没有合适的资源?快使用搜索试试~ 我知道了~
首页2012版《图算法》详解:奠基之作,深入浅出
2012版《图算法》详解:奠基之作,深入浅出
需积分: 9 1 下载量 28 浏览量
更新于2024-07-28
收藏 1.47MB PDF 举报
《图算法,第二版》是由Shimon Even和Guy Even在2012年出版的一本经典著作,它基于Shimon Even于1979年推出的开创性教材《图算法》。这本书在第一版的基础上进行了全面修订,增添了Richard M. Karp的序言以及Andrew V. Goldberg的注释,旨在保持其在介绍图论算法方面的卓越表现。作者们以其直观且直接的方式,用简单易懂的语言解释复杂的算法概念。 本书内容覆盖了图论的基本理论,如图和最短路径分析,介绍了树结构、深度优先搜索(DFS)和广度优先搜索(BFS)等基础算法。这些是理解网络结构和通信的关键基石。随后,书的主体部分深入探讨了网络流的概念及其应用,这是许多实际问题求解中的核心工具,如路由优化和资源分配。 在书的末尾,作者们专辟两章讨论平面图和测试图的平面性,这对于计算机图形学和算法设计中处理复杂布局问题至关重要。平面图的性质对诸如地图绘制、电路设计和网络拓扑规划等领域具有重要意义。 Shimon Even(1935-2004)是图算法和密码学领域的先驱,他在以色列的魏茨曼研究所和科技大学推动了计算机科学教育的发展。他的教学影响力深远,不仅作为专业上的灵感源泉,更是数代学生和研究者的榜样。他还是《算法组合学》(1973年)的作者,这表明他对算法理论的贡献不仅限于图论领域,而是扩展到了更广泛的数学和计算机科学领域。 《图算法,第二版》是一本既适合初学者入门又满足专业人士需求的经典之作,无论是理论学习还是实际应用,都能从中收获丰富的知识和洞见。通过阅读这本书,读者将掌握一系列关键的图论算法,并理解它们如何在信息技术领域发挥作用。
资源详情
资源推荐

2 1 Paths in Graphs
e
3
v
1
e
1
e
2
v
2
v
3
v
4
e
5
e
4
v
5
Figure 1.1: Example of a graph.
The notation u
e
v means that the edge e is incident on vertices u and v.In
this case we also say that e connects vertices u and v, or that vertices u and v
are adjacent.
A path, P, is a sequence of vertices and edges, interweaved in the following
way: P starts with a vertex, say v
0
,followedbyanedgee
1
incident to v
0
,
followed by the other endpoint v
1
of e
1
, and so on. We write
P : v
0
e
1
v
1
e
2
v
2
···
If P is finite, it ends with a vertex, say v
l
. We call v
0
the start-vertex of P and
v
l
the end-vertex of P. The number of edge appearances in P, l, is called the
length of P.Ifl = 0, then P is said to be empty, but it has a start-vertex and
an end-vertex, which are identical. (We shall not use the term “path” unless a
start-vertex exists.)
In a path, edges and vertices may appear more than once, unless otherwise
stated. If no vertex appears more than once, and therefore no edge can appear
more than once, the path is called simple.
A circuit, C,isafinite path in which the start and end vertices are identical.
However, an empty path is not considered a circuit. By definition, the start and
end verticesof a circuit are the same, and ifthere isno other repetition ofa vertex,
the circuit is called simple. However, a circuit of lengthtwo,a
e
b
e
a,where
the same edge, e, appears twice, is not considered simple. (For a longer circuit,
it is superfluous to state that if it is simple, then no edge appears more than
once.) A self-loop is a simple circuit of length one.
If for every two vertices u and v of a graph G,thereisa(finite) path that starts
in u and ends in v,thenG is said to be connected.
A digraph or directed graph G(V,E) is defined similarly to a graph, except
that the pair of endpoints of every edge is now ordered. If the ordered pair of

1.2 Computer Representation of Graphs 3
endpoints of a (directed) edge e is (u,v), we write
u
e
−→ v.
The vertex u is called the start-vertex of e; and the vertex, v,theend-vertex of
e. The edge e is said to be directed from u to v. Edges with the same start-vertex
and the same end-vertex are called parallel.Ifu = v, u
e
1
−→ v and v
e
2
−→ u,then
e
1
and e
2
are antiparallel. An edge u −→ u is called a self-loop.
The out-degree d
out
(v) of vertex v is the number of (directed) edges having
v as their start-vertex; in-degree d
in
(v) is similarly defined. Clearly, for every
finite digraph G(V,E),
v∈V
d
in
(v)=
v∈V
d
out
(v).
A directed path is similar to a path in an undirected graph; if the sequence of
edges is e
1
,e
2
,··· then for every i 1, the end-vertex of e
i
is the start-vertex of
e
i+1
. The directed path is simple if no vertex appears on it more than once. A
finite directed path C is a directed circuit if the start-vertex and end-vertex of C
are the same. If C consists of one edge, it is a self-loop. As stated, the start and
end vertices of C are identical, but if there is no other repetition of a vertex, C
is simple. A digraph is said to be strongly connected if, for every ordered pair
of vertices (u,v) there is a directed path which starts at u and ends in v.
1.2 Computer Representation of Graphs
To understand the time and space complexities of graph algorithms one needs
to know how graphs are represented in the computers memory. In this section
two of the most common methods of graph representation are briefly described.
Let us consider graphs and digraphs that have no parallel edges. For such
graphs, the specification of the two endpoints is sufficient to specify the edge;
for digraphs, the specification of the start-vertex and the end-vertexis sufficient.
Thus, we can represent such a graph or digraph of n vertices by an n× n matrix
M,whereM
ij
= 1 if there is an edge connecting vertex v
i
to v
j
,andM
ij
= 0, if
not. Clearly, in the case of (undirected) graphs, M
ij
= 1 implies that M
ji
= 1;
or in other words,M is symmetric. But in the case of digraphs, any n×n matrix
of zeros and ones is possible. This matrix is called the adjacency matrix.
Given the adjacency matrix M of a graph, one can compute d(v
i
) by counting
the number of ones in the i-th row, except that a one on the main diagonal
representsa self-loop and contributestwoto the count. For a digraph,the number

4 1 Paths in Graphs
of ones in the i-th row is equal to d
out
(v
i
), and the number of ones in the j-th
column is equal to d
in
(v
j
).
The adjacency matrix is not an efficientrepresentationof the graph if thegraph
is sparse; namely, the number of edges is significantly smaller than n
2
.Inthese
cases, it is more efficient to use the incidence lists representation, described
later. We use this representation, which also allows parallel edges, in this book
unless stated otherwise.
A vertex array is used. For each vertex v, it lists v’s incident edges and a
pointer indicating the current edge. The incidence list maysimplybeanarray
or may be a linked list. Initially, the pointer points to the first edge on the list.
Also, we use an edge array, which tells us for each edge its two endpoints (or
start-vertex and end-vertex, in the case of a digraph).
Assume we want an algorithm TRACE(s,P), such that given a finite graph
G(V,E) and a start-vertex s ∈ V traces a maximal path P that starts at s and does
not use any edge more than once. Note that by “maximal” we do not mean that
the resulting path, P, will be the longest possible; we only mean that P cannot
be extended, that is, there are no unused incident edges at the end-vertex.
We can trace a path starting at s by taking the first edge e
1
on the incidence list
of s, marking e
1
as “used” in the edge array, and looking up its other endpoint
v
1
(which is s if e
1
is a self-loop). Next, use the vertex array to find the pointer
to the current edge on the list of v
1
. Scan the incidence list of v
1
for the first
unused edge, take it, and so on. If the scanning hits the last edge and it is used,
TRACE(s,P) halts. A PASCAL-like description of TRACE(s,P) is presented
in Algorithm 1.1. Here is a list of the data structures it uses:
(i) A vertex table such that, for every v ∈ V, it includes the following:
– A list of the edges incident on v, which ends with NIL
– A pointer N(v) to the current item in this list. Initially, N(v) points to
the first edge on the list (or to NIL, if the list is empty).
(ii) An edge table such that every e ∈ E consists of the following:
– The two endpoints of e
– A flag that indicates whether e is used or unused. Initially, all edges are
unused.
(iii) An array (or linked list) P of edges that is initially empty, and when
TRACE(s,P) halts, will contain the resulting path.
Notice that in each application of the “while” loop of TRACE (lines 2–10 in
Algorithm 1.1), either N(v) is moved to the next item on the incidence list of
v (line 4), or lines 6–10 are applied, but not both. The number of times line
1.2 Computer Representation of Graphs 5
Procedure TRACE(s,P)
1 v ← s
2 while N(v) points to an edge (and not to NIL) do
3 if N(v) points to a used edge do
4 change N(v) to point to the next item on the list
5 else do
6 e ← N(v)
7 change the flag of e to used
8adde to the end of P
9 use the edge table to find the second endpoint of e,sayu
10 v ← u
Algorithm 1.1: The TRACE algorithm.
4 is applied is clearly O(|E|). The number of times lines 6–10 are applied is
also O(| E|), since the flag of an unused edge changes to used, and each of these
lines takes time bounded by a constant to run. Thus, the time complexity of
TRACEisO(|E| ).
1
(Infact,ifthelengthoftheresultingPisLthenthetime
complexity is O(l); this follows from the fact that each edge that joins P can
“cause a waste” of computing time only twice: once when it joins P and, at
most, once again by its appearance on the incidence list of the adjacent vertex.)
If one uses the adjacency matrix representation, in the worst case, the tracing
algorithmtakestime(andspace)complexityΩ(|V |
2
).
2
Andif |E|<< |V |
2
,asis
the case for sparse graphs, the complexity is reduced by using the incidence-list
representation. Since in most applications, the graphs are sparse, we prefer to
use the incidence-list representation.
Note that in our discussions of complexity, we assume that the word length of
our computer is sufficient to store the names of our atomic components: vertices
and edges. If one does not make this assumption, then one may have to allow
Ω(log(|E| + |V|)) bits to represent the atomic components, and to multiply the
complexities by this factor.
1
f(x) is O(g(x)) if there are two constants k
1
and k
2
, such that for every x, f(x)k
1
·
g(x)+k
2
.
2
f(x) is Ω(g(x)) if there are two constants k
3
and k
4
, such that for every x, f(x)k
3
·
g(x)+k
4
.
6 1 Paths in Graphs
1.3 Euler Graphs
An Euler path of a finite undirected graph G(V,E) isapathsuchthatevery
edge of G appears on it once. Therefore, the length of an Euler path is |E|.IfG
has an Euler path, then it is called an Euler graph.
Theorem 1.1 A finite (undirected) connected graph is an Euler graph if and
only if exactly two vertices are of odd degree or all vertices are of even degree.
In the latter case, every Euler path of the graph is a circuit, and in the former
case, none is.
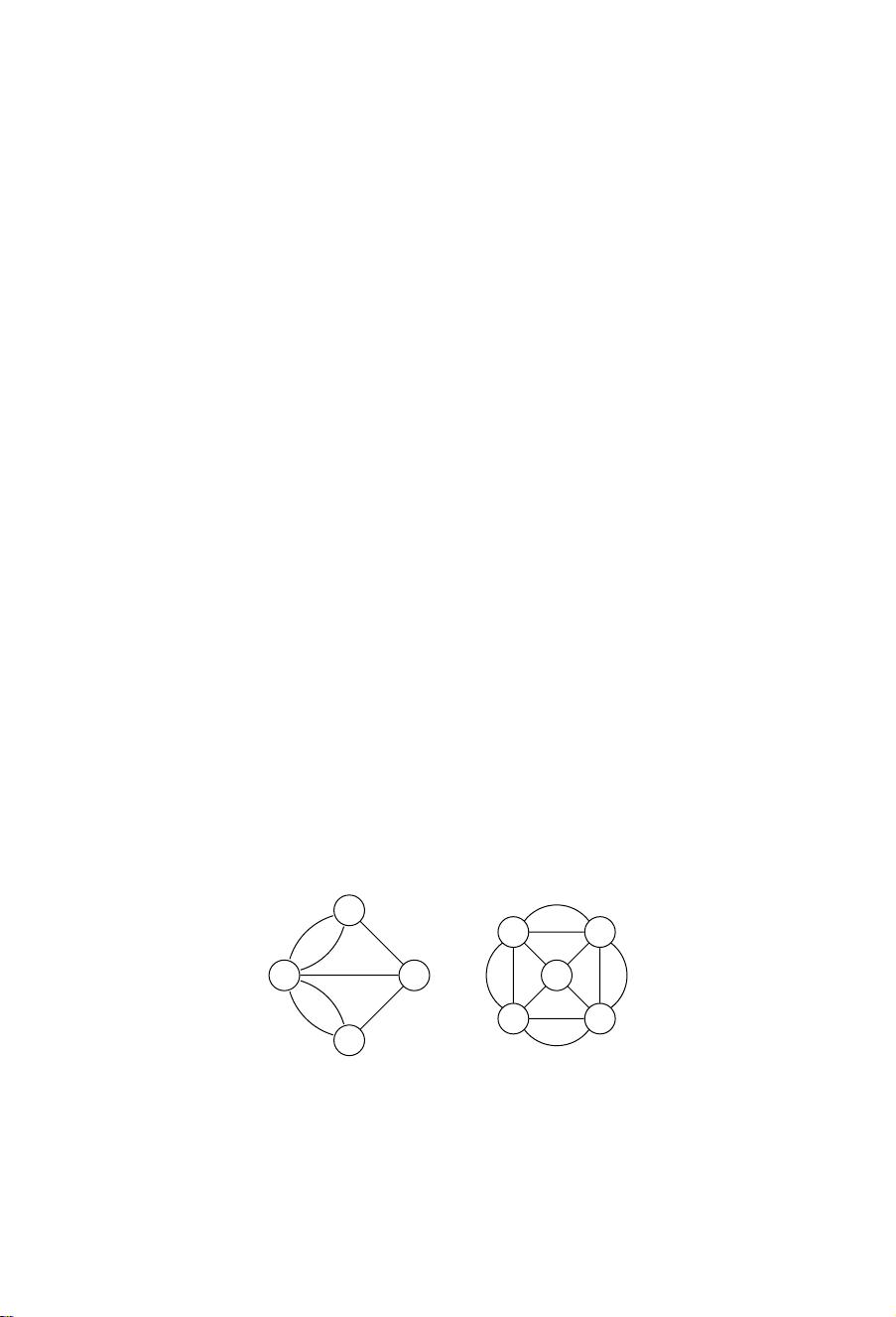
As an immediate conclusion of Theorem 1.1 we observe that none of the
graphs in Figure 1.2 is an Euler graph because both have four vertices of odd
degree. The graph shown in Figure 1.2(a) is the famous Königsberg bridge
problem solved by Euler in 1736. Thegraph shown in Figure1.2(b) is a common
misleading puzzle of the type “draw without lifting your pen from the paper.”
Proof: It is clear that if a graph has an Euler path that is not a circuit, then
the start-vertex and the end-vertex of the path are of odd degree, while all the
other vertices are of even degree. Also, if a graph has an Euler circuit, then all
vertices are of even degree.
Assume now that G is a finite graph with exactly two vertices of odd degree,
a and b. We now describe an algorithm (A), which will find an Euler path from
a to b.
First, trace a maximal path P, as in the previous section, starting at vertex a.
Since G is finite, the algorithm halts, producing a path. But as soon as the path
emanates from a, one of the edges incident to a is used, and a’s residual degree
becomes even. Thus, every time a is reentered, there is an unused edge to leave
(a) (b)
Figure 1.2: Non-Eulerian graphs.
剩余203页未读,继续阅读
zou_mono
- 粉丝: 0
- 资源: 40
上传资源 快速赚钱
 我的内容管理
展开
我的内容管理
展开
 我的资源
快来上传第一个资源
我的资源
快来上传第一个资源
 我的收益 登录查看自己的收益
我的收益 登录查看自己的收益 我的积分
登录查看自己的积分
我的积分
登录查看自己的积分
 我的C币
登录后查看C币余额
我的C币
登录后查看C币余额
 我的收藏
我的收藏  我的下载
我的下载  下载帮助
下载帮助

最新资源
- 构建Cadence PSpice仿真模型库教程
- VMware 10.0安装指南:步骤详解与网络、文件共享解决方案
- 中国互联网20周年必读:影响行业的100本经典书籍
- SQL Server 2000 Analysis Services的经典MDX查询示例
- VC6.0 MFC操作Excel教程:亲测Win7下的应用与保存技巧
- 使用Python NetworkX处理网络图
- 科技驱动:计算机控制技术的革新与应用
- MF-1型机器人硬件与robobasic编程详解
- ADC性能指标解析:超越位数、SNR和谐波
- 通用示波器改造为逻辑分析仪:0-1字符显示与电路设计
- C++实现TCP控制台客户端
- SOA架构下ESB在卷烟厂的信息整合与决策支持
- 三维人脸识别:技术进展与应用解析
- 单张人脸图像的眼镜边框自动去除方法
- C语言绘制图形:余弦曲线与正弦函数示例
- Matlab 文件操作入门:fopen、fclose、fprintf、fscanf 等函数使用详解
资源上传下载、课程学习等过程中有任何疑问或建议,欢迎提出宝贵意见哦~我们会及时处理!
点击此处反馈



安全验证
文档复制为VIP权益,开通VIP直接复制
 信息提交成功
信息提交成功