没有合适的资源?快使用搜索试试~ 我知道了~
首页云辅助隐私保护移动健康监控系统设计
"本文主要探讨了云计算辅助的隐私保护移动健康监测系统(CAM)。随着移动通信和云计算技术的普及,移动健康(mHealth)监测作为一种革新性的医疗保健解决方案,旨在提升医疗服务的质量并降低费用。然而,这种便利性带来了严峻的隐私和知识产权挑战,这可能会阻碍mHealth技术的广泛应用。 CAM系统的关键目标是解决这些问题,设计出一种能够在保护用户隐私和监测服务提供商的知识产权的同时,提供安全且高效的远程健康数据监控和决策支持。核心创新包括: 1. 隐私保护机制:系统采用了先进的外包解密技术,将数据加密后的计算任务转移到云端,从而避免了数据在传输过程中的潜在泄露,确保了用户的个人健康信息得到严格的保密。 2. 关键私有代理重加密:为了进一步加强隐私保护,文中提出了一种新的私有代理重加密策略。通过这种技术,服务提供商可以在不掌握原始数据的情况下,对数据进行处理和转换,实现了数据在云中的安全操作,同时维护了服务提供商的算法和技术优势。 3. 安全与性能评估:论文详细地分析了系统的安全性,评估了其在保护隐私和执行任务效率之间的平衡。通过实验和理论分析,研究人员证明了CAM能够在满足隐私需求的同时,保持系统的稳定性和响应速度。 总结来说,CAM系统通过创新的隐私保护技术和计算模式,为移动健康监测的广泛应用扫清了障碍,为患者、医疗机构和数据服务商提供了一个安全、可靠且经济的平台,推动了医疗领域数字化转型的进步。然而,随着系统的实施,未来的研究还需关注法律法规、数据所有权和用户教育等方面,以确保全面的隐私保护和合规性。"
资源详情
资源推荐
4
(t
4
, Max]:
N
[0, t
4
]:
Y
(t
4
, Max]:
N
[0, t
4
]:
Y
(t
4
, Max]:
N
[0, t
4
]:
Y
(t
4
, Max]:
N
[0, t
4
]:
Y
(t
4
, Max]:
N
[0, t
4
]:
Y
(t
4
, Max]:
N
[0, t
4
]:
Y
(t
4
, Max]:
N
[0, t
4
]:
Y
[0, t
3
]:N
[0, t
3
]:N
(t
3
, Max]:Y
(t
3
, Max]:Y[0, t
3
]:N
(t
3
, Max]:Y
(t
3
, Max]:Y
[0, t
3
]:N
(t
1
, Max]: H[0, t
1
]: L
Systolic BP
[t
1
]
Missed
Medication [t
2
]
(t
2
, Max]:N
[0, t
2
]:Y
(t
2
, Max]:N
[0, t
2
]:Y
Missed
Medication [t
2
]
Physical Activity
[t
3
]
Physical Activity
[t
3
]
Physical Activity
[t
3
]
Physical Activity
[t
3
]
Normal Diet
[t
4
]
Normal Diet
[t
4
]
Normal Diet
[t
4
]
Normal Diet
[t
4
]
Normal Diet
[t
4
]
Normal Diet
[t
4
]
Normal Diet
[t
4
]
Normal Diet
[t
4
]
D
2
D
7
D
6
D
6
(t
4
, Max]:
N
[0, t
4
]:
Y
D
2
D
3
D
4
D
5
D
2
D
3
D
4
D
5
D
2
D
3
D
4
D
2
D
3
D
4
D
2
D
4
D
5
D
7
D
2
D
4
D
7
D
2
D
5
D
7
D
4
D
5
D
6
D
5
D
6
D
1
D
3
D
4
D
5
D
6
D
1
D
3
D
4
D
5
D
6
D
1
D
3
D
4
D
5
D
6
D
1
D
3
D
4
D
5
D
6
D
1
: Take extra medication
D
2
: Increase fluid intake
D
3
: Notify Physician
D
4
: Notify Next of Kin
D
5
: Modify daily diet
D
6
: Take regular medication
D
7
: Do not take next dosage of medication
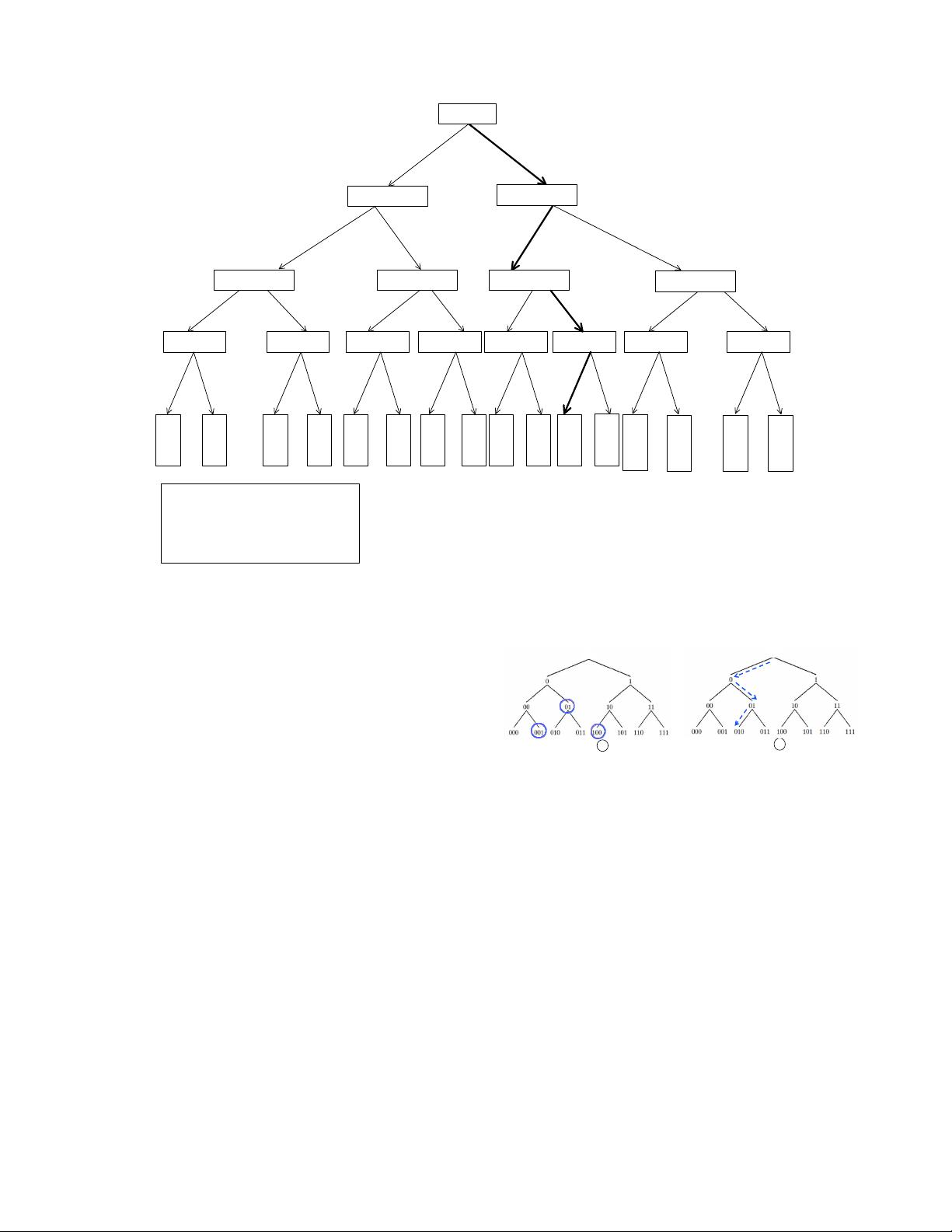
Fig. 2. Using branching program to represent a real monitoring program in MediNet project
h = L(1), else h = R(1). Repeat the process recursively for
p
h
, and so on, until one of the leaf nodes is reached with
decision information.
To illustrate how a practical monitoring program can be
transformed into a branching program, we use the monitor-
ing program introduced in the MediNet project [32], [33]
to construct a branching program as shown in Fig. 2. The
MediNet aims to provide automatic personalized monitoring
service for patients with diabetes or cardiovascular diseases.
Clients input their related health data such as systolic blood
pressure (BP), whether they missed daily medications or had
an abnormal diet, and the energy consumption of physical
activity to the decision support system, which will then
return a recommendation on how the clients can improve
their conditions. For instance, assume a hypertension patient
inputs an attribute vector consisting of the following elements
“[Systolic BP: 150, Missed one medication=0 (indicating he
did miss the medication), Energy Expenditure: 900 kcal,
salt intake: 1000 milligrams]” and the respective threshold
is “t
1
= 130, t
2
= 0, t
3
= 700kcal, t
4
= 1500”. The
recommendation returned from the monitoring program (Fig.
2) would be “ D
4
, D
5
, D
6
” (by following the path through
comparing each attribute element with the respective threshold
at each node), which indicates the clients need to “notify
next kin, modify daily diet, and take regular medication”. The
health data related to the input attribute vector can be sampled
either by a portable sensor or input by the client.
S
[001, 100]
={001, 01, 100}
S
010
={ŏ, 0, 01, 010}
ŏ
ŏ
Fig. 3. Basic idea of MDRQ
C. Homomorphic encryption
Homomorphic encryption is widely used as an underlying
tool for constructing secure protocols in the literature [34],
[35]. CAM adopts a semantically secure additively homomor-
phic public-key encryption technique. Intuitively, for homo-
morphic encryption HEnc(·), given two encrypted messages
HEnc(m
1
) and HEnc(m
2
), the encryption of the addition of
the two underlying messages can be computed additively as
follows: HEnc(m
1
+m
2
) = HEnc(m
1
)⋆HEnc(m
2
), where ⋆ is
the corresponding operation in the ciphertext space. A typical
additively homomorphic encryption scheme was proposed by
Paillier cryptosystem [36], [37]. Homomorphic encryption
enables a client to obtain the token corresponding to the input
attribute vectors obliviously from TA.
剩余16页未读,继续阅读
weixin_38722874
- 粉丝: 3
- 资源: 916
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

最新资源
- 李兴华Java基础教程:从入门到精通
- U盘与硬盘启动安装教程:从菜鸟到专家
- C++面试宝典:动态内存管理与继承解析
- C++ STL源码深度解析:专家级剖析与关键技术
- C/C++调用DOS命令实战指南
- 神经网络补偿的多传感器航迹融合技术
- GIS中的大地坐标系与椭球体解析
- 海思Hi3515 H.264编解码处理器用户手册
- Oracle基础练习题与解答
- 谷歌地球3D建筑筛选新流程详解
- CFO与CIO携手:数据管理与企业增值的战略
- Eclipse IDE基础教程:从入门到精通
- Shell脚本专家宝典:全面学习与资源指南
- Tomcat安装指南:附带JDK配置步骤
- NA3003A电子水准仪数据格式解析与转换研究
- 自动化专业英语词汇精华:必备术语集锦
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功