万事屋小贱 CTF全栈入门指南:从基础知识到高级攻击
"《CTF全栈指南(入门篇)》是一本由万事屋小贱所著的针对网络安全领域特别是Capture the Flag (CTF)比赛的全面教程。这本书特别注重新手入门,旨在帮助读者掌握CTF中的各类技能,包括Web、逆向工程、Pwn(Payload Writing)、密码学以及各种实用工具和技巧。
首先,书籍从网络通信和TCP/IP协议的基础知识开始,介绍了OSI七层模型与TCP/IP模型的关系,详细讲解了IPv4的子网掩码及其在实际网络环境中的应用。接着,章节深入到Pwn技术,涉及如何理解和利用程序漏洞,如栈溢出、函数指针、函数调用约定以及汇编语言中的特定函数如`objdump`和`__builtin_return_address`。
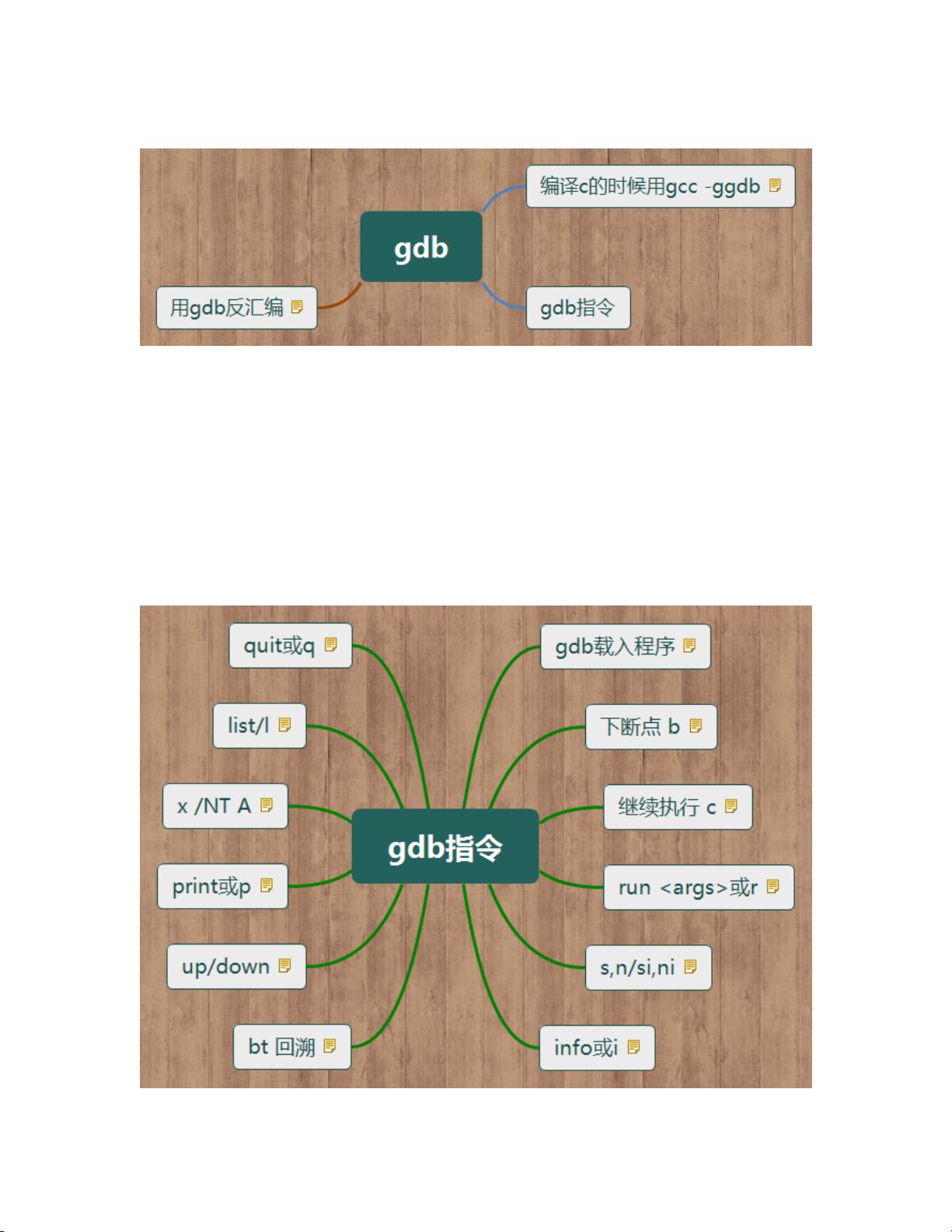
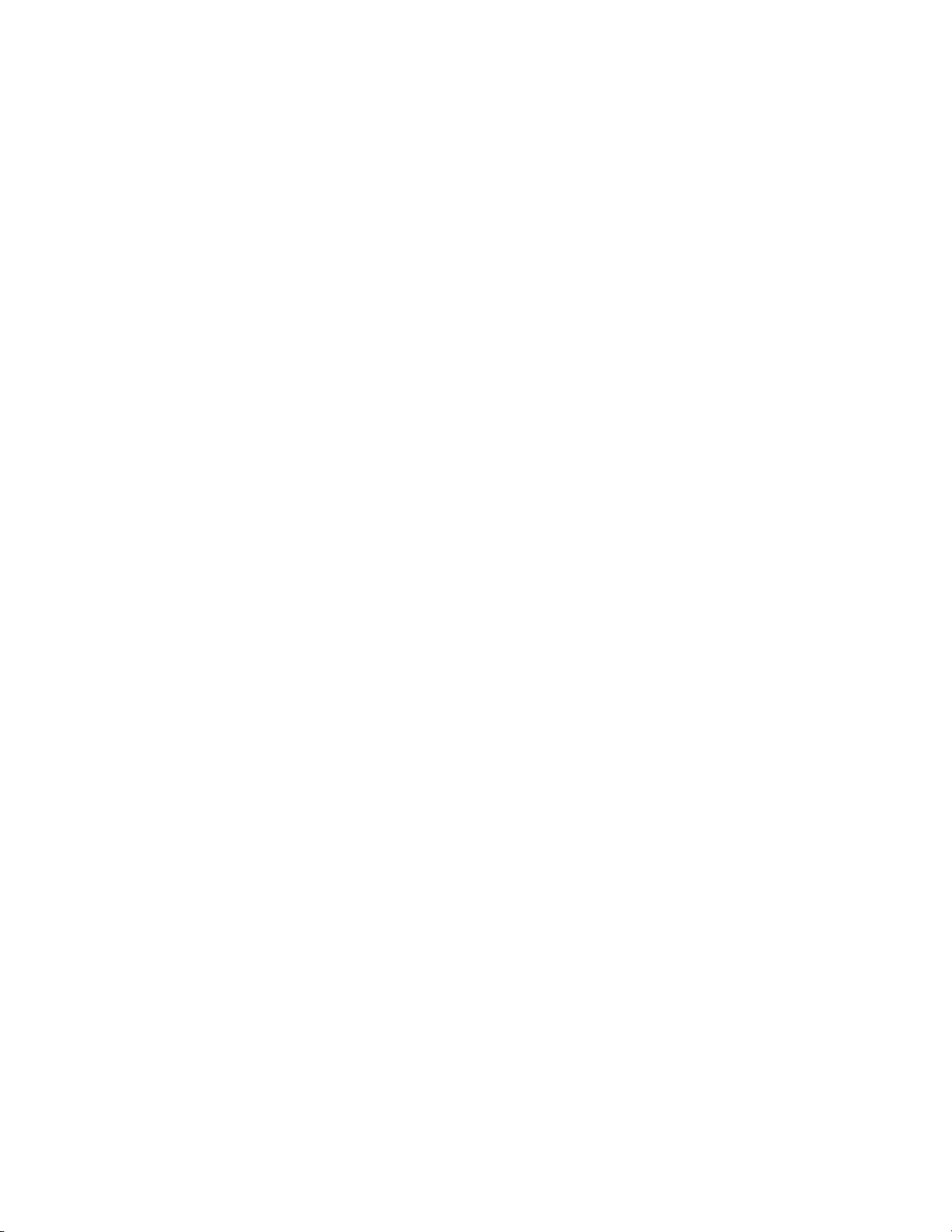
在逆向工程部分,书中涵盖了栈帧的理解、NX选项和GOT/PLT概念,以及信息泄露的实现方法,同时强调了`gdb`工具的使用和结合`checksec`脚本进行安全分析。此外,还介绍了Linux攻击的基本技巧,如利用缓冲区溢出、整数溢出和格式化字符串漏洞,以及高级攻击策略。
在Web安全方面,书中涵盖了ASCII码表、HTML实体符号表,以及Web开发者应具备的基础知识,如前端开发和常见的Web安全问题,如伪造IP、用户登录验证、验证码绕过、同源策略的理解等。信息收集是关键环节,书中介绍如何通过全面扫描、踩点网站、DNS解析、Whois查询、Nmap工具等手段获取目标信息。
关于SQL注入,本书提供了详尽的指导,包括错误注入、不同数据库系统的注入方法(MySQL、MSSQL、SQLite和PostgreSQL),以及基本的注入原理、判断类型、注入格式和使用工具如`sqlmap`进行自动化攻击。此外,还有挖掘经验和手动注入的深入剖析。
最后,书中还包含了一份黑客工具和技术的速查表(Cheat-sheet),帮助读者快速查阅和记忆关键知识点。整体而言,《CTF全栈指南(入门篇)》是一本实用的指南,适合希望在CTF竞赛或网络安全领域入门者阅读,无论是理论学习还是实战演练都极具价值。"
2024-01-14 上传
2023-06-21 上传
2024-12-01 上传
2021-07-17 上传
2023-04-26 上传
notwiner
- 粉丝: 22
- 资源: 2
最新资源
- VOIP的配置资料1111111111111
- WindowsXP对宽带连接速度进行了限制,是否意味着我们可以改造操作系统,得到更快的上网速度
- myeclipse优化详解
- 多媒体与数字图像压缩技术
- 分页的JSP代码分页的JSP代码
- 面向对象系统设计循序渐进
- 小型游戏贪吃蛇的程序
- PIC 单片机的C 语言编程.pdf
- 第2代图像压缩技术回顾与性能分析.pdf
- 基于游程编码的分块交叉数字图像压缩算法.pdf
- 三星s3c2410数据手册
- OpenSceneGraph Quick Start__ Guide
- 快速成型中基于ST EP 的直接分层算法
- memcached中文学习文档
- 基于本体实现网页规则分类的方法
- EXT中文框架学习文档