764 Peer-to-Peer Netw. Appl. (2016) 9:762–773
are formalized. We present notations and cryptographic
primitives in Section 3. In Section 4, we propose our
scheme. Followed by the security analysis and performance
evaluation of our scheme in Section 5 and Section 6, respec-
tively. We present the related work in Section 7. Finally, we
conclude this paper in Section 8.
2 System model and security requirements
2.1 System model
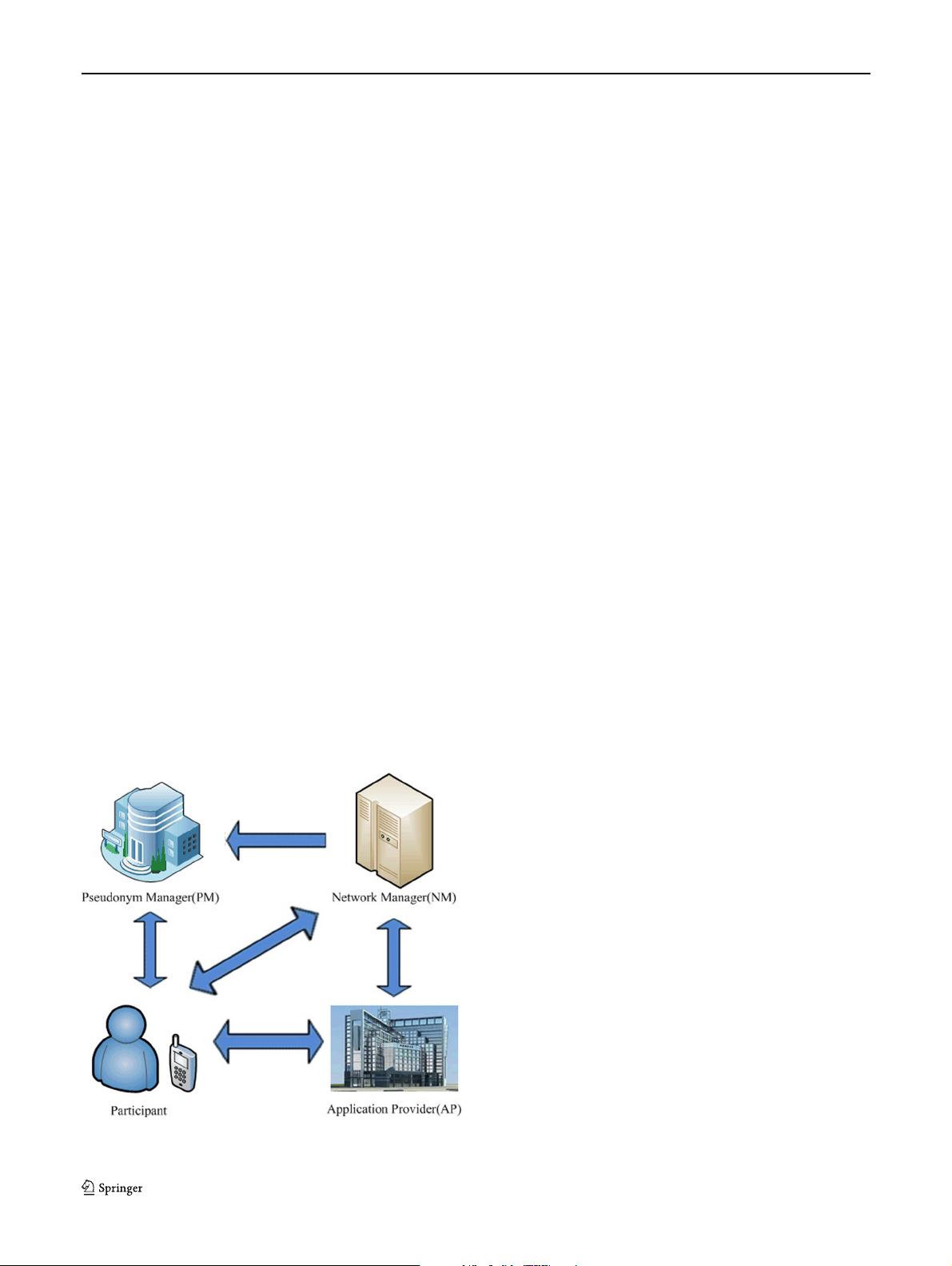
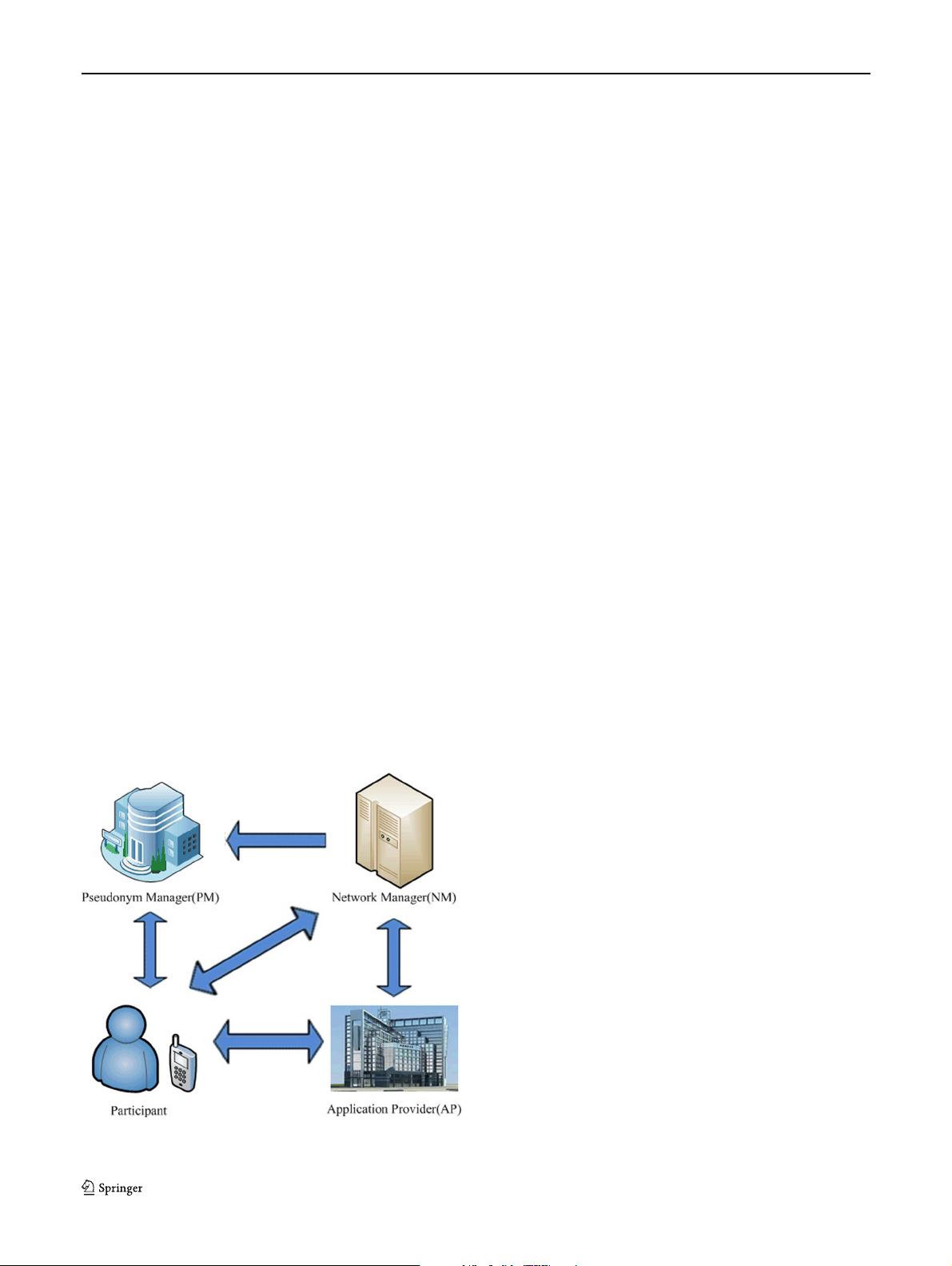
As shown in Fig. 2, there are four types of entities involved
in our scheme: participant, pseudonym manager(PM for
short), application provider(AP for short) and network man-
ager(NM for short).
– Participant: Participant is the entity that measures
and shares required data about a subject of inter-
est to the application provider by using sensors on
everyday devices, such as smart phones, personal
digital assistant(PDA). However, not all participants
are always honest since some participants maybe
misbehave.
– Pseudonym Manager(PM):PMisinchargeofmap-
ping the participant’s resources id(e.g., IP address,
MAC address), to the pseudonyms. PM is the first
entity that the participant must contact, which deter-
mines whether the participant is permitted to register or
not. As a result, PM’s duties are limited to determin-
ing the right of registration and mapping IP address to
pseudonym.
Fig. 2 System model for anonymous authentication scheme
– Application Provider(AP): AP not only provides the
services to the user but also manages the reputa-
tion scores of a participant, including scoring grades,
updating scores and modifying scores. In addtion, AP
maintains a blacklist which is used to determine parti-
cipant’s right of enjoying the anonymous environment
of MCS. AP lays down the policies that each participant
must satisfy, otherwise, the participant cannot enjoy the
anonymous environment.
– Network Manager(NM): NM is the control center of
the system. NM initializes the system parameters, such
as secret keys and secure hash functions, and issues
them to other entities. Moreover, NM is in charge of
maintaining and computing the participant’s current
scores and generating the participant’s credentials in
order to authenticate with AP. As we will explain, NM
only knows which AP that participant wants to con-
tact, the other information, such as the participant’s IP
address, is kept unknown.
2.2 Security requirements
We present informal definitions of the desired security prop-
erties. The security requirements in our scheme should
cover these four aspects.
– Anonymity: Adversary can get only a train of pseudo-
nyms of participants instead of the real identity based
on the existing communication.
– Blacklistability: Only a participant who is not in the
black list can obtain the anonymous service. In other
words, a participant cannot obtain the service if he has
been put in the backlist.
– Nonrepudiation: The property of nonreputation is a
fundamental requirement for our scheme. Namely, a
participant cannot deny that he has accessed the service
provided by AP.
– Unlinkability: All of the messages generated by a par-
ticipant should not leak any information to an adversary
by allowing the adversary to trace them.
3 Preliminaries
3.1 Notation
For easier illustration, Table 1 lists some important notations
which will be given further explanation where they occur
for the first time.
4 Proposed scheme
In this section, we propose our scheme, which mainly con-
sists of the following five phases: System Initialization,
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助 


 信息提交成功
信息提交成功