Gaëtan Leurent and Thomas Peyrin 7
difference of the two blocks have opposite signs: 0
δ
M
δ
O
and
δ
O
−δ
M
−δ
O
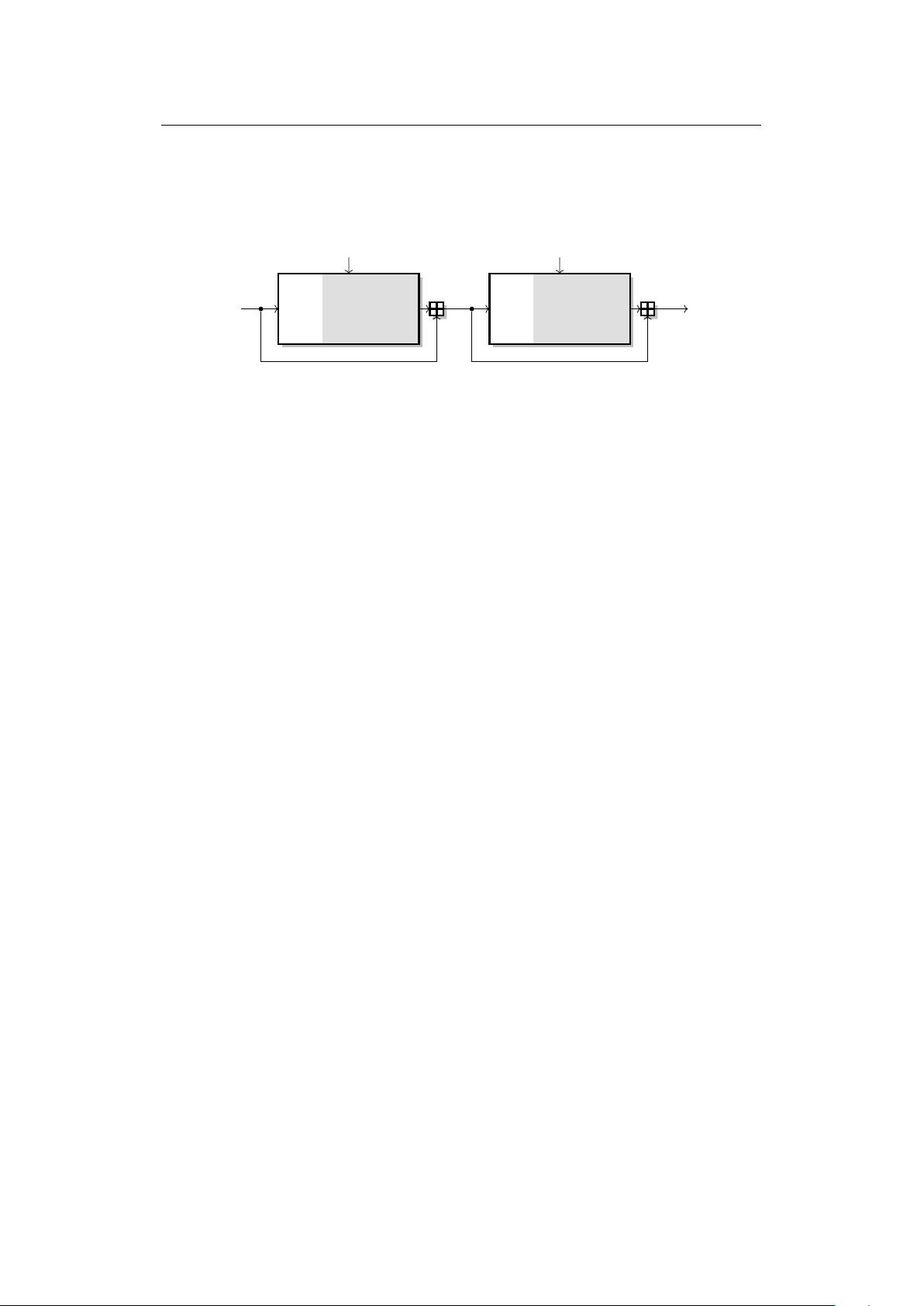
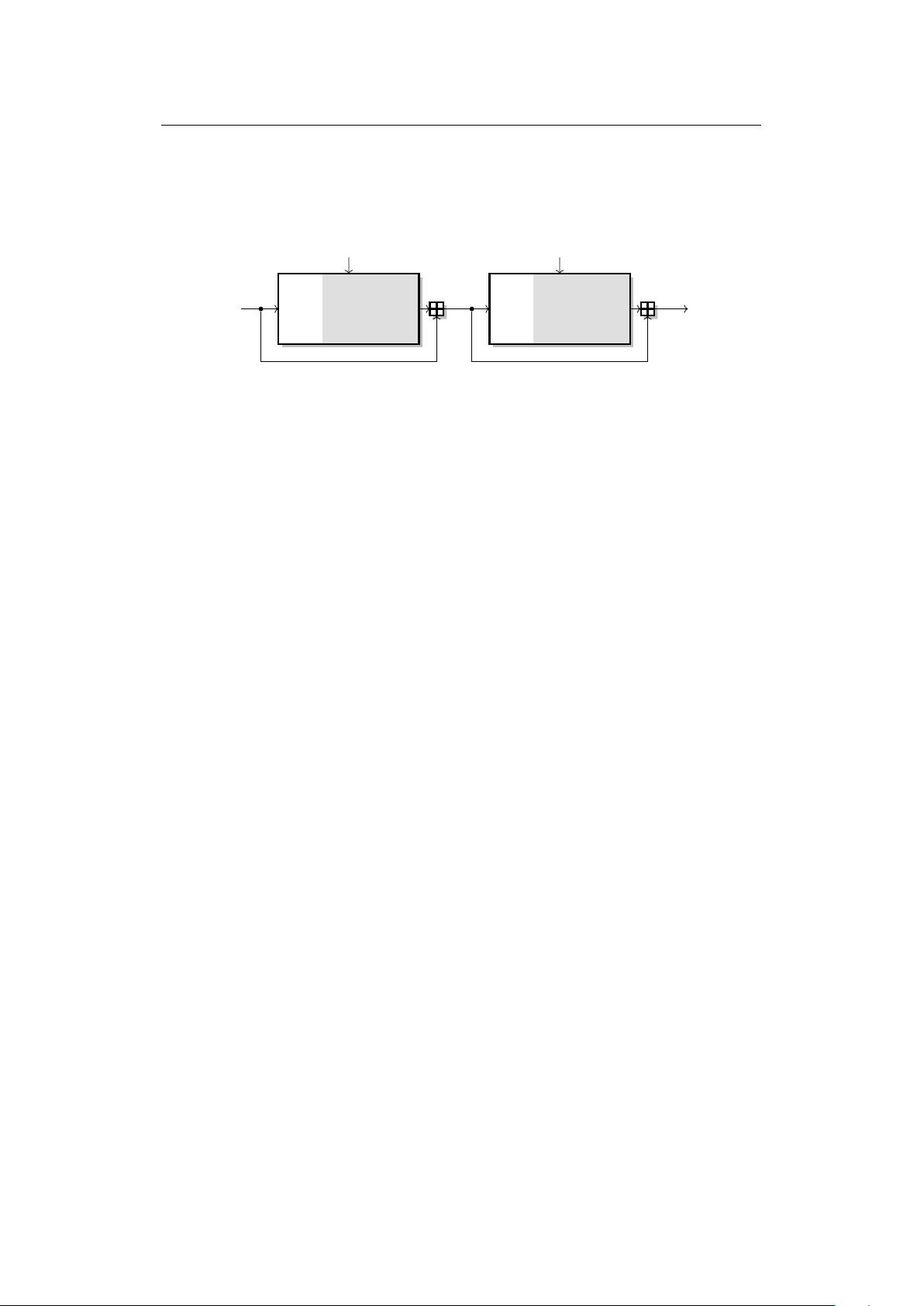
), one can see in
Figure 1 that a collision is obtained at the end of the second block because the internal
state differences cancel out.
IV H
m
1
m
2
hδ
M
i h−δ
M
i
h0i hδ
I
i hδ
O
i hδ
O
i h−δ
I
i h−δ
O
i
h0i hδ
O
i h0i
NL
1
NL
2
L L
Figure 1:
2-block collision attack using a linear trail
δ
I
δ
M
δ
O
and two non-linear trails
0
δ
I
and
δ
O
−δ
I
in the first 10 15 steps. Green values between bracket represent
differences in the state.
2.2.2 Computing a Collision for SHA-1 with Amortization Techniques
Once the differential trail is set, for each successive block the attacker can concentrate
on finding a pair of messages that follows it. For this, he constructs a large number of
messages that follow the trail up to some predetermined step (using the freedom degrees
available from the message input), and then computes the remaining
SHA-1
steps to test
whether the output difference is the expected one
δ
O
(this part is only probabilistic).
Compared to a pure naive search, it can be observed that the computational cost is
reduced by using a simple early-abort strategy for the 16 first steps. Yet, more advanced
amortization methods such as neutral bits [
BCJ
+
05
], boomerangs [
Kli06
,
JP07
] or message
modification [
WYY05
] can reach a few more steps further. Because of this amortization,
usually the first 20 or so steps do not contribute to the final complexity of the attack
(which is a good thing because the first 10
∼
15 steps of the differential path are non-linear
and thus will be verified with quite low probability).
Neutral bits were firstly introduced for the cryptanalysis of
SHA-0
[
BC04
,
BCJ
+
05
].
The idea is that once a message pair following the differential path until a certain step
x
was found, one could get another message pair valid until step
x
for free by applying a small
message modification (one or a few bits). The hope is basically that such a modification
would not interact too much with necessary conditions in the differential path before step
x
. The fact that a certain modification was neutral or not until a step
x
with a good
probability could be pre-analysed before running the attack and a key observation was
that any combination of two of more neutral bits until step
x
was likely to be neutral as
well until step x, which gives an exponential potential amortization.
Boomerangs [
JP07
] or tunnels [
Kli06
] are very similar amortization tools to neutral bits.
Basically, they can be seen as neutral bits that are planned in advance: build from one or
a few local collisions (or relaxed versions of a local collision), one expects this perturbation
to be neutral to the differential path after a few steps with a certain probability, but
extra conditions are forced in the internal state and message to increase this probability.
Boomerangs are generally more powerful than neutral bits (in the sense that they produce
candidates valid with high probability for later steps than classical neutral bits), but
consume more freedom degrees. For this reason, you can generally only place a few of
them due to a lack of available freedom degrees, but their amortization gain is almost a
factor 2.
Note that a lot of details have to be taken into account when using neutral bits or
boomerangs, as many equations between some internal state bits and potentially message
bits must be fulfilled in order for the planned differential path to be valid. Thus, one can’t
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助 


 信息提交成功
信息提交成功