没有合适的资源?快使用搜索试试~ 我知道了~
首页林舒新书:经典与现代信道编码权威指南
林舒新书:经典与现代信道编码权威指南
"《Channel Codes Classical and Modern》是由林舒教授与他人合作的一本深入讲解数字通信和数据存储核心理论的图书。该书旨在为对信道编码领域没有先验知识的新手提供一个全面的入门指南,同时涵盖了现代通道编码技术的最新发展,如涡轮码和低密度奇偶校验(LDPC)码。 书中详尽阐述了诸如BCH码、Reed-Solomon码、卷积码、有限几何码以及产品码等经典编码方法,使读者能够系统地掌握这两种类别下的编码技术和设计原理。对于编码与解码过程,作者以其清晰易懂的笔触,详细介绍了各个环节的操作步骤和技术细节。 进一步,本书深入探讨了高级主题,如代码集性能分析和代数码设计,这些内容对于理解编码效率和优化通信系统的性能至关重要。值得一提的是,书中还提供了大量的练习题,共计250个,形式多样且富有挑战性,旨在通过实践增强学习者的理解和应用能力,使得无论是学生还是从业者都能从中受益匪浅。 作为一本不可或缺的资源,《Channel Codes Classical and Modern》不仅适合正在学习通信理论的基础学员,也适合在实际工作中寻求提升或研究最新编码技术的专业人士。它不仅是一份全面的参考书,更是一个引导读者从基础到进阶,全面掌握信道编码领域的宝典。"
资源详情
资源推荐

xiv Preface
been scattered across many journal and conference papers. With this book, those
entering the field of channel coding, and those wishing to advance their knowledge,
conveniently have a single resource for learning about both classical and modern
channel codes. Further, whereas the archival literature is written for experts, this
textbook is appropriate for both the novice (earlier chapters) and the expert (later
chapters). The book begins slowly and does not presuppose prior knowledge in the
field of channel coding. It then extends to frontiers of the field, as is evident from
the table of contents.
The topics selected for this book, of course, reflect the experiences and interests
of the authors, but they were also selected for their importance in the study of
channel codes – not to mention the fact that additional chapters would make the
book physically unwieldy. Thus, the emphasis of this book is on codes for binary-
input channels, including the binary-input additive white-Gaussian-noise channel,
the binary symmetric channel, and the binary erasure channel. One notable area
of omission is coding for wireless channels, such as MIMO channels. However, this
book is useful for students and researchers in that area as well because many of
the techniques applied to the additive white-Gaussian-noise channel, our main
emphasis, can be extended to wireless channels. Another notable omission is soft-
decision decoding of Reed–Solomon codes. While extremely important, this topic
is not as mature as those in this book.
Several different course outlines are possible with this book. The most obvious
for a first graduate course on channel codes includes selected topics from Chap-
ters 1, 2, 3, 4, 5, and 7. Such a course introduces the student to capacity limits for
several common channels (Chapter 1). It then provides the student with an intro-
duction to just enough algebra (Chapter 2) to understand BCH and Reed–Solomon
codes and their decoders (Chapter 3). Next, this course introduces the student to
convolutional codes and their decoders (Chapter 4). This course next provides the
student with an introduction to LDPC codes and iterative decoding (Chapter 5).
Finally, with the knowledge gained from Chapters 4 and 5 in place, the student
is ready to tackle turbo codes and turbo decoding (Chapter 7). The material con-
tained in Chapters 1, 2, 3, 4, 5, and 7 is too much for a single-semester course and
the instructor will have to select a preferred subset of that material.
For a more advanced course centered on LDPC code design, the instructor could
select topics from Chapters 10, 11, 12, 13, and 14. This course would first intro-
duce the student to LDPC code design using Euclidean geometries and projective
geometries (Chapter 10). Then the student would learn about LDPC code design
using finite fields (Chapter 11) and combinatorics and graphs (Chapter 12). Next,
the student would apply some of the techniques from these earlier chapters to
design codes for the binary erasure channel (Chapter 13). Lastly, the student
would learn design techniques for nonbinary LDPC codes (Chapter 14).
As a final example of a course outline, a course could be centered on computer-
based design of LDPC codes. Such a course would include Chapters 5, 6, 8,
and 9. This course would be for those who have had a course on classical channel

Preface
xv
codes, but who are interested in LDPC codes. The course would begin with an
introduction to LDPC codes and various LDPC decoders (Chapter 5). Then,
the student would learn about various computer-based code-design approaches,
including Gallager codes, MacKay codes, codes based on protographs, and codes
based on accumulators (Chapter 6). Next, the student would learn about assessing
the performance of LDPC code ensembles from a weight-distribution perspective
(Chapter 8). Lastly, the student would learn about assessing the performance of
(long) LDPC codes from a decoding-threshold perspective via the use of density
evolution and EXIT charts (Chapter 9).
All of the chapters contain a good number of problems. The problems are of
various types, including those that require routine calculations or derivations,
those that require computer solution or computer simulation, and those that might
be characterized as a semester project. The authors have selected the problems
to strengthen the student’s knowledge of the material in each chapter (e.g., by
requiring a computer simulation of a decoder) and to extend that knowledge (e.g.,
by requiring the proof of a result not contained in the chapter).
We wish to thank, first of all, Professor Ian Blake, who read an early version
of the entire manuscript and provided many important suggestions that led to a
much improved book.
We also wish to thank the many graduate students who have been a tremendous
help in the preparation of this book. They have helped with typesetting, computer
simulations, proofreading, and figures, and many of their research results can be
found in this book. The students (former and current) who have contributed to
W. Ryan’s portion of the book are Dr. Yang Han, Dr. Yifei Zhang, Dr. Michael
(Sizhen) Yang, Dr. Yan Li, Dr. Gianluigi Liva, Dr. Fei Peng, Shadi Abu-Surra,
Kristin Jagiello (who proofread eight chapters), and Matt Viens. Gratitude is also
due to Li Zhang (S. Lin’s student) who provided valuable feedback on Chapters 6
and 9. Finally, W. Ryan acknowledges Sara Sandberg of Lule˚a Institute of Tech-
nology for helpful feedback on an early version of Chapter 5. The students who
have contributed to S. Lin’s portion of the book are Dr. Bo Zhou, Qin Huang,
Dr. Ying Y. Tai, Dr. Lan Lan, Dr. Lingqi Zeng, Jingyu Kang, and Li Zhang; Dr.
Bo Zhou and Qin Huang deserve special appreciation for typing S. Lin’s chapters
and overseeing the preparation of the final version of his chapters.
We thank Professor Dan Costello, who sent us reference material for the con-
volutional LDPC code section in Chapter 15, Dr. Marc Fossorier, who provided
comments on Chapter 14, and Professor Ali Ghrayeb, who provided comments on
Chapter 7.
We are grateful to the National Science Foundation, the National Aeronautics
and Space Administration, and the Information Storage Industry Consortium for
their many years of funding support in the area of channel coding. Without their
support, many of the results in this book would not have been possible. We also
thank the University of Arizona and the University of California, Davis for their
support in the writing of this book.

xvi Preface
We also acknowledge the talented Mrs. Linda Wyrgatsch whose painting on the
back cover was created specifically for this book. We note that the paintings on
the front and back covers are classical and modern, respectively.
Finally, we would like to give special thanks to our wives (Stephanie and Ivy),
children, and grandchildren for their continuing love and affection throughout this
project.
William E. Ryan Shu Lin
University of Arizona University of California, Davis
Web sites for this book:
www.cambridge.org/9780521848688
http://www.ece.arizona.edu/˜ryan/ChannelCodesBook/
1
Coding and Capacity
1.1 Digital Data Communication and Storage
Digital communication systems are ubiquitous in our daily lives. The most obvious
examples include cell phones, digital television via satellite or cable, digital radio,
wireless internet connections via Wi-Fi and WiMax, and wired internet connec-
tion via cable modem. Additional examples include digital data-storage devices,
including magnetic (“hard”) disk drives, magnetic tape drives, optical disk drives
(e.g., CD, DVD, blu-ray), and flash drives. In the case of data-storage, informa-
tion is communicated from one point in time to another rather than one point in
space to another. Each of these examples, while widely different in implementa-
tion details, generally fits into a common digital communication framework first
established by C. Shannon in his 1948 seminal paper, A Mathematical Theory
of Communication [1]. This framework is depicted in Figure 1.1, whose various
components are described as follows.
Source and user (or sink ). The information source may be originally in analog
form (e.g., speech or music) and then later digitized, or it may be originally in
digital form (e.g., computer files). We generally think of its output as a sequence
of bits, which follow a probabilistic model. The user of the information may be
a person, a computer, or some other electronic device.
Source encoder and source decoder. The encoder is a processor that converts
the information source bit sequence into an alternative bit sequence with a
more efficient representation of the information, i.e., with fewer bits. Hence, this
operation is often called compression. Depending on the source, the compression
can be lossless (e.g., for computer data files) or lossy (e.g., for video, still images,
or music, where the loss can be made to be imperceptible or acceptable). The
source decoder is the encoder’s counterpart which recovers the source sequence
exactly, in the case of lossless compression, or approximately, in the case of lossy
compression, from the encoder’s output sequence.
Channel encoder and channel decoder. The role of the channel encoder is to
protect the bits to be transmitted over a channel subject to noise, distortion,
and interference. It does so by converting its input into an alternate sequence
possessing redundancy, whose role is to provide immunity from the various
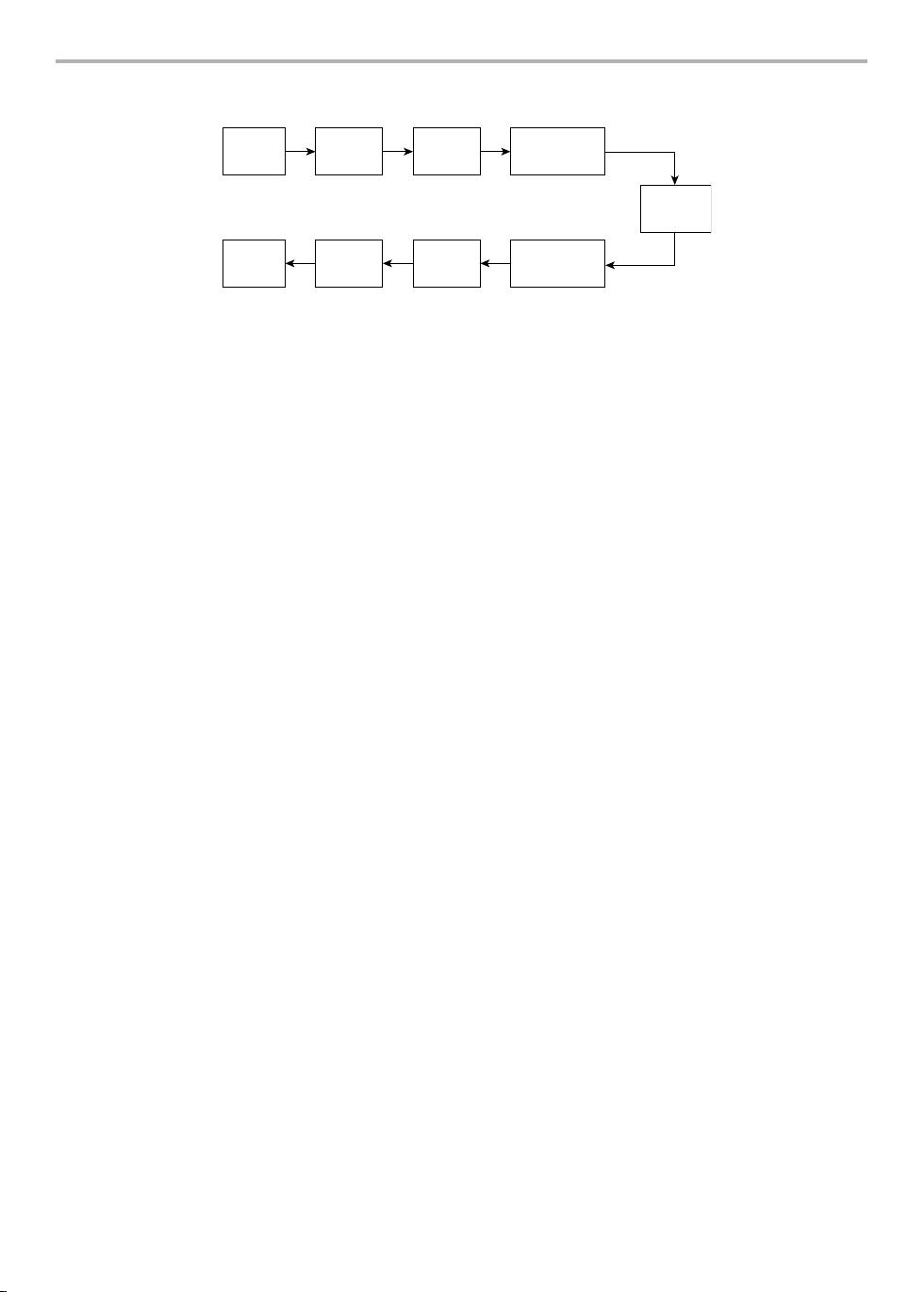
2 Coding and Capacity
Source
Source
encoder
Channel
encoder
Modulator
Source
decoder
Channel
decoder
DemodulatorUser
Channel
Figure 1.1 Basic digital communication- (or storage-) system block diagram due to Shannon.
channel impairments. The ratio of the number of bits that enter the channel
encoder to the number that depart from it is called the code rate, denoted by
R, with 0 <R<1. For example, if a 1000-bit codeword is assigned to each
500-bit information word, R =1/2, and there are 500 redundant bits in each
codeword. The function of the channel decoder is to recover from the channel
output the input to the channel encoder (i.e., the compressed sequence) in spite
of the presence of noise, distortion, and interference in the received word.
Modulator and demodulator. The modulator converts the channel-encoder out-
put bit stream into a form that is appropriate for the channel. For example,
for a wireless communication channel, the bit stream must be represented by
a high-frequency signal to facilitate transmission with an antenna of reason-
able size. Another example is a so-called modulation code used in data storage.
The modulation encoder output might be a sequence that satisfies a certain
runlength constraint (runs of like symbols, for example) or a certain spectral
constraint (the output contains a null at DC, for example). The demodulator is
the modulator’s counterpart which recovers the modulator input sequence from
the modulator output sequence.
Channel. The channel is the physical medium through which the modulator
output is conveyed, or by which it is stored. Our experience teaches us that
the channel adds noise and often interference from other signals, on top of the
signal distortion that is ever-present, albeit sometimes to a minor degree. For
our purposes, the channel is modeled as a probabilistic device, and examples will
be presented below. Physically, the channel can included antennas, amplifiers,
and filters, both at the transmitter and at the receiver at the ends of the system.
For a hard-disk drive, the channel would include the write head, the magnetic
medium, the read head, the read amplifier and filter, and so on.
Following Shannon’s model, Figure 1.1 does not include such blocks as encryp-
tion/decryption, symbol-timing recovery, and scrambling. The first of these is
optional and the other two are assumed to be ideal and accounted for in the
probabilistic channel models. On the basis of such a model, Shannon showed that
a channel can be characterized by a parameter, C, called the channel capacity,
which is a measure of how much information the channel can convey, much like
剩余709页未读,继续阅读
清江渔人
- 粉丝: 3
- 资源: 3
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

最新资源
- zlib-1.2.12压缩包解析与技术要点
- 微信小程序滑动选项卡源码模版发布
- Unity虚拟人物唇同步插件Oculus Lipsync介绍
- Nginx 1.18.0版本WinSW自动安装与管理指南
- Java Swing和JDBC实现的ATM系统源码解析
- 掌握Spark Streaming与Maven集成的分布式大数据处理
- 深入学习推荐系统:教程、案例与项目实践
- Web开发者必备的取色工具软件介绍
- C语言实现李春葆数据结构实验程序
- 超市管理系统开发:asp+SQL Server 2005实战
- Redis伪集群搭建教程与实践
- 掌握网络活动细节:Wireshark v3.6.3网络嗅探工具详解
- 全面掌握美赛:建模、分析与编程实现教程
- Java图书馆系统完整项目源码及SQL文件解析
- PCtoLCD2002软件:高效图片和字符取模转换
- Java开发的体育赛事在线购票系统源码分析
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功