没有合适的资源?快使用搜索试试~ 我知道了~
首页B-树:文件组织的标准选择
B-树:文件组织的标准选择
需积分: 9 4 下载量 180 浏览量
更新于2024-07-27
收藏 1.31MB PDF 举报
"The Ubiquitous B-Tree" 这篇文章主要探讨了B树在计算机科学中的广泛应用,特别是作为文件组织的标准。B树是一种自平衡的搜索树数据结构,它在数据库系统、用户文件索引以及通用访问方法中都有所应用。本文作者Douglas Comer对B树进行了回顾,并分析了其成功的原因。 B树的核心特性在于它能够保持数据结构的平衡,使得搜索、插入和删除操作的时间复杂度保持在一个相对较低的对数级别。这使得B树成为处理大量数据时的理想选择,尤其是在磁盘等次级存储设备上,因为这些设备的读写速度远慢于内存。 文章提到了B树的主要变种,包括B*树和B+树。B*树相比B树更倾向于保持内部节点的充分填充,减少了磁盘I/O操作,从而提高了性能。而B+树的所有数据都存储在叶子节点,并且叶子节点之间有指针连接,这样可以确保范围查询的高效性。每种实现方式都有其独特的优点和成本,适用于不同的场景。 此外,作者还介绍了一种使用B树实现的通用访问方法。这种方法利用B树的数据结构特性,能有效地支持各种数据操作,包括查找、插入和删除,同时兼顾到磁盘I/O效率。 关键词和短语包括:B树、B*树、B+树、文件组织、索引。根据CRC分类,该主题涉及到计算机科学的多个领域,如数据存储、数据库系统和文件系统设计。 B树及其变体在现代信息技术中扮演着至关重要的角色,它们的灵活性和效率使得它们在处理大规模数据时成为首选的数据结构。通过理解B树的工作原理和变种,开发者可以更好地设计和优化存储解决方案,提升系统的整体性能。
资源详情
资源推荐
124 • D. Comer
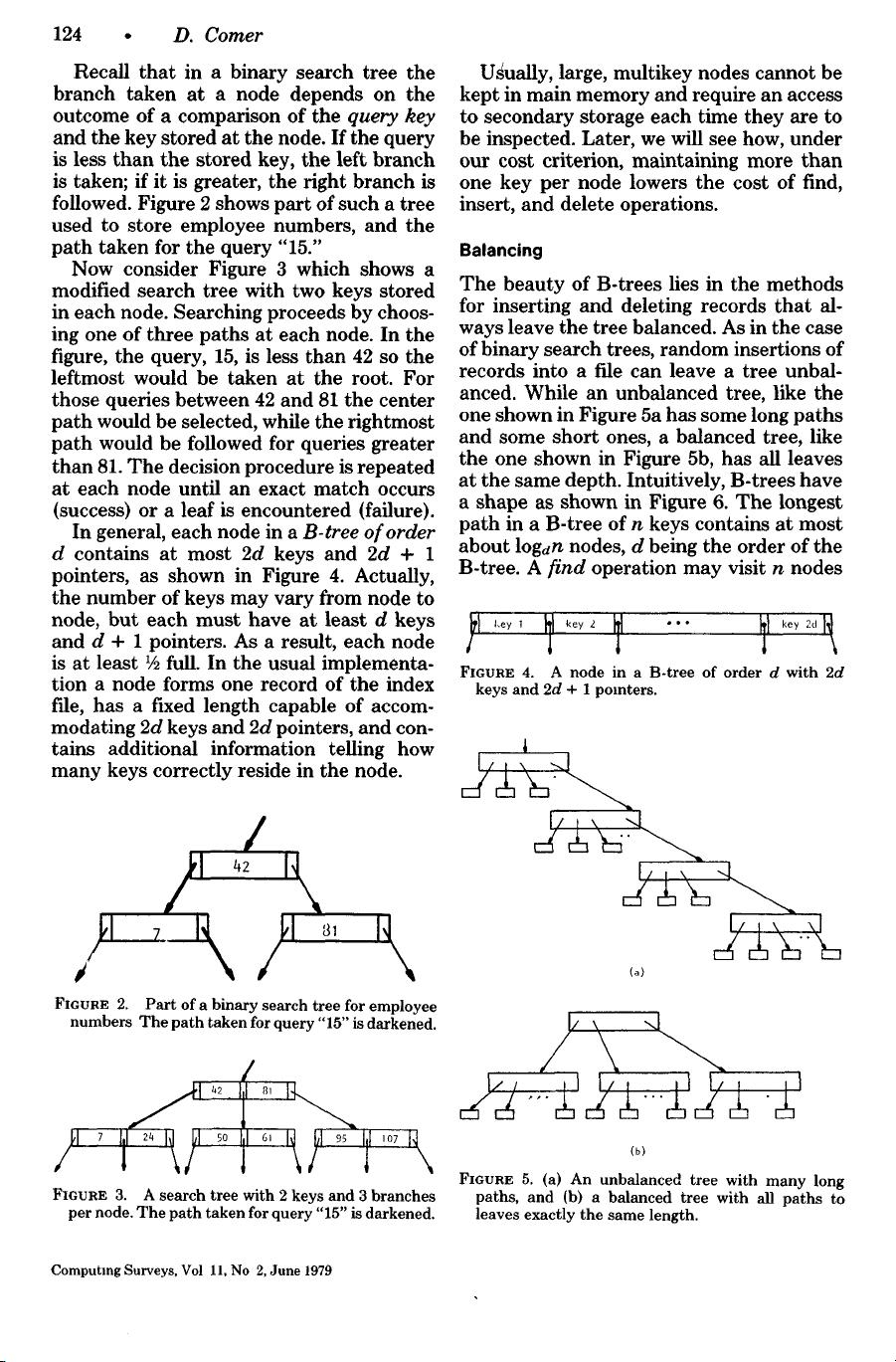
Recall that in a binary search tree the
branch taken at a node depends on the
outcome of a comparison of the query key
and the key stored at the node. If the query
is less than the stored key, the left branch
is taken; if it is greater, the right branch is
followed. Figure 2 shows part of such a tree
used to store employee numbers, and the
path taken for the query "15."
Now consider Figure 3 which shows a
modified search tree with two keys stored
in each node. Searching proceeds by choos-
ing one of three paths at each node. In the
figure, the query, 15, is less than 42 so the
leftmost would be taken at the root. For
those queries between 42 and 81 the center
path would be selected, while the rightmost
path would be followed for queries greater
than 81. The decision procedure is repeated
at each node until an exact match occurs
(success) or a leaf is encountered (failure).
In general, each node in a B-tree of order
d contains at most 2d keys and 2d + 1
pointers, as shown in Figure 4. Actually,
the number of keys may vary from node to
node, but each must have at least d keys
and d + 1 pointers. As a result, each node
is at least 1/~ full. In the usual implementa-
tion a node forms one record of the index
f'fle, has a fixed length capable of accom-
modating 2d keys and 2d pointers, and con-
tains additional information telling how
many keys correctly reside in the node.
/ \ / \
FIGURE 2. Part of a binary search tree for employee
numbers The path taken for query "15" is darkened.
/
I N\
/
!~2 I,I ~3, I
1
1
/
1
1 1
\
FIGURE 3. A search tree with 2 keys and 3 branches
per node. The path taken for query "15" is darkened.
Ugually, large, multikey nodes cannot be
kept in main memory and require an access
to secondary storage each time they are to
be inspected. Later, we will see how, under
our cost criterion, maintaining more than
one key per node lowers the cost of find,
insert, and delete operations.
Balancing
The beauty of B-trees lies in the methods
for inserting and deleting records that al-
ways leave the tree balanced. As in the case
of binary search trees, random insertions of
records into a file can leave a tree unbal-
anced. While an unbalanced tree, like the
one shown in Figure 5a has some long paths
and some short ones, a balanced tree, like
the one shown in Figure 5b, has all leaves
at the same depth. Intuitively, B-trees have
a shape as shown in Figure 6. The longest
path in a B-tree of n keys contains at most
about logdn nodes, d being the order of the
B-tree. A find operation may visit n nodes
FIGURE 4. A node in a B-tree of order d with 2d
keys and 2d + 1 pointers.
1
I,, , -, \1
I/t',
--1
I/i,, \1
I/ \ -..I
--....
(b)
FIGURE 5. (a) An unbalanced tree with many long
paths, and (b) a balanced tree with all paths to
leaves exactly the same length.
Computing Surveys, Vol 11, No 2, June 1979
剩余16页未读,继续阅读
rtxbc
- 粉丝: 5
- 资源: 17
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

最新资源
- 构建Cadence PSpice仿真模型库教程
- VMware 10.0安装指南:步骤详解与网络、文件共享解决方案
- 中国互联网20周年必读:影响行业的100本经典书籍
- SQL Server 2000 Analysis Services的经典MDX查询示例
- VC6.0 MFC操作Excel教程:亲测Win7下的应用与保存技巧
- 使用Python NetworkX处理网络图
- 科技驱动:计算机控制技术的革新与应用
- MF-1型机器人硬件与robobasic编程详解
- ADC性能指标解析:超越位数、SNR和谐波
- 通用示波器改造为逻辑分析仪:0-1字符显示与电路设计
- C++实现TCP控制台客户端
- SOA架构下ESB在卷烟厂的信息整合与决策支持
- 三维人脸识别:技术进展与应用解析
- 单张人脸图像的眼镜边框自动去除方法
- C语言绘制图形:余弦曲线与正弦函数示例
- Matlab 文件操作入门:fopen、fclose、fprintf、fscanf 等函数使用详解
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功