没有合适的资源?快使用搜索试试~ 我知道了~
首页SoC与IP安全基石:设计、验证与调试指南
《IP与SoC安全基础》是一本深度探讨嵌入式系统及其硬件IP和系统级芯片(System-on-Chip, SoC)安全的权威指南。该书由Swarup Bhunia、Sandip Ray和Susmita Sur-Kolay三位编辑共同编撰,涵盖了系统设计、验证和调试中的关键问题。作者们从嵌入式系统安全的基本要求出发,详细阐述了SoC设计中确保和验证安全策略的架构定义和选择,以及在安全、功能性和调试需求之间可能存在的权衡和冲突。 书中强调了安全问题的“跨领域”视角,即它如何与架构设计、实现、验证和调试等各个环节相互作用。读者可以了解到从整体概述到深入的实施分析,再到具体的设计、验证和调试案例研究,内容全面且实用,涵盖了IP和SoC安全的核心知识点。例如,书中可能会涵盖加密技术在SoC中的应用,硬件安全模块的设计,以及如何在满足安全要求的同时避免性能瓶颈,同时保证系统的可调试性。 此外,本书还关注当前工业实践中的实际挑战,提供了从设计阶段到实现和验证的深度洞察,帮助工程师们理解和解决在实际项目中遇到的安全问题。对于那些致力于嵌入式系统和SoC安全领域的专业人士,这本书不仅提供了一个全面的学习平台,也是在快速发展的安全威胁环境中保持竞争力的重要参考资源。 《IP与SoC安全基础》是一本综合性的教程,旨在提升设计者对SoC安全的理解和实践能力,使他们能够在保障系统安全的同时,兼顾功能性和效率,确保在不断变化的市场和技术环境中做出明智决策。通过阅读这本书,读者将获得宝贵的知识和实践经验,以应对日益复杂的嵌入式系统安全挑战。
资源详情
资源推荐
10 S. Ray et al.
Usages Assets Exposed
Browsing Browsing history
Fitness tracking Health information,sleep pattern
GPS Location
Phone call Contacts
Banking,Stock trading Finances
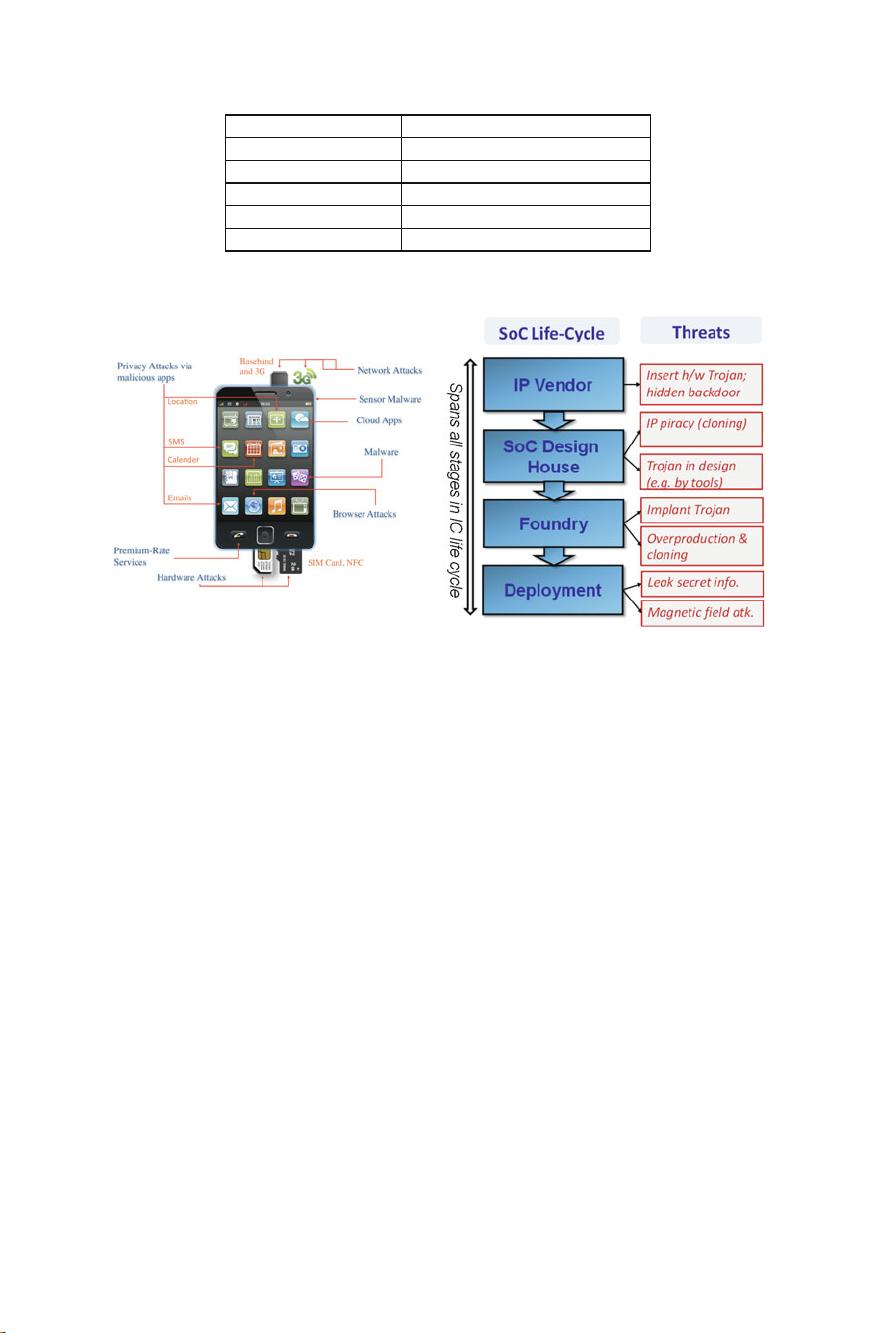
Fig. 2.1 Some typical smartphone applications and corresponding private end user information
(a) (b)
Fig. 2.2 Some potential attacks on a modern SoC design. a Potential attack areas for a smartphone
after production and deployment. b Potential threats from untrusted supply chain during the design
life cycle of an SoC design
out to unauthorized sources. This includes cryptographic and DRM keys, premium
content locks, firmware execution flows, debug modes, etc. Note that the notion of
“unauthorized source” changes based on what asset we are talking about: end user
may be an unauthorized source for DRM keys while manufacturer/OEM may be an
unauthorized source for end user private information.
In addition to criticality of the assets involved, another factor that makes SoC
security both critical and challenging is the high diversity of attacks possible.
Figure 2.2 provides a flavor of potential attacks on a modern SoC design. Of par-
ticular concern are the following two observations:
∙ Because of the untrusted nature of the supply chain, there are security threats at
most stages of the design development, even before deployment and production.
∙ A deployed SoC design inside a computing device (e.g., smartphone) in the hand
of the end user is prone to a large number of potential attacker entry points, includ-
ing applications, software, and network, browser, and sensors. Security assurance
must permit protection against this large attack surface.
We discuss security validation for the continuum of attacks from design to deploy-
ment. Given that the attacks are diverse, protection mechanisms are also varied, and

2 Security Validation in Modern SoC Designs 11
each induces a significantly different validation challenge. However, validation tech-
nology is still quite limited. For most of the security requirements, we still very much
depend on the perspicuity, talent, and experience of the human validators to identify
potential vulnerabilities.
2.2 Supply Chain Security Threats
The life cycle of a SoC from concept to deployment involves number of security
threats at all stages involving various parties. Figure 2.2b shows the SoC life cycle
and the security threats that span the entire life cycle. These threats are increasing
with the rapid globalization of the SoC design, fabrication, validation, and distribu-
tion steps, driven by the global economic trend.
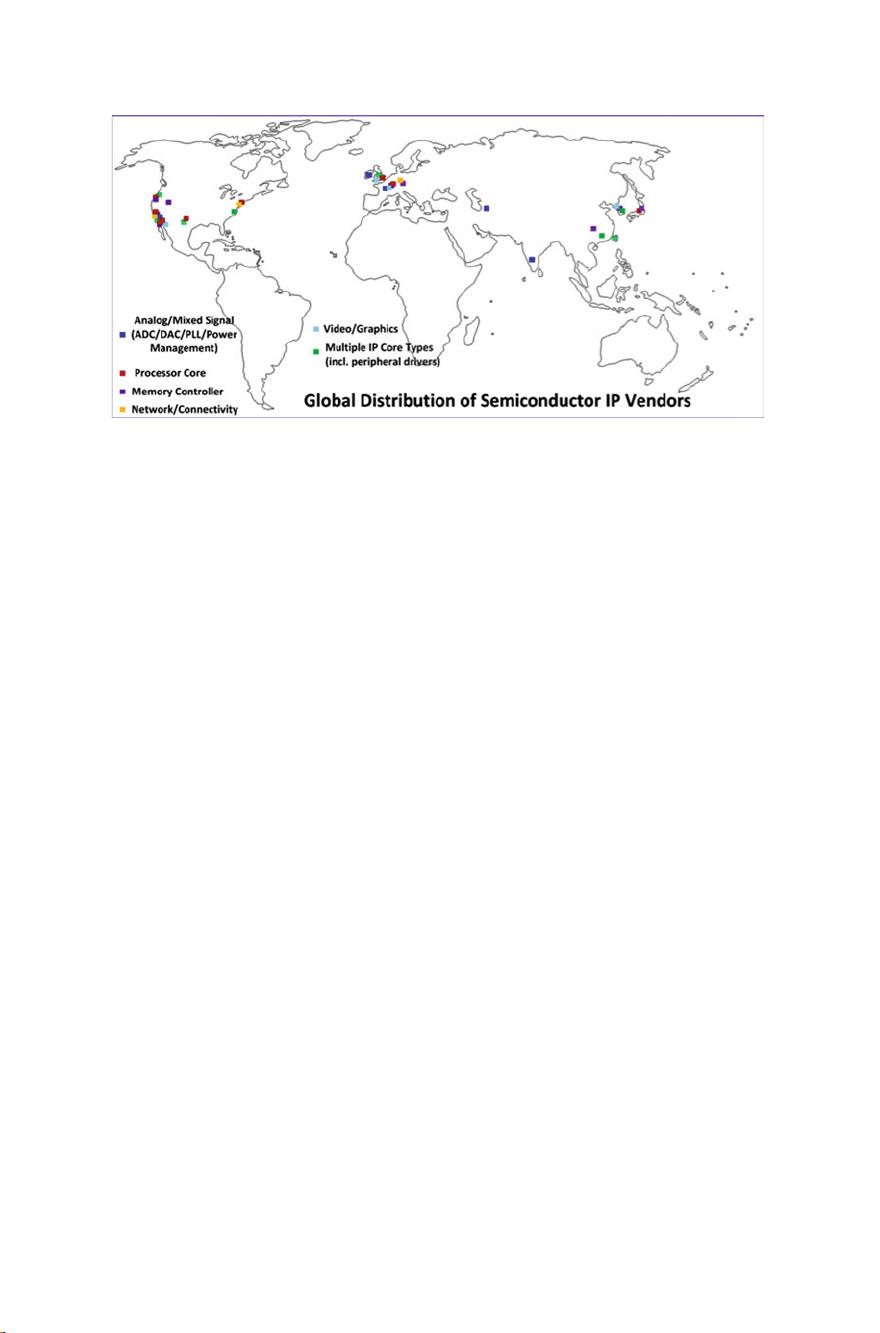
This growing reliance on reusable pre-verified hardware IPs during SoC design,
often gathered from untrusted third-party vendors, severely affects the security and
trustworthiness of SoC computing platforms. Statistics show that the global market
for third-party semiconductor IPs grew by more than 10 % to reach more than 2.1
billion in late 2012 [1]. The design, fabrication, and supply chain for these IP cores is
generally distributed across the globe involving USA, Europe, and Asia. Figure 2.3
illustrates the scenario for an example SoC that includes processor, memory con-
trollers, security, graphics, and analog core. Due to growing complexity of the IPs
as well as the SoC integration process, SoC designers increasingly tend to treat these
IPs as black box and rely on the IP vendors on the structural/functional integrity of
these IPs. However, such design practices greatly increase the number of untrusted
components in a SoC design and make the overall system security a pressing con-
cern.
Hardware IPs acquired from untrusted third-party vendors can have diverse secu-
rity and integrity issues. An adversary inside an IP design house involved in the
IP design process can deliberately insert a malicious implant or design modifi-
cation to incorporate hidden/undesired functionality. In addition, since many of
the IP providers are small vendors working under highly aggressive schedules,
it is difficult to ensure a stringent IP validation requirement in this ecosystem.
Design features may also introduce unintentional vulnerabilities, e.g., intentional
information leakage through hidden test/debug interfaces or side-channels through
power/performance profiles. Similarly, IPs can have uncharacterized parametric
behavior (e.g., power/thermal) which can be exploited by an attacker to cause irrecov-
erable damage to an electronic system. There are documented instances of such
attacks. For example, in 2012, a study by a group of researchers in Cambridge
revealed an undocumented silicon level backdoor in a highly secure military-grade
ProAsic3 FPGA device from MicroSemi (formerly Actel) [2], which was later
described as a vulnerability induced unintentionally by on-chip debug infrastruc-
ture. In a recent report, researchers have demonstrated such an attack where a mali-
cious upgrade of a firmware destroys the processor it is controlling by affecting
the power management system [3]. It manifests a new attack mode for IPs, where
12 S. Ray et al.
Fig. 2.3 An SoC would often contain hardware IP blocks obtained from entities distributed across
the globe
firmware/software update can maliciously affect the power/performance/temperature
profile of a chip to either destroy a system or reveal secret information through appro-
priate side-channel attack, e.g., a fault or timing attack.
Trusted and untrusted CAD tools pose similar trust issues to the SoC design-
ers. Such tools are designed to optimize a design for power, performance, and area.
Security optimization is not an option in today’s tools, hence sometimes during the
optimization new vulnerabilities are introduced [4]. Rogue designers in an untrusted
design facility, e.g., in case of a design outsourced to a facility for Design-for-Test
(DFT) or Design-for-Debug (DFD) insertion, can compromise the integrity of a SoC
design through insertion of stealthy hardware Trojan. These Trojans can act as back-
door or compromise the functional/parametric properties of a SoC in various ways.
Finally, many SoC manufacturers today are fabless and hence must rely upon
external untrusted foundries for fabrication service. An untrusted foundry would
have access to the entire SoC design and thus brings in several serious security con-
cerns, which include reverse-engineering and piracy of the entire SoC design or the
IP blocks as well as tampering in the form of malicious design alterations or Trojan
attacks. During distribution of fabricated SoCs through a typically long globally dis-
tributed supply chain, consisting of multiple layers of distributors, wholesalers, and
retailers, the threat of counterfeits is a growing one. These counterfeits can be low-
quality clones, overproduced chips in untrusted foundry, or recycled ones [5]. Even
after deployment, the systems are vulnerable to physical attacks, e.g., side-channel
attacks which target information leakage, and magnetic field attacks that aim at cor-
rupting memory content to cause denial-of-service (DoS) attacks.
2 Security Validation in Modern SoC Designs 13
2.3 Security Policies: Requirements from Design
In addition to supply-chain threats, the design itself may have exploitable vulnerabil-
ities. Vulnerabilities in system design, in fact, forms the quintessential objective of
security study, and has been the focus of research for over three decades. At a high
level, the definition of security requirement for assets in a SoC design follows the
well-known “CIA” paradigm, developed as part of information security research [6].
In this paradigm, accesses and updates to secure assets are subject to the following
three requirements:
∙ Confidentiality: An asset cannot be accessed by an agent unless authorized to do
so.
∙ Integrity: An asset can be mutated (e.g., the data in a secure memory location can
be modified) only by an agent authorized to do so.
∙ Availability: An asset must be accessible to an agent that requires such access as
part of correct system functionality.
Of course, mapping these high-level requirements to constraints on individual assets
in a system is nontrivial. This is achieved by defining a collection of security poli-
cies that specify which agent can access a specific asset and under what conditions.
Following are two examples of representative security policies. Note that while illus-
trative, these examples are made up and do not represent security policy of a specific
company or system.
Example 1 During boot time, data transmitted by the cryptographic engine cannot
be observed by any IP in the SoC other than its intended target.
Example 2 A programmable fuse containing a secure key can be updated during
manufacturing but not after production.
Example 1 is an instance of confidentiality, while Example 2 is an instance of
integrity policy; however, the policies are at a lower level of abstraction since they
are intended to be translated to “actionable” information, e.g., architectural or design
features. The above examples, albeit hypothetical, illustrate an important character-
istic of security policies: the same agent may or may not be authorized access (or
update) of the same security asset depending on (1) the phase of the execution (i.e.,
boot or normal), or (2) the phase of the design life cycle (i.e., manufacturing or pro-
duction). These factors make security policies difficult to implement. Exacerbating
the problem is the fact that there is typically no central documentation for security
policies; documentation of policies can range from microarchitectural and system
integration documents to informal presentations and conversations among architects,
designers, and implementors. Finally, the implementation of a policy is an exercise
in concurrency, with different components of the policy implemented in different IPs
(in hardware, software, or firmware), that coordinate together to ensure adherence to
the policy.
Unfortunately, security policies in a modern SoC design are themselves signifi-
cantly complex, and developed in ad hoc manner based on customer requirements

14 S. Ray et al.
and product needs. Following are some representative policy classes. They are not
complete, but illustrate the diversity of policies employed.
Access Control. This is the most common class of policies, and specifies how differ-
ent agents in an SoC can access an asset at different points of the execution. Here an
“agent” can be a hardware or software component in any IP of the SoC. Examples 1
and 2 above represent such policy. Furthermore, access control forms the basis of
many other policies, including information flow, integrity, and secure boot.
Information Flow. Values of secure assets can sometimes be inferred without direct
access, through indirect observation or “snooping” of intermediate computation or
communications of IPs. Information flow policies restrict such indirect inference.
An example of information flow policy might be the following.
∙ Key Obliviousness: A low-security IP cannot infer the cryptographic keys by
snooping only the data from crypto engine on a low-security communication fab-
ric.
Information flow policies are difficult to analyze. They often require highly sophisti-
cated protection mechanisms and advanced mathematical arguments for correctness,
typically involving hardness or complexity results from information security. Con-
sequently they are employed only on critical assets with very high confidentiality
requirements.
Liveness. These policies ensure that the system performs its functionality without
“stagnation” throughout its execution. A typical liveness policy is that a request for
a resource by an IP is followed by an eventual response or grant. Deviation from
such a policy can result in system deadlock or livelock, consequently compromising
system availability requirements.
Time-of-Check Versus Time of Use (TOCTOU). This refers to the requirement
that any agent accessing a resource requiring authorization is indeed the agent that
has been authorized. A critical example of TOCTOU requirement is in firmware
update; the policy requires firmware eventually installed on update is the same
firmware that has been authenticated as legitimate by the security or crypto engine.
Secure Boot. Booting a system entails communication of significant security assets,
e.g., fuse configurations, access control priorities, cryptographic keys, firmware
updates, debug and post-silicon observability information, etc. Consequently, boot
imposes more stringent security requirements on IP internals and communications
than normal execution. Individual policies during boot can be access control, infor-
mation flow, and TOCTOU requirements; however, it is often convenient to coalesce
them into a unified set of boot policies.
剩余315页未读,继续阅读
soctest2010
- 粉丝: 0
- 资源: 6
上传资源 快速赚钱
 我的内容管理
收起
我的内容管理
收起
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

会员权益专享
最新资源
- 电力电子系统建模与控制入门
- SQL数据库基础入门:发展历程与关键概念
- DC/DC变换器动态建模与控制方法解析
- 市***专有云IaaS服务:云主机与数据库解决方案
- 紫鸟数据魔方:跨境电商选品神器,助力爆款打造
- 电力电子技术:DC-DC变换器动态模型与控制
- 视觉与实用并重:跨境电商产品开发的六重价值策略
- VB.NET三层架构下的数据库应用程序开发
- 跨境电商产品开发:关键词策略与用户痛点挖掘
- VC-MFC数据库编程技巧与实现
- 亚马逊新品开发策略:选品与市场研究
- 数据库基础知识:从数据到Visual FoxPro应用
- 计算机专业实习经验与项目总结
- Sparkle家族轻量级加密与哈希:提升IoT设备数据安全性
- SQL数据库期末考试精选题与答案解析
- H3C规模数据融合:技术探讨与应用案例解析
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功