平台在设备装置中的应用
- 使用git-log-to-tikz.py将Git日志转换为TIKZ图形
- 小栗子源码2.9.3版本发布
- 使用Tinder-Hack-Client实现Tinder API交互
- Android Studio新模板:个性化Material Design导航抽屉
- React API分页模块:数据获取与页面管理
- C语言实现顺序表的动态分配方法
- 光催化分解水产氢固溶体催化剂制备技术揭秘
- VS2013环境下tinyxml库的32位与64位编译指南
- 网易云歌词情感分析系统实现与架构
- React应用展示GitHub用户详细信息及项目分析
- LayUI2.1.6帮助文档API功能详解
- 全栈开发实现的chatgpt应用可打包小程序/H5/App
- C++实现顺序表的动态内存分配技术
- Java制作水果格斗游戏:策略与随机性的结合
- 基于若依框架的后台管理系统开发实例解析